某局点S10504 ICMP报文不匹配策略路由的经验案例
- 0关注
- 1收藏 1827浏览
组网及说明
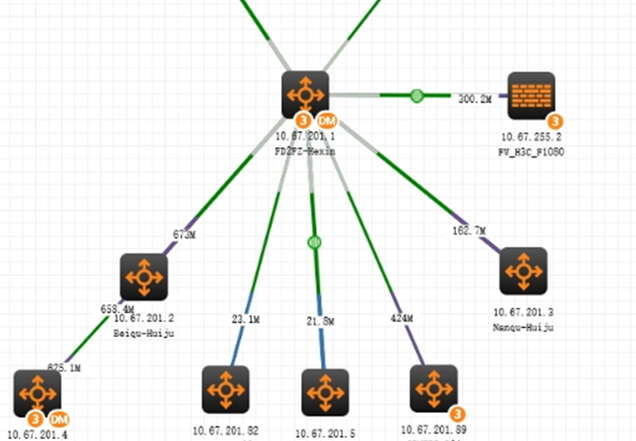
现场拓扑如上, 现场防火墙旁挂在核心交换机10504上,现场通过配置策略路由,想让内网终端访问交换机本身的流量也到防火墙上过一遍。
问题描述
现场流量路径大概如下,
1、终端流量上来到达interface Vlan-interface12接口,匹配ip policy-based-route to_fw的node20下一跳转到防火墙
interface Vlan-interface12
description TO-DHCP-client
ip address 10.67.96.1 255.255.240.0
ip policy-based-route to_fw
policy-based-route to_fw permit node 10
if-match acl 3900
#
policy-based-route to_fw permit node 20
if-match acl 3901
apply next-hop 10.67.255.2
apply default-next-hop 10.67.255.2
2、防火墙配置默认路由,指到交换机,流量回到交换机,
#
interface Route-Aggregation99//交换机与防火墙互联接口
ip address 10.67.255.1 255.255.255.252
ip policy-based-route fw_in
#
3、交换机回包时,匹配ip local policy-based-route local_to_fw,再指到防火墙上
policy-based-route local_to_fw permit node 20
if-match acl 3801
apply next-hop 10.67.255.2
apply default-next-hop 10.67.255.2
4、防火墙转回交换机上之后,交换机查路由转发给终端。
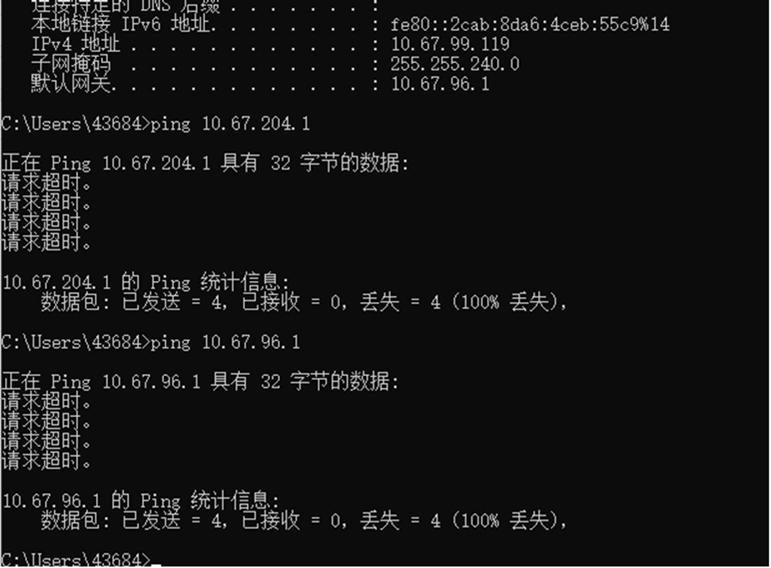
但是现场测试,终端ping不通交换机,但是SSH交换机是能通的。
过程分析
在终端ping不通交换机时,在防火墙上抓包,发现只有ICMP的回包
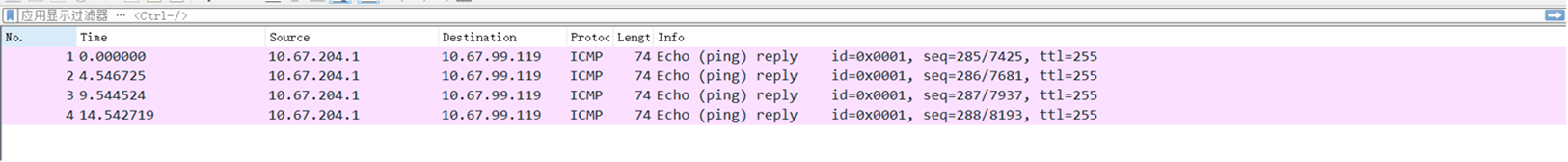
SSH交换机的时候,在防火墙上能看到完整的会话信息。即SSH报文正确匹配网关接口PBR转到了防火墙,且交换机回包也正常转给了防火墙,路径正确。
1.
2.是否被pbr匹配上,需要确认协议对应的底层acl是否有取消三层转发字段L3Switch Cancel L3Switch NextHopIndex 0x4001,icmp有该字段,不会被pbr抓走,而ssh无该字段,会被PBR抓走。
Ssh和Telnet规则
[ZLYY_WK_2F_IDC_Core_SW-probe]debug qacl show chassis 1 slot 0 c 0 verbose 0 sysidx 65
========
Acl-Type RX IPv4 Middle, Stage IFP, Pipe 0, Global, Installed, Active
Prio Mjr/Sub 524/18, Group 1 [1], Slice/Idx 8/42, Entry 46, Double: 6186/6698
Rule Match --------
Ports: 0x000000000000001fffe; 0x60000000000007fffff
Lookup: VLAN ID valid[y], STP forwarding, 0x1c, 0x1c
IP protocol: tcp
IP Type: Any IPv4 packet
L4 Dst Port: 23, 0xffff
Dest Port: CPU
DropBit: 0x0, Mask : 0x1
L3 Dest Class id: 0x20
Actions --------
CAR cir 0x200, cbs 0x800, pir 0x200, pbs 0x800, mode srTCM color blind,Bytes
Account mode packets, green and non-green
Change CPU pkt COS 27
Red Deny
Red_Copy_to_cpu : No
Yel Deny
Yel_Copy_to_cpu : No
MatchedName:65, TELNET/SSH
Accounting: Hi 0, LO 0
Imcp规则
[ZLYY_WK_2F_IDC_Core_SW-probe]debug qacl show chassis 1 slot 0 c 0 verbose 0 sysidx 44
========
Acl-Type RX IPv4 Middle, Stage IFP, Pipe 0, Global, Installed, Active
Prio Mjr/Sub 524/18, Group 1 [1], Slice/Idx 8/39, Entry 38, Double: 6183/6695
Rule Match --------
Ports: 0x000000000000001fffe; 0x60000000000007fffff
Lookup: VLAN ID valid[y], STP forwarding, 0x1c, 0x1c
IP protocol: icmp
IP Type: Any IPv4 packet
Dest Port: CPU
DropBit: 0x0, Mask : 0x1
SysmRule Index : 44
L3 Dest Class id: 0x20
My Station Hit
Actions --------
CAR cir 0x200, cbs 0x800, pir 0x200, pbs 0x800, mode srTCM color blind,Bytes
Account mode packets, green and non-green
L3Switch Cancel L3Switch NextHopIndex 0x4001
Change CPU pkt COS 22
Red Deny
Red_Copy_to_cpu : No
Yel Deny
Yel_Copy_to_cpu : No
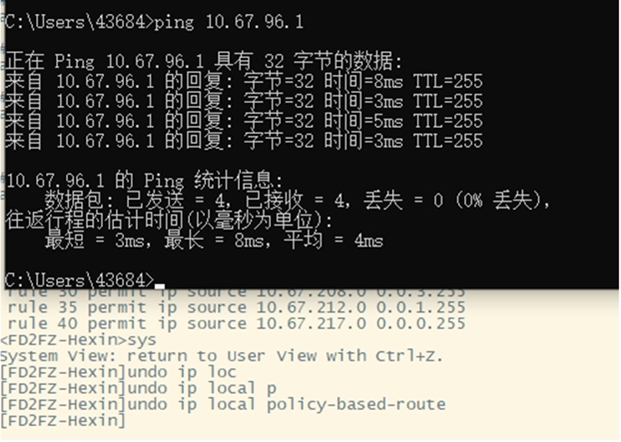
解决方法
现场想要终端能够正常ping通交换机的话,可以让访问本地的ICMP流量不经过防火墙,直接通过查找路由进行转发即可。可以修改 ip local policy-based-route local_to_fw,添加如下配置:
policy-based-route local_to_fw permit node 10
if-match acl 3800
rule 0 permit icmp
添加如上配置之后,终端访问交换机的ICMP流量到达交换机后,直接上送CPU进行处理,之后回包时,直接匹配本地PBR(
ip local policy-based-route local_to_fw
)的node10节点,通过查找路由转发,直接回复给终端,从而内网终端可以ping通交换机。
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作


