组网及说明
无
问题描述
客户分公司要访问总公司的服务器,需要搭建一条IPSEC VPN来实现两端的网络互访,两台设备配置完毕后隧道无法成功建立。
过程分析
1.两台设备都是直接连接公网,没有再经过NAT设备,公网地址互Ping无丢包,并且在公网出口的NAT Outbound已经将感兴趣流Deny掉了,配置检查没问题。
分支配置:
#
ipsec transform-set 1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy RTB 1 isakmp
transform-set 1
security acl 3501
remote-address 12.1.1.1
ike-profile RTB
#
ike identity fqdn RTB
ike logging negotiation enable
#
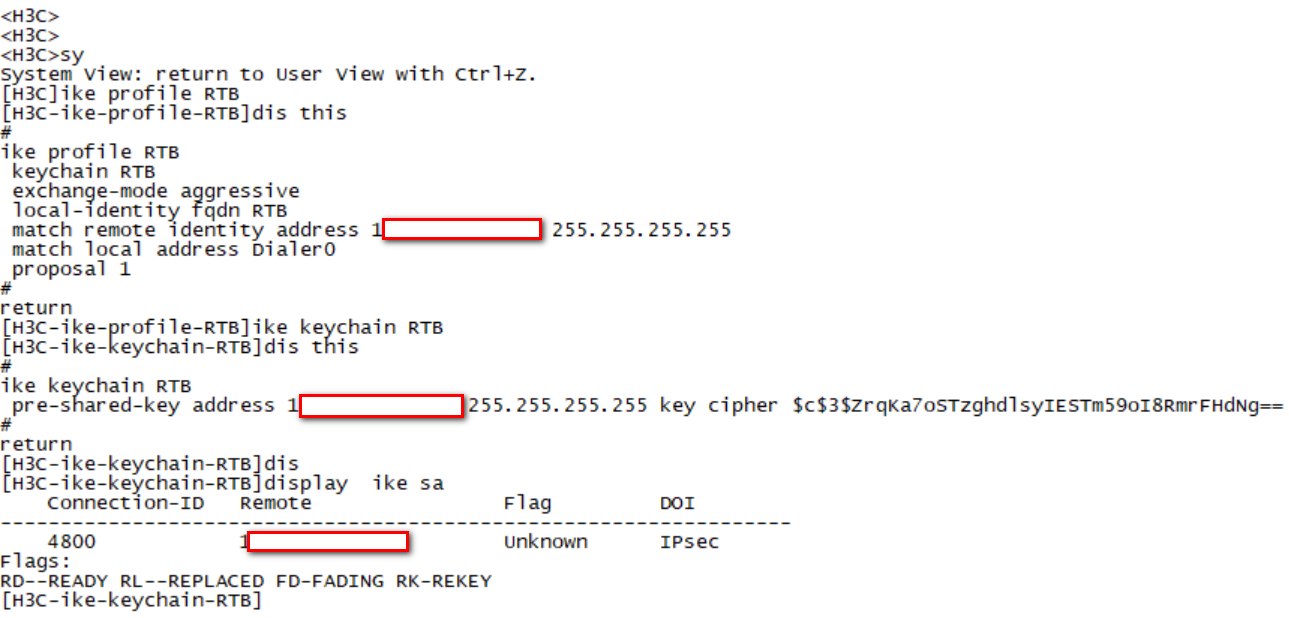
ike profile RTB
keychain RTB
exchange-mode aggressive
local-identity fqdn RTB
match remote identity address 12.1.1.1 255.255.255.255
match local address Dialer0
proposal 1
#
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
#
ike keychain RTB
pre-shared-key address 12.1.1.1 255.255.255.255 key cipher $c$3$ZrqKa7oSTzghdlsyIESTm59oI8RmrFHdNg==
2.查看两端的Ike Sa的状态,Ike Sa是有的,但是状态不正常;两端的Ike Profile及Ike keychain配置正确。
3.两端收集Debug调试信息分析;分支主动触发,分支发出了Ike的第一个报文,在总部侧查看是收到了第一个报文,同时回复了报文;但是从分支的debug来看,没收到第二个报文,一直在重传第一个报文。
分支debug:
*Apr 23 22:51:03:683 2020 H3C IKE/7/PACKET: vrf = 0, local = 11.1.1.1, remote = 12.1.1.1/500
Retransmit phase 1 packet.
*Apr 23 22:51:03:683 2020 H3C IKE/7/PACKET: vrf = 0, local = 11.1.1.1, remote = 12.1.1.1/500
Sending packet to 12.1.1.1 remote port 500, local port 500.
*Apr 23 22:51:03:683 2020 H3C IKE/7/PACKET: vrf = 0, local = 11.1.1.1, remote = 12.1.1.1/500
I-COOKIE: 42e93d3b70952b61
R-COOKIE: 0000000000000000
next payload: SA
version: ISAKMP Version 1.0
exchange mode: Aggressive
flags:
message ID: 0
length: 348
*Apr 23 22:51:03:683 2020 H3C IKE/7/PACKET: vrf = 0, local = 11.1.1.1, remote = 12.1.1.1/500
Sending an IPv4 packet.
总部:
*Apr 24 00:29:34:284 2020 F1060 IKE/7/PACKET: -COntext=1; vrf = 0, local = 12.1.1.1, remote = 11.1.1.1/500
Received packet from 11.1.1.1 source port 500 destination port 500.
*Apr 24 00:29:34:284 2020 F1060 IKE/7/PACKET: -COntext=1; vrf = 0, local = 12.1.1.1, remote = 11.1.1.1/500
I-COOKIE: 531e90853d3ee0ca
R-COOKIE: 0000000000000000
next payload: SA
version: ISAKMP Version 1.0
exchange mode: Aggressive
flags:
message ID: 0
length: 348
*Apr 24 00:29:34:284 2020 F1060 IKE/7/EVENT: -COntext=1; IKE thread 1099351118512 processes a job.
*Apr 24 00:29:34:287 2020 F1060 IKE/7/PACKET: -COntext=1; vrf = 0, local = 12.1.1.1, remote = 11.1.1.1/500
Sending packet to 11.1.1.1 remote port 500, local port 500.
*Apr 24 00:29:34:287 2020 F1060 IKE/7/PACKET: -COntext=1; vrf = 0, local = 12.1.1.1, remote = 11.1.1.1/500
I-COOKIE: 531e90853d3ee0ca
R-COOKIE: c81878907b16b11b
next payload: SA
version: ISAKMP Version 1.0
exchange mode: Aggressive
flags:
message ID: 0
length: 352
*Apr 24 00:29:34:287 2020 F1060 IKE/7/PACKET: -COntext=1; vrf = 0, local = 12.1.1.1, remote = 11.1.1.1/500
Sending an IPv4 packet.
4.通过调试信息分析,怀疑是公网链路或者F100设备有问题。公网地址互Ping是没丢包的,所以公网传输应该没问题。NGFW系列防火墙提供了 WEB界面抓包的方式,直接在F100防火墙抓包查看:
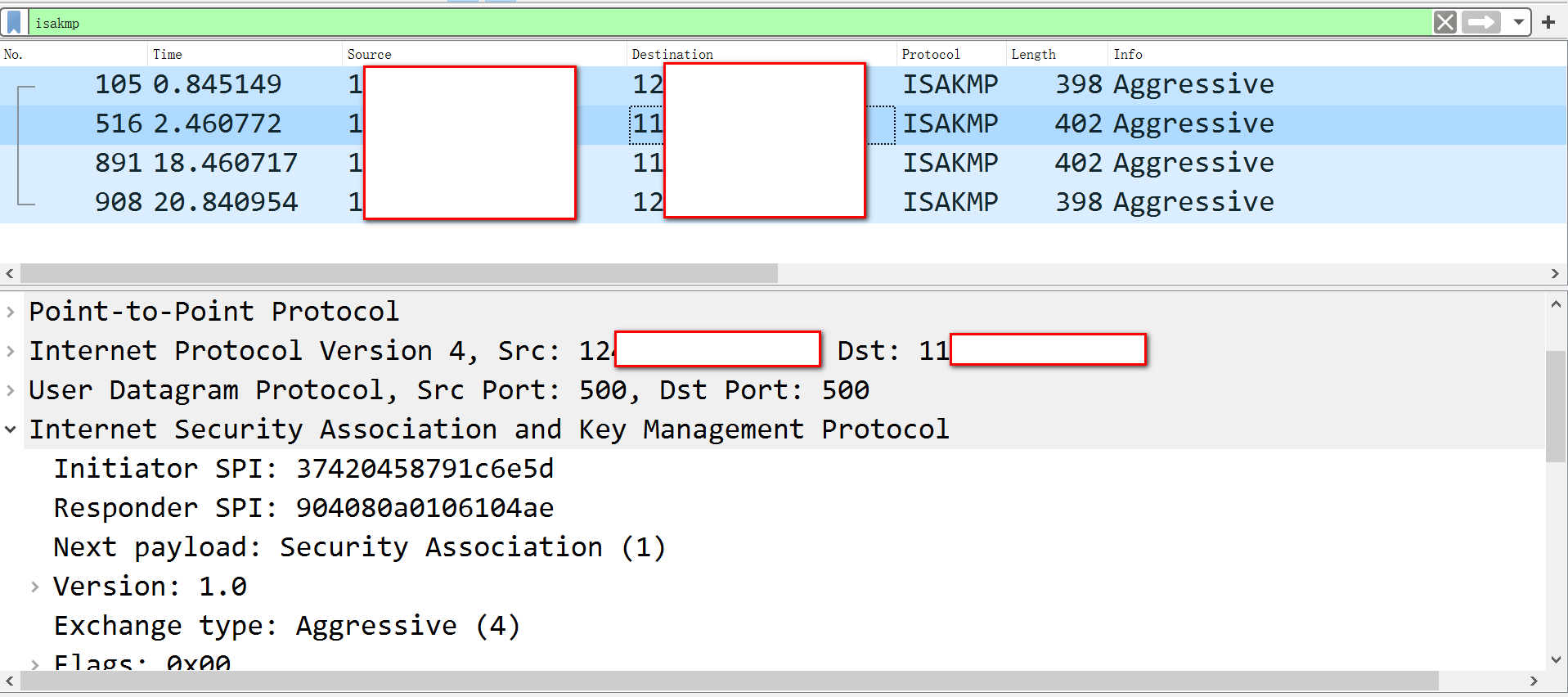
5.结合抓包和Debug调试信息分析,问题是出在F100设备侧,通过查看现场版本是Ess 9524P08的版本,版本太老。
解决方法
和产品线工程师确认,升级官网最新版本(R9536P14)解决。
该案例对您是否有帮助:
您的评价:1
若您有关于案例的建议,请反馈:
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
