如何在已有出链路负载均衡的防火墙上做ipsec配置?
- 0关注
- 0收藏,1491浏览
问题描述:
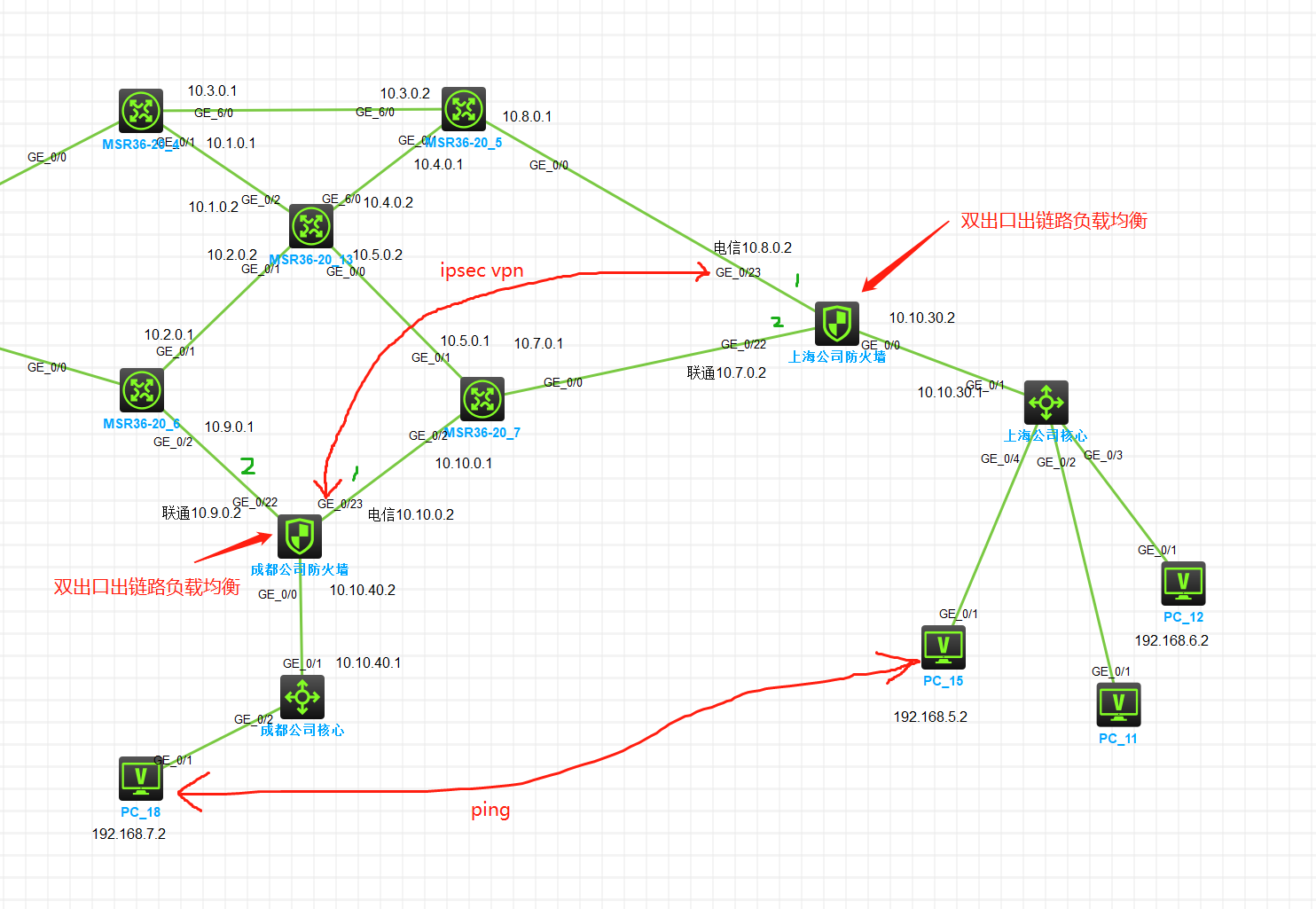
这是按照我们实.际搭建的环境。网络都已经通了没问题。防火墙的配置在附.件中。
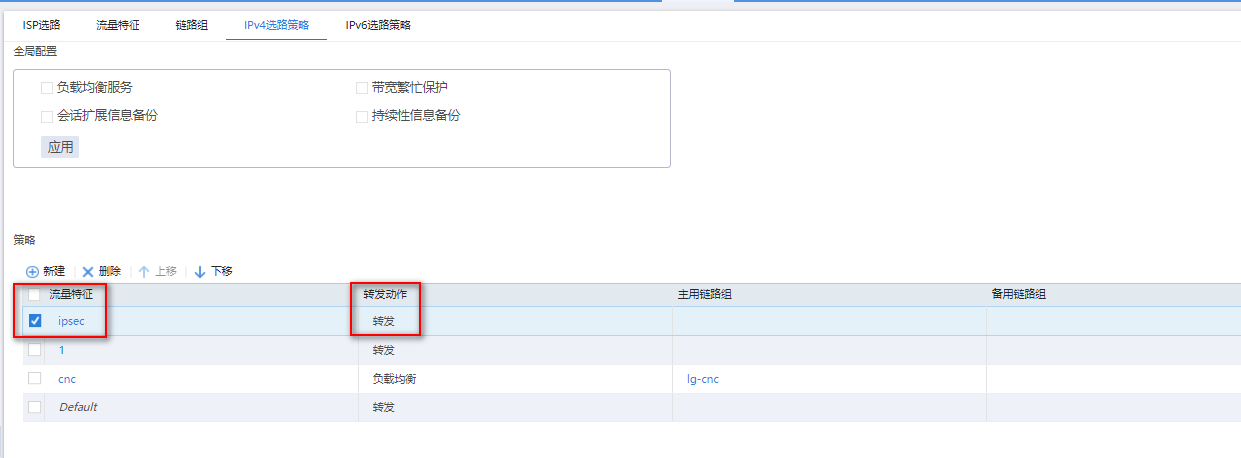
目前想通过ipsec连接Cheng.Du跟Shang.Hai之间的内网,让 192.168.7.2 和192.168.5.2 相互ping通。但两边的防火墙都有双口链路负载均衡,并且使用没问题,在两边的DX线路上加入ipsec 后两边不能ping通。如果在Cheng.Du防火墙上加上 192.168.5.2 32 10.10.0.1的静态路由,那ShangHai就能ping通Cheng.Du,反向则不通,ShangHai也加上 192.168.7.2 32 10.8.0.1 的静态路由两边就都可以通了,关闭两条LT线路和关闭负载均衡虚拟服务器也可以通。很明显感觉问题还是出在负载均衡上,但我已经设置了到两边的流量不经过负载均衡的。虽然加静态路由能用,但感觉这个静态路由不应该加,还有就是未来想做双口的ipsec,如果加了静态路由就影响了吧?
配置好几天了,不知道我的问题出在哪里,希望大.神能够指.点一.二,小.的在此先行谢过
- 2024-03-20提问
- 举报
-
(0)

组网信息
- 2024-03-20回答
- 评论(1)
- 举报
-
(0)
# version 7.1.064, Alpha 7164 # sysname ChenDu-FW # context Admin id 1 # telnet server enable # irf mac-address persistent timer irf auto-update enable undo irf link-delay irf member 1 priority 1 # security-zone intra-zone default permit # ip unreachables enable ip ttl-expires enable # xbar load-single password-recovery enable lpu-type f-series # vlan 1 # interface NULL0 # interface Vlan-interface1 ip address 10.10.40.2 255.255.255.0 # interface GigabitEthernet1/0/1 port link-mode route combo enable copper shutdown ip address 192.168.56.2 255.255.255.0 # interface GigabitEthernet1/0/2 port link-mode route combo enable copper # interface GigabitEthernet1/0/3 port link-mode route combo enable copper # interface GigabitEthernet1/0/4 port link-mode route combo enable copper # interface GigabitEthernet1/0/5 port link-mode route combo enable copper # interface GigabitEthernet1/0/6 port link-mode route combo enable copper # interface GigabitEthernet1/0/7 port link-mode route combo enable copper # interface GigabitEthernet1/0/8 port link-mode route combo enable copper # interface GigabitEthernet1/0/9 port link-mode route combo enable copper # interface GigabitEthernet1/0/10 port link-mode route combo enable copper # interface GigabitEthernet1/0/11 port link-mode route combo enable copper # interface GigabitEthernet1/0/12 port link-mode route combo enable copper # interface GigabitEthernet1/0/13 port link-mode route combo enable copper # interface GigabitEthernet1/0/14 port link-mode route combo enable copper # interface GigabitEthernet1/0/15 port link-mode route combo enable copper # interface GigabitEthernet1/0/16 port link-mode route combo enable copper # interface GigabitEthernet1/0/17 port link-mode route combo enable copper # interface GigabitEthernet1/0/18 port link-mode route combo enable copper # interface GigabitEthernet1/0/19 port link-mode route combo enable copper # interface GigabitEthernet1/0/20 port link-mode route combo enable copper # interface GigabitEthernet1/0/21 port link-mode route combo enable copper # interface GigabitEthernet1/0/22 port link-mode route combo enable copper ip address 10.9.0.2 255.255.255.0 nat outbound 3200 port-preserved # interface GigabitEthernet1/0/23 port link-mode route combo enable copper ip address 10.10.0.2 255.255.255.0 nat outbound 3200 port-preserved ipsec apply policy map1 # interface GigabitEthernet1/0/0 port link-mode bridge combo enable copper # security-zone name Local # security-zone name Trust import interface Vlan-interface1 # security-zone name DMZ # security-zone name Untrust import interface GigabitEthernet1/0/22 import interface GigabitEthernet1/0/23 # security-zone name Management import interface GigabitEthernet1/0/1 # scheduler logfile size 16 # line class aux user-role network-operator # line class console user-role network-admin # line class tty user-role network-operator # line class vty user-role network-operator # line aux 0 user-role network-admin # line con 0 authentication-mode scheme user-role network-admin # line vty 0 4 authentication-mode scheme user-role network-admin # line vty 5 63 user-role network-operator # ip route-static 10.8.0.2 32 10.10.0.1 ip route-static 192.168.7.0 24 10.10.40.1 # info-center loghost 127.0.0.1 port 3301 format default info-center source CFGLOG loghost level informational # acl advanced 3100 description 不需要走负载均衡的放这里 rule 0 permit ip destination 192.168.7.0 0.0.0.255 rule 15 permit ip source 192.168.2.0 0.0.0.255 rule 20 permit ip source 192.168.5.0 0.0.0.255 # acl advanced 3101 description 需要走联通出口的流量放这里 # acl advanced 3102 description 需要走电信出口的流量放这里 rule 0 permit ip destination 192.168.2.0 0.0.0.255 rule 5 permit ip destination 192.168.5.0 0.0.0.255 # acl advanced 3200 description 确定哪些流量是否需要NAT rule 0 deny ip destination 192.168.2.0 0.0.0.255 rule 1 deny ip destination 192.168.5.0 0.0.0.255 rule 10 permit ip source 192.168.7.0 0.0.0.255 # acl advanced 3300 description VPN rule 0 permit ip source 192.168.7.0 0.0.0.255 destination 192.168.5.0 0.0.0.255 # undo password-control aging enable undo password-control length enable undo password-control composition enable undo password-control history enable password-control length 4 undo password-control complexity user-name check # domain system # aaa session-limit ftp 16 aaa session-limit telnet 16 aaa session-limit ssh 16 domain default enable system # role name level-0 description Predefined level-0 role # role name level-1 description Predefined level-1 role # role name level-2 description Predefined level-2 role # role name level-3 description Predefined level-3 role # role name level-4 description Predefined level-4 role # role name level-5 description Predefined level-5 role # role name level-6 description Predefined level-6 role # role name level-7 description Predefined level-7 role # role name level-8 description Predefined level-8 role # role name level-9 description Predefined level-9 role # role name level-10 description Predefined level-10 role # role name level-11 description Predefined level-11 role # role name level-12 description Predefined level-12 role # role name level-13 description Predefined level-13 role # role name level-14 description Predefined level-14 role # user-group system # local-user admin class manage password hash $h$6$wnRilXZmOYievKp2$k6bfMzW///qs8ZQ5LNNMeaNMKTHsBUlx369XgLdByvhIReVeuR38fTj0Vw/crcLXvEb8fUHyvKvQB+JT0wBqgQ== service-type telnet terminal http https authorization-attribute user-role level-3 authorization-attribute user-role network-admin authorization-attribute user-role network-operator # ipsec transform-set tran1 esp encryption-algorithm aes-cbc-128 esp authentication-algorithm sha1 # ipsec policy map1 10 isakmp transform-set tran1 security acl 3300 local-address 10.10.0.2 remote-address 10.8.0.2 ike-profile profile1 # ike profile profile1 keychain keychain1 match remote identity address 10.8.0.2 255.255.255.255 match local address 10.10.0.2 proposal 65535 # ike proposal 65535 encryption-algorithm aes-cbc-128 authentication-algorithm sha256 # ike keychain keychain1 pre-shared-key address 10.8.0.2 255.255.255.255 key cipher $c$3$eLKy8ZKZ1wz+SUinWUHAPu0lnbK9o1oj3qmo # ip http enable ip https enable # sticky-group sg1 type address-port ip source # loadbalance link-group link-group_all predictor hash address source transparent enable success-criteria at-least 1 link link_dianxin-all success-criteria at-least 1 link link_liantong-all success-criteria at-least 1 # loadbalance link-group link-group_dianxin predictor hash address source transparent enable success-criteria at-least 1 link link_dianxin-2 success-criteria at-least 1 # loadbalance link-group link-group_liantong predictor hash address source transparent enable success-criteria at-least 1 link link_liantong-2 success-criteria at-least 1 # loadbalance class class-to-dianxin type link-generic match-any match 1 acl 3102 # loadbalance class class-to-forward-all type link-generic match-any match 1 acl 3100 # loadbalance class class-to-liantong type link-generic match-any match 1 acl 3101 # loadbalance action action-forward-all type link-generic forward all # loadbalance action action-to-dianxin type link-generic link-group link-group_dianxin # loadbalance action action-to-liantong type link-generic link-group link-group_liantong # loadbalance action action-to-link-all type link-generic link-group link-group_all sticky sg1 # loadbalance policy lp type link-generic class class-to-forward-all action action-forward-all class class-to-dianxin action action-to-dianxin class class-to-liantong action action-to-liantong default-class action action-to-link-all # virtual-server vs1 type link-ip virtual ip address 0.0.0.0 0 lb-policy lp bandwidth interface statistics enable service enable # loadbalance link link_dianxin-2 router ip 10.10.0.1 # loadbalance link link_dianxin-all router ip 10.10.0.1 # loadbalance link link_liantong-2 router ip 10.9.0.1 # loadbalance link link_liantong-all router ip 10.9.0.1 # security-policy ip rule 0 name all action pass source-zone Trust destination-zone local rule 1 name bac action pass source-zone local destination-zone Trust rule 2 name bbb action pass source-zone Trust destination-zone Trust rule 3 name nat action pass source-zone Trust destination-zone untrust rule 4 name untrust_to_untrust action pass source-zone local destination-zone untrust rule 5 name vpn action pass source-zone trust destination-ip-range 192.168.4.1 192.168.4.5 destination-ip-range 192.168.5.1 192.168.5.3 rule 6 name untrust_to_local action pass source-zone untrust destination-zone local rule 7 name vpn2 action pass source-ip-range 192.168.5.1 192.168.5.200 destination-ip-range 192.168.2.1 192.168.2.200 rule 8 name vpn3 action pass source-ip-range 192.168.2.1 192.168.2.200 destination-ip-range 192.168.5.1 192.168.5.200 rule 9 name anytoany action pass # return

1、负载策略中新增策略,流量特征匹配ipsec感兴趣流acl,动作为转发,位置顺序放在最前面:

2、需要将ipsec感兴趣流配置静态路由下一跳走原先出口,可能新增链路后,配置两条等价默认路由,在负载转发策略的情况下,流量走路由表转发。
- 2024-03-20回答
- 评论(1)
- 举报
-
(0)
感谢答疑。这里的配置发不了,好多都无法上传。您回答的第二条 配置静态路由是必须的吗? 不管如何配置都应配置感兴趣流里目的地址的静态路由吗?
感谢答疑。这里的配置发不了,好多都无法上传。您回答的第二条 配置静态路由是必须的吗? 不管如何配置都应配置感兴趣流里目的地址的静态路由吗?
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明


# version 7.1.064, Alpha 7164 # sysname ChenDu-FW # context Admin id 1 # telnet server enable # irf mac-address persistent timer irf auto-update enable undo irf link-delay irf member 1 priority 1 # security-zone intra-zone default permit # ip unreachables enable ip ttl-expires enable # xbar load-single password-recovery enable lpu-type f-series # vlan 1 # interface NULL0 # interface Vlan-interface1 ip address 10.10.40.2 255.255.255.0 # interface GigabitEthernet1/0/1 port link-mode route combo enable copper shutdown ip address 192.168.56.2 255.255.255.0 # interface GigabitEthernet1/0/2 port link-mode route combo enable copper # interface GigabitEthernet1/0/3 port link-mode route combo enable copper # interface GigabitEthernet1/0/4 port link-mode route combo enable copper # interface GigabitEthernet1/0/5 port link-mode route combo enable copper # interface GigabitEthernet1/0/6 port link-mode route combo enable copper # interface GigabitEthernet1/0/7 port link-mode route combo enable copper # interface GigabitEthernet1/0/8 port link-mode route combo enable copper # interface GigabitEthernet1/0/9 port link-mode route combo enable copper # interface GigabitEthernet1/0/10 port link-mode route combo enable copper # interface GigabitEthernet1/0/11 port link-mode route combo enable copper # interface GigabitEthernet1/0/12 port link-mode route combo enable copper # interface GigabitEthernet1/0/13 port link-mode route combo enable copper # interface GigabitEthernet1/0/14 port link-mode route combo enable copper # interface GigabitEthernet1/0/15 port link-mode route combo enable copper # interface GigabitEthernet1/0/16 port link-mode route combo enable copper # interface GigabitEthernet1/0/17 port link-mode route combo enable copper # interface GigabitEthernet1/0/18 port link-mode route combo enable copper # interface GigabitEthernet1/0/19 port link-mode route combo enable copper # interface GigabitEthernet1/0/20 port link-mode route combo enable copper # interface GigabitEthernet1/0/21 port link-mode route combo enable copper # interface GigabitEthernet1/0/22 port link-mode route combo enable copper ip address 10.9.0.2 255.255.255.0 nat outbound 3200 port-preserved # interface GigabitEthernet1/0/23 port link-mode route combo enable copper ip address 10.10.0.2 255.255.255.0 nat outbound 3200 port-preserved ipsec apply policy map1 # interface GigabitEthernet1/0/0 port link-mode bridge combo enable copper # security-zone name Local # security-zone name Trust import interface Vlan-interface1 # security-zone name DMZ # security-zone name Untrust import interface GigabitEthernet1/0/22 import interface GigabitEthernet1/0/23 # security-zone name Management import interface GigabitEthernet1/0/1 # scheduler logfile size 16 # line class aux user-role network-operator # line class console user-role network-admin # line class tty user-role network-operator # line class vty user-role network-operator # line aux 0 user-role network-admin # line con 0 authentication-mode scheme user-role network-admin # line vty 0 4 authentication-mode scheme user-role network-admin # line vty 5 63 user-role network-operator # ip route-static 10.8.0.2 32 10.10.0.1 ip route-static 192.168.7.0 24 10.10.40.1 # info-center loghost 127.0.0.1 port 3301 format default info-center source CFGLOG loghost level informational # acl advanced 3100 description 不需要走负载均衡的放这里 rule 0 permit ip destination 192.168.7.0 0.0.0.255 rule 15 permit ip source 192.168.2.0 0.0.0.255 rule 20 permit ip source 192.168.5.0 0.0.0.255 # acl advanced 3101 description 需要走联通出口的流量放这里 # acl advanced 3102 description 需要走电信出口的流量放这里 rule 0 permit ip destination 192.168.2.0 0.0.0.255 rule 5 permit ip destination 192.168.5.0 0.0.0.255 # acl advanced 3200 description 确定哪些流量是否需要NAT rule 0 deny ip destination 192.168.2.0 0.0.0.255 rule 1 deny ip destination 192.168.5.0 0.0.0.255 rule 10 permit ip source 192.168.7.0 0.0.0.255 # acl advanced 3300 description VPN rule 0 permit ip source 192.168.7.0 0.0.0.255 destination 192.168.5.0 0.0.0.255 # undo password-control aging enable undo password-control length enable undo password-control composition enable undo password-control history enable password-control length 4 undo password-control complexity user-name check # domain system # aaa session-limit ftp 16 aaa session-limit telnet 16 aaa session-limit ssh 16 domain default enable system # role name level-0 description Predefined level-0 role # role name level-1 description Predefined level-1 role # role name level-2 description Predefined level-2 role # role name level-3 description Predefined level-3 role # role name level-4 description Predefined level-4 role # role name level-5 description Predefined level-5 role # role name level-6 description Predefined level-6 role # role name level-7 description Predefined level-7 role # role name level-8 description Predefined level-8 role # role name level-9 description Predefined level-9 role # role name level-10 description Predefined level-10 role # role name level-11 description Predefined level-11 role # role name level-12 description Predefined level-12 role # role name level-13 description Predefined level-13 role # role name level-14 description Predefined level-14 role # user-group system # local-user admin class manage password hash $h$6$wnRilXZmOYievKp2$k6bfMzW///qs8ZQ5LNNMeaNMKTHsBUlx369XgLdByvhIReVeuR38fTj0Vw/crcLXvEb8fUHyvKvQB+JT0wBqgQ== service-type telnet terminal http https authorization-attribute user-role level-3 authorization-attribute user-role network-admin authorization-attribute user-role network-operator # ipsec transform-set tran1 esp encryption-algorithm aes-cbc-128 esp authentication-algorithm sha1 # ipsec policy map1 10 isakmp transform-set tran1 security acl 3300 local-address 10.10.0.2 remote-address 10.8.0.2 ike-profile profile1 # ike profile profile1 keychain keychain1 match remote identity address 10.8.0.2 255.255.255.255 match local address 10.10.0.2 proposal 65535 # ike proposal 65535 encryption-algorithm aes-cbc-128 authentication-algorithm sha256 # ike keychain keychain1 pre-shared-key address 10.8.0.2 255.255.255.255 key cipher $c$3$eLKy8ZKZ1wz+SUinWUHAPu0lnbK9o1oj3qmo # ip http enable ip https enable # sticky-group sg1 type address-port ip source # loadbalance link-group link-group_all predictor hash address source transparent enable success-criteria at-least 1 link link_dianxin-all success-criteria at-least 1 link link_liantong-all success-criteria at-least 1 # loadbalance link-group link-group_dianxin predictor hash address source transparent enable success-criteria at-least 1 link link_dianxin-2 success-criteria at-least 1 # loadbalance link-group link-group_liantong predictor hash address source transparent enable success-criteria at-least 1 link link_liantong-2 success-criteria at-least 1 # loadbalance class class-to-dianxin type link-generic match-any match 1 acl 3102 # loadbalance class class-to-forward-all type link-generic match-any match 1 acl 3100 # loadbalance class class-to-liantong type link-generic match-any match 1 acl 3101 # loadbalance action action-forward-all type link-generic forward all # loadbalance action action-to-dianxin type link-generic link-group link-group_dianxin # loadbalance action action-to-liantong type link-generic link-group link-group_liantong # loadbalance action action-to-link-all type link-generic link-group link-group_all sticky sg1 # loadbalance policy lp type link-generic class class-to-forward-all action action-forward-all class class-to-dianxin action action-to-dianxin class class-to-liantong action action-to-liantong default-class action action-to-link-all # virtual-server vs1 type link-ip virtual ip address 0.0.0.0 0 lb-policy lp bandwidth interface statistics enable service enable # loadbalance link link_dianxin-2 router ip 10.10.0.1 # loadbalance link link_dianxin-all router ip 10.10.0.1 # loadbalance link link_liantong-2 router ip 10.9.0.1 # loadbalance link link_liantong-all router ip 10.9.0.1 # security-policy ip rule 0 name all action pass source-zone Trust destination-zone local rule 1 name bac action pass source-zone local destination-zone Trust rule 2 name bbb action pass source-zone Trust destination-zone Trust rule 3 name nat action pass source-zone Trust destination-zone untrust rule 4 name untrust_to_untrust action pass source-zone local destination-zone untrust rule 5 name vpn action pass source-zone trust destination-ip-range 192.168.4.1 192.168.4.5 destination-ip-range 192.168.5.1 192.168.5.3 rule 6 name untrust_to_local action pass source-zone untrust destination-zone local rule 7 name vpn2 action pass source-ip-range 192.168.5.1 192.168.5.200 destination-ip-range 192.168.2.1 192.168.2.200 rule 8 name vpn3 action pass source-ip-range 192.168.2.1 192.168.2.200 destination-ip-range 192.168.5.1 192.168.5.200 rule 9 name anytoany action pass # return