Network Topology
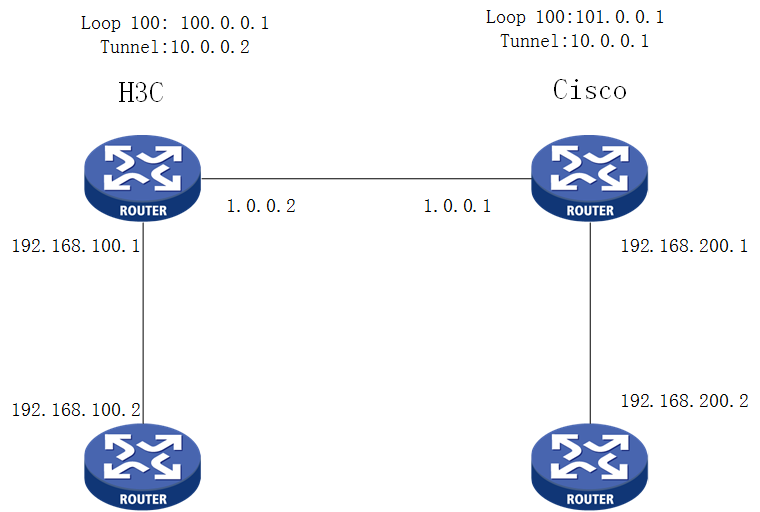
AS
Configuration Steps
H3C
#
interface GigabitEthernet0/0
port link-mode route
description ipsec_test
speed 100
ip address 1.0.0.2 255.255.255.0
nat outbound
ipsec apply policy tunnel
#
interface Tunnel0 mode gre
ip address 10.0.0.2 255.255.255.0
source 1.0.0.2
destination 1.0.0.1
#
ip route-static 101.0.0.0 24 Tunnel0
ip route-static 192.168.200.0 24 Tunnel0
#
acl advanced 3001
rule 5 permit ip source 1.0.0.2 0 destination 1.0.0.1 0
#
ipsec transform-set test
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy tunnel 1 isakmp
transform-set test
security acl 3001
local-address 1.0.0.2
remote-address 1.0.0.1
ike-profile tunnel
#
ike profile tunnel
keychain tunnel
local-identity address 1.0.0.2
match remote identity address 1.0.0.1 255.255.255.0
proposal 1
#
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
sa duration 3600
#
ike keychain tunnel
pre-shared-key address 1.0.0.1 255.255.255.0 key simple 12345678
#
CISCO:
!
crypto isakmp policy 20
encr 3des
hash md5
authentication pre-share
lifetime 3600
crypto isakmp key 12345678 address 1.0.0.2
!
!
crypto ipsec transform-set test esp-3des esp-md5-hmac
mode transport
!
crypto map tunnel 20 ipsec-isakmp
set peer 1.0.0.2
set transform-set test
match address 102
!
interface Tunnel0
ip address 10.0.0.1 255.255.255.0
tunnel source 1.0.0.1
tunnel destination 1.0.0.2
!
interface FastEthernet0/0
ip address 1.0.0.1 255.255.255.0
crypto map tunnel
!
access-list 102 permit ip host 1.0.0.1 host 1.0.0.2
!
!
Key Configuration
ACL:
rule 5 permit ip source 1.0.0.2 0 destination 1.0.0.1 0 (from internet address to remote end)
access-list 102 permit ip host 1.0.0.1 host 1.0.0.2
该案例对您是否有帮助:
您的评价:1
若您有关于案例的建议,请反馈:
No comments
Add Comments:
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
