某局点S5560-54C-EI 终端未通过802.1X未认证,但是可以使用QQ等应用故障排查经验案例
- 0关注
- 0收藏 1313浏览
组网及说明
现场使用S5560-54C-EI交换机作为802.1x认证的接入设备,想要实现只让认证通过的终端可以访问内外网资源。组网大致拓扑图如下:
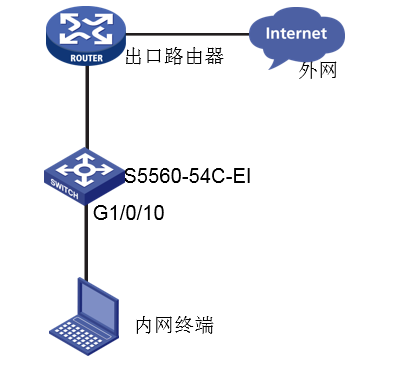
本次涉及设备的型号以及版本:S5560-54C-EI Version 7.1.070, Release 3506P07
问题描述
过程分析
1、首先通过display dot1x interface查看连接认证终端的接口下是否有该用户的认证信息,可以看到全局和接口下都已经使能了802.1x认证,但是接口下并没有认证通过的用户在线,然而该用户却可以使用qq和微信。
Global 802.1X parameters:
802.1X authentication : Enabled
EAP authentication : Enabled
Max-tx period : 30 s
Handshake period : 60 s
Offline detect period : 300 s
Quiet timer : Disabled
Quiet period : 60 s
Supp timeout : 30 s
Server timeout : 100 s
Reauth period : 60 s
Max auth requests : 5
User aging period for Auth-Fail VLAN : 1000 s
User aging period for critical VLAN : 1000 s
User aging period for guest VLAN : 1000 s
EAD assistant function : Enabled
Free IP : 172.10.255.28 255.255.255.255
: 172.10.11.134 255.255.255.255
EAD timeout : 30 min
Domain delimiter : @
Max EAP-TLS-fragment (to-server) : N/A
Online 802.1X wired users : 0
GigabitEthernet1/0/10 is link-up
802.1X authentication : Enabled
Handshake : Enabled
Handshake reply : Disabled
Handshake security : Enabled
Offline detection : Disabled
Unicast trigger : Disabled
Periodic reauth : Enabled
Port role : Authenticator
Authorization mode : Auto
Port access control : Port-based
Multicast trigger : Enabled
Mandatory auth domain : freeradius
Guest VLAN : Not configured
Auth-Fail VLAN : Not configured
Critical VLAN : Not configured
Critical voice VLAN : Disabled
Add Guest VLAN delay : Disabled
Re-auth server-unreachable : Logoff
Max online users : 4294967295
User IP freezing : Disabled
Reauth period : 1800 s
Send Packets Without Tag : Disabled
Max Attempts Fail Number : 0
User aging : Enabled
Server-recovery online-user-sync : Disabled
Auth-Fail EAPOL : Disabled
Critical EAPOL : Disabled
Discard duplicate EAPOL-Start : No
EAPOL packets: Tx 4781, Rx 723
Sent EAP Request/Identity packets : 4416
EAP Request/Challenge packets: 131
EAP Success packets: 85
EAP Failure packets: 149
Received EAPOL Start packets : 196
EAPOL LogOff packets: 143
EAP Response/Identity packets : 267
EAP Response/Challenge packets: 117
Error packets: 0
Online 802.1X users: 0
2、检查现场的配置,发现除了常见的802.1X的配置外,设备还配置了ead快速部署。
dot1x ead-assistant enable
dot1x ead-assistant free-ip 172.10.255.28 255.255.255.255
dot1x ead-assistant free-ip 172.10.11.134 255.255.255.255
开启了ead快速部署,对于没认证通过的用户,底层会下发三条规则,http(tcp 80端口)、https(tcp 443端口)重定向到cpu规则,其余IP报文丢弃规则。此时需要配置dot1x ead-assistant url,该命令是配置用户http或https访问的重定向url,否则报文会进行软转。下发的acl规则信息可以进入probe视图后通过如下命令收集:
debug qacl show 1 0 verbose 0
debug qacl show 1 0 verbose 20
debug qacl show 1 0 verbose 40
debug qacl show 1 0 verbose 60
............................................. (每20 一个步长,一直收集到没有显示内容为止)
Acl-Type EAD Auth-Rule, Stage IFP, SinglePort, Installed, Active
Prio Mjr/Sub 516/10, Group 7 [7], Slice/Idx 8/5, Entry 810, Double: 2053/2309
Rule Match --------
Ports: 0x0000000000040000; 0x3cffffffffffffff
L4 Dst Port: 80, 0xffff
Actions --------
CAR cir 0x80, cbs 0x800, pir 0x80, pbs 0x800, mode srTCM color blind
Account mode packets, green and non-green
Redirect and copy to cpu
Copy_to_cpu : Yes
Change CPU pkt COS 0
Red Deny
Red_Copy_to_cpu : No
Yel Deny
Yel_Copy_to_cpu : No
Color Independent 1
Accounting: Hi 284, LO 0
========
Acl-Type EAD Auth-Rule, Stage IFP, SinglePort, Installed, Active
Prio Mjr/Sub 516/10, Group 7 [7], Slice/Idx 8/6, Entry 811, Double: 2054/2310
Rule Match --------
Ports: 0x0000000000040000; 0x3cffffffffffffff
L4 Dst Port: 443, 0xffff
Actions --------
CAR cir 0x80, cbs 0x800, pir 0x80, pbs 0x800, mode srTCM color blind
Account mode packets, green and non-green
Redirect and copy to cpu
Copy_to_cpu : Yes
Change CPU pkt COS 0
Red Deny
Red_Copy_to_cpu : No
Yel Deny
Yel_Copy_to_cpu : No
Color Independent 1
Accounting: Hi 10016, LO 0
[HFJD-F20RDJ1-BG-H5560-1-probe]debug qacl show slot 1 chip 0 verbose 80
========
Acl-Type EAD Deny, Stage IFP, SinglePort, Installed, Active
Prio Mjr/Sub 516/9, Group 7 [7], Slice/Idx 8/11, Entry 812, Double: 2059/2315
Rule Match --------
Ports: 0x0000000000040000; 0x3cffffffffffffff
IP Type: IPv4 and IPv6 packets
Actions --------
Deny
配置重定向url的话需要配置对https报文进行重定向的内部侦听端口号http-redirect https-port port-number,设备才会对https报文进行重定向。
3、现场按照如上排查过程配置了重定向的url以及https重定向的内部侦听端口号后发现问题依旧存在。于是进一步排查下发的acl规则,看是否存在其它acl的干扰导致了该异常现象。发现连接终端的接口所关联的vlan虚接口下发了包过滤的acl。检查对应vlan虚接口下的配置发现调用了包过滤,并且配置了permit规则。
interface Vlan-interface2003
description 2003
ip address 172.10.11.190 255.255.255.192
packet-filter name LeSuo-bingdu_control inbound
packet-filter name LeSuo-bingdu_control outbound
interface GigabitEthernet1/0/10
port link-mode bridge
description W10-to-desk-22-A-08
port access vlan 2003
acl number 3000 name LeSuo-bingdu_control
rule 10 deny udp destination-port eq 445
rule 15 deny tcp destination-port eq 445
rule 20 permit tcp
rule 25 permit udp
查看ead和包过滤规则的优先级,包过滤规则的优先级更高,让现场去掉这个包过滤或者修改一下acl,删除permit的规则后问题解决。
Pri 11, Group 7,usedEntries 49,mode Double, physlice 8/9/
=========================================
acl type usedEntries[49]
=========================================
[56 ]EAD Free-IP 2
[58 ]EAD Middle 3
[60 ]EAD Auth-Rule 4
[61 ]EAD Deny 1
[35 ]Portal Redirect 2
[36 ]Portal Deny 1
[29 ]PortBind Bind 35
[28 ]PortBind Default 1
======================================
------------------------------------------------------
Pri 13, Group 4,usedEntries 22,mode Single, physlice 11/
=========================================
acl type usedEntries[22]
=========================================
[98 ]PktFilter IP on PORT 6
[99 ]PktFilter IP on VRF 16
解决方法
1、设备开启了ead快速部署,需要配置用户http以及https重定向的url;
2、配置https重定向报文的监听端口;
3、检查是否有优先级更高的acl规则,比如接口下是否配置了包过滤等。
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
