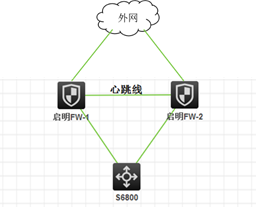
某局点S6800-54QF开启ARP主动确认功能时上行防火墙vrrp主备切换断网一分钟问题
- 0关注
- 0收藏 1291浏览
组网及说明
问题描述
Arp active-ack enable
Arp source-suppression enable
Arp source-suppression limit 100
过程分析
ARP的主动确认功能主要应用于网关设备上,防止攻击者仿冒用户欺骗网关设备。
·收到目标IP
·收到ARP
|
|
|
|
|
|
system-view |
- |
|
|
arp active-ack [ strict ] enable |
|
因为现场没有收集反馈任何信息,因此只能采用相同版本进行本地模拟复现,结果并未复现,
S125-X-----S6800
<2064-6800>dis arp
Type: S-Static D-Dynamic O-Openflow R-Rule M-Multiport I-Invalid
IP address MAC address VLAN/VSI Interface/Link ID Aging Type
120.1.1.2 74ea-c830-5001 1 XGE1/0/31 1191 D
[125X]int vlan 1
[125X-Vlan-interface1]shut
[125X-Vlan-interface1]%Sep 12 11:07:57:146 2019 125X IFNET/3/PHY_UPDOWN: -MDC=1; Physical state on the interface Vlan-interface1 changed to down.
%Sep 12 11:07:57:146 2019 125X IFNET/5/LINK_UPDOWN: -MDC=1; Line protocol state on the interface Vlan-interface1 changed to down.
[125X-Vlan-interface1]mac-address 74ea-c830-5102
[125X-Vlan-interface1]undo shut
[125X-Vlan-interface1]%Sep 12 11:09:48:000 2019 125X IFNET/3/PHY_UPDOWN: -MDC=1; Physical state on the interface Vlan-interface1 changed to up.
%Sep 12 11:09:48:001 2019 125X IFNET/5/LINK_UPDOWN: -MDC=1; Line protocol state on the interface Vlan-interface1 changed to up.
<2064-6800>
*Sep 12 03:12:27:223 2019 2064-6800 ARP/7/ARP_RCV: Received an ARP message, operation: 1, sender MAC: 74ea-c830-5102, sender IP: 120.1.1.2, target MAC: 0000-0000-0000, target IP: 120.1.1.2 ---------------收到免费arp 1(网卡起来会发两次免费arp)
*Sep 12 03:12:27:223 2019 2064-6800 ARP/7/ARP_SEND: Sent an ARP message, operation: 1, sender MAC: 9ce8-9572-8330, sender IP: 120.1.1.1, target MAC: 74ea-c830-5001, target IP: 120.1.1.2 ---------------不信这个arp的表项发生了变化,先发出个老mac的arp 请求报文
*Sep 12 03:12:27:227 2019 2064-6800 ARP/7/ARP_RCV: Received an ARP message, operation: 2, sender MAC: 74ea-c830-5102, sender IP: 120.1.1.2, target MAC: 9ce8-9572-8330, target IP: 120.1.1.1 ----------------收到了这个ip就是新mac的应答。
*Sep 12 03:12:31:432 2019 2064-6800 ARP/7/ARP_RCV: Received an ARP message, operation: 1, sender MAC: 74ea-c830-5102, sender IP: 120.1.1.2, target MAC: 0000-0000-0000, target IP: 120.1.1.2 ----------------收到免费arp 2(网卡起来会发两次免费arp)
*Sep 12 03:12:31:860 2019 2064-6800 ARP/7/ARP_SEND: Sent an ARP message, operation: 1, sender MAC: 9ce8-9572-8330, sender IP: 120.1.1.1, target MAC: 74ea-c830-5102, target IP: 120.1.1.2 ----------------再去请求这个ip对应新mac的arp请求报文。
*Sep 12 03:12:31:862 2019 2064-6800 ARP/7/ARP_RCV: Received an ARP message, operation: 2, sender MAC: 74ea-c830-5102, sender IP: 120.1.1.2, target MAC: 9ce8-9572-8330, target IP: 120.1.1.1 ------------------得到应答。 主动确认过程结束。 更新arp表项。
<2064-6800>dis arp
Type: S-Static D-Dynamic O-Openflow R-Rule M-Multiport I-Invalid
IP address MAC address VLAN/VSI Interface/Link ID Aging Type
120.1.1.2 74ea-c830-5102 1 XGE1/0/31 1199 D
<2064-6800>
[H3C]#*Jan 1 01:59:48:100 2011 H3C ARP/7/ARP_RCV: Received an ARP message, operation: 1, sender MAC: 0010-f37d-ac88, sender IP: 10.197.254.173, target MAC: 0000-0000-0000, target IP: 10.197.254.173
[H3C]*Jan 1 02:00:16:961 2011 H3C ARP/7/ARP_RCV: Received an ARP message, operation: 1, sender MAC: 0010-f37d-a940, sender IP: 10.197.254.173, target MAC: 0000-0000-0000, target IP: 10.197.254.173
*Jan 1 02:00:16:962 2011 H3C ARP/7/ARP_RCV: Received an ARP message, operation: 1, sender MAC: 0010-f37d-a940, sender IP: 10.197.254.173, target MAC: 0000-0000-0000, target IP: 10.197.254.173
*Jan 1 02:00:17:151 2011 H3C ARP/7/ARP_RCV: Received an ARP message, operation: 1, sender MAC: 0010-f37d-a940, sender IP: 10.197.254.173, target MAC: 0000-0000-0000, target IP: 10.197.254.173
*Jan 1 02:00:17:154 2011 H3C ARP/7/ARP_RCV: Received an ARP message, operation: 1, sender MAC: 0010-f37d-a940, sender IP: 10.197.254.173, target MAC: 0000-0000-0000, target IP: 10.197.254.173
[H3C]*Jan 1 02:01:08:219 2011 H3C ARP/7/ARP_RCV: Received an ARP message, operation: 1, sender MAC: 0010-f37d-a940, sender IP: 10.197.254.173, target MAC: 0000-0000-0000, target IP: 10.197.254.173
*Jan 1 02:01:08:219 2011 H3C ARP/7/ARP_SEND: Sent an ARP message, operation: 1, sender MAC: 5098-b817-f3a0, sender IP: 10.197.254.169, target MAC: 0010-f37d-ac88, target IP: 10.197.254.173
*Jan 1 02:01:13:031 2011 H3C ARP/7/ARP_SEND: Sent an ARP message, operation: 1, sender MAC: 5098-b817-f3a0, sender IP: 10.197.254.169, target MAC: 0010-f37d-a940, target IP: 10.197.254.173
*Jan 1 02:01:13:033 2011 H3C ARP/7/ARP_RCV: Received an ARP message, operation: 2, sender MAC: 0010-f37d-a940, sender IP: 10.197.254.173, target MAC: 5098-b817-f3a0, target IP: 10.197.254.169
*Jan 1 02:01:38:457 2011 H3C ARP/7/ARP_RCV: Received an ARP message, operation: 1, sender MAC: 0010-f37d-a940, sender IP: 10.197.254.173, target MAC: 0000-0000-0000, target IP: 10.197.254.173
最后找到平台研发走读代码发现,ARP主动确认发起过程有个判断机制,如果一个arp是1分钟内学习或者更新的,不会立刻触发主动确认功能,而是会1分钟后才会切换,目的是避免受到反复变化的arp恶意攻击。
1、
解决方法
解决方法:
本侧关闭arp主动确认功能或者对端调大、关闭定时发送免费arp功能。
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作