IPSEC防火墙组网问题
- 0关注
- 0收藏,351浏览
问题描述:
东站交换机(192.168.1.4)-防火墙(IPSEC-VLANIF)-PTN-外网-总公司PTN-防火墙(IPSEC-VLANIF)-服务器(192.168.1.1)
如上组网全二层,分支与总公司使用同一个组网由于一些原因内网地址不可更改现插入两台防火墙做IPSEC采用VLANIF建立IPSEC隧道如何配置防火墙
- 2026-03-29提问
- 举报
-
(0)
最佳答案


关键配置步骤与命令:
1. 接口与地址:为防火墙连接内网的接口(如G1/0/1)创建VLAN,并配置VLANIF接口地址,作为内网网关(例如`192.168.1.254/24`)。
interface vlan-interface 10
ip address 192.168.1.254 255.255.255.0
interface gigabitethernet 1/0/1
port link-mode route
port access vlan 10
2. IPsec策略:创建IPsec安全策略,采用手工方式(适用于地址固定)或IKE动态协商方式。
* IKE方式示例:
ike proposal 10
encryption-algorithm aes-cbc 256
authentication-algorithm sha256
dh group14
ike keychain keychain1
pre-shared-key address 对端VLANIF公网地址 key simple YourPSK
ike profile profile1
keychain keychain1
local-identity address 本端VLANIF公网地址
match remote identity address 对端VLANIF公网地址
ipsec transform-set transform1
esp encryption-algorithm aes-cbc 256
esp authentication-algorithm sha256
ipsec policy policy1 10 isakmp
security acl 3000
ike-profile profile1
transform-set transform1
local-address 本端VLANIF公网地址
remote-address 对端VLANIF公网地址
3. 应用策略:在VLANIF接口上应用IPsec策略。
interface vlan-interface 10
ipsec apply policy policy1
4. ACL定义感兴趣流:ACL 3000需精确匹配需要加密的流量(源:分支内网网段,目的:总部服务器网段)。
acl advanced 3000
rule permit ip source 192.168.1.0 0.0.0.255 destination 192.168.1.1 0
5. 路由:在分支防火墙配置静态路由,指向总部的服务器网段,下一跳为对端防火墙VLANIF的公网地址(或建立IPsec隧道后,此路由用于触发隧道建立)。
重要提醒:
地址规划:两端VLANIF接口必须配置可路由的公网IP地址(由运营商分配),用于建立IP
- 2026-03-29回答
- 评论(0)
- 举报
-
(0)

内网地址冲突,一端先NAT在走隧道
ipsec网络,当两端局域网ip重叠,可以通过PBR+nat outbound方式解决两端局域网访问不通的问题。
参考案例:
ipsec VPN,两端地址重叠,导致ipsec建立成功后,两端不能互访,实验室组网拓扑简图如图一所示:
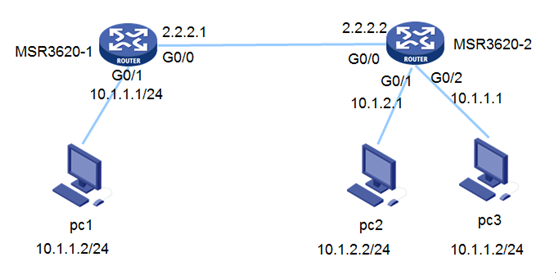
图一 组网拓扑
两端局域网出口设备建立ipsec之后,由PC1侧发起ping操作到PC2侧时,ping报文可以到达PC2,但当PC2回应报文时,由于在MSR3620-2侧直接查找本地路由到了PC3,无法到达设备出接口封装ipsec报文头,导致两端局域网终端无法互访。
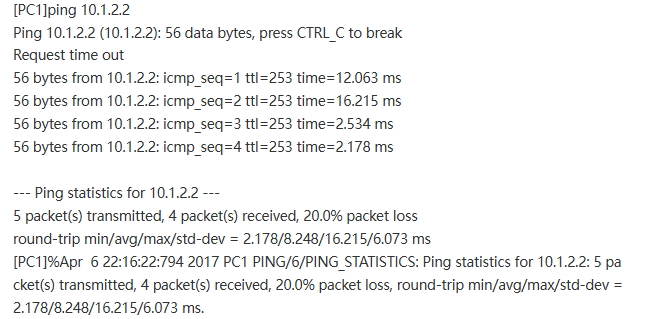
在连接PC2的接口上配nat outbound和PBR,PC1发出的报文在该接口上先
匹配nat outbound,替换为该接口ip地址到达pc2,pc2回应的时候匹配PBR,下一跳为MSR3620-2的出接口ip地址,将该报文送到MSR3620-2的ipsec接口上,使PC1访问PC2的报文得到回应。
关键配置如下:
MSR3620-1:
#
interface GigabitEthernet0/0
port link-mode route
combo enable copper
ip address 2.2.2.1 255.255.255.0
ipsec apply policy map1
#
interface GigabitEthernet0/1
port link-mode route
combo enable copper
ip address 10.1.1.1 255.255.255.0
#
ip route-static 10.1.2.0 24 GigabitEthernet0/0 2.2.2.2
#
acl advanced 3101
rule 0 permit ip source 10.1.1.0 0.0.0.255 destination 10.1.2.0 0.0.0.255
#
ipsec transform-set tran1
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec policy map1 10 isakmp
transform-set tran1
security acl 3101
local-address 2.2.2.1
remote-address 2.2.2.2
ike-profile profile1
#
ike profile profile1
keychain keychain1
match remote identity address 2.2.2.2 255.255.255.0
#
ike keychain keychain1
pre-shared-key address 2.2.2.2 255.255.255.0 key cipher $c$3$0hpFFye6lOO9kcA9W2ZftyUCBV6c6A==
#
MSR3620-2:
policy-based-route aaa permit node 5
if-match acl 3000
apply next-hop 2.2.2.1
#
interface GigabitEthernet0/0
port link-mode route
combo enable copper
ip address 2.2.2.2 255.255.255.0
ipsec apply policy use1
#
interface GigabitEthernet0/1
port link-mode route
combo enable copper
ip address 10.1.2.1 255.255.255.0
nat outbound
ip policy-based-route aaa
#
interface GigabitEthernet0/2
port link-mode route
combo enable copper
ip address 10.1.1.1 255.255.255.0
#
ip route-static 10.1.1.0 24 GigabitEthernet0/0 2.2.2.1
#
acl advanced 3000
rule 0 permit ip source 10.1.2.2 0 destination 10.1.1.2 0
#
acl advanced 3101
rule 0 permit ip source 10.1.2.0 0.0.0.255 destination 10.1.1.0 0.0.0.255
#
ipsec transform-set tran1
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec policy use1 10 isakmp
transform-set tran1
security acl 3101
local-address 2.2.2.2
remote-address 2.2.2.1
ike-profile profile1
#
ike profile profile1
keychain keychain1
match remote identity address 2.2.2.1 255.255.255.0
#
ike keychain keychain1
pre-shared-key address 2.2.2.1 255.255.255.0 key cipher $c$3$FmI8sXpm7iD4vhMvu4cbssfcsSqiIQ==
验证:
- 2026-03-29回答
- 评论(0)
- 举报
-
(0)
暂无评论

核心思路与拓扑定位
- 网络环境:全二层透明传输,内网地址(192.168.1.0/24)固定不可变。
- 防火墙角色:作为透明模式(Layer 2)或配置VLANIF接口的路由模式设备,串接在交换机与PTN之间。
- 配置难点:IPSec隧道两端的内网地址相同,需在防火墙侧配置NAT以避免路由冲突。
防火墙配置步骤
物理接口与VLAN配置
- 物理接口配置
- 将连接东站交换机的接口配置为Access模式,允许VLAN 10。
- 将连接PTN的接口配置为Trunk或Access模式,根据PTN侧要求配置。
- VLANIF接口配置
- 创建VLAN 10,并配置VLANIF 10接口IP为192.168.1.254(作为内网网关)。
- 确保该接口与东站交换机的192.168.1.4在同一网段。
- 物理接口配置
- 将连接服务器的接口配置为Access模式,允许VLAN 10。
- 将连接PTN的接口配置为Trunk或Access模式。
- VLANIF接口配置
- 创建VLAN 10,并配置VLANIF 10接口IP为192.168.1.253(作为内网网关)。
- 确保该接口与服务器的192.168.1.1在同一网段。
IPSec隧道配置
- 安全策略
- 允许VLANIF 10接口访问外网接口的流量。
- IPSec配置
- 配置IKEv2或IKEv1,定义预共享密钥。
- 配置IPSec策略,指定对端公网IP(PTN外网IP)。
- 启用NAT穿越(NAT-T)功能。
- 安全策略
- 允许VLANIF 10接口访问外网接口的流量。
- IPSec配置
- 配置IKEv2或IKEv1,使用与东站侧相同的预共享密钥。
- 配置IPSec策略,指定对端公网IP(PTN外网IP)。
- 启用NAT穿越(NAT-T)功能。
NAT配置(关键步骤)
- 配置源NAT,将VLANIF 10接口的流量转换为防火墙外网接口IP。
- 配置源NAT,将VLANIF 10接口的流量转换为防火墙外网接口IP。
验证与测试
- 连通性测试
- 从东站交换机ping总公司服务器,验证隧道连通性。
- 日志检查
- 检查防火墙日志,确认IPSec隧道建立成功。
- NAT验证
- 确认流量经过NAT转换,内网地址未冲突。
- 2026-03-30回答
- 评论(0)
- 举报
-
(0)
暂无评论
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明

暂无评论