组网及说明
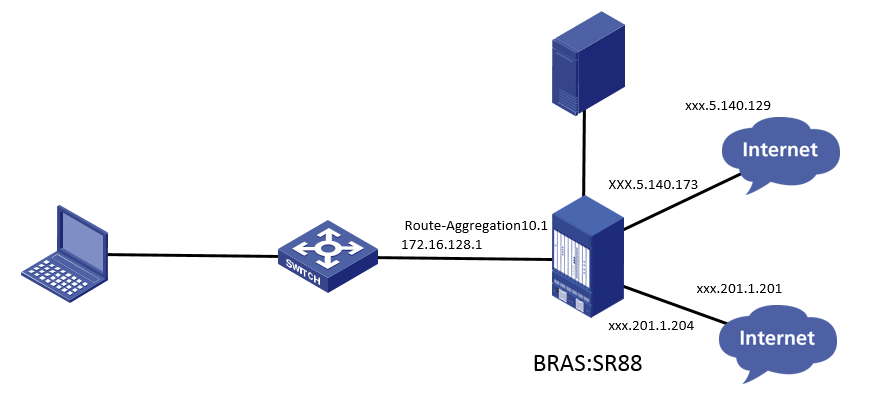
SR88在出口做bras,两个公网出口,需要使用内网用户IPOE WEB认证通过后,通过服务器下发不同的用户组,不同用户组的用户走不同的公网口出去
问题描述
现场内网终端IPOE认证通过后,服务器用户组user-group下发成功,通过PBR策略匹配用户组后,引流到不同公网出口,但是无法访问外网,取消PBR后能够访问外网
过程分析
首先查看设备配置及用户组下发情况
IPOE认证部分配置如下:
#
traffic classifier 1 operator and
if-match acl 2001
#
traffic classifier 2 operator and
if-match acl 2001
#
traffic classifier permit operator and
if-match acl name permit
#
traffic classifier web_deny operator and
if-match acl name ip
#
traffic classifier web_http operator and
if-match acl name web_http
#
traffic classifier web_https operator and
if-match acl name web_https
#
traffic classifier web_out operator and
if-match acl name web_out
#
traffic classifier web_permit operator and
if-match acl name web_permit
#
traffic behavior 1
redirect slot 2
#
traffic behavior 2
filter permit
free account
#
traffic behavior permit
filter deny
#
traffic behavior web_deny
filter deny
free account
#
traffic behavior web_http
redirect http-to-cpu
#
traffic behavior web_https
redirect https-to-cpu
#
traffic behavior web_out
filter permit
free account
#
traffic behavior web_permit
filter permit
free account
#
qos policy 1
classifier 1 behavior 1
#
qos policy 2
classifier 2 behavior 2
#
qos policy out
classifier web_out behavior web_out
classifier web_deny behavior web_deny
#
qos policy web
classifier web_permit behavior web_permit
classifier web_http behavior web_http
classifier web_https behavior web_https
classifier web_deny behavior web_deny
classifier 1 behavior 1
#
interface Route-Aggregation10.1
ip address 172.16.128.1 255.255.128.0
vlan-type dot1q vid 400 to 500 second-dot1q any
vlan-termination broadcast enable
dhcp server apply ip-pool pool_sf
ip policy-based-route nat
ip subscriber l2-connected enable
ip subscriber user-detect ip arp retry 2 interval 30
ip subscriber authentication-method web
ip subscriber pre-auth domain dm1
ip subscriber web-auth domain dm2
#
qos apply policy web global inbound 全局调用QOS放通需要放通的内网流量
qos apply policy out global outbound
#
acl basic 2000
rule 5 permit source 172.21.255.0 0.0.0.255
rule 10 permit source 172.16.0.0 0.0.255.255
#
acl basic 2001
rule 0 permit
#
acl advanced 3000
rule 5 permit ip source 172.16.128.0 0.0.0.255
#
acl advanced 3001
rule 5 permit ip source 172.16.129.0 0.0.0.255
#
acl advanced 3003
rule 5 permit ip
#
acl advanced name deny
rule 0 permit ip destination 172.21.255.3 0
rule 1 permit ip destination 172.21.255.4 0
rule 2 permit ip destination 172.21.255.2 0
rule 5 permit ip destination 172.16.128.1 0
#
acl advanced name dns
rule 5 permit ip destination 172.21.255.4 0
#
acl advanced name dns-cmcc
rule 0 permit ip destination xxx.201.4.3 0 user-group cmcc
rule 5 permit ip destination xxx.201.17.2 0 user-group cmcc
#
acl advanced name dns-unicom
rule 0 permit ip destination xxx.7.92.98 0 user-group unicom
rule 5 permit ip destination xxx.5.203.98 0 user-group unicom
#
acl advanced name ip
rule 0 permit ip user-group web
#
acl advanced name permit
rule 5 permit ip destination 172.16.0.0 0.0.128.255 user-group cmcc
rule 10 permit ip destination 172.16.0.0 0.0.128.255 user-group unicom
#
acl advanced name web_http
rule 0 permit tcp destination-port eq www user-group web
#
acl advanced name web_https
rule 0 permit tcp destination-port eq 443 user-group web
#
acl advanced name web_out
rule 0 permit ip source 172.21.255.3 0 user-group web
rule 5 permit ip source 172.21.255.4 0 user-group web
#
acl advanced name web_permit
rule 0 permit ip destination 172.21.255.3 0 user-group web
rule 5 permit ip destination 172.21.255.4 0 user-group web
#
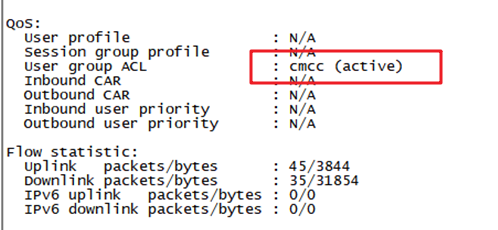
IPOE认证配置完成后,终端能够认证成功并且下发对应的用户组

用户组下发成功
接口取消调用PBR后能够认证成功访问互联网,接口调用PBR后无法访问外网
PBR配置如下:
匹配不同的用户组流量
acl advanced name unicom
rule 5 permit ip user-group Unicom
acl advanced name cmcc
rule 5 permit ip user-group cmcc
重定向到不同运营商出口
policy-based-route nat permit node 5
if-match acl name cmcc
apply next-hop xxx.201.1.201
#
policy-based-route nat permit node 10
if-match acl name unicom
apply next-hop xxx.5.140.129
#
policy-based-route nat deny node 15
if-match acl name deny
#
policy-based-route 1 permit node 1
if-match acl 3000
apply next-hop xxx.201.1.201
#
policy-based-route 1 permit node 2
if-match acl 3001
apply next-hop xxx.5.140.129
#
检查配置可以发现,全局多了一个c b对,最后一个CB对是用来对内网用户进行nat引流的,因为全局qos高于接口qos,所以先匹配了全局qos,导致接口的匹配不上。
qos policy web
classifier web_permit behavior web_permit
classifier web_http behavior web_http
classifier web_https behavior web_https
classifier web_deny behavior web_deny
classifier 1 behavior 1
#
traffic classifier 1 operator and
if-match acl 2001
traffic behavior 1
redirect slot 2
#
另外,设备既要做bras又要做nat引流,这种场景,无法实现,因为流量只能匹配并执行一种动作,需要配置防火墙插卡,或者将nat移到其他上行设备
解决方法
取消调用nat引流的CB对,使流量只匹配PBR策略进行重定向
另:如需实现IPOE认证下发不同用户组,不同用户组流量走不同公网口出去,在正常配置完IPOE认证及用户组相关配置后,建议使用QOS策略匹配对应用户组流量实现重定向
关键配置如下:
#
user-group group1
#
user-group group2
#
acl advanced 3030
rule 5 permit ip user-group group1
#
acl advanced 3040
rule 5 permit ip user-group group2
#
traffic classifier 3040 operator and
if-match acl 3040
#
traffic behavior 3030
accounting packet
redirect next-hop 3.3.3.2
#
traffic behavior 3040
accounting packet
redirect next-hop 5.5.5.2
#
qos policy plcy
……
classifier 3030 behavior 3030
classifier 3040 behavior 3040
#
interface GigabitEthernet3/1/1
qos apply policy plcy inbound
#
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
