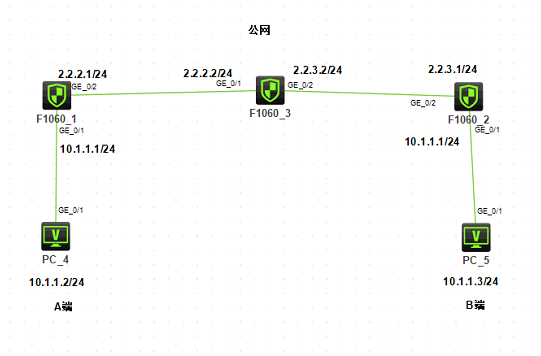
组网及说明
1.组网
问题描述
2.需求
客户两端的内网网段一样,并且由于某些原因无法更改内网网段,现在需要通过ipsec VPN实现A端设备10.1.1.2要能访问对端内网的10.1.1.3,同时要求对端也能访问自己。
过程分析
配置思路:
由于两端内网一样,互访的流量根本不会到达防火墙上面,从而无法触发ipsec隧道建立,所以需要在A端防火墙内网接口的入方向配置目的地址转换,出方向配置源地址转换,对端防火墙也做同样的配置,同时防火墙上还需要配置PBR引流。
最终结果:PC4通过访问10.1.3.1访问PC5,PC5通过访问10.1.4.1访问PC4。
解决方法
3.关键配置
FWA:
#
nat address-group 0
address 10.1.4.1 10.1.4.1
#
//将本端发起访问的流量引流至公网接口
policy-based-route huqi permit node 0
if-match acl 3000
apply next-hop 2.2.2.2
#
interface GigabitEthernet1/0/1
port link-mode route
description LAN
combo enable copper
ip address 10.1.1.1 255.255.255.0
//对对端主动发起的流量做源地址转换
nat outbound 3002 address-group 0
//对本端发起的流量做目的地址转换
nat server global 10.1.3.1 inside 10.1.1.3
ip policy-based-route huqi
#
interface GigabitEthernet1/0/2
port link-mode route
description WAN
combo enable copper
ip address 2.2.2.1 255.255.255.0
nat outbound 3001
ipsec apply policy map1
#
security-zone name Trust
import interface GigabitEthernet1/0/1
#
security-zone name Untrust
import interface GigabitEthernet1/0/2
#
ip route-static 0.0.0.0 0 2.2.2.2
#
acl advanced 3000
rule 0 permit ip source 10.1.1.0 0.0.0.255 destination 10.1.1.0 0.0.0.255
#
acl advanced 3001
rule 0 deny ip source 10.1.1.0 0.0.0.255 destination 10.1.1.0 0.0.0.255
rule 5 permit ip
#
acl advanced 3002
rule 0 permit ip source 10.1.1.3 0 destination 10.1.1.2 0
#
ipsec transform-set tran1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy map1 10 isakmp
transform-set tran1
security acl 3000
remote-address 2.2.3.1
ike-profile profile1
#
ike profile profile1
keychain keychain1
local-identity address 2.2.2.1
match remote identity address 2.2.3.1 255.255.255.255
proposal 1
#
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
#
ike keychain keychain1
pre-shared-key address 2.2.3.1 255.255.255.0 key cipher $c$3$LXO7Pf3k1FxL1jfkO3moC7K747FDXR8fSg==
#
security-policy ip
rule 0 name AllPass
action pass
#
FWB:
#
nat address-group 1
address 10.1.3.1 10.1.3.1
#
policy-based-route huqi permit node 0
if-match acl 3000
apply next-hop 2.2.3.2
#
interface GigabitEthernet1/0/1
port link-mode route
description LAN
combo enable copper
ip address 10.1.1.1 255.255.255.0
//对对端主动发起的流量做源地址转换
nat outbound 3002 address-group 1
//对本端发起的流量做目的地址转换
nat server global 10.1.4.1 inside 10.1.1.2
ip policy-based-route huqi
#
interface GigabitEthernet1/0/2
port link-mode route
description WAN
combo enable copper
ip address 2.2.3.1 255.255.255.0
nat outbound 3001
ipsec apply policy use1
#
security-zone name Trust
import interface GigabitEthernet1/0/1
#
security-zone name Untrust
import interface GigabitEthernet1/0/2
#
ip route-static 0.0.0.0 0 2.2.3.2
#
acl advanced 3000
rule 0 permit ip source 10.1.1.0 0.0.0.255 destination 10.1.1.0 0.0.0.255
#
acl advanced 3001
rule 0 deny ip source 10.1.1.0 0.0.0.255 destination 10.1.1.0 0.0.0.255
rule 5 permit ip
#
acl advanced 3002
rule 0 permit ip source 10.1.1.2 0 destination 10.1.1.3 0
#
ipsec transform-set tran1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy use1 10 isakmp
transform-set tran1
security acl 3000
local-address 2.2.3.1
remote-address 2.2.2.1
ike-profile profile1
#
ike profile profile1
keychain keychain1
local-identity address 2.2.3.1
match remote identity address 2.2.2.1 255.255.255.255
proposal 1
#
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
#
ike keychain keychain1
pre-shared-key address 2.2.2.1 255.255.255.0 key cipher $c$3$ENS6gWDmdnktKQfRKaaMhCy7tBTExUQLzA==
#
ip http enable
ip https enable
#
security-policy ip
rule 0 name allpass
action pass
#
4.测试
PC4访问PC5:
<H3C>ping 10.1.3.1
Ping 10.1.3.1 (10.1.3.1): 56 data bytes, press CTRL_C to break
Request time out
56 bytes from 10.1.3.1: icmp_seq=1 ttl=253 time=4.000 ms
56 bytes from 10.1.3.1: icmp_seq=2 ttl=253 time=2.000 ms
56 bytes from 10.1.3.1: icmp_seq=3 ttl=253 time=3.000 ms
56 bytes from 10.1.3.1: icmp_seq=4 ttl=253 time=3.000 ms
--- Ping statistics for 10.1.3.1 ---
5 packet(s) transmitted, 4 packet(s) received, 20.0% packet loss
round-trip min/avg/max/std-dev = 2.000/3.000/4.000/0.707 ms
PC5访问PC4:
<H3C>ping 10.1.4.1
Ping 10.1.4.1 (10.1.4.1): 56 data bytes, press CTRL_C to break
56 bytes from 10.1.4.1: icmp_seq=0 ttl=253 time=8.000 ms
56 bytes from 10.1.4.1: icmp_seq=1 ttl=253 time=3.000 ms
56 bytes from 10.1.4.1: icmp_seq=2 ttl=253 time=2.000 ms
56 bytes from 10.1.4.1: icmp_seq=3 ttl=253 time=2.000 ms
56 bytes from 10.1.4.1: icmp_seq=4 ttl=253 time=3.000 ms
--- Ping statistics for 10.1.4.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 2.000/3.600/8.000/2.245 ms
在FWA端查看:
<H3C>dis ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
1 2.2.3.1 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
<H3C>dis ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/2
-------------------------------
-----------------------------
IPsec policy: map1
Sequence number: 10
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1444
Tunnel:
local address: 2.2.2.1
remote address: 2.2.3.1
Flow:
sour addr: 10.1.1.0/255.255.255.0 port: 0 protocol: ip
dest addr: 10.1.1.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 1645681406 (0x62171afe)
Connection ID: 4294967296
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843198/2252
Max received sequence-number: 19
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 688198837 (0x290514b5)
Connection ID: 4294967297
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843198/2252
Max sent sequence-number: 19
UDP encapsulation used for NAT traversal: N
Status: Active
在FWB端查看:
<H3C>dis ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
1 2.2.2.1 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
<H3C>dis ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/2
-------------------------------
-----------------------------
IPsec policy: use1
Sequence number: 10
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1444
Tunnel:
local address: 2.2.3.1
remote address: 2.2.2.1
Flow:
sour addr: 10.1.1.0/255.255.255.0 port: 0 protocol: ip
dest addr: 10.1.1.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 688198837 (0x290514b5)
Connection ID: 4294967296
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843198/2177
Max received sequence-number: 19
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 1645681406 (0x62171afe)
Connection ID: 4294967297
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843198/2177
Max sent sequence-number: 19
UDP encapsulation used for NAT traversal: N
Status: Active
PC4访问PC5,FW1的debug信息:
<H3C>*Jun 16 13:24:16:445 2020 H3C IPFW/7/IPFW_PACKET: -COntext=1;
Receiving, interface = GigabitEthernet1/0/1
version = 4, headlen = 20, tos = 0
pktlen = 84, pktid = 11, offset = 0, ttl = 255, protocol = 1
checksum = 41881, s = 10.1.1.2, d = 10.1.3.1
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
prompt: Receiving IP packet from interface GigabitEthernet1/0/1.
Payload: ICMP
type = 8, code = 0, checksum = 0xb406.
*Jun 16 13:24:16:445 2020 H3C NAT/7/COMMON: -COntext=1;
PACKET: (GigabitEthernet1/0/1-in-config) Protocol: ICMP
10.1.1.2: 169 - 10.1.3.1: 2048(VPN: 0) ------>
10.1.1.2: 169 - 10.1.1.3: 2048(VPN: 0)
*Jun 16 13:24:16:445 2020 H3C PBR4/7/PBR Forward Info: -COntext=1; Policy: huqi, Node: 0, match succeeded.
*Jun 16 13:24:16:445 2020 H3C PBR4/7/PBR Forward Info: -COntext=1; apply next-hop 2.2.2.2.
*Jun 16 13:24:16:446 2020 H3C IPFW/7/IPFW_PACKET: -COntext=1;
Sending, interface = GigabitEthernet1/0/2
version = 4, headlen = 20, tos = 0
pktlen = 136, pktid = 23, offset = 0, ttl = 255, protocol = 50
checksum = 45607, s = 2.2.2.1, d = 2.2.3.1
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
prompt: Sending IP packet from local at interface GigabitEthernet1/0/2.
Payload: F9 31 D4 B3 00 00 00 12 F3 7E DA 8A A0 88 21 C6 39 2C 1A 7C
*Jun 16 13:24:16:449 2020 H3C IPFW/7/IPFW_PACKET: -COntext=1;
Receiving, interface = GigabitEthernet1/0/2
version = 4, headlen = 20, tos = 0
pktlen = 136, pktid = 30, offset = 0, ttl = 254, protocol = 50
checksum = 45856, s = 2.2.3.1, d = 2.2.2.1
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
prompt: Receiving IP packet from interface GigabitEthernet1/0/2.
Payload: 14 47 02 DA 00 00 00 1A FB FF 97 88 A0 88 64 C6 DA 9C 85 53
*Jun 16 13:24:16:450 2020 H3C IPFW/7/IPFW_PACKET: -COntext=1;
Receiving, interface = GigabitEthernet1/0/2
version = 4, headlen = 20, tos = 0
pktlen = 84, pktid = 11, offset = 0, ttl = 254, protocol = 1
checksum = 42647, s = 10.1.1.3, d = 10.1.1.2
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
prompt: Receiving IP packet from interface GigabitEthernet1/0/2.
Payload: ICMP
type = 0, code = 0, checksum = 0xbc06.
*Jun 16 13:24:16:450 2020 H3C NAT/7/COMMON: -COntext=1;
PACKET: (GigabitEthernet1/0/1-out-session) Protocol: ICMP
10.1.1.3: 169 - 10.1.1.2: 0(VPN: 0) ------>
10.1.3.1: 169 - 10.1.1.2: 0(VPN: 0)
*Jun 16 13:24:16:450 2020 H3C IPFW/7/IPFW_PACKET: -COntext=1;
Sending, interface = GigabitEthernet1/0/1
version = 4, headlen = 20, tos = 0
pktlen = 84, pktid = 11, offset = 0, ttl = 253, protocol = 1
checksum = 42393, s = 10.1.3.1, d = 10.1.1.2
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
prompt: Sending IP packet received from interface GigabitEthernet1/0/2 at interface GigabitEthernet1/0/1.
Payload: ICMP
type = 0, code = 0, checksum = 0xbc06.
PC5访问PC4,FW2的debug信息:
[H3C]*Jun 16 13:13:14:601 2020 H3C IPFW/7/IPFW_PACKET: -COntext=1;
Receiving, interface = GigabitEthernet1/0/1
version = 4, headlen = 20, tos = 0
pktlen = 84, pktid = 11, offset = 0, ttl = 255, protocol = 1
checksum = 41624, s = 10.1.1.3, d = 10.1.4.1
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
prompt: Receiving IP packet from interface GigabitEthernet1/0/1.
Payload: ICMP
type = 8, code = 0, checksum = 0x1289.
*Jun 16 13:13:14:601 2020 H3C NAT/7/COMMON: -COntext=1;
PACKET: (GigabitEthernet1/0/1-in-config) Protocol: ICMP
10.1.1.3: 160 - 10.1.4.1: 2048(VPN: 0) ------>
10.1.1.3: 160 - 10.1.1.2: 2048(VPN: 0)
*Jun 16 13:13:14:601 2020 H3C PBR4/7/PBR Forward Info: -COntext=1; Policy: huqi, Node: 0, match succeeded.
*Jun 16 13:13:14:601 2020 H3C PBR4/7/PBR Forward Info: -COntext=1; apply next-hop 2.2.3.2.
*Jun 16 13:13:14:601 2020 H3C IPFW/7/IPFW_PACKET: -COntext=1;
Sending, interface = GigabitEthernet1/0/2
version = 4, headlen = 20, tos = 0
pktlen = 136, pktid = 19, offset = 0, ttl = 255, protocol = 50
checksum = 45611, s = 2.2.3.1, d = 2.2.2.1
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
prompt: Sending IP packet from local at interface GigabitEthernet1/0/2.
Payload: 14 47 02 DA 00 00 00 0F BB 75 13 3C 01 00 00 00 8D 06 32 34
*Jun 16 13:13:14:607 2020 H3C IPFW/7/IPFW_PACKET: -COntext=1;
Receiving, interface = GigabitEthernet1/0/2
version = 4, headlen = 20, tos = 0
pktlen = 136, pktid = 12, offset = 0, ttl = 254, protocol = 50
checksum = 45874, s = 2.2.2.1, d = 2.2.3.1
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
prompt: Receiving IP packet from interface GigabitEthernet1/0/2.
Payload: F9 31 D4 B3 00 00 00 07 3F FC 9D 55 01 00 00 00 55 32 79 4B
*Jun 16 13:13:14:607 2020 H3C IPFW/7/IPFW_PACKET: -COntext=1;
Receiving, interface = GigabitEthernet1/0/2
version = 4, headlen = 20, tos = 0
pktlen = 84, pktid = 11, offset = 0, ttl = 254, protocol = 1
checksum = 42647, s = 10.1.1.2, d = 10.1.1.3
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
prompt: Receiving IP packet from interface GigabitEthernet1/0/2.
Payload: ICMP
type = 0, code = 0, checksum = 0x1a89.
*Jun 16 13:13:14:607 2020 H3C NAT/7/COMMON: -COntext=1;
PACKET: (GigabitEthernet1/0/1-out-session) Protocol: ICMP
10.1.1.2: 160 - 10.1.1.3: 0(VPN: 0) ------>
10.1.4.1: 160 - 10.1.1.3: 0(VPN: 0)
*Jun 16 13:13:14:608 2020 H3C IPFW/7/IPFW_PACKET: -COntext=1;
Sending, interface = GigabitEthernet1/0/1
version = 4, headlen = 20, tos = 0
pktlen = 84, pktid = 11, offset = 0, ttl = 253, protocol = 1
checksum = 42136, s = 10.1.4.1, d = 10.1.1.3
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
prompt: Sending IP packet received from interface GigabitEthernet1/0/2 at interface GigabitEthernet1/0/1.
Payload: ICMP
type = 0, code = 0, checksum = 0x1a89.
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作



没有写错,先匹配NAT server进行目前地址转换,转换完之后就是ACL 3000中的内容,需要引流至从公网接口出,命中IPSEC 策略走隧道。 # interface GigabitEthernet1/0/1 port link-mode route description LAN combo enable copper ip address 10.1.1.1 255.255.255.0 //对对端主动发起的流量做源地址转换 nat outbound 3002 address-group 0 //对本端发起的流量做目的地址转换 nat server global 10.1.3.1 inside 10.1.1.3 ip policy-based-route huqi #