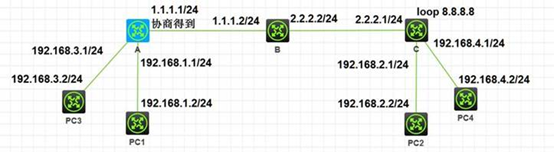
组网及说明
需求:两个MSR36之间同时通过主模式和野蛮模式建立2条ipsec vpn隧道,公网线路只有一条,保护不同的数据流。
配置步骤
[A]设备的基本配置
interface GigabitEthernet0/0
port link-mode route
combo enable copper
ip address dhcp-alloc
ipsec apply policy policy1
#
ip route-static 192.168.2.0 24 1.1.1.2
ip route-static 192.168.4.0 24 1.1.1.2
#
acl advanced 3000
rule 0 permit ip source 192.168.1.0 0.0.0.255 destination 192.168.2.0 0.0.0.255
#
acl advanced 3001
rule 0 permit ip source 192.168.3.0 0.0.0.255 destination 192.168.4.0 0.0.0.255
#
ipsec transform-set tran1
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec transform-set tran2
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec policy policy1 1 isakmp
transform-set tran1
security acl 3000
remote-address 2.2.2.1
ike-profile profile1
#
ipsec policy policy1 2 isakmp
transform-set tran2
security acl 3001
remote-address 8.8.8.8
ike-profile profile2
#
ike identity fqdn rta
#
ike profile profile1
keychain keychain1
exchange-mode aggressive
match remote identity fqdn rtb
proposal 1
#
ike profile profile2
keychain keychain2
local-identity address 1.1.1.1
match remote identity address 8.8.8.8 255.255.255.255
proposal 2
#
ike proposal 1
authentication-algorithm md5
#
ike proposal 2
encryption-algorithm 3des-cbc
authentication-algorithm md5
#
ike keychain keychain1
pre-shared-key address 2.2.2.1 255.255.255.0 key cipher $c$3$LPfGmJNHUhMEAwGOO6QmJOTYANy7SA==
#
ike keychain keychain2
pre-shared-key address 8.8.8.8 255.255.255.255 key cipher $c$3$75RKWL/+vR9sbfeKRVzSvagndMMkc/M/GQ==
C设备的基本配置
interface LoopBack0
ip address 8.8.8.8 255.255.255.255
#
interface GigabitEthernet0/0
port link-mode route
combo enable copper
ip address 2.2.2.1 255.255.255.0
ipsec apply policy policy1
ip route-static 192.168.1.0 24 2.2.2.2
ip route-static 192.168.3.0 24 2.2.2.2
#
acl advanced 3000
rule 0 permit ip source 192.168.2.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
#
acl advanced 3001
rule 0 permit ip source 192.168.4.0 0.0.0.255 destination 192.168.3.0 0.0.0.255
#
ipsec transform-set tran1
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec transform-set tran2
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec policy-template template1 1
transform-set tran1
security acl 3000
ike-profile profile1
#
ipsec policy policy1 1 isakmp template template1
#
ipsec policy policy1 2 isakmp
transform-set tran2
security acl 3001
local-address 8.8.8.8
remote-address 1.1.1.1
ike-profile profile2
#
ike identity fqdn rtb
#
ike profile profile1
keychain keychain1
exchange-mode aggressive
match remote identity fqdn rta
proposal 1
#
ike profile profile2
keychain keychain2
local-identity address 8.8.8.8
match remote identity address 1.1.1.1 255.255.255.0
proposal 2
#
ike proposal 1
authentication-algorithm md5
#
ike proposal 2
encryption-algorithm 3des-cbc
authentication-algorithm md5
#
ike keychain keychain1
pre-shared-key hostname rta key cipher $c$3$pwVKjfLPeJTguQGt933ztIxPbum89Q==
#
ike keychain keychain2
pre-shared-key address 1.1.1.1 255.255.255.0 key cipher $c$3$JdQsVUYxTEcCEtw2B4pXe/RdSBESdo81vw==
[PC1]ping 192.168.2.2
Ping 192.168.2.2 (192.168.2.2): 56 data bytes, press CTRL_C to break
56 bytes from 192.168.2.2: icmp_seq=0 ttl=253 time=3.000 ms
56 bytes from 192.168.2.2: icmp_seq=1 ttl=253 time=4.000 ms
56 bytes from 192.168.2.2: icmp_seq=2 ttl=253 time=2.000 ms
56 bytes from 192.168.2.2: icmp_seq=3 ttl=253 time=2.000 ms
56 bytes from 192.168.2.2: icmp_seq=4 ttl=253 time=1.000 ms
[PC3]ping 192.168.4.2
Ping 192.168.4.2 (192.168.4.2): 56 data bytes, press CTRL_C to break
56 bytes from 192.168.4.2: icmp_seq=0 ttl=253 time=7.000 ms
56 bytes from 192.168.4.2: icmp_seq=1 ttl=253 time=2.000 ms
56 bytes from 192.168.4.2: icmp_seq=2 ttl=253 time=2.000 ms
56 bytes from 192.168.4.2: icmp_seq=3 ttl=253 time=2.000 ms
56 bytes from 192.168.4.2: icmp_seq=4 ttl=253 time=2.000 ms
<A>dis ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
3 8.8.8.8 RD IPsec
4 2.2.2.1 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
<A>dis ipsec sa
-------------------------------
Interface: GigabitEthernet0/0
-------------------------------
-----------------------------
IPsec policy: policy1
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1428
Tunnel:
local address: 1.1.1.1
remote address: 2.2.2.1
Flow:
sour addr: 192.168.1.0/255.255.255.0 port: 0 protocol: ip
dest addr: 192.168.2.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 1851293844 (0x6e588094)
Connection ID: 12884901889
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/3586
Max received sequence-number: 4
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 706730433 (0x2a1fd9c1)
Connection ID: 12884901888
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/3586
Max sent sequence-number: 4
UDP encapsulation used for NAT traversal: N
Status: Active
-----------------------------
IPsec policy: policy1
Sequence number: 2
Mode: ISAKMP
-----------------------------
Tunnel id: 1
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1428
Tunnel:
local address: 1.1.1.1
remote address: 8.8.8.8
Flow:
sour addr: 192.168.3.0/255.255.255.0 port: 0 protocol: ip
dest addr: 192.168.4.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 4132429910 (0xf64fe056)
Connection ID: 12884901891
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/3478
Max received sequence-number: 4
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 645568134 (0x267a9686)
Connection ID: 55834574850
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/3478
Max sent sequence-number: 4
UDP encapsulation used for NAT traversal: N
Status: Active
<C>display ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
3 1.1.1.1 RD IPsec
4 1.1.1.1 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
<C>display ipsec sa
-------------------------------
Interface: GigabitEthernet0/0
-------------------------------
-----------------------------
IPsec policy: policy1
Sequence number: 1
Mode: Template
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1428
Tunnel:
local address: 2.2.2.1
remote address: 1.1.1.1
Flow:
sour addr: 192.168.2.0/255.255.255.0 port: 0 protocol: ip
dest addr: 192.168.1.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 706730433 (0x2a1fd9c1)
Connection ID: 12884901889
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/3592
Max received sequence-number: 4
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 1851293844 (0x6e588094)
Connection ID: 12884901888
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/3592
Max sent sequence-number: 4
UDP encapsulation used for NAT traversal: N
Status: Active
-----------------------------
IPsec policy: policy1
Sequence number: 2
Mode: ISAKMP
-----------------------------
Tunnel id: 1
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1428
Tunnel:
local address: 8.8.8.8
remote address: 1.1.1.1
Flow:
sour addr: 192.168.4.0/255.255.255.0 port: 0 protocol: ip
dest addr: 192.168.3.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 645568134 (0x267a9686)
Connection ID: 12884901891
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/3484
Max received sequence-number: 4
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 4132429910 (0xf64fe056)
Connection ID: 12884901890
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/3484
Max sent sequence-number: 4
UDP encapsulation used for NAT traversal: N
Status: Active
配置关键点
无