SecPath防火墙攻击防范典型配置
- 0关注
- 1收藏 1564浏览
SecPath防火墙攻击防范典型配置
一、组网需求
SecPath开启攻击防范,对内外网的双向流量进行监控,对攻击进行告警和阻断。
二、组网图
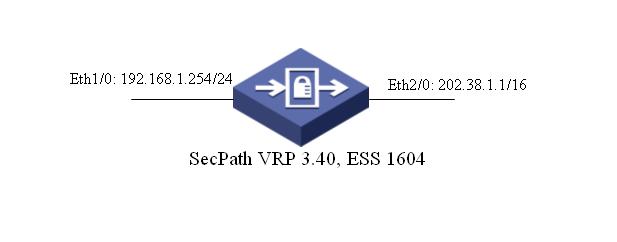
软件版本如下:
SecPath100F:VRP 3.40 ESS 1604;
三、配置步骤
[Quidway]
#
sysname Quidway
#
firewall packet-filter enable
firewall packet-filter default permit
#
undo connection-limit enable
connection-limit default deny
connection-limit default amount upper-limit 50 lower-limit 20
#
firewall statistic system enable
#
radius scheme system
#
domain system
#
local-user admin
password cipher .]@USE=B,53Q=^Q`MAF4<1!!
service-type telnet terminal
level 3
service-type ftp
#
interface Ethernet1/0
ip address 192.168.1.254 255.255.255.0
#
interface Ethernet2/0
ip address 202.38.1.1 255.255.0.0
#
interface NULL0
#
firewall zone local
set priority 100
#
firewall zone trust
add interface Ethernet1/0
set priority 85
#
firewall zone untrust
add interface Ethernet2/0
set priority 5
#
firewall zone DMZ
set priority 50
#
firewall interzone local trust
#
firewall interzone local untrust
#
firewall interzone local DMZ
#
firewall interzone trust untrust
#
firewall interzone trust DMZ
#
firewall interzone DMZ untrust
#
FTP server enable
#
firewall defend ip-spoofing \\防范IP欺骗
firewall defend land \\防范Land攻击
firewall defend smurf \\防范Smurf攻击
firewall defend fraggle \\防范Fraggle攻击
firewall defend winnuke \\防范Winnuke攻击
firewall defend icmp-redirect \\防范ICMP重定向攻击
firewall defend icmp-unreachable \\防范ICMP不可达攻击
firewall defend source-route \\防范源路由攻击
firewall defend route-record \\防范记录路由攻击
firewall defend tracert \\防范Tracert攻击
firewall defend ping-of-death \\防范死亡之Ping攻击
firewall defend tcp-flag \\防范TCP-flag攻击
firewall defend ip-fragment \\防范IP分片攻击
firewall defend large-icmp \\防范超大ICMP包攻击
firewall defend teardrop \\防范teardrop(泪滴)攻击
firewall defend ip-sweep \\防范IP扫描攻击
firewall defend port-scan \\防范端口扫描攻击
firewall defend arp-spoofing \\防范arp欺骗攻击
firewall defend arp-reverse-query \\防范反向arp请求攻击
firewall defend arp-flood \\防范arp洪水攻击
firewall defend frag-flood \\防范分片洪水攻击
firewall defend syn-flood enable \\使能syn-flood攻击防范
firewall defend udp-flood enable \\使能udp-flood攻击防范
firewall defend icmp-flood enable \\使能icmp-flood攻击防范
#
user-interface con 0
user-interface vty 0 4
authentication-mode scheme
#
return
四、配置关键点
1.在全局模式下使用firewall defend xx打开对xx攻击的防范;
2.注意:对于syn-flood、udp-flood和icmp-flood的攻击防范,情况有所不同。除了使能外,还需要进行开启报文统计,详见“SecPath防火墙常见flood攻击防范典型配置”。
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作