组网及说明
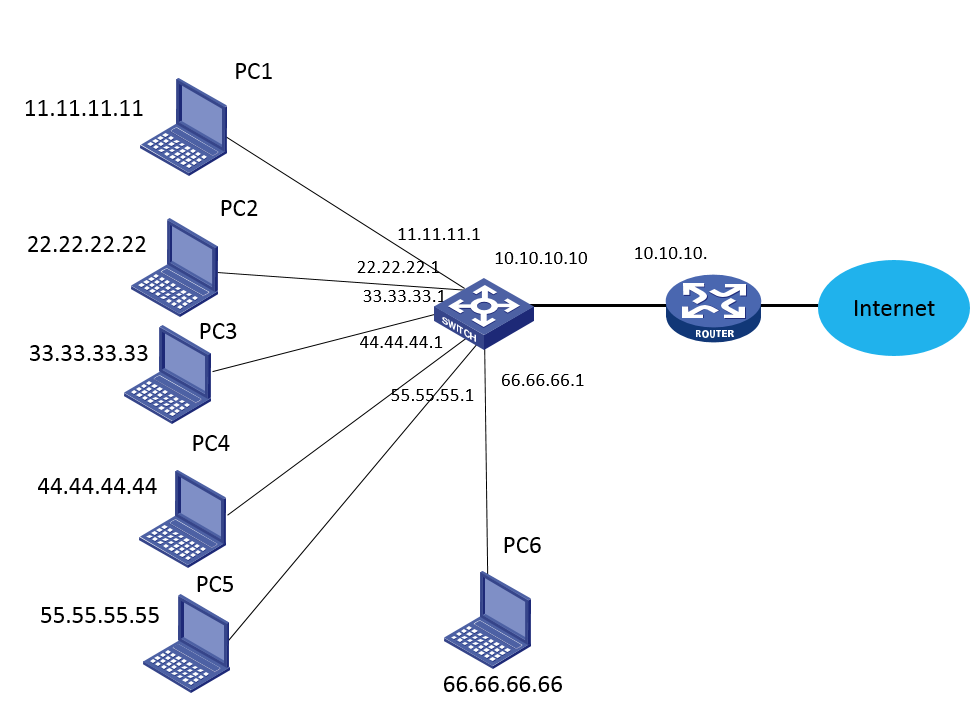
组网地址非实际地址
问题描述
BRAS使能IPOE web认证,有三层认证、二层认证、静态会话、DHCP触发
所有用户突然无法上网了,通过排查发现10.100.1.44和192.168.99.16 这两个dns服务器不通了导致所有用户无法上网,这两个ip正常情况是从3层认证过来的,接口为 ragg1.2,但查看IPOE会话发现,会话接口为ragg.1.800,此接口为二层认证接口
过程分析
查看设备在线信息
[zcmu-bras]dis ip subscriber session ip 192.168.99.16
Type: D-DHCP S-Static U-Unclassified-IP N-NDRS
Interface IP address MAC address Type State
IPv6 address SVLAN/CVLAN VXLAN
IPv6 PD prefix Username
RAGG1.800 192.168.99.16 542b-dedf-4201 S/- Online
- 800/- -
- 192.168.99.16
[zcmu-bras]dis ip subscriber session ip 192.168.99.16 ver
[zcmu-bras]dis ip subscriber session ip 192.168.99.16 verbose
Basic:
Description : server
Username : 192.168.99.16
Authorization domain : auth-free
Authentication domain : auth-free
VPN instance : N/A
IP address : 192.168.99.16
User address type : N/A
MAC address : 542b-dedf-4201
Service-VLAN/Customer-VLAN : 800/-
Access interface : RAGG1.800
User ID : 0x3822df06
VPI/VCI(for ATM) : -/-
VSI Index : -
VSI link ID : -
VXLAN ID : -
DNS servers : N/A
IPv6 DNS servers : N/A
DHCP lease : N/A
DHCP remain lease : N/A
Access time : Mar 8 06:25:10 2021
Online time(hh:mm:ss) : 03:43:55
Service node : Slot 1 CPU 0
Authentication type : Web pre-auth
IPv4 access type : Static
IPv4 detect state : Detecting
State : Online
此时查看BRAS ARP,MAC地址依旧是与三层认证ragg1.2互联的核心交换机三层接口MAC,会话MAC也是这个mac,即使确实存在终端漫游或者IP地址冲突的情况,新产生的会话MAC地址也应该是终端的实际mac才对,现场ragg1.2口IPOE认证功能关闭后,清空192.168.99.16的IPOE会话,还是会产生新的会话,接口是ragg.1800,将接口1.800 shutdown在开启来之后,99.16这个ip的IPOE会话就不产生了
<zcmu-bras>dis arp | include 542b-dedf-4201
192.168.255.254 542b-dedf-4201 -- RAGG1.1 13 D
192.168.254.249 542b-dedf-4201 -- RAGG1.2 13 D
10.100.1.44 542b-dedf-4201 -- RAGG1.800 -- R
172.20.176.76 542b-dedf-4201 -- RAGG1.800 -- R
192.168.99.16 542b-dedf-4201 -- RAGG1.800 -- R
Basic:
Description : server
Username : 192.168.99.16
Authorization domain : auth-free
Authentication domain : auth-free
VPN instance : N/A
IP address : 192.168.99.16
User address type : N/A
MAC address : 542b-dedf-4201
Service-VLAN/Customer-VLAN : 800/-
Access interface : RAGG1.800
User ID : 0x3822df06
另外日志里有报IP地址冲突
%@89457%Mar 8 06:25:10:563 2021 zcmu-bras ARP/4/ARP_HOST_IP_CONFLICT: The host 192.168.99.16 connected to interface Route-Aggregation1.800 cannot communicate correctly, because it uses the same IP address as the host connected to interface Route-Aggregation1.2.
这个现象一直存在,是因为DNS的会话异常导致全部用户无法上网,才发现这个问题,另外看日志报地址冲突的IP全都是静态会话的IP地址
后把 1.2 接口认证开起来了,发现还是有会话冲突的情况,例如172.16.46.1 同时从 ragg1.2 和 xg0/0/4.1 上来了,0/0/4.1 下面是接的一个测试的交换机(没有用户),不可能有这个ip段的。ipoe会话匹配错了
<zcmu-bras>dis ip subscriber session ip 172.16.46.1
Type: D-DHCP S-Static U-Unclassified-IP N-NDRS
Interface IP address MAC address Type State
IPv6 address SVLAN/CVLAN VXLAN
IPv6 PD prefix Username
RAGG1.2 172.16.46.1 542b-dedf-4201 S/- Online
- 300/- -
- DHCP-l3defpre
XGE0/0/4.1 172.16.46.1 4077-a921-d71c S/- Online
- 4000/- -
- DHCP-l3defpre
<zcmu-bras>dis ip rou
<zcmu-bras>dis ip routing-table 172.16.46.1
Summary count : 2
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/0 Static 60 0 192.168.255.70 RAGG1.1
172.16.0.0/12 Static 60 0 192.168.254.249 RAGG1.2
%Mar 8 13:47:42:802 2021 zcmu-bras ARP/4/ARP_HOST_IP_CONFLICT: The host 172.20.10.2 connected to interface Route-Aggregation1.805 cannot communicate correctly, because it uses the same IP address as the host connected to interface Route-Aggregation1.815.
%Mar 8 13:49:52:283 2021 zcmu-bras SHELL/6/SHELL_CMD: -Line=vty1-IPAddr=172.16.127.16-User=admin; Command is ip subscriber routed enable
%Mar 8 13:49:52:378 2021 zcmu-bras ARP/4/ARP_HOST_IP_CONFLICT: The host 172.16.41.90 connected to interface Route-Aggregation1.2 cannot communicate correctly, because it uses the same IP address as the host connected to interface Ten-GigabitEthernet0/0/4.1.
%Mar 8 13:49:52:420 2021 zcmu-bras ARP/4/ARP_HOST_IP_CONFLICT: The host 172.16.46.1 connected to interface Route-Aggregation1.2 cannot communicate correctly, because it uses the same IP address as the host connected to interface Ten-GigabitEthernet0/0/4.1.
后续排查总结如下
1、诊断中多处dns指定为remote-server,这个是配错了还是dns同时也作为dhcp服务器。
dhcp server ip-pool vlan-2110
gateway-list 10.100.16.254 export-route
remote-server 192.168.99.16 10.100.1.44
#
dhcp server ip-pool vlan-2111
gateway-list 10.100.17.254 export-route
remote-server 192.168.99.16 10.100.1.44
dhcp server ip-pool vlan-110
gateway-list 172.19.191.254 export-route
network 172.19.128.0 mask 255.255.192.0
dns-list 10.100.1.44 192.168.99.16
#
dhcp server ip-pool vlan-805
gateway-list 172.20.159.254 export-route
network 172.20.144.0 mask 255.255.240.0
dns-list 10.100.1.44 192.168.99.16
#
2、看现象就是地址冲突导致,怀疑下联交换上有配置vlan-interface 800,使得该接口也有发报文到设备,当该虚接口先发报文到设备时,便以该mac触发了会话,后续通过vlan300 三层口上来的认证,因为交换机的mac地址已经在R1.800口下建立会话,便不会重新建立会话,导致不通。(因为这种情况下interface-vlan800和interface-vlan300的mac相同)
如果是这种情况,需要交换机接口下关闭vlan-interface 800,只放通vlan800即可,没必要创建该虚接口。
最后定为为很多网段全局的静态会话所用的域都相同,且大都共用聚合组1的子接口。现场在绑定全局静态会话中指明接口后会话正常。
ip subscriber session static ip 192.168.98.1 192.168.98.254 domain auth-free interface Route-Aggregation 1.2 description server
ip subscriber session static ip 192.168.99.1 192.168.99.254 domain auth-free interface Route-Aggregation 1.2 description server
解决方法
造成冲突的原因是下联二层放通的接口混乱,同一个终端可以从多个接口到达设备,造成多个接口均生成ipoe会话
现场在绑定全局静态会话中指明接口,从其他接口上来的报文不处理规避,后续可排查交换机二层放通的情况,合理规划接口放通的vlan
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
