防火墙怎么新建SSL-VPN策略组
- 0关注
- 0收藏,873浏览
最佳答案

SSL VPN中建立新的实例
- 2025-07-23回答
- 评论(2)
- 举报
-
(0)
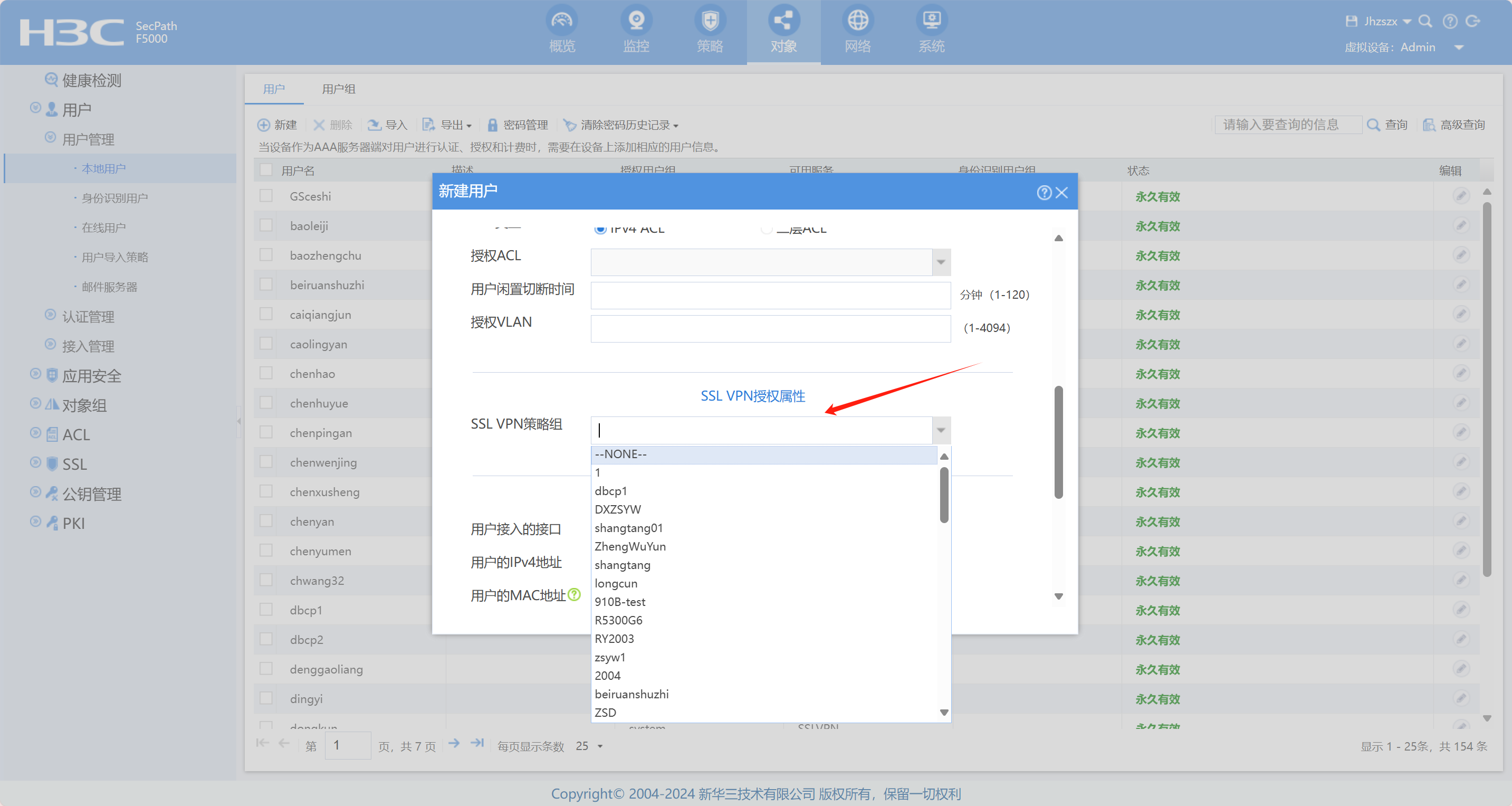
SSL VPN配置里面去加
没有看到策略组呀
SSL VPN配置里面去加

1.13.2 SSL VPN用户的身份识别与管理配置举例
1. 组网需求
Device为SSL VPN网关设备,连接公网用户和企业私有网络。其中,企业私有网络内部提供了Web服务器资源供远程用户访问(通过HTTP协议和80端口号)。配置Device对用户进行本地认证和本地授权,具体要求如下:
· Device从本地用户数据库学习身份识别账户。
· Device基于角色为SSL VPN用户授权策略组,使得用户可以通过Device安全地访问位于私有网络内部的Web server。
2. 组网图
图1-4 SSL VPN用户的身份识别与管理配置组网图
表1-3 组网图示例接口与设备实际接口对应关系
组网图示例接口 | 设备实际接口 |
Interface1 | GigabitEthernet1/0/1 |
Interface2 | GigabitEthernet1/0/2 |
3. 配置准备
Device已获取到CA证书ca.cer和服务器证书server.pfx,若SSL VPN网关不引用SSL服务端策略,则使用设备缺省证书。
根据组网图中规划的信息,确保用户主机、Device与Web server之间路由可达。
4. 配置步骤
(1) 配置接口IP地址
# 根据组网图中规划的信息,配置各接口的IP地址,具体配置步骤如下。
<Device> system-view
[Device] ip http enable
[Device] ip https enable
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] ip address 2.1.1.1 255.255.255.0
[Device-GigabitEthernet1/0/1] quit
请参考以上步骤配置其他接口的IP地址,具体配置步骤略。
(2) 配置安全域
# 请根据组网图中规划的信息,将接口加入对应的安全域,具体配置步骤如下。
[Device] security-zone name untrust
[Device-security-zone-Untrust] import interface gigabitethernet 1/0/1
[Device-security-zone-Untrust] quit
[Device] security-zone name trust
[Device-security-zone-Trust] import interface gigabitethernet 1/0/2
[Device-security-zone-Trust] quit
(3) 配置安全策略放行Untrust与Local安全域之间的流量,用于用户访问SSL VPN网关设备。
# 配置名称为sslvpnlocalout1的安全策规则,使Device可以向用户发送报文,具体配置步骤如下。
[Device] security-policy ip
[Device-security-policy-ip] rule name sslvpnlocalout1
[Device-security-policy-ip-1-sslvpnlocalout1] source-zone local
[Device-security-policy-ip-1-sslvpnlocalout1] destination-zone untrust
[Device-security-policy-ip-1-sslvpnlocalout1] source-ip-host 2.1.1.1
[Device-security-policy-ip-1-sslvpnlocalout1] destination-ip-host 4.4.4.1
[Device-security-policy-ip-1-sslvpnlocalout1] destination-ip-host 4.4.4.2
[Device-security-policy-ip-1-sslvpnlocalout1] destination-ip-host 4.4.4.3
[Device-security-policy-ip-1-sslvpnlocalout1] action pass
[Device-security-policy-ip-1-sslvpnlocalout1] quit
# 配置名称为sslvpnlocalin1的安全策略规则,使用户可以向Device发送报文,具体配置步骤如下。
[Device-security-policy-ip] rule name sslvpnlocalin1
[Device-security-policy-ip-2-sslvpnlocalin1] source-zone untrust
[Device-security-policy-ip-2-sslvpnlocalin1] destination-zone local
[Device-security-policy-ip-2-sslvpnlocalin1] source-ip-host 4.4.4.1
[Device-security-policy-ip-2-sslvpnlocalin1] source-ip-host 4.4.4.2
[Device-security-policy-ip-2-sslvpnlocalin1] source-ip-host 4.4.4.3
[Device-security-policy-ip-2-sslvpnlocalin1] destination-ip-host 2.1.1.1
[Device-security-policy-ip-2-sslvpnlocalin1] action pass
[Device-security-policy-ip-2-sslvpnlocalin1] quit
# 配置名称为sslvpnlocalout2的安全策规则,使Device可以向Web server发送报文,具体配置步骤如下。
[Device-security-policy-ip] rule name sslvpnlocalout2
[Device-security-policy-ip-3-sslvpnlocalout2] source-zone local
[Device-security-policy-ip-3-sslvpnlocalout2] destination-zone trust
[Device-security-policy-ip-3-sslvpnlocalout2] source-ip-host 3.3.3.3
[Device-security-policy-ip-3-sslvpnlocalout2] destination-ip-host 20.2.2.2
[Device-security-policy-ip-3-sslvpnlocalout2] action pass
[Device-security-policy-ip-3-sslvpnlocalout2] quit
# 配置名称为sslvpnlocalin2的安全策略规则,使Web server可以向Device发送报文,具体配置步骤如下。
[Device-security-policy-ip] rule name sslvpnlocalin2
[Device-security-policy-ip-4-sslvpnlocalin2] source-zone trust
[Device-security-policy-ip-4-sslvpnlocalin2] destination-zone local
[Device-security-policy-ip-4-sslvpnlocalin2] source-ip-host 20.2.2.2
[Device-security-policy-ip-4-sslvpnlocalin2] destination-ip-host 3.3.3.3
[Device-security-policy-ip-4-sslvpnlocalin2] action pass
[Device-security-policy-ip-4-sslvpnlocalin2] quit
[Device-security-policy-ip] quit
(4) 配置PKI域,设置证书申请所需的相关参数
[Device] pki domain sslvpn
[Device-pki-domain-sslvpn] public-key rsa general name sslvpn
[Device-pki-domain-sslvpn] undo crl check enable
[Device-pki-domain-sslvpn] quit
[Device] pki import domain sslvpn der ca filename ca.cer
[Device] pki import domain sslvpn p12 local filename server.pfx
(5) 配置SSL服务器端策略,引用PKI域
[Device] ssl server-policy ssl
[Device-ssl-server-policy-ssl] pki-domain sslvpn
[Device-ssl-server-policy-ssl] quit
(6) 配置用户身份识别角色
# 创建网络接入类本地SSL VPN用户usera、userb、userc。
[Device] local-user usera class network
[Device-luser-network-usera] password simple a123456
[Device-luser-network-usera] service-type sslvpn
[Device-luser-network-usera] quit
[Device] local-user userb class network
[Device-luser-network-userb] password simple b123456
[Device-luser-network-userb] service-type sslvpn
[Device-luser-network-userb] quit
[Device] local-user userc class network
[Device-luser-network-userc] password simple c123456
[Device-luser-network-userc] service-type sslvpn
[Device-luser-network-userc] quit
# 创建本地用户组group1,将本地用户usera、userb、userc加入用户组group1。
[Device] user-group group1
[Device-ugroup-group1] identity-member user usera
[Device-ugroup-group1] identity-member user userb
[Device-ugroup-group1] identity-member user userc
[Device-ugroup-group1] quit
# 创建身份识别角色r1。
[Device] user-identity role name r1
# 引用身份识别用户组group1。
[Device-identity-role-r1] user-group name group1
[Device-identity-role-r1] quit
# 开启用户身份识别功能。
[Device] user-identity enable
(7) 配置SSL VPN网关,为用户提供登录SSL VPN网关的入口
# 配置SSL VPN网关gw的IP地址为2.1.1.1,端口号为2000。
[Device] sslvpn gateway gw
[Device-sslvpn-gateway-gw] ip address 2.1.1.1 port 2000
[Device-sslvpn-gateway-gw] service enable
[Device-sslvpn-gateway-gw] quit
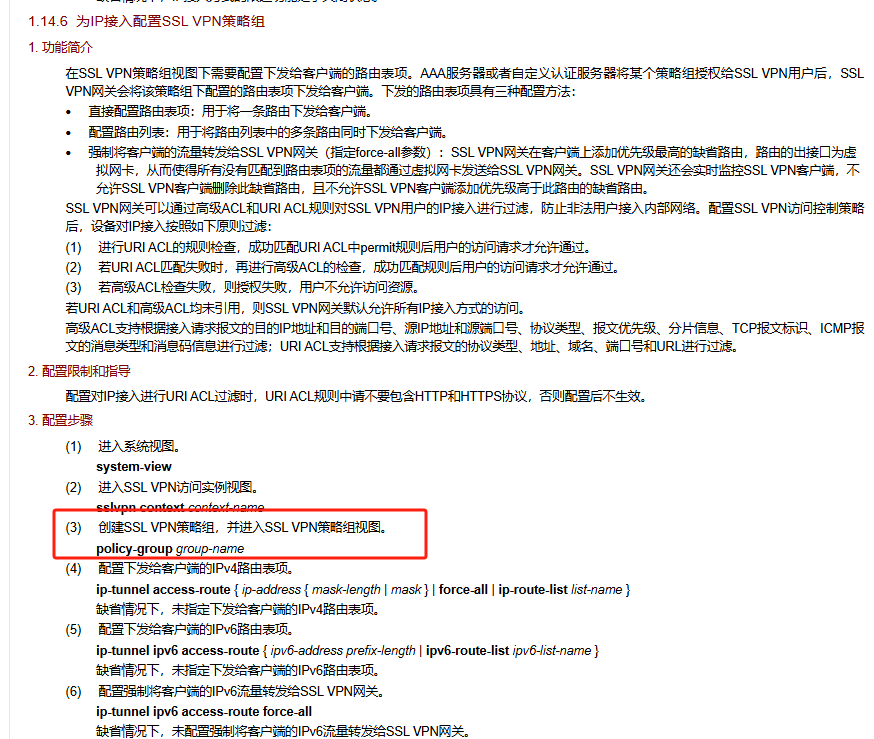
(8) 配置SSL VPN访问实例,为用户提供SSL VPN Web接入服务
# 配置SSL VPN访问实例ctx1引用SSL VPN网关gw。
[Device] sslvpn context ctx1
[Device-sslvpn-context-ctx1] url-item urlitem
[Device-sslvpn-context-ctx1-url-item-urlitem] url http://20.2.2.2
[Device-sslvpn-context-ctx1-url-item-urlitem] quit
[Device-sslvpn-context-ctx1] url-list urllist
[Device-sslvpn-context-ctx1-url-list-urllist] heading web
[Device-sslvpn-context-ctx1-url-list-urllist] resources url-item urlitem
[Device-sslvpn-context-ctx1-url-list-urllist] quit
[Device-sslvpn-context-ctx1] policy-group p1
[Device-sslvpn-context-ctx1-policy-group-p1] resources url-list urllist
[Device-sslvpn-context-ctx1-policy-group-p1] quit
# 配置SSL VPN基于角色r1授权策略组p1。
[Device-sslvpn-context-ctx1] role r1
[Device-sslvpn-context-ctx1-role-r1] resources policy-group p1
[Device-sslvpn-context-ctx1-role-r1] web-access enable
[Device-sslvpn-context-ctx1-role-r1] quit
[Device-sslvpn-context-ctx1] service enable
[Device-sslvpn-context-ctx1] quit
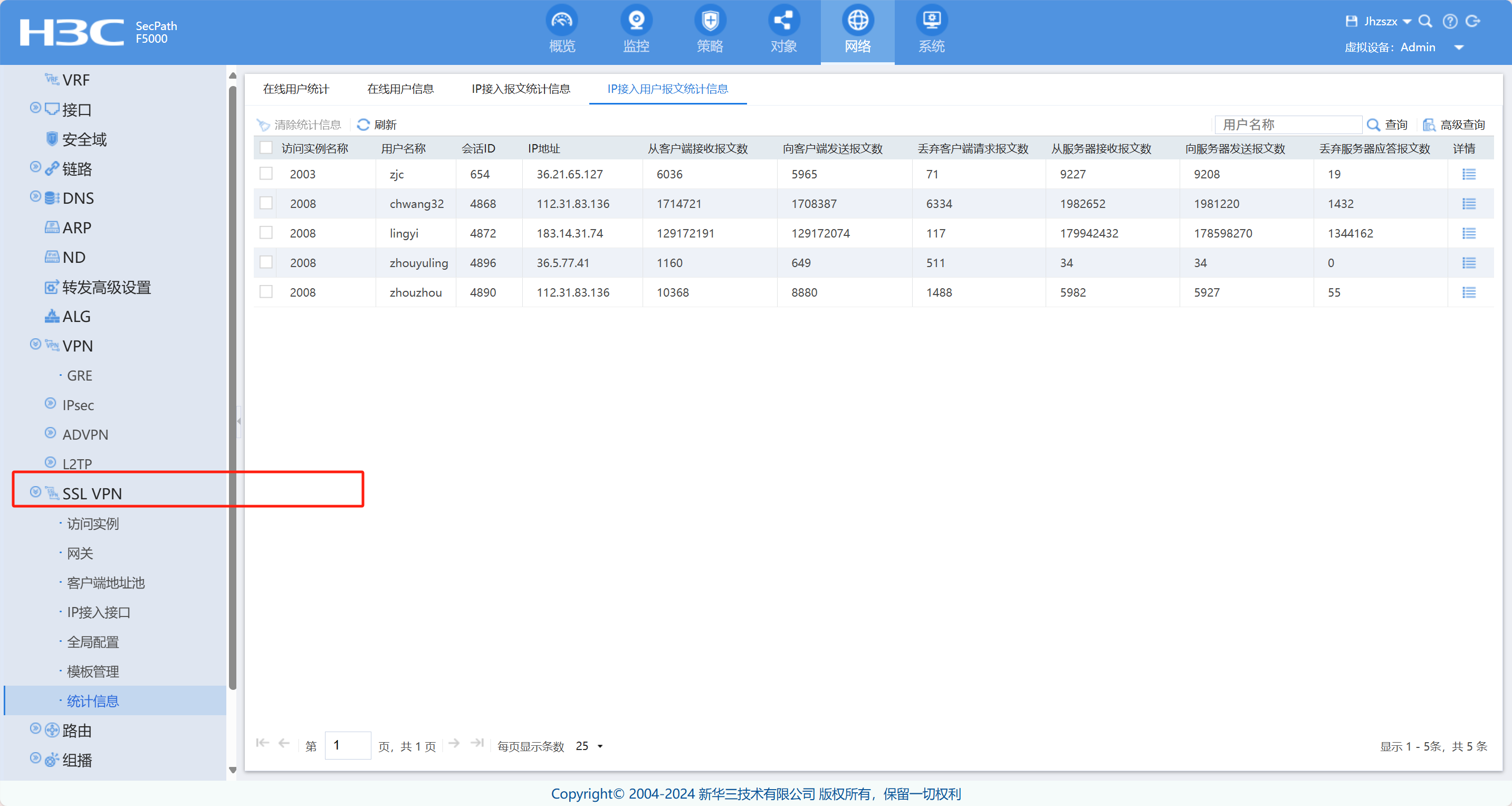
5. 验证配置
# 以上配置完成后,可通过如下显示命令查看身份识别角色引用信息。
[Device] display user-identity role
--------------------------------------------------------------------------
Role name: default
This role is assigned to all identity users that do not obtain an administer-defined role.
--------------------------------------------------------------------------
Role name: r1
User group name Domain name
group1 N/A
Total 2 records matched.
SSL VPN用户在浏览器上输入https://2.1.1.1:2000/后,输入对应的本地用户名及密码即可成功登录网关。之后,该用户就能够通过浏览器访问网关为其所属角色授权的远端Web服务器资源。
- 2025-07-26回答
- 评论(0)
- 举报
-
(0)
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明