引流
- 0关注
- 1收藏,2237浏览
最佳答案

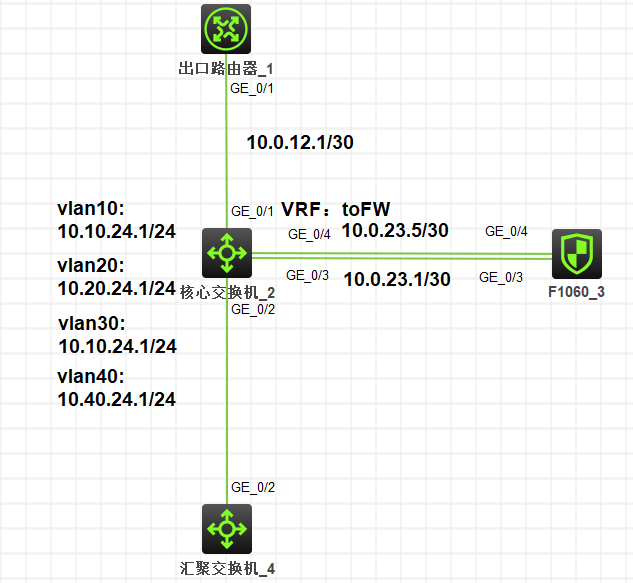
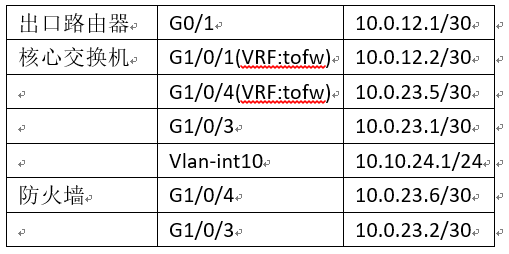
参考案例:
要求:
1、
2、
3、
配置步骤
Ps:内网以vlan 10为例,其他内网网段配置过程一样
一、出口路由器配置
<H3C>system-view
[H3C]sysname Router
[Router]
#配置下行接口IP地址
[Router]inter GigabitEthernet 0/1
[Router-GigabitEthernet0/1]ip address 10.0.12.1 30
[Router-GigabitEthernet0/1]qu
[Router]
#配置内网网段的回程路由,下一跳为核心交换机与路由器互联接口的地址
[Router]ip route-static 10.10.24.0 24 10.0.12.2
#保存配置
Router]save force
Validating file. Please wait...
Configuration is saved to device successfully.
二、汇聚交换机配置
<H3C>system-view
[H3C]sysname L2 SW
[L2 SW]
#创建业务vlan10
[L2 SW]vlan 10
[L2 SW-vlan10]quit
[L2 SW]
#配置上行接口为trunk模式,允许vlan10通过,禁止vlan1通过(非必配)
[L2 SW]inter GigabitEthernet 1/0/2
[L2 SW-GigabitEthernet1/0/2]port trunk permit vlan 10
[L2 SW-GigabitEthernet1/0/2]undo port trunk permit vlan 1
[L2 SW-GigabitEthernet1/0/2]qu
[L2 SW]
#保存配置
[L2 SW]save force
Validating file. Please wait...
Saved the current configuration to mainboard device successfully.
三、核心交换机配置
<H3C>system-view
#创建VRF,名称为tofw
[Core]ip vpn-instance tofw
[Core-vpn-instance-tofw]qu
[Core]
#创建业务vlan10
[Core]vlan 10
[Core-vlan10]qu
[Core]
#配置连接汇聚交换机的接口为trunk模式,允许vlan10通过,禁止vlan1通过(非必配)
[Core]inter GigabitEthernet 1/0/2
[Core-GigabitEthernet1/0/2]port link-type trunk
[Core-GigabitEthernet1/0/2]port trunk permit vlan 10
[Core-GigabitEthernet1/0/2]undo port trunk permit vlan 1
[Core-GigabitEthernet1/0/2]qu
[Core]
#创建vlan-interface 10作为业务网关,地址为10.10.24.1/24
[Core]inter vlan 10
[Core-Vlan-interface10]ip address 10.10.24.1 24
[Core-Vlan-interface10]qu
[Core]
#配置连接防火墙的第一个接口为三层模式,地址为10.0.23.1/30,这个接口作为内网流量出交换机进入防火墙的接口
[Core]inter GigabitEthernet 1/0/3
[Core-GigabitEthernet1/0/3]port link-mode route
[Core-GigabitEthernet1/0/3]ip address 10.0.23.1 30
[Core-GigabitEthernet1/0/3]qu
[Core]
#配置连接防火墙的第二个接口为三层模式,绑定此前创建的VRF,地址为10.0.23.5/30,这个接口作为内网流量从防火墙进入交换机的接口
[Core]inter GigabitEthernet 1/0/4
[Core-GigabitEthernet1/0/4]port link-mode route
[Core-GigabitEthernet1/0/4]ip binding vpn-instance tofw
Some configurations on the interface are removed.
#三层接口绑定VRF后,原有的IP等会被删除掉,因此要先绑定VRF,再配置IP地址
[Core-GigabitEthernet1/0/4]ip address 10.0.23.5 30
[Core-GigabitEthernet1/0/4]qu
[Core]
#配置连接上行路由器的接口为三层模式,绑定此前创建的VRF,配置地址为10.0.12.2/30
[Core]inter GigabitEthernet 1/0/1
[Core-GigabitEthernet1/0/1]port link-mode route
[Core-GigabitEthernet1/0/1]ip binding vpn-instance tofw
Some configurations on the interface are removed.
[Core-GigabitEthernet1/0/1]ip address 10.0.12.2 30
[Core-GigabitEthernet1/0/1]qu
[Core]
#为了保证防火墙任意链路故障交换机可以快速感知到,配置NQA来检测链路状态
#创建一个管理员名为fwprobe,测试操作标签为main的NQA测试组
[Core]nqa entry fwprobe main
#测试类型为ICMP-echo
[Core-nqa-fwprobe-main]type icmp-echo
#探测的目的地址是10.0.23.6
[Core-nqa-fwprobe-main-icmp-echo] destination ip 10.0.23.6
#探测时间间隔为1000ms
[Core-nqa-fwprobe-main-icmp-echo] frequency 1000
#配置探测报文的下一跳地址为10.0.23.2,这样做有一个好处,就是一个探测组即可同时完成两条链路的探测
[Core-nqa-fwprobe-main-icmp-echo] next-hop ip 10.0.23.2
#探测的超时时间为500ms
[Core-nqa-fwprobe-main-icmp-echo] probe timeout 500
#配置序号为1的联动项,连续探测失败5次,触发其他模块联动
[Core-nqa-fwprobe-main-icmp-echo] reaction 1 checked-element probe-fail thresho
ld-type consecutive 5 action-type trigger-only
[Core-nqa-fwprobe-main-icmp-echo]quit
[Core]
#配置立即启动管理员名称为fwprobe,标签为main的测试组一直进行测试
[Core] nqa schedule fwprobe main start-time now lifetime forever
[Core]
#配置track1与NQA测试组fwprobe main关联
[Core]track 1 nqa entry fwprobe main reaction 1
[Core-track-1]quit
[Core]
#配置默认路由指向防火墙,同时与track1联动,即NQA探测链路正常时这条路由生效,探测失败(FW与核心交换机互联的任意链路故障)时路由失效
[Core]ip route-static 0.0.0.0 0 10.0.23.2 track 1 description tofw
[Core]
#为了保证在防火墙故障时,交换机还可以正常将流量转发到出口服务器,配置一条优先级为70(优先级小于上一条)的默认路由,直接指向出口路由器
[Core]ip route-static 0.0.0.0 0 vpn-instance tofw 10.0.12.1 preference 70 descri
ption backup
[Core]
#正向流量从防火墙的G1/0/4口回到交换机的G1/0/4时,流量属于tofw这个VRF,为了保证流量可以正常转发到出口路由器,为VRF:tofw增加一条默认路由指向出口路由器
[Core]ip route-static vpn-instance tofw 0.0.0.0 0 10.0.12.1
[Core]
#回程流量从出口路由器的G0/0口回到交换机的G1/0/1时,流量属于tofw这个VRF,为了保证回程流量可以继续原路返回到防火墙,为VRF:tofw增加一条明细路由指向防火墙,同时也和track1联动,当NQA探测失败(FW与核心交换机互联的任意链路故障),这条路由失效
[Core]ip route-static vpn-instance tofw 10.10.24.0 24 10.0.23.6 track 1
[Core]
#为了防止防火墙与核心交换机的任意互联链路故障,回程流量无法正常发送到内网,所以需要保证在故障场景,VRF:tofw中有到内网网段的路由,下面通过路由复制+EAA策略的方式来实现故障期间复制缺省public实例的内网路由,非故障期间使用手动的静态路由
#配置一个名为backup地址前缀列表,用于过滤只让VRF:tofw学习到的路由,比如10.10.24.0/24和10.20.24.0/24
[Core]ip prefix-list backup index 10 permit 10.10.24.0 24
[Core]ip prefix-list backup index 15 permit 10.20.24.0 24
#配置名为backup的路由策略(路由策略名称可以跟前缀列表名称不一致),用来匹配上面定义的前缀列表
[Core]route-policy backup permit node 10
[Core-route-policy-backup-10]if-match ip address prefix-list backup
[Core-route-policy-backup-10]qu
[Core]
#配置名为backup的EAA策略,当track1检测失败,即FW与核心交换机任意链路故障时,配置路由复制,学习内网网段路由
[Core]rtm cli-policy backup
[Core-rtm-backup]event track 1 state negative
[Core-rtm-backup]action 0 cli system-view
[Core-rtm-backup]action 1 cli ip vpn-instance tofw
[Core-rtm-backup]action 2 cli address-family ipv4
[Core-rtm-backup]action 3 cli route-replicate from public protocol direct route-
policy backup
[Core-rtm-backup]action 4 cli save f
[Core-rtm-backup]user-role network-admin
[Core-rtm-backup]commit
[Core-rtm-backup]quit
[Core]
#配置名为Delbackup的EAA策略,当track1检测恢复,即FW与核心交换机所有链路故障恢复时,取消路由复制,发往内网的回程流量还是走静态路由回防火墙
[Core]rtm cli-policy Delbackup
[Core-rtm-Delbackup]event track 1 state positive
[Core-rtm-Delbackup]action 0 cli system-view
[Core-rtm-Delbackup]action 1 cli ip vpn-instance tofw
[Core-rtm-Delbackup]action 2 cli undo address-family ipv4
[Core-rtm-Delbackup]action 3 cli save f
[Core-rtm-Delbackup]user-role network-admin
[Core-rtm-Delbackup]commit
[Core-rtm-Delbackup]quit
[Core]
#保存当前配置
[Core]save force
Validating file. Please wait...
Saved the current configuration to mainboard device successfully.
四、防火墙配置
<H3C>system-view
[H3C]sysname FW
[FW]
#配置防火墙与核心交换机G1/0/4互联的接口IP为10.0.23.6/30
[FW]inter GigabitEthernet 1/0/4
[FW-GigabitEthernet1/0/4]ip address 10.0.23.6 30
[FW-GigabitEthernet1/0/4]qu
[FW]
#配置防火墙与核心交换机G1/0/3互联的接口IP为10.0.23.2/30
[FW]inter GigabitEthernet 1/0/3
[FW-GigabitEthernet1/0/3]ip address 10.0.23.2 30
[FW-GigabitEthernet1/0/3]qu
[FW]
#因为内网出去的流量是从G1/0/3进入防火墙的,按照配置习惯,将接口G1/0/3加入trust安全域
[FW]security-zone name Trust
[FW-security-zone-Trust]import interface GigabitEthernet 1/0/3
[FW-security-zone-Trust]qu
[FW]
#内网的流量从G1/0/4发往公网,因此将接口G1/0/4加入untrust安全域
[FW]security-zone name Untrust
[FW-security-zone-Untrust]import interface GigabitEthernet 1/0/4
[FW-security-zone-Untrust]qu
[FW]
#配置IPV4安全策略规则
[FW]security-policy ip
#因为交换机有NQA探测,这部分流量是需要访问防火墙本地的,所以放行所有到local安全域的流量
[FW-security-policy-ip]rule 1 name any2local
[FW-security-policy-ip-1-any2local]destination-zone local
[FW-security-policy-ip-1-any2local]action pass
[FW-security-policy-ip-1-any2local]qu
#配置安全策略规则,放行内网到公网的所有流量,本次测试不做限制,实际可根据需求增加源目ip等过滤条件
[FW-security-policy-ip]rule 5 name trust2untrust
[FW-security-policy-ip-5-trust2untrust]source-zone trust
[FW-security-policy-ip-5-trust2untrust]destination-zone untrust
[FW-security-policy-ip-5-trust2untrust]action pass
[FW-security-policy-ip-5-trust2untrust]qu
[FW-security-policy-ip]qu
[FW]
[FW]session statistics enable
This command is CPU intensive and might affect ongoing services. Are you sure you want to continue? [Y/N]:Y
[FW]
#配置默认路由指向核心交换机的G1/0/4口,保证正向流量防火墙检测完成后可发回核心交换机
[FW]ip route-static 0.0.0.0 0 10.0.23.5
#配置内网网段的明细路由指向核心交换机的G1/0/3口,保证回程流量防火墙检测完成后可发回核心交换机
[FW]ip route-static 10.10.24.0 24 10.0.23.1
#保存配置
[FW]save force
Validating file. Please wait...
Saved the current configuration to mainboard device successfully.
五、测试
1、
#核心public路由表:
[Core]dis ip routing-table
Destinations : 17 Routes : 17
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/0 Static 60 0 10.0.23.2 GE1/0/3
#可以看到,当前缺省路由的下一跳地址是防火墙的10.0.23.2
…
[Core]
#核心VRF:tofw路由表:
[Core]dis ip routing-table vpn-instance tofw
Destinations : 18 Routes : 18
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/0 Static 60 0 10.0.12.1 GE1/0/1
10.10.24.0/24 Static 60 0 10.0.23.6 GE1/0/4
#可以看到,当前VRF:tofw的缺省路由指向出口路由器,明细路由是指向防火墙的静态路由
…
#内网可以正常ping通出口路由器地址
<L2 SW>ping 10.0.12.1
Ping 10.0.12.1 (10.0.12.1): 56 data bytes, press CTRL_C to break
56 bytes from 10.0.12.1: icmp_seq=0 ttl=252 time=9.000 ms
56 bytes from 10.0.12.1: icmp_seq=1 ttl=252 time=2.000 ms
56 bytes from 10.0.12.1: icmp_seq=2 ttl=252 time=2.000 ms
56 bytes from 10.0.12.1: icmp_seq=3 ttl=252 time=2.000 ms
56 bytes from 10.0.12.1: icmp_seq=4 ttl=252 time=1.000 ms
--- Ping statistics for 10.0.12.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 1.000/3.200/9.000/2.926 ms
#查看防火墙有来回的会话信息:
<FW>dis session table ipv4 source-ip 10.10.24.254 destination-ip 10.0.12.1 proto
col icmp verbose
Slot 1:
Initiator:
Source IP/port: 10.10.24.254/304
Destination IP/port: 10.0.12.1/2048
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: GigabitEthernet1/0/3
Source security zone: Trust
Responder:
Source IP/port: 10.0.12.1/304
Destination IP/port: 10.10.24.254/0
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: GigabitEthernet1/0/4
Source security zone: Untrust
State: ICMP_REPLY
Application: ICMP
Rule ID: 5
Rule name: trust2untrust
Start time: 2021-12-18 22:12:08 TTL: 0s
Initiator->Responder: 5 packets 420 bytes
Responder->Initiator: 5 packets 420 bytes
Total sessions found: 1
2、
[Core]inter GigabitEthernet 1/0/3
[Core-GigabitEthernet1/0/3]shutdown
[Core-GigabitEthernet1/0/3]
%Dec 18 22:13:50:278 2021 Core IFNET/3/PHY_UPDOWN: Physical state on the interface GigabitEthernet1/0/3 changed to down.
%Dec 18 22:13:50:279 2021 Core IFNET/5/LINK_UPDOWN: Line protocol state on the interface GigabitEthernet1/0/3 changed to down.
#可以看到,NQA探测失败
%Dec 18 22:13:51:080 2021 Core NQA/6/NQA_ENTRY_PROBE_RESULT: Reaction entry 1 of NQA entry admin-name fwprobe operation-tag main: probe-fail.
#backup的EAA策略也正常执行
%Dec 18 22:13:51:310 2021 Core RTM/6/RTM_POLICY: CLI policy backup is running successfully.
[Core-GigabitEthernet1/0/3]qu
#核心public路由表:
[Core]dis ip routing-table
Destinations : 13 Routes : 13
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/0 Static 70 0 10.0.12.1 GE1/0/1
#可以看到,故障发生后,默认路由的下一跳直接指向了出口路由器,而非防火墙
…
#核心VRF:tofw路由表:
[Core]dis ip routing-table vpn-instance tofw
Destinations : 18 Routes : 18
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/0 Static 60 0 10.0.12.1 GE1/0/1
10.10.24.0/24 Direct 0 0 10.10.24.1 Vlan10
#可以看到,故障期间VRF:tofw到内网的回程路由已变成了通过路由复制学习到的直连路由,而非指向防火墙的静态路由
…
#内网依旧可以ping通出口路由器地址
<L2 SW>ping 10.0.12.1
Ping 10.0.12.1 (10.0.12.1): 56 data bytes, press CTRL_C to break
56 bytes from 10.0.12.1: icmp_seq=0 ttl=254 time=1.000 ms
56 bytes from 10.0.12.1: icmp_seq=1 ttl=254 time=0.000 ms
56 bytes from 10.0.12.1: icmp_seq=2 ttl=254 time=2.000 ms
56 bytes from 10.0.12.1: icmp_seq=3 ttl=254 time=1.000 ms
56 bytes from 10.0.12.1: icmp_seq=4 ttl=254 time=3.000 ms
--- Ping statistics for 10.0.12.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 0.000/1.400/3.000/1.020 ms
3、
[Core]inter GigabitEthernet 1/0/3
[Core-GigabitEthernet1/0/3]dis this
#
interface GigabitEthernet1/0/3
port link-mode route
combo enable fiber
shutdown
ip address 10.0.23.1 255.255.255.252
#
return
[Core-GigabitEthernet1/0/3]undo shutdown
[Core-GigabitEthernet1/0/3]%Dec 18 22:18:04:608 2021 Core IFNET/3/PHY_UPDOWN: Physical state on the interface GigabitEthernet1/0/3 changed to up.
%Dec 18 22:18:04:608 2021 Core IFNET/5/LINK_UPDOWN: Line protocol state on the interface GigabitEthernet1/0/3 changed to up.
#可以看到,NQA检测成功
%Dec 18 22:18:04:774 2021 Core NQA/6/NQA_ENTRY_PROBE_RESULT: Reaction entry 1 of NQA entry admin-name fwprobe operation-tag main: probe-pass.
#Delbackup的EAA策略也正常执行
%Dec 18 22:18:05:027 2021 Core RTM/6/RTM_POLICY: CLI policy Delbackup is running successfully.
[Core-GigabitEthernet1/0/3]quit
#核心public路由表:
[Core]dis ip routing-table
Destinations : 17 Routes : 17
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/0 Static 60 0 10.0.23.2 GE1/0/3
#可以看到,故障恢复后默认路由的下一跳地址又回到了防火墙的10.0.23.2
…
[Core]
#核心VRF:tofw路由表:
[Core]dis ip routing-table vpn-instance tofw
Destinations : 18 Routes : 18
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/0 Static 60 0 10.0.12.1 GE1/0/1
10.10.24.0/24 Static 60 0 10.0.23.6 GE1/0/4
#可以看到,恢复后VRF:tofw的缺省路由指向出口路由器,明细路由是指向防火墙的静态路由
…
#内网可以正常ping通出口路由器地址
<L2 SW>ping 10.0.12.1
Ping 10.0.12.1 (10.0.12.1): 56 data bytes, press CTRL_C to break
56 bytes from 10.0.12.1: icmp_seq=0 ttl=252 time=9.000 ms
56 bytes from 10.0.12.1: icmp_seq=1 ttl=252 time=2.000 ms
56 bytes from 10.0.12.1: icmp_seq=2 ttl=252 time=2.000 ms
56 bytes from 10.0.12.1: icmp_seq=3 ttl=252 time=2.000 ms
56 bytes from 10.0.12.1: icmp_seq=4 ttl=252 time=1.000 ms
--- Ping statistics for 10.0.12.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 1.000/3.200/9.000/2.926 ms
#查看防火墙有来回的会话信息:
<FW>dis session table ipv4 source-ip 10.10.24.254 destination-ip 10.0.12.1 proto
col icmp verbose
Slot 1:
Initiator:
Source IP/port: 10.10.24.254/312
Destination IP/port: 10.0.12.1/2048
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: GigabitEthernet1/0/3
Source security zone: Trust
Responder:
Source IP/port: 10.0.12.1/312
Destination IP/port: 10.10.24.254/0
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: GigabitEthernet1/0/4
Source security zone: Untrust
State: ICMP_REPLY
Application: ICMP
Rule ID: 5
Rule name: trust2untrust
Start time: 2021-12-18 22:27:36 TTL: 22s
Initiator->Responder: 5 packets 420 bytes
Responder->Initiator: 5 packets 420 bytes
Total sessions found: 1
配置关键点
#为了防止防火墙与核心交换机的任意互联链路故障,回程流量无法正常发送到内网,所以需要保证在故障场景,VRF:tofw中有到内网网段的路由,下面通过路由复制+EAA策略的方式来实现故障期间复制缺省public实例的内网路由,非故障期间使用手动的静态路由
- 2024-09-17回答
- 评论(0)
- 举报
-
(1)
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明


暂无评论