F1050防火墙SSLVPN隧道建立失败
- 0关注
- 0收藏,1446浏览
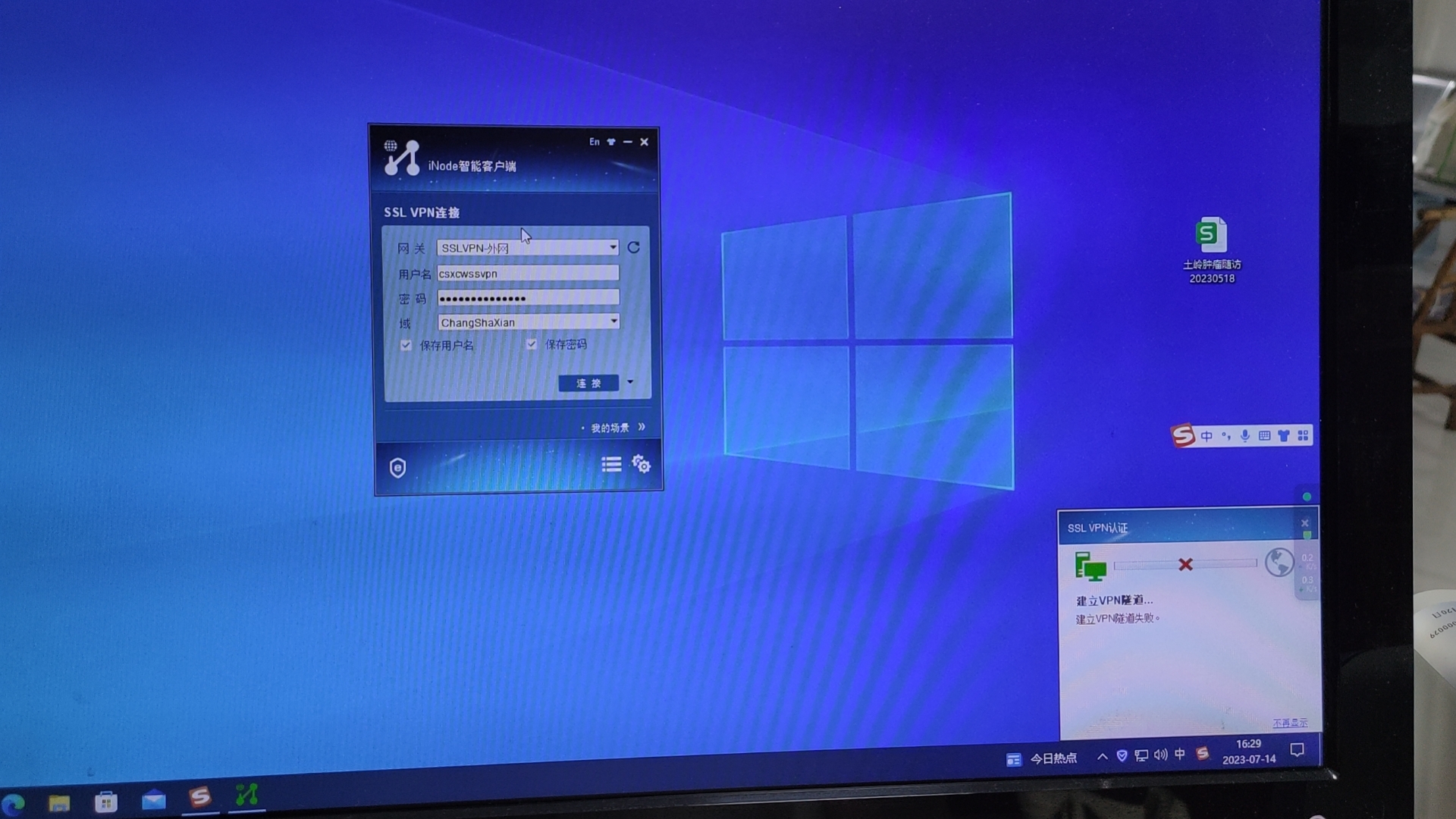
问题描述:
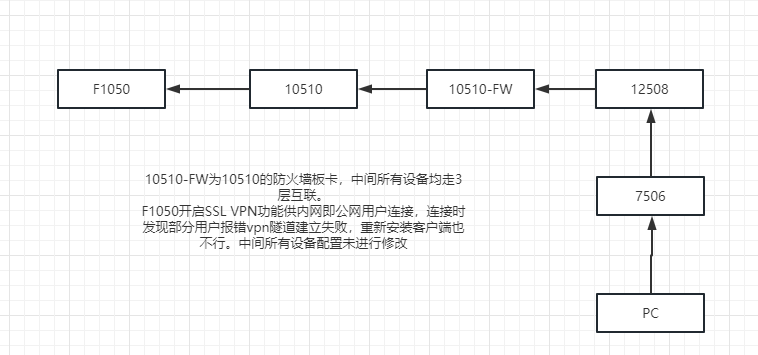
F1050防火墙开启SSLVPN功能,正常正常连接后突然断开,再次连接时提示VPN隧道建立失败。中间所有设备配置均为修改。
组网及组网描述:
- 2023-07-17提问
- 举报
-
(0)

同时开启debug与抓包,然后拨测看一下
- 2023-07-17回答
- 评论(2)
- 举报
-
(0)
还有一点,多次连接有时又能脸上,设备同时在线数60多,在授权范围内。
HN-CSX-ExtDC-G02-F1050-01>*Jul 14 15:16:13:261 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 594, pktid = 36004, offset = 0, ttl = 123, protocol = 6 checksum = 27167, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61885, destination port = 2000 sequence num = 0x8a0060cd, acknowledgement num = 0x1c562daf, flags = 0x18 window size = 511, checksum = 0xf3d7, header length = 20. *Jul 14 15:16:13:266 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 40, pktid = 36005, offset = 0, ttl = 123, protocol = 6 checksum = 27720, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61885, destination port = 2000 sequence num = 0x8a0062f7, acknowledgement num = 0x1c56302d, flags = 0x10 window size = 508, checksum = 0x73ed, header length = 20. *Jul 14 15:16:13:266 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 40, pktid = 36006, offset = 0, ttl = 123, protocol = 6 checksum = 27719, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61885, destination port = 2000 sequence num = 0x8a0062f7, acknowledgement num = 0x1c56302d, flags = 0x11 window size = 508, checksum = 0x73ec, header length = 20. *Jul 14 15:16:13:268 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 40, pktid = 36007, offset = 0, ttl = 123, protocol = 6 checksum = 27718, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61885, destination port = 2000 sequence num = 0x8a0062f8, acknowledgement num = 0x1c56302e, flags = 0x10 window size = 508, checksum = 0x73eb, header length = 20. *Jul 14 15:16:13:915 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Receiving, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 52, pktid = 36008, offset = 0, ttl = 123, protocol = 6 checksum = 27705, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Receiving IP packet from interface GigabitEthernet1/0/1.29. Payload: TCP source port = 61886, destination port = 2000 sequence num = 0x89320617, acknowledgement num = 0x00000000, flags = 0x2 window size = 64240, checksum = 0xe464, *Jul 14 15:16:13:915 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 52, pktid = 36008, offset = 0, ttl = 123, protocol = 6 checksum = 27705, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61886, destination port = 2000 sequence num = 0x89320617, acknowledgement num = 0x00000000, flags = 0x2 window size = 64240, checksum = 0xe618, header length = 32. *Jul 14 15:16:13:923 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 40, pktid = 36009, offset = 0, ttl = 123, protocol = 6 checksum = 27716, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61886, destination port = 2000 sequence num = 0x89320618, acknowledgement num = 0x439b8eab, flags = 0x10 window size = 512, checksum = 0x4bd2, header length = 20. *Jul 14 15:16:13:924 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 239, pktid = 36010, offset = 0, ttl = 123, protocol = 6 checksum = 27516, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61886, destination port = 2000 sequence num = 0x89320618, acknowledgement num = 0x439b8eab, flags = 0x18 window size = 512, checksum = 0xe53b, header length = 20. *Jul 14 15:16:13:935 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 40, pktid = 36011, offset = 0, ttl = 123, protocol = 6 checksum = 27714, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61886, destination port = 2000 sequence num = 0x893206df, acknowledgement num = 0x439b959c, flags = 0x10 window size = 512, checksum = 0x441a, header length = 20. *Jul 14 15:16:13:943 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 238, pktid = 36012, offset = 0, ttl = 123, protocol = 6 checksum = 27515, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61886, destination port = 2000 sequence num = 0x893206df, acknowledgement num = 0x439b959c, flags = 0x18 window size = 512, checksum = 0x738d, header length = 20. *Jul 14 15:16:13:950 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 258, pktid = 36013, offset = 0, ttl = 123, protocol = 6 checksum = 27494, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61886, destination port = 2000 sequence num = 0x893207a5, acknowledgement num = 0x439b9686, flags = 0x18 window size = 511, checksum = 0xbb0a, header length = 20. *Jul 14 15:16:13:955 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 40, pktid = 36014, offset = 0, ttl = 123, protocol = 6 checksum = 27711, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61886, destination port = 2000 sequence num = 0x8932087f, acknowledgement num = 0x439b9721, flags = 0x10 window size = 510, checksum = 0x40f7, header length = 20. *Jul 14 15:16:13:956 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 40, pktid = 36015, offset = 0, ttl = 123, protocol = 6 checksum = 27710, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61886, destination port = 2000 sequence num = 0x8932087f, acknowledgement num = 0x439b9721, flags = 0x11 window size = 510, checksum = 0x40f6, header length = 20. *Jul 14 15:16:13:967 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Receiving, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 52, pktid = 36016, offset = 0, ttl = 123, protocol = 6 checksum = 27697, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Receiving IP packet from interface GigabitEthernet1/0/1.29. Payload: TCP source port = 61887, destination port = 2000 sequence num = 0xf91ab041, acknowledgement num = 0x00000000, flags = 0x2 window size = 64240, checksum = 0xca50, *Jul 14 15:16:13:967 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 52, pktid = 36016, offset = 0, ttl = 123, protocol = 6 checksum = 27697, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61887, destination port = 2000 sequence num = 0xf91ab041, acknowledgement num = 0x00000000, flags = 0x2 window size = 64240, checksum = 0xcc04, header length = 32. *Jul 14 15:16:13:971 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 40, pktid = 36017, offset = 0, ttl = 123, protocol = 6 checksum = 27708, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61887, destination port = 2000 sequence num = 0xf91ab042, acknowledgement num = 0x356f0b6f, flags = 0x10 window size = 512, checksum = 0xc326, header length = 20. *Jul 14 15:16:13:971 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 239, pktid = 36018, offset = 0, ttl = 123, protocol = 6 checksum = 27508, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61887, destination port = 2000 sequence num = 0xf91ab042, acknowledgement num = 0x356f0b6f, flags = 0x18 window size = 512, checksum = 0x67ea, header length = 20. *Jul 14 15:16:13:975 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 40, pktid = 36019, offset = 0, ttl = 123, protocol = 6 checksum = 27706, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61887, destination port = 2000 sequence num = 0xf91ab109, acknowledgement num = 0x356f1260, flags = 0x10 window size = 512, checksum = 0xbb6e, header length = 20. *Jul 14 15:16:13:985 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 238, pktid = 36020, offset = 0, ttl = 123, protocol = 6 checksum = 27507, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61887, destination port = 2000 sequence num = 0xf91ab109, acknowledgement num = 0x356f1260, flags = 0x18 window size = 512, checksum = 0xa70e, header length = 20. *Jul 14 15:16:13:989 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 306, pktid = 36021, offset = 0, ttl = 123, protocol = 6 checksum = 27438, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61887, destination port = 2000 sequence num = 0xf91ab1cf, acknowledgement num = 0x356f134a, flags = 0x18 window size = 511, checksum = 0x9691, header length = 20. *Jul 14 15:16:13:992 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 40, pktid = 36022, offset = 0, ttl = 123, protocol = 6 checksum = 27703, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61887, destination port = 2000 sequence num = 0xf91ab2d9, acknowledgement num = 0x356f13f4, flags = 0x11 window size = 510, checksum = 0xb80b, header length = 20. *Jul 14 15:16:13:993 2023 HN-CSX-ExtDC-G02-F1050-01 IPFW/7/IPFW_PACKET: -COntext=1; Delivering, interface = GigabitEthernet1/0/1.29 version = 4, headlen = 20, tos = 0 pktlen = 40, pktid = 36023, offset = 0, ttl = 123, protocol = 6 checksum = 27702, s = 10.82.212.66, d = 10.82.29.252 channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0. prompt: Forwarding IP packet to upper layer. Payload: TCP source port = 61887, destination port = 2000 sequence num = 0xf91ab2da, acknowledgement num = 0x356f13f5, flags = 0x10 window size = 510, checksum = 0xb80a, header length = 20. 这是隧道建立失败时的debug信息, 建立失败时看了虚拟网卡,状态是正常的。
还有一点,多次连接有时又能脸上,设备同时在线数60多,在授权范围内。


您好,是iNode连接的吗
- 2023-07-17回答
- 评论(3)
- 举报
-
(0)
E0548,这个是定制的版本,我再搞个试下。
是的
你用的版本是啥?用新的适配比较好一点
E0548,这个是定制的版本,我再搞个试下。
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明