组网及说明
pc-----------------FW--------------IMC
PC分别SSH和telnet防火墙的管理口,防火墙墙上配置trap发送给IMC,本案例假设已回配置防火墙上的SNMP和IMC,保证路由可达。
配置步骤
如何查看SSH以后的trap MIB节点呢?
(1)配置debug
<F5020>debugging snmp trap packet
This command is CPU intensive and might affect ongoing services. Are you sure you want to continue? [Y/N]:y
(2)打开调试信息
<9006>terminal debugging
The current terminal is enabled to display debugging logs.
<9006>terminal monitor
The current terminal is enabled to display logs.
(3)PC ssh 防火墙,输入账户密码
(4)防火墙上可以看到如下的打印
<9006>%Nov 10 21:17:09:674 2021 M9006_IRF SSHS/6/SSHS_LOG: Accepted password for admin from 172.31.0.22 port 44571.
*Nov 10 21:17:09:684 2021 M9006_IRF SNMP/7/TRAP_PACKET:
hh3cSSHUserLogin trap<v2>
send to: 172.31.0.65
Request ID: 1035517460
Error status: 0
Error index: 0
UDP port: 162
Trap successfully sent
*Nov 10 21:17:09:684 2021 M9006_IRF SNMP/7/VBLIST:
sysUpTime.0: 61942276
*Nov 10 21:17:09:685 2021 M9006_IRF SNMP/7/VBLIST:
snmpTrapOID.0: 1.3.6.1.4.1.25506.2.22.1.3.0.3
*Nov 10 21:17:09:685 2021 M9006_IRF SNMP/7/VBLIST:
hh3cSSHSessionUserName.15521: admin
*Nov 10 21:17:09:685 2021 M9006_IRF SNMP/7/VBLIST:
hh3cSSHSessionUserIpAddrType.15521: 1
*Nov 10 21:17:09:685 2021 M9006_IRF SNMP/7/VBLIST: hh3cSSHSessionUserIpAddr.15521: ac.1f.00.18
%Nov 10 21:17:09:686 2021 M9006_IRF SNMP/6/SNMP_NOTIFY: Notification hh3cSSHUserLogin(1.3.6.1.4.1.25506.2.22.1.3.0.3) with hh3cSSHSessionUserName(1.3.6.1.4.1.25506.2.22.1.1.3.1.2.15521)=admin;hh3cSSHSessionUserIpAddrType(1.3.6.1.4.1.25506.2.22.1.1.3.1.3.15521)=1;hh3cSSHSessionUserIpAddr(1.3.6.1.4.1.25506.2.22.1.1.3.1.4.15521)=ac-1f-00-16[hex].
%Nov 10 21:17:10:691 2021 M9006_IRF SSHS/6/SSHS_CONNECT: SSH user admin (IP: 172.31.0.22) connected to the server successfully.
解释:1.3.6.1.4.1.25506.2.22.1.3.0.3就是SSH节点
接下来的几个就是类似信息的节点,例如admin是:1.3.6.1.4.1.25506.2.22.1.1.3.1.2.15521
IP的输出类型1.3.6.1.4.1.25506.2.22.1.1.3.1.3.15521
登录的IP地址ac-1f-00-16:1.3.6.1.4.1.25506.2.22.1.1.3.1.4.15521
抓包的展现是:
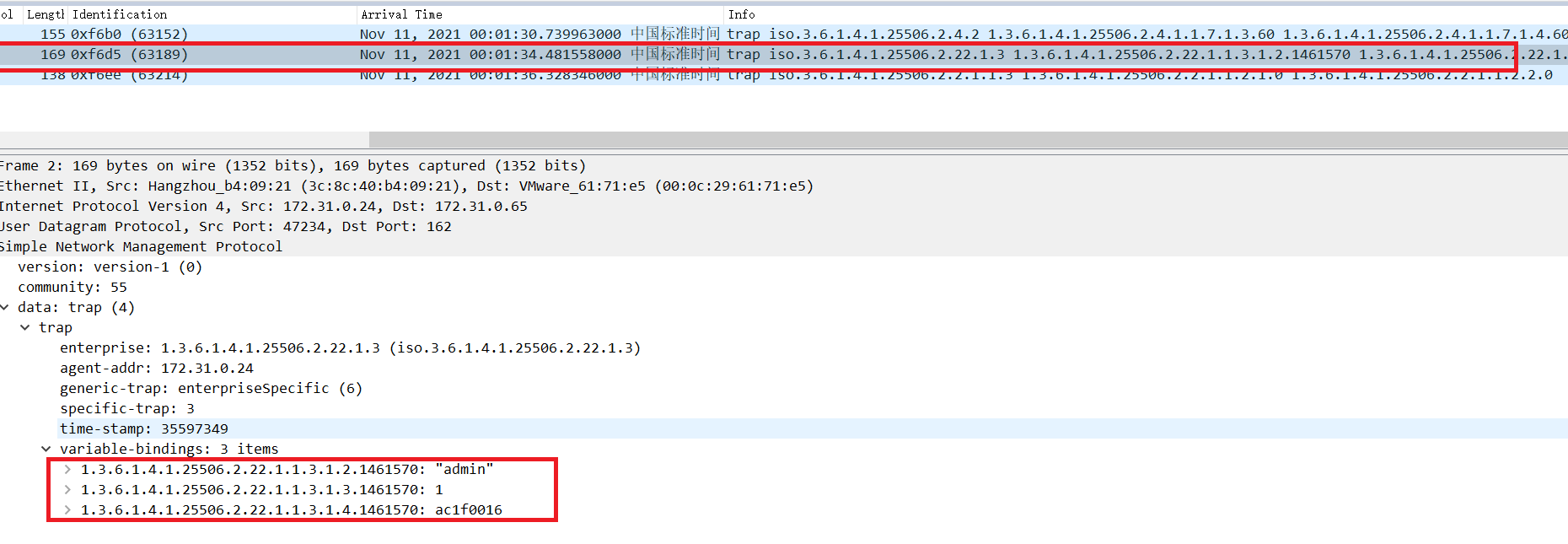
忽略上面的IP地址,只说明现象。
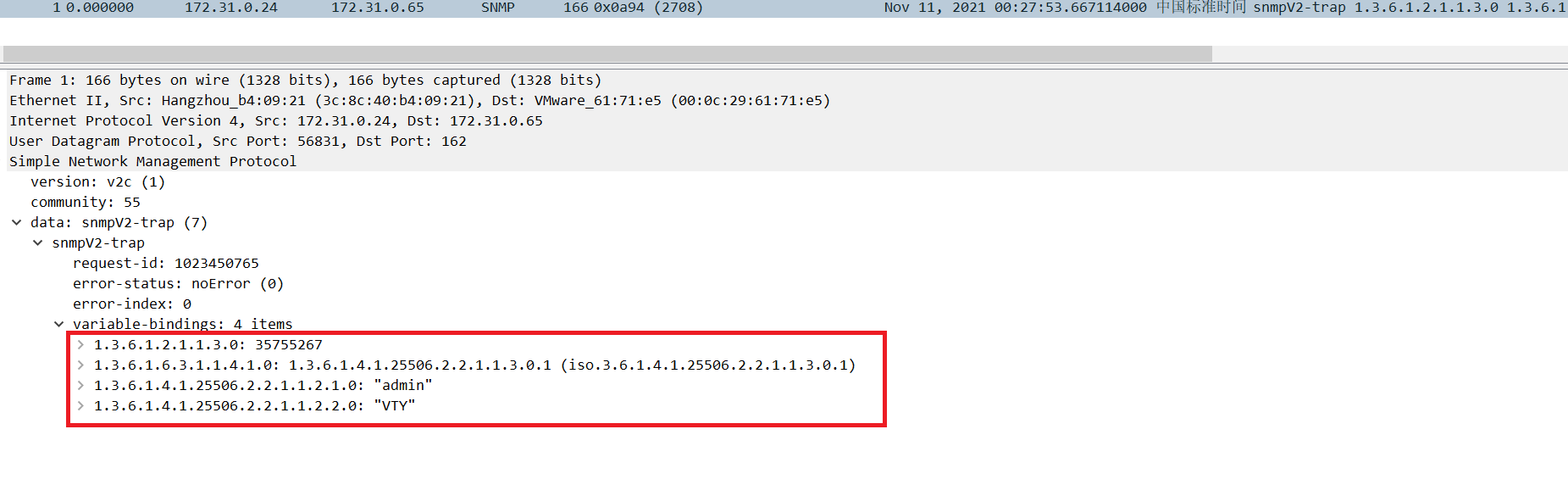
如何查看telnet以后的trap MIB节点呢?
(1)和上面一样debug
<M9006_IRF>%Nov 10 21:18:28:102 2021 M9006_IRF SHELL/5/SHELL_LOGIN: admin logged in from 172.31.0.24.
*Nov 10 21:18:28:103 2021 M9006_IRF SNMP/7/TRAP_PACKET:
hh3cLogIn trap<v2>
send to: 172.31.0.65
Request ID: 1035517468
Error status: 0 Error index: 0
UDP port: 162
Trap successfully sent
*Nov 10 21:18:28:103 2021 M9006_IRF SNMP/7/VBLIST:
sysUpTime.0: 61950118
*Nov 10 21:18:28:103 2021 M9006_IRF SNMP/7/VBLIST:
snmpTrapOID.0: 1.3.6.1.4.1.25506.2.2.1.1.3.0.1
*Nov 10 21:18:28:103 2021 M9006_IRF SNMP/7/VBLIST:
hh3cTerminalUserName.0: admin
*Nov 10 21:18:28:104 2021 M9006_IRF SNMP/7/VBLIST:
hh3cTerminalSource.0: VTY
%Nov 10 21:18:28:104 2021 M9006_IRF SNMP/6/SNMP_NOTIFY: Notification hh3cLogIn(1.3.6.1.4.1.25506.2.2.1.1.3.0.1) with hh3cTerminalUserName(1.3.6.1.4.1.25506.2.2.1.1.2.1.0)=admin;hh3cTerminalSource(1.3.6.1.4.1.25506.2.2.1.1.2.2.0)=VTY.
配置关键点
无
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
