★ H3C to Cisco IPsec configuration(Main mode)
- 0关注
- 4收藏 2598浏览
Network Topology
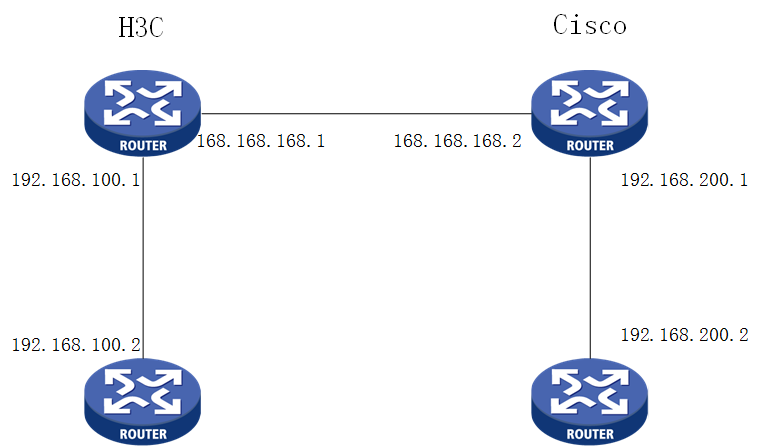
AS
Configuration Steps
H3C:
#
dhcp server ip-pool lan1
gateway-list 192.168.100.1
network 192.168.100.0 mask 255.255.255.0
address range 192.168.100.50 192.168.100.254
dns-list 8.8.8.8
#
interface Vlan-interface1
ip address 192.168.100.1 255.255.255.0
#
interface GigabitEthernet0/0
port link-mode route
description Single_Line1
ip address 168.168.168.1 255.255.255.252
packet-filter name GigabitEthernet0/0 inbound
nat outbound 3005
ipsec apply policy map1
#
#
line vty 0 63
authentication-mode scheme
user-role network-operator
#
ip route-static 192.168.200.0 24 168.168.168.2
#
acl advanced 3005
rule 0 deny ip source 192.168.100.0 0.0.0.255 destination 192.168.200.0 0.0.0.255 ////Use NAT to reject ipsec interested flow
#
acl advanced 3101
rule 0 permit ip source 192.168.100.0 0.0.0.255 destination 192.168.200.0 0.0.0.255//IPSEC interested flow
#
#
domain system
#
ipsec transform-set tran1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy map1 10 isakmp
transform-set tran1
security acl 3101
Local-address 168.168.168.1
remote-address 168.168.168.2
ike-profile profile1
#
ike profile profile1
keychain keychain1
local-identity address 168.168.168.1
match remote identity address 168.168.168.2 255.255.255.252
proposal 1
#
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
sa duration 3600
#
ike keychain keychain1
pre-shared-key address 168.168.168.2 255.255.255.252 key simple 12345678
#
CISCO:
ip dhcp pool LAN
network 192.168.200.0 255.255.255.0
default-router 192.168.200.1 //dhcp 网关
dns-server 8.8.8.8
!
!
!
crypto isakmp policy 20
encr 3des
hash md5
authentication pre-share
lifetime 3600
crypto isakmp key cisco123 address 168.168.168.1
!
!
crypto ipsec transform-set mysetto esp-3des esp-md5-hmac
!
crypto map mymap 20 ipsec-isakmp
set peer 168.168.168.1
set transform-set mysetto
match address 100
!
!
!
interface FastEthernet0/0
ip address 168.168.168.2 255.255.255.252
duplex auto
speed auto
crypto map mymap
!
interface FastEthernet0/1
ip address 192.168.200.1 255.255.255.0
duplex auto
speed auto
!
ip classless
ip route 192.168.100.0 255.255.255.0 168.168.168.1
!
access-list 100 permit ip 192.168.200.0 0.0.0.255 192.168.100.0 0.0.0.255 //acl
!
!
Key Configuration
1.The encryption and authentication algorithms configured on both sides must be consistent
2.ACL source and destination address is the subnet address
No comments
Add Comments:
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
