l2tp over ipsec 5G无线组网,同时只有一个分支l2tp隧道能正常建立
- 0关注
- 0收藏,1573浏览
问题描述:
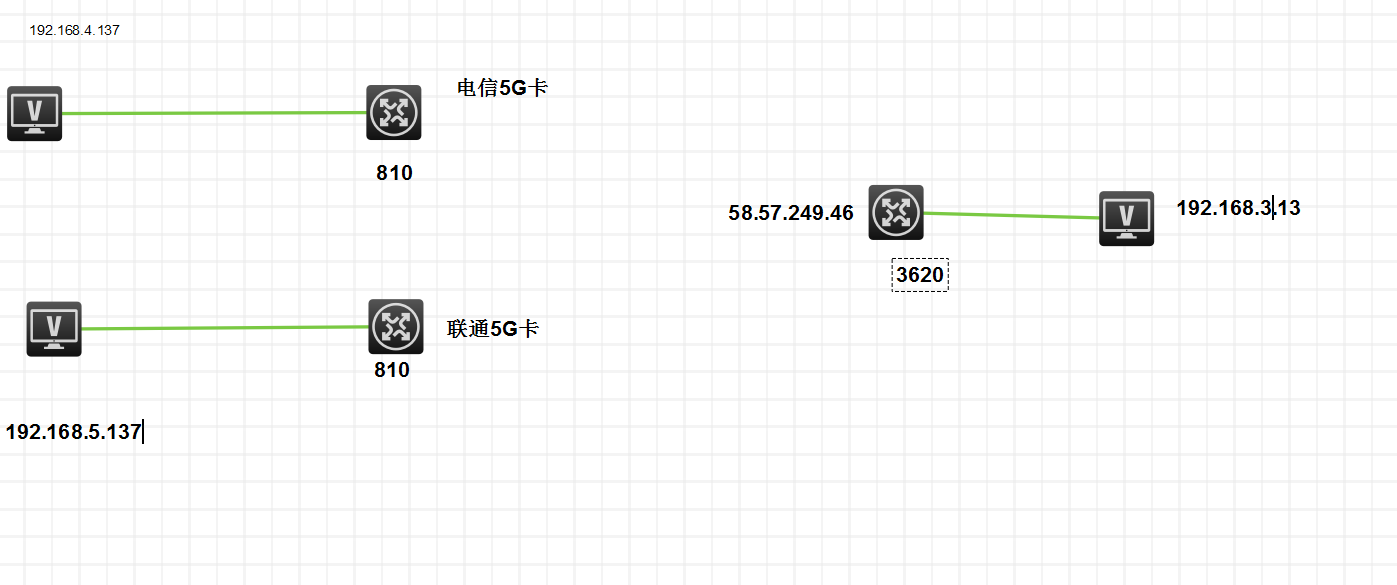
如示意图,l2tp over ipsec 组网。2个 msr810 是分部,插得运营商的流量卡,做l2tp客户端,msr3620是总部路由器,接的电信专线的公网地址,用dis ike sa命令查看ipsec通道两个分部和总部建立正常,但是同时只有一个客户端能和总部建立成功l2tp隧道,只有其中一个分部的时正常,只要两个分部个同时接入,其中一个就必定l2tp隧道不能建立。
分部的debugging信息
<fenbu1>*Jan 1 03:46:38:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Message-Type AVP:
80 08 00 00 00 00 00 04
*Jan 1 03:46:38:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Assigned-Tunnel-ID AVP:
80 08 00 00 00 09 c5 47
*Jan 1 03:46:38:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Result-Code AVP:
80 08 00 00 00 01 00 01
*Jan 1 03:46:39:204 2011 fenbu1 L2TPV2/7/EVENT:
TunnelID=45432: Delay-Cleanup timer expired and deleted the local tunnel.
*Jan 1 03:46:41:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Message-Type AVP:
80 08 00 00 00 00 00 01
*Jan 1 03:46:41:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Protocol-Version AVP:
80 08 00 00 00 02 01 00
*Jan 1 03:46:41:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Host-Name AVP:
80 09 00 00 00 07 4c 41 43
*Jan 1 03:46:41:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Vendor-Name AVP:
00 10 00 00 00 08 48 33 43 20 4d 53 52 38 31 30
*Jan 1 03:46:41:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Framing-Capabilities AVP:
80 0a 00 00 00 03 00 00 00 03
*Jan 1 03:46:41:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Assigned-Tunnel-ID AVP:
80 08 00 00 00 09 4a cc
*Jan 1 03:46:41:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Bearer-Capabilities AVP:
80 0a 00 00 00 04 00 00 00 03
*Jan 1 03:46:41:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Receive-Window-Size AVP:
80 08 00 00 00 0a 04 00
*Jan 1 03:46:41:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Challenge AVP:
80 16 00 00 00 0b 1a 38 f3 9b 5f 38 17 04 7b 1d
31 87 71 e2 06 cc
*Jan 1 03:46:42:204 2011 fenbu1 L2TPV2/7/EVENT:
TunnelID=19148: Resent the packet for 1 times.
*Jan 1 03:46:44:204 2011 fenbu1 L2TPV2/7/EVENT:
TunnelID=19148: Resent the packet for 2 times.
*Jan 1 03:46:48:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Message-Type AVP:
80 08 00 00 00 00 00 04
*Jan 1 03:46:48:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Assigned-Tunnel-ID AVP:
80 08 00 00 00 09 4a cc
*Jan 1 03:46:48:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Result-Code AVP:
80 08 00 00 00 01 00 01
*Jan 1 03:46:49:204 2011 fenbu1 L2TPV2/7/EVENT:
TunnelID=21894: Delay-Cleanup timer expired and deleted the local tunnel.
*Jan 1 03:46:51:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Message-Type AVP:
80 08 00 00 00 00 00 01
*Jan 1 03:46:51:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Protocol-Version AVP:
80 08 00 00 00 02 01 00
*Jan 1 03:46:51:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Host-Name AVP:
80 09 00 00 00 07 4c 41 43
*Jan 1 03:46:51:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Vendor-Name AVP:
00 10 00 00 00 08 48 33 43 20 4d 53 52 38 31 30
*Jan 1 03:46:51:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Framing-Capabilities AVP:
80 0a 00 00 00 03 00 00 00 03
*Jan 1 03:46:51:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Assigned-Tunnel-ID AVP:
80 08 00 00 00 09 1a d9
*Jan 1 03:46:51:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Bearer-Capabilities AVP:
80 0a 00 00 00 04 00 00 00 03
*Jan 1 03:46:51:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Receive-Window-Size AVP:
80 08 00 00 00 0a 04 00
*Jan 1 03:46:51:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Challenge AVP:
80 16 00 00 00 0b 76 7a 80 99 0a 10 03 b5 01 54
d9 a9 e1 42 35 9b
*Jan 1 03:46:52:204 2011 fenbu1 L2TPV2/7/EVENT:
TunnelID=6873: Resent the packet for 1 times.
*Jan 1 03:46:54:204 2011 fenbu1 L2TPV2/7/EVENT:
TunnelID=6873: Resent the packet for 2 times.
*Jan 1 03:46:58:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Message-Type AVP:
80 08 00 00 00 00 00 04
*Jan 1 03:46:58:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Assigned-Tunnel-ID AVP:
80 08 00 00 00 09 1a d9
*Jan 1 03:46:58:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Result-Code AVP:
80 08 00 00 00 01 00 01
*Jan 1 03:46:59:204 2011 fenbu1 L2TPV2/7/EVENT:
TunnelID=22553: Delay-Cleanup timer expired and deleted the local tunnel.
*Jan 1 03:47:01:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Message-Type AVP:
80 08 00 00 00 00 00 01
*Jan 1 03:47:01:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Protocol-Version AVP:
80 08 00 00 00 02 01 00
*Jan 1 03:47:01:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Host-Name AVP:
80 09 00 00 00 07 4c 41 43
*Jan 1 03:47:01:204 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Vendor-Name AVP:
00 10 00 00 00 08 48 33 43 20 4d 53 52 38 31 30
*Jan 1 03:47:01:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Framing-Capabilities AVP:
80 0a 00 00 00 03 00 00 00 03
*Jan 1 03:47:01:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Assigned-Tunnel-ID AVP:
80 08 00 00 00 09 18 34
*Jan 1 03:47:01:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Bearer-Capabilities AVP:
80 0a 00 00 00 04 00 00 00 03
*Jan 1 03:47:01:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Receive-Window-Size AVP:
80 08 00 00 00 0a 04 00
*Jan 1 03:47:01:205 2011 fenbu1 L2TPV2/7/CONTROL-PKT:
Encapsulated Challenge AVP:
80 16 00 00 00 0b 26 33 76 ce df ae a5 fa 97 82
65 ba 51 be 2c 3f
*Jan 1 03:47:02:204 2011 fenbu1 L2TPV2/7/EVENT:
TunnelID=6196: Resent the packet for 1 times.
总部的debugging信息
<H3C>*Jun 13 12:52:03:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=20750: Resent the packet for 1 times.
*Jun 13 12:52:04:239 2023 H3C L2TPV2/7/EVENT:
Parsed Message-Type AVP: 1.
*Jun 13 12:52:04:239 2023 H3C L2TPV2/7/EVENT:
Parsed Protocol-Version AVP. Version=1, Revision=0.
*Jun 13 12:52:04:239 2023 H3C L2TPV2/7/EVENT:
Parsed Host-Name AVP: LAC.
*Jun 13 12:52:04:239 2023 H3C L2TPV2/7/EVENT:
Parsed Vendor-Name AVP: H3C MSR810.
*Jun 13 12:52:04:239 2023 H3C L2TPV2/7/EVENT:
Parsed Framing-Capabilities AVP: 3.
*Jun 13 12:52:04:239 2023 H3C L2TPV2/7/EVENT:
Parsed Assigned-Tunnel-ID AVP: 39716.
*Jun 13 12:52:04:239 2023 H3C L2TPV2/7/EVENT:
Parsed Bearer-Capabilities AVP: 3.
*Jun 13 12:52:04:239 2023 H3C L2TPV2/7/EVENT:
Parsed Receive-Window-Size AVP: 1024.
*Jun 13 12:52:04:239 2023 H3C L2TPV2/7/EVENT:
Parsed Challenge AVP: 86 10 de 85 f0 ff 84 e9 83 06 88 5e 63 a5 f7 f8
*Jun 13 12:52:04:240 2023 H3C L2TPV2/7/EVENT:
TunnelID=53999: Processed SCCRQ packet in Idle state, sent SCCRP packet and changed the tunnel state to Wait-connect.
*Jun 13 12:52:04:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=47718: Resent the packet for 2 times.
*Jun 13 12:52:05:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=20750: Resent the packet for 2 times.
*Jun 13 12:52:05:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=53999: Resent the packet for 1 times.
*Jun 13 12:52:07:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=53999: Resent the packet for 2 times.
*Jun 13 12:52:09:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=50616: Delay-Cleanup timer expired and deleted the local tunnel.
*Jun 13 12:52:10:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=53955: Delay-Cleanup timer expired and deleted the local tunnel.
*Jun 13 12:52:11:244 2023 H3C L2TPV2/7/EVENT:
Parsed Message-Type AVP: 1.
*Jun 13 12:52:11:244 2023 H3C L2TPV2/7/EVENT:
Parsed Protocol-Version AVP. Version=1, Revision=0.
*Jun 13 12:52:11:244 2023 H3C L2TPV2/7/EVENT:
Parsed Host-Name AVP: LAC.
*Jun 13 12:52:11:244 2023 H3C L2TPV2/7/EVENT:
Parsed Vendor-Name AVP: H3C MSR810.
*Jun 13 12:52:11:244 2023 H3C L2TPV2/7/EVENT:
Parsed Framing-Capabilities AVP: 3.
*Jun 13 12:52:11:244 2023 H3C L2TPV2/7/EVENT:
Parsed Assigned-Tunnel-ID AVP: 50222.
*Jun 13 12:52:11:244 2023 H3C L2TPV2/7/EVENT:
Parsed Bearer-Capabilities AVP: 3.
*Jun 13 12:52:11:244 2023 H3C L2TPV2/7/EVENT:
Parsed Receive-Window-Size AVP: 1024.
*Jun 13 12:52:11:244 2023 H3C L2TPV2/7/EVENT:
Parsed Challenge AVP: 40 b6 e9 b8 74 b1 e1 35 f0 7a 18 3c 0d a3 62 5a
*Jun 13 12:52:11:245 2023 H3C L2TPV2/7/EVENT:
TunnelID=61871: Processed SCCRQ packet in Idle state, sent SCCRP packet and changed the tunnel state to Wait-connect.
*Jun 13 12:52:12:231 2023 H3C L2TPV2/7/EVENT:
Parsed Message-Type AVP: 1.
*Jun 13 12:52:12:232 2023 H3C L2TPV2/7/EVENT:
Parsed Protocol-Version AVP. Version=1, Revision=0.
*Jun 13 12:52:12:232 2023 H3C L2TPV2/7/EVENT:
Parsed Host-Name AVP: LAC.
*Jun 13 12:52:12:232 2023 H3C L2TPV2/7/EVENT:
Parsed Vendor-Name AVP: H3C MSR810.
*Jun 13 12:52:12:232 2023 H3C L2TPV2/7/EVENT:
Parsed Framing-Capabilities AVP: 3.
*Jun 13 12:52:12:232 2023 H3C L2TPV2/7/EVENT:
Parsed Assigned-Tunnel-ID AVP: 50222.
*Jun 13 12:52:12:232 2023 H3C L2TPV2/7/EVENT:
Parsed Bearer-Capabilities AVP: 3.
*Jun 13 12:52:12:232 2023 H3C L2TPV2/7/EVENT:
Parsed Receive-Window-Size AVP: 1024.
*Jun 13 12:52:12:232 2023 H3C L2TPV2/7/EVENT:
Parsed Challenge AVP: 40 b6 e9 b8 74 b1 e1 35 f0 7a 18 3c 0d a3 62 5a
*Jun 13 12:52:12:232 2023 H3C L2TPV2/7/EVENT:
TunnelID=4332: Processed SCCRQ packet in Idle state, sent SCCRP packet and changed the tunnel state to Wait-connect.
*Jun 13 12:52:12:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=5720: Delay-Cleanup timer expired and deleted the local tunnel.
*Jun 13 12:52:12:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=61871: Resent the packet for 1 times.
*Jun 13 12:52:13:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=4332: Resent the packet for 1 times.
*Jun 13 12:52:14:248 2023 H3C L2TPV2/7/EVENT:
Parsed Message-Type AVP: 1.
*Jun 13 12:52:14:248 2023 H3C L2TPV2/7/EVENT:
Parsed Protocol-Version AVP. Version=1, Revision=0.
*Jun 13 12:52:14:248 2023 H3C L2TPV2/7/EVENT:
Parsed Host-Name AVP: LAC.
*Jun 13 12:52:14:248 2023 H3C L2TPV2/7/EVENT:
Parsed Vendor-Name AVP: H3C MSR810.
*Jun 13 12:52:14:248 2023 H3C L2TPV2/7/EVENT:
Parsed Framing-Capabilities AVP: 3.
*Jun 13 12:52:14:248 2023 H3C L2TPV2/7/EVENT:
Parsed Assigned-Tunnel-ID AVP: 50222.
*Jun 13 12:52:14:248 2023 H3C L2TPV2/7/EVENT:
Parsed Bearer-Capabilities AVP: 3.
*Jun 13 12:52:14:248 2023 H3C L2TPV2/7/EVENT:
Parsed Receive-Window-Size AVP: 1024.
*Jun 13 12:52:14:248 2023 H3C L2TPV2/7/EVENT:
Parsed Challenge AVP: 40 b6 e9 b8 74 b1 e1 35 f0 7a 18 3c 0d a3 62 5a
*Jun 13 12:52:14:248 2023 H3C L2TPV2/7/EVENT:
TunnelID=13560: Processed SCCRQ packet in Idle state, sent SCCRP packet and changed the tunnel state to Wait-connect.
*Jun 13 12:52:14:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=61871: Resent the packet for 2 times.
*Jun 13 12:52:15:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=4332: Resent the packet for 2 times.
*Jun 13 12:52:15:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=13560: Resent the packet for 1 times.
*Jun 13 12:52:17:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=13560: Resent the packet for 2 times.
*Jun 13 12:52:19:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=63873: Delay-Cleanup timer expired and deleted the local tunnel.
*Jun 13 12:52:20:274 2023 H3C L2TPV2/7/EVENT:
TunnelID=58572: Delay-Cleanup timer expired and deleted the local tunnel.
*Jun 13 12:52:21:240 2023 H3C L2TPV2/7/EVENT:
Parsed Message-Type AVP: 1.
*Jun 13 12:52:21:240 2023 H3C L2TPV2/7/EVENT:
Parsed Protocol-Version AVP. Version=1, Revision=0.
*Jun 13 12:52:21:240 2023 H3C L2TPV2/7/EVENT:
Parsed Host-Name AVP: LAC.
*Jun 13 12:52:21:240 2023 H3C L2TPV2/7/EVENT:
Parsed Vendor-Name AVP: H3C MSR810.
*Jun 13 12:52:21:240 2023 H3C L2TPV2/7/EVENT:
Parsed Framing-Capabilities AVP: 3.
*Jun 13 12:52:21:240 2023 H3C L2TPV2/7/EVENT:
Parsed Assigned-Tunnel-ID AVP: 60977.
*Jun 13 12:52:21:240 2023 H3C L2TPV2/7/EVENT:
Parsed Bearer-Capabilities AVP: 3.
*Jun 13 12:52:21:240 2023 H3C L2TPV2/7/EVENT:
Parsed Receive-Window-Size AVP: 1024.
*Jun 13 12:52:21:240 2023 H3C L2TPV2/7/EVENT:
Parsed Challenge AVP: b4 03 c2 43 75 7e e7 2f 9d d9 7a 24 28 0d 56 88
*Jun 13 12:52:21:240 2023 H3C L2TPV2/7/EVENT:
TunnelID=14337: Processed SCCRQ packet in Idle state, sent SCCRP packet and changed the tunnel state to Wait-connect.
undo debugging all
All possible debugging has been turned off.
组网及组网描述:
- 2023-06-13提问
- 举报
-
(0)
最佳答案


分部的配置
#
version 7.1.064, Release 6728P19
#
sysname zaozhuang
#
password-recovery enable
#
vlan 1
#
vlan 100
#
controller Cellular0/0
#
controller Cellular1/0
eth-channel 0
#
controller Cellular1/1
eth-channel 0
#
interface Virtual-PPP1
ppp chap password cipher $c$3$7D0286vceDqcYCWTEFj0RI2z5UicplFQrZjCja57
ppp chap user gdgcc
ip address ppp-negotiate
l2tp-auto-client l2tp-group 1
#
interface NULL0
#
interface Vlan-interface100
ip address 192.168.4.202 255.255.255.0
#
interface GigabitEthernet0/0
port link-mode route
#
interface GigabitEthernet0/1
port link-mode route
ip address 192.168.254.3 255.255.255.0
#
interface GigabitEthernet0/5
port link-mode route
#
interface GigabitEthernet0/2
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/3
port link-mode bridge
#
interface GigabitEthernet0/4
port link-mode bridge
#
interface Eth-channel1/0:0
tcp mss 1280
#
interface Eth-channel1/1:0
dialer circular enable
dialer-group 1
dialer timer idle 0
dialer timer wait-carrier 30
dialer timer autodial 5
dialer number #777 autodial
ip address cellular-alloc
tcp mss 1280
ipsec apply policy 1
#
scheduler logfile size 16
#
line class console
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line con 0
user-role network-admin
#
line vty 0 63
user-role network-operator
#
ip route-static 0.0.0.0 0 Eth-channel1/1:0
ip route-static 192.168.3.13 32 Virtual-PPP1
#
performance-management
#
acl advanced 3300
rule 5 permit ip destination 58.57.249.46 0
#
domain system
#
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
security-enhanced level 1
#
ipsec transform-set 1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy 1 1 isakmp
transform-set 1
security acl 3300
remote-address 58.57.249.46
ike-profile 1
#
l2tp-group 1 mode lac
lns-ip 58.57.249.46
tunnel name zaozhuang
tunnel password cipher $c$3$CjL3c5iqm/rWNN4KNCE1pmbPkWKv1sYiVIiQk+Z/
#
l2tp enable
#
ike profile 1
keychain 1
exchange-mode aggressive
match remote identity address 58.57.249.46 255.255.255.255
#
ike keychain 1
pre-shared-key address 58.57.249.46 255.255.255.255 key cipher $c$3$rBUE1H3Eu336B/MPB20QbkPv/+rqLTOTzlYjztRU
#
return
总部的配置:
#
version 7.1.064, Release 6728P25
#
sysname H3C
#
clock timezone Beijing add 08:00:00
clock protocol none
#
wlan global-configuration
#
telnet server enable
telnet server port 11013
#
undo resource-monitor output syslog snmp-notification netconf-event
#
security-zone intra-zone default permit
#
track 1 nqa entry admin test reaction 1
#
ip pool l2tp1 192.168.10.2 192.168.10.254
ip pool l2tp1 gateway 192.168.10.1
#
ip load-sharing mode per-flow src-ip global
#
dhcp enable
dhcp server always-broadcast
#
dns proxy enable
#
mirroring-group 1 local
#
system-working-mode standard
password-recovery enable
#
vlan 1
#
vlan 2
#
vlan 100
#
nqa entry admin test
type icmp-echo
destination ip 192.168.254.2
frequency 100
next-hop ip 192.168.254.2
reaction 1 checked-element probe-fail threshold-type consecutive 5 action-type trigger-only
#
nqa schedule admin test start-time now lifetime forever
#
controller Cellular0/0
eth-channel 0
#
interface Dialer1
mtu 1492
#
interface Virtual-Template1
ppp authentication-mode chap domain system
remote address pool l2tp1
ip address 192.168.10.1 255.255.255.0
#
interface NULL0
#
interface LoopBack0
#
interface LoopBack100
ip address 2.1.1.1 255.255.255.255
#
interface Vlan-interface2
ip address 192.168.1.1 255.255.255.0
#
interface Vlan-interface100
ip address 192.168.3.200 255.255.255.0
#
interface GigabitEthernet0/0
port link-mode route
description LAN-interface
tcp mss 1280
#
interface GigabitEthernet0/1
port link-mode route
description Single_Line1
ip address 58.57.249.46 255.255.255.252
dns server 219.146.1.66
tcp mss 1280
mirroring-group 1 mirroring-port both
ipsec apply policy 1
#
interface GigabitEthernet0/2
port link-mode route
mirroring-group 1 mirroring-port both
#
interface GigabitEthernet0/3
port link-mode route
#
interface GigabitEthernet0/4
port link-mode route
tcp mss 1280
#
interface GigabitEthernet0/5
port link-mode route
ip address 192.168.254.1 255.255.255.0
ipsec apply policy youxian
#
interface GigabitEthernet0/6
port link-mode route
proxy-arp enable
mirroring-group 1 monitor-port
#
interface GigabitEthernet0/7
port link-mode route
#
interface GigabitEthernet0/8
port link-mode bridge
#
interface GigabitEthernet0/9
port link-mode bridge
#
interface GigabitEthernet0/10
port link-mode bridge
#
interface GigabitEthernet0/11
port link-mode bridge
#
interface GigabitEthernet0/12
port link-mode bridge
#
interface GigabitEthernet0/13
port link-mode bridge
#
interface GigabitEthernet0/14
port link-mode bridge
#
interface GigabitEthernet0/15
port link-mode bridge
port access vlan 100
#
interface Ten-GigabitEthernet0/16
port link-mode route
#
interface Ten-GigabitEthernet0/17
port link-mode route
#
interface Ten-GigabitEthernet0/18
port link-mode route
#
interface Ten-GigabitEthernet0/19
port link-mode route
#
interface Ten-GigabitEthernet0/20
port link-mode route
#
interface Ten-GigabitEthernet0/21
port link-mode route
#
interface VE-L2VPN1
#
interface Eth-channel0/0:0
#
scheduler logfile size 16
#
line class console
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line con 0
user-role network-admin
#
line vty 0 63
authentication-mode scheme
user-role network-admin
user-role network-operator
protocol inbound telnet
#
ip route-static 0.0.0.0 0 GigabitEthernet0/1 58.57.249.45
ip route-static 115.0.0.0 8 58.57.249.45
ip route-static 117.0.0.0 8 58.57.249.45
ip route-static 140.249.148.132 32 58.57.249.45
ip route-static 192.168.4.137 32 192.168.254.2 track 1
ip route-static 192.168.4.137 32 192.168.10.2 preference 70
ip route-static 192.168.100.0 24 192.168.10.0
ip route-static 192.168.100.0 24 192.168.10.2
ip route-static 219.0.0.0 8 58.57.249.45
ip route-static 220.0.0.0 8 58.57.249.45
#
info-center loghost 127.0.0.1 port 3301
info-center source CFGLOG loghost level informational
#
performance-management
#
ssh server enable
ssh server port 11011
#
acl advanced 3000
#
acl advanced 3001
rule 0 permit ip source 192.168.3.13 0 destination 192.168.4.0 0.0.0.255
#
acl advanced 3100
rule 1 deny ip source 2.1.1.1 0 destination 1.1.1.1 0
rule 2 deny ip source 192.168.3.200 0 destination 192.168.3.0 0.0.0.255
rule 3 deny ip source 192.168.3.13 0 destination 192.168.4.0 0.0.0.255
rule 10 permit ip
#
acl advanced 3300
rule 0 permit ip source 2.1.1.1 0 destination 1.1.1.1 0
rule 1 permit ip source 192.168.3.13 0 destination 192.168.4.137 0
#
undo password-control aging enable
undo password-control history enable
password-control length 6
password-control login-attempt 3 exceed lock-time 10
password-control update-interval 0
password-control login idle-time 0
#
radius scheme 1
#
domain system
authorization-attribute ip-pool l2tp1
authentication ppp local
authorization ppp local
#
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user admin class manage
password hash $h$6$7mFT4CUzxu5KRihu$NbBd/JcOZ3OoyT5+rLHNwAvZzA2pAhy1u8v2DHnksFO99h0oYwTylOP8mXtdFQJ1gB2iYvxAFDjIwZBV/VpNaA==
service-type ftp
service-type ssh telnet http https
authorization-attribute user-role network-admin
#
local-user admin1 class network
password cipher $c$3$TEAQCle27KSRpPNq8MMBGfIzBLl/W1eL4h6+IzI=
service-type ppp
authorization-attribute user-role network-operator
authorization-attribute ip 192.168.10.2
#
local-user gdgcc class network
password cipher $c$3$LutOAX7TzbCFRzira94CfCF76dXsK1oavzBWhnJV
service-type ppp
authorization-attribute user-role network-operator
#
security-enhanced level 2
#
ipsec transform-set 1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec transform-set youxian
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy-template 1 1
transform-set 1
ike-profile 1
#
ipsec policy-template youxian 1
transform-set youxian
ike-profile 1
#
ipsec policy 1 1 isakmp template 1
#
ipsec policy policy1 10 isakmp template temp1
#
ipsec policy youxian 1 isakmp template youxian
#
l2tp-group 1 mode lns
allow l2tp virtual-template 1
tunnel name LNS
tunnel password cipher $c$3$xwS5mHywRk6Qo2gU0/8p5L5mBCJz+l5ce64nFcLM
#
l2tp enable
#
ike profile 1
keychain 1
exchange-mode aggressive
match remote identity address 0.0.0.0 0.0.0.0
#
ike keychain 1
pre-shared-key address 0.0.0.0 0.0.0.0 key cipher $c$3$Tg+OTcPJl29i1DDo/pgPltyPT7T4BkBlPDFSU828
#
ip http port 6666
ip https port 11111
ip http enable
ip https enable
web new-style
#
url-filter category custom severity 65535
#
wlan ap-group default-group
vlan 1
#
return
- 2023-06-13回答
- 评论(0)
- 举报
-
(0)


现在在总部和两个分部的出接口上去掉ipsec policy apply ,只保留l2tp,两个分部和总部就能同时建立l2隧道了,各位老师能帮忙看看ipsec是哪里配置错了吗,困扰好几天了,以前厂家给配置的时候只有一个分部,那时候运行正常,现在我们自己想加个分部,就出现这个问题了。
- 2023-06-13回答
- 评论(0)
- 举报
-
(0)
暂无评论
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明
暂无评论