组网及说明
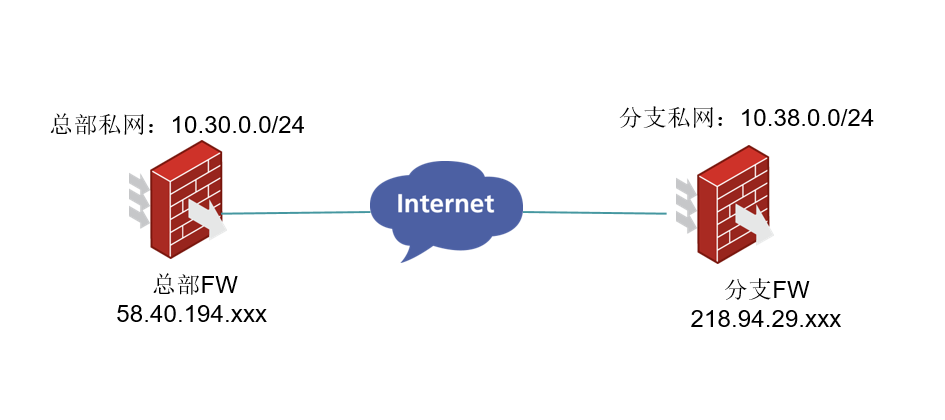
组网总部和多分支建立主模式ipsec,总部采用policy方式,图中只画了一个分支作为示例。
问题描述
总部F1000-AK145作为总部和多个分支建立ipsec,ike sa显示unknown。
<H3C-fenzhi>dis ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
68 58.40.194.xxx Unknown IPsec
过程分析
1、核对两端ike协商参数配置一致性检查,都使用的 3des-cbc和md5。
2、ike keychain的 pre-shared-key已经手动重新配置“123456”。
之前有遇到过*Nov 11 10:57:44:985 2014 M9K IKE/7/ERROR: -Chassis=2-Slot=3.1; 2th byte of the
structure ISAKMP Identification Payload must be 0.
由于配置了不对称的密钥,解密失败后,导致协商报文的载荷内容检查失败,就会报如上错误。
3、reset ike sa从新建立,依旧显示unknown。
收集两端debug信息发现如下报错:
Sending packet to 58.40.194.xxx remote port 500, local port 500.
*Nov 29 15:34:43:353 2021 H3C-FENZHI IKE/7/PACKET: -COntext=1; vrf = 0, local = 218.94.29.xxx, remote = 58.40.194.xxx/500
I-COOKIE: aa28397afd5e7218
R-COOKIE: 27cb92459a4b4a5a
next payload: ID //主模式ike 第5/6号报文载荷信息
version: ISAKMP Version 1.0
exchange mode: Main
flags: ENCRYPT
message ID: 0
length: 92
*Nov 29 15:34:43:354 2021 H3C-FENZHI IKE/7/PACKET: -COntext=1; vrf = 0, local = 218.94.29.xxx, remote = 58.40.194.xxx/500
Sending an IPv4 packet.
*Nov 29 15:34:43:354 2021 H3C-FENZHI IKE/7/EVENT: -COntext=1; vrf = 0, local = 218.94.29.xxx, remote = 58.40.194.xxx/500
Sent data to socket successfully.
*Nov 29 15:34:43:368 2021 H3C-FENZHI IKE/7/EVENT: -COntext=1; Received packet successfully.
*Nov 29 15:34:43:368 2021 H3C-FENZHI IKE/7/PACKET: -COntext=1; vrf = 0, local = 218.94.29.xxx, remote = 58.40.194.xxx/500
Received packet from 58.40.194.xxx source port 500 destination port 500.
*Nov 29 15:34:43:368 2021 H3C-FENZHI IKE/7/PACKET: -COntext=1; vrf = 0, local = 218.94.29.xxx, remote = 58.40.194.xxx/500
I-COOKIE: aa28397afd5e7218
R-COOKIE: 27cb92459a4b4a5a
next payload: HASH
version: ISAKMP Version 1.0
exchange mode: Info //表示报错报文
flags: ENCRYPT
message ID: 2c921d54
length: 76
*Nov 29 15:34:43:368 2021 H3C-FENZHI IKE/7/EVENT: -COntext=1; IKE thread 1099242853024 processes a job.
*Nov 29 15:34:43:368 2021 H3C-FENZHI IKE/7/EVENT: -COntext=1; Info packet process started.
*Nov 29 15:34:43:368 2021 H3C-FENZHI IKE/7/PACKET: -COntext=1; vrf = 0, local = 218.94.29.xxx, remote = 58.40.194.xxx/500
Decrypt the packet.
*Nov 29 15:34:43:369 2021 H3C-FENZHI IKE/7/PACKET: -COntext=1; vrf = 0, local = 218.94.29.xxx, remote = 58.40.194.xxx/500
Received ISAKMP Hash Payload.
*Nov 29 15:34:43:369 2021 H3C-FENZHI IKE/7/ERROR: -COntext=1; 2th byte of the structure ISAKMP Hash Payload must be 0.
//产生的报错代码
*Nov 29 15:34:43:369 2021 H3C-FENZHI IKE/7/ERROR: -COntext=1; vrf = 0, local = 218.94.29.xxx, remote = 58.40.194.xxx/500
Failed to parse informational exchange packet. Reason INVALID_PAYLOAD_TYPE.
*Nov 29 15:34:49:183 2021 H3C-FENZHI IKE/7/PACKET: -COntext=1; vrf = 0, local = 218.94.29.xxx, remote = 58.40.194.xxx/500
Retransmit phase 1 packet.
*Nov 29 15:34:49:183 2021 H3C-FENZHI IKE/7/PACKET: -COntext=1; vrf = 0, local = 218.94.29.xxx, remote = 58.40.194.xxx/500
Sending packet to 58.40.194.xxx remote port 500, local port 500.
*Nov 29 15:34:49:183 2021 H3C-FENZHI IKE/7/PACKET: -COntext=1; vrf = 0, local = 218.94.29.xxx, remote = 58.40.194.xxx/500
解决方法
检查总部配置发现,ipsec对应调用的ike profile如下:
ike profile GE1/0/4_IPv4_30
keychain GE1/0/4_IPv4_30
local-identity address 58.40.194.xxx
match remote identity address 218.94.29.xxx 255.255.255.255
match local address GigabitEthernet1/0/4
proposal 30 //现场调用的proposal
ike proposal 30
encryption-algorithm 3des-cbc
dh group5
authentication-algorithm md5
#设备还有一个相同加密参数的proposal被其他分支局点引用
ike proposal 10
encryption-algorithm 3des-cbc
dh group5
authentication-algorithm md5
经查证:
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
