1、双方使用野蛮模式建立IPsec隧道,保护L2TP数据流;
2、双方使用预共享密钥的方式建立IPsec;
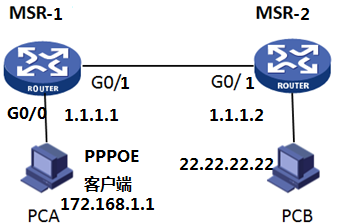
3、MSR-1(1.1.1.1)作为LAC,MSR-2(1.1.1.2)作为LNS
4、LAC采用电脑ppp客户端报文去促发建立到LNS的L2TP隧道。
MSR-1(MSR930)和MSR-2(MSR930)之间路由可达,PCA使用MSR930-1上的G0/0连接PPPOE客户端,PCB由MSR930-2上的loopback 0口代替。
MSR930-1配置:
#配置出接口地址:
interface GigabitEthernet0/1
port link-mode route
ip address 1.1.1.1 255.255.255.0
#使用G0/0接口连接内网PPPOE客户端电脑
interface GigabitEthernet0/0
port link-mode route
pppoe-server bind Virtual-Template 1
ip address 172.16.1.2 255.255.255.0
# 配置ACL 3000,定义要保护L2TP的数据流。
rule 0 permit udp source-port eq 1701 destination-port eq 1701
# 创建IPsec安全提议qq
ipsec transform-set qq
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
esp encryption-algorithm des
#配置ike peer
ike peer qq
exchange-mode aggressive
pre-shared-key cipher qq
remote-name lns
remote-address 1.1.1.2
local-name lac
#配置标识本端身份
ike local-name lac
#配置IPSEC策略调用了IKE IPSEC提议、安全ACL
ipsec policy qq 1 isakmp
security acl 3000
ike-peer qq
transform-set qq
#接口下调用IPSEC策略
interface GigabitEthernet0/1
port link-mode route
ip address 1.1.1.1 255.255.255.0
ipsec policy qq
#配置L2TP
l2tp enable
l2tp-group 1
undo tunnel authentication
start l2tp ip 1.1.1.2 fullusername qq
#创建虚拟PPP接口Virtual-PPP 1,并配置PPP验证方式为chap
ppp authentication-mode chap
# 创建本地用户,配置用户名、密码及服务类型。
local-user qq
password cipher qq
service-type ppp
MSR930-2配置:
#配置出接口地址:
interface GigabitEthernet0/1
port link-mode route
ip address 1.1.1.2 255.255.255.0
#创建loopback 0口,模拟内网的终端设备
interface LoopBack0
ip address 22.22.22.22 255.255.255.25
#配置ike peer
ike peer qq
exchange-mode aggressive
pre-shared-key cipher qq
remote-name lac
local-name lns
# 创建IPsec安全提议tran1
ipsec transform-set qq
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
esp encryption-algorithm des
#配置IPSEC策略模版
ipsec policy-template qq 1
ike-peer qq
transform-set qq
#配置IPSEC策略,调用策略模版
ipsec policy qqq 1 isakmp template qq
#物理接口下调用IPSEC策略
interface GigabitEthernet0/1
port link-mode route
ip address 1.1.1.2 255.255.255.0
ipsec policy qqq
#配置标识本端身份
ike local-name lns
# 创建本地用户,配置用户名、密码及服务类型。
local-user qq
password cipher qq
service-type ppp
# 配置虚拟模板接口Virtual-Template1的相关信息。
interface Virtual-Template0
ppp authentication-mode chap
ppp chap user qq
remote address pool 1
ip address 33.33.33.1 255.255.255.0
# 对用户采用本地验证。
domain system
authentication ppp local
ip pool 1 33.33.33.10 33.33.33.33
#配置L2TP,
l2tp enable
l2tp-group 1
undo tunnel authentication
allow l2tp virtual-template 0
结果测试:
LNS端
*down: administratively down
(s): spoofing (l): loopback
Interface Physical Protocol IP Address Description
Aux0 up up -- --
Cellular0/0 down down -- --
GE0/0 down down -- --
GE0/1 up up 1.1.1.2 --
Loop0 up up(s) 22.22.22.22 --
VT0 up up(s) 33.33.33.1 --
Routing Tables: Public
Destinations : 10 Routes : 10
Destination/Mask Proto Pre Cost NextHop Interface
1.1.1.0/24 Direct 0 0 1.1.1.2 GE0/1
1.1.1.2/32 Direct 0 0 127.0.0.1 InLoop0
4.4.4.0/24 Static 60 0 33.33.33.1 VT0
22.22.22.22/32 Direct 0 0 127.0.0.1 InLoop0
33.33.33.0/24 Direct 0 0 33.33.33.1 VT0
33.33.33.1/32 Direct 0 0 127.0.0.1 InLoop0
33.33.33.14/32 Direct 0 0 33.33.33.14 VT0(终端客户端虚拟网卡获得ip)
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
PING 33.33.33.14: 56 data bytes, press CTRL_C to break
Reply from 33.33.33.14: bytes=56 Sequence=0 ttl=128 time=2 ms
Reply from 33.33.33.14: bytes=56 Sequence=1 ttl=128 time=2 ms
Reply from 33.33.33.14: bytes=56 Sequence=2 ttl=128 time=2 ms
Reply from 33.33.33.14: bytes=56 Sequence=3 ttl=128 time=2 ms
Reply from 33.33.33.14: bytes=56 Sequence=4 ttl=128 time=2 ms
--- 33.33.33.14 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 2/2/2 ms
Total tunnel = 1
LocalTID RemoteTID RemoteAddress Port Sessions RemoteName
1 1 1.1.1.1 1701 1 H3C
Total session = 1
LocalSID RemoteSID LocalTID
18887 2577 1
===============================
Interface: GigabitEthernet0/1
path MTU: 1500
===============================
-----------------------------
IPsec policy name: "qq"
sequence number: 1
acl version: None
mode: template
-----------------------------
PFS: N, DH group: none
inside VRF:
tunnel:
local address: 1.1.1.2
remote address: 1.1.1.1
flow:
sour addr: 0.0.0.0/0.0.0.0 port: 1701 protocol: UDP
dest addr: 0.0.0.0/0.0.0.0 port: 1701 protocol: UDP
[inbound ESP SAs]
spi: 0xB4D605EC(3033925100)
transform: ESP-ENCRYPT-DES ESP-AUTH-MD5
in use setting: Tunnel
connection id: 3
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843075/2835
anti-replay detection: Enabled
anti-replay window size(counter based): 32
udp encapsulation used for nat traversal: N
[outbound ESP SAs]
spi: 0xF8326F08(4164054792)
transform: ESP-ENCRYPT-DES ESP-AUTH-MD5
in use setting: Tunnel
connection id: 4
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843134/2835
anti-replay detection: Enabled
anti-replay window size(counter based): 32
udp encapsulation used for nat traversal: N
total phase-1 SAs: 1
connection-id peer flag phase doi
----------------------------------------------------------------
5 1.1.1.1 RD 1 IPSEC
6 1.1.1.1 RD 2 IPSEC
flag meaning
RD--READY ST--STAYALIVE RL--REPLACED FD--FADING TO--TIMEOUT RK—REKEY
1 电脑的网关路由最终要指向LAC(msr)
2 LAC 和LNS的虚拟接口VT的验证方式要一样,比如本实验都是chap,两边配置的验证的用户名和密码要一致,
3 LAC和LNS的外网地址需要路由可达,这个方式不需要写去对方的目的的路由,因为是有客户端ppp报文去促发L2TP隧道的,
4 ipsec策略路由应用在物理接口上,保护L2TP隧道的数据。
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
