问题描述:
A防火墙配置 IPSec
#匹配兴趣流
acl advanced name IPsec_shanghai_IPv4_1
rule 0 permit ip source 100.86.226.0 0.0.0.255 destination 100.86.10.0 0.0.0.255
# 创建ike密钥
ike keychain shanghai_IPv4_1
match local address GigabitEthernet1/0/7
pre-shared-key address 【B公网IP】 255.255.255.128 key simple qwer
# 创建ike-id
ike identity address 【A公网IP】
# ike proposal 安全提议
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
# 创建ike profile描述
ike profile shanghai_IPv4_1
keychain shanghai_IPv4_1
local-identity address 【A公网IP】
match remote identity address 【B公网IP】 255.255.255.128
match local address GigabitEthernet1/0/7
proposal 1
# 创建IPSec安全提议加密算法/认证算法
ipsec transform-set shanghai_IPv4_1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
pfs dh-group1
#配置IPSec策略
ipsec policy shanghai 1 isakmp
transform-set shanghai_IPv4_1
security acl name IPsec_shanghai_IPv4_1
local-address 【A公网IP】
remote-address 【B公网IP】
ike-profile shanghai_IPv4_1
sa trigger-mode auto
#在端口上运行ipsec策略
interface GigabitEthernet1/0/7
ipsec apply policy shanghai
---------------------
<firewall>dis acl all
Basic IPv4 ACL 2000, 1 rule,
ACL's step is 5
rule 0 permit
Advanced IPv4 ACL 3000, 1 rule,
ACL's step is 5
rule 0 permit ip (12833937 times matched)
Advanced IPv4 ACL named IPsec_shanghai_IPv4_1, 1 rule,
ACL's step is 5
rule 0 permit ip source 100.86.226.0 0.0.0.255 destination 100.86.10.0 0.0.0.255
<firewall>dis ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
10 【B公网IP】 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
<firewall>display ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/7
-------------------------------
-----------------------------
IPsec policy: shanghai
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy: dh-group1
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1444
Tunnel:
local address: 【A公网IP】
remote address: 【B公网IP】
Flow:
sour addr: 100.86.226.0/255.255.255.0 port: 0 protocol: ip
dest addr: 100.86.10.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 1523471462 (0x5ace5466)
Connection ID: 1095216660480
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/787
Max received sequence-number: 0
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 1786696126 (0x6a7ed1be)
Connection ID: 4342211936257
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/787
Max sent sequence-number: 0
UDP encapsulation used for NAT traversal: N
Status: Active
-----------------------------
IPsec policy: shanghai
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy: dh-group1
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1444
Tunnel:
local address: 【A公网IP】
remote address: 【B公网IP】
Flow:
sour addr: 100.86.226.0/255.255.255.0 port: 0 protocol: ip
dest addr: 100.86.10.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 3519410599 (0xd1c5f1a7)
Connection ID: 38654705666
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/3488
Max received sequence-number: 0
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 2590343634 (0x9a6581d2)
Connection ID: 1730871820291
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/3488
Max sent sequence-number: 0
UDP encapsulation used for NAT traversal: N
Status: Active
B防火墙配置 IPSec
#匹配兴趣流
acl advanced name IPsec_wuhu_IPv4_1
rule 0 permit ip source 100.86.10.0 0.0.0.255 destination 100.86.226.0 0.0.0.255
# 创建ike密钥
ike keychain wuhu_IPv4_1
match local address GigabitEthernet1/0/6
pre-shared-key address 【A公网IP】 255.255.255.252 key simple qwer
#创建ike-id
ike identity address 【B公网IP】
# ike proposal 安全提议
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
# 创建ike profile描述
ike profile wuhu_IPv4_1
keychain wuhu_IPv4_1
local-identity address 【B公网IP】
match remote identity address 【A公网IP】 255.255.255.252
match local address GigabitEthernet1/0/6
proposal 1
# 创建IPSec安全提议加密算法/认证算法
ipsec transform-set wuhu_IPv4_1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
pfs dh-group1
#配置IPSec策略
ipsec policy wuhu 1 isakmp
transform-set wuhu_IPv4_1
security acl name IPsec_wuhu_IPv4_1
local-address 【B公网IP】
remote-address 【A公网IP】
ike-profile wuhu_IPv4_1
sa trigger-mode auto
#在端口上运行ipsec策略
interface g1/0/6
ipsec apply policy wuhu
--------------------------------------
<firewall>dis acl all
Basic IPv4 ACL 2000, 1 rule,
ACL's step is 5
rule 0 permit
Advanced IPv4 ACL 3000, 2 rules,
ACL's step is 5
rule 0 permit ip (115 times matched)
rule 5 permit ip source 100.86.10.0 0.0.0.255
Advanced IPv4 ACL named IPsec_wuhu_IPv4_1, 1 rule,
ACL's step is 5
rule 0 permit ip source 100.86.10.0 0.0.0.255 destination 100.86.226.0 0.0.0.255
<firewall>dis ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
30 【A公网IP】 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
<firewall>display ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/6
-------------------------------
-----------------------------
IPsec policy: wuhu
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy: dh-group1
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1444
Tunnel:
local address: 【B公网IP】
remote address: 【A公网IP】
Flow:
sour addr: 100.86.10.0/255.255.255.0 port: 0 protocol: ip
dest addr: 100.86.226.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 1786696126 (0x6a7ed1be)
Connection ID: 1249835483137
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/733
Max received sequence-number: 0
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 1523471462 (0x5ace5466)
Connection ID: 3431678869504
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/733
Max sent sequence-number: 0
UDP encapsulation used for NAT traversal: N
Status: Active
-----------------------------
IPsec policy: wuhu
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy: dh-group1
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1444
Tunnel:
local address: 【B公网IP】
remote address: 【A公网IP】
Flow:
sour addr: 100.86.10.0/255.255.255.0 port: 0 protocol: ip
dest addr: 100.86.226.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 2590343634 (0x9a6581d2)
Connection ID: 1181116006403
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/3434
Max received sequence-number: 0
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 3519410599 (0xd1c5f1a7)
Connection ID: 571230650370
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/3434
Max sent sequence-number: 0
UDP encapsulation used for NAT traversal: N
Status: Active


- 2022-01-07提问
- 举报
-
(0)
最佳答案

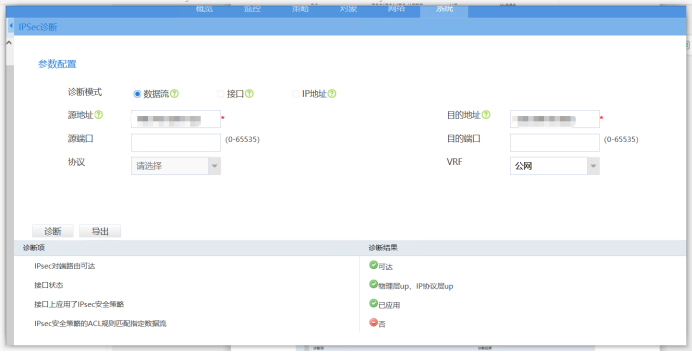
公网接口内网兴趣流地址做了deny了么,就是就不走nat,要加个acl
- 2022-01-07回答
- 评论(12)
- 举报
-
(0)
具体是什么样的?
你ip上网不是公网接口做了个natoutbound ,这个要在permit any 前面加一条,deny 本端地址,对端地址,和你的感兴趣流一样,为的是让ipsec流量走nat出去了
acl advanced 3888 rule 0 deny ip source 100.86.226.0 0.0.0.255 destination 100.86.10.0 0.0.0.255 nat outbound 3888 是这样吗?
另一个防火墙的出口也是,deny是反过来,和感兴趣流一样
interface GigabitEthernet1/0/7 port link-mode route bandwidth 100000 ip address 公网IP 255.255.255.252 nat outbound 3888 ipsec apply policy shanghai gateway ****
[firewall]display acl all Basic IPv4 ACL 2000, 1 rule, ACL's step is 5 rule 0 permit Advanced IPv4 ACL 3000, 1 rule, ACL's step is 5 rule 0 permit ip (12833937 times matched) Advanced IPv4 ACL 3888, 1 rule, ACL's step is 5 rule 0 permit ip (48348 times matched) Advanced IPv4 ACL named IPsec_shanghai_IPv4_1, 1 rule, ACL's step is 5 rule 0 permit ip source 100.86.226.0 0.0.0.255 destination 100.86.10.0 0.0.0.255
还是不行
我手机不好打那么多, acl ad 3888 rule 10 deny ip sou 本地私网 de 对端私网 rule 100 permit any
A端 # acl advanced 3888 rule 10 deny ip source 100.86.226.0 0.0.0.255 destination 100.86.10.0 0.0.0.255 rule 100 permit ip # B端 # acl advanced 3888 rule 10 deny ip source 100.86.10.0 0.0.0.255 destination 100.86.226.0 0.0.0.255 rule 100 permit ip # 大佬,这样正确吗?


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明



A端 # acl advanced 3888 rule 10 deny ip source 100.86.226.0 0.0.0.255 destination 100.86.10.0 0.0.0.255 rule 100 permit ip # B端 # acl advanced 3888 rule 10 deny ip source 100.86.10.0 0.0.0.255 destination 100.86.226.0 0.0.0.255 rule 100 permit ip # 大佬,这样正确吗?