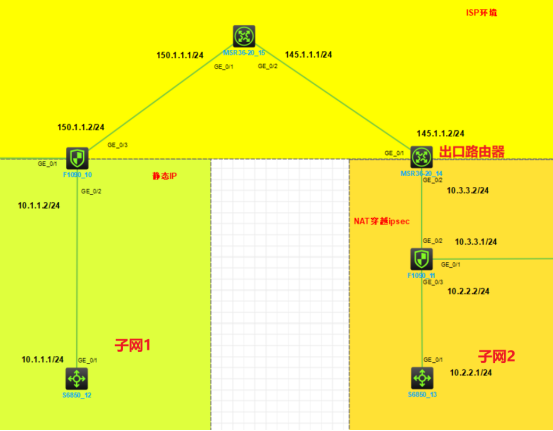
组网及说明
本案例采用H3C HCL模拟器的F1090防火墙来模拟IPSEC NAT穿越的典型组网配置。在网络拓扑图中存在子网1和子网2。为了保障子网1和子网2相互传输数据的安全性,因此需要在FW10与FW11采用建立IPSEC VPN隧道,由于FW11的出接口地址不固定且出口路由器为NAT设备,因此采用IKE野蛮模式。
配置步骤
1、按照网络拓扑图正确配置IP地址,确保主干链路网络互通正常
2、FW10,FW11和出口路由器均配置NAT
3、FW10与FW11的互联接口加入安全域,并放通域间策略
4、FW1与FW2建立IPSEC VPN隧道,采用IKE野蛮模式
配置关键点
一、主要设备的配置(web和命令行)
出口路由器:
interface GigabitEthernet0/1 //配置接口地址和接口SNAT
port link-mode route
combo enable copper
ip address 145.1.1.2 255.255.255.0
nat outbound 3000
#
interface GigabitEthernet0/2 //配置接口地址
port link-mode route
combo enable copper
ip address 10.3.3.2 255.255.255.0
#
ip route-static 0.0.0.0 0 145.1.1.1 //默认路由
#
acl advanced 3000 //定义用于SNAT的ACL
rule 1 permit ip counting
FW10:


interface GigabitEthernet1/0/2 //定义内网口
port link-mode route
combo enable copper
ip address 10.1.1.2 255.255.255.0
#
interface GigabitEthernet1/0/3 //定义外网口和应用ipsec策略
port link-mode route
combo enable copper
ip address 150.1.1.2 255.255.255.0
ipsec apply policy 和对端pppoe建立
#
security-zone name Trust //内网接口加入Trust区域
import interface GigabitEthernet1/0/2
#
security-zone name Untrust //外网接口加入Untrust区域
import interface GigabitEthernet1/0/3
#
ip route-static 0.0.0.0 0 150.1.1.1 //默认路由
#
acl advanced name IPsec_和对端pppoe建立_IPv4_1 //感兴趣流网段的ACL
rule 0 permit ip source 10.1.1.0 0.0.0.255 destination 10.2.2.0 0.0.0.255
#
ipsec transform-set 和对端pppoe建立_IPv4_1 //ipsec转换流,aes-cbc-128加密,sha1认证方式,均为默认
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec policy 和对端pppoe建立 1 isakmp //ipsec策略,包括ipsec转化流,感兴趣网段,IP标识,ike模板
transform-set 和对端pppoe建立_IPv4_1
security acl name IPsec_和对端pppoe建立_IPv4_1
local-address 150.1.1.2
remote-address 145.1.1.2
description 对端公网地址
ike-profile 和对端pppoe建立_IPv4_1
sa trigger-mode auto
#
nat global-policy //配置全局策略NAT,第一条排除感兴趣网段,第二条是允许内网访问外网
rule name 禁止感兴网段
source-ip subnet 10.1.1.0 24
destination-ip subnet 10.2.2.0 24
action snat no-nat
counting enable
rule name SNAT
action snat easy-ip
counting enable
#
ike profile 和对端pppoe建立_IPv4_1 //IKE模板,引用秘钥参数,野蛮模式,本端和对端地址,ike提议等
keychain 和对端pppoe建立_IPv4_1
exchange-mode aggressive
local-identity address 150.1.1.2
match remote identity address 145.1.1.2 255.255.255.255
match local address GigabitEthernet1/0/3
proposal 1
#
ike proposal 1 //新建了IKE提议1,和default提议参数一致
#
ike keychain 和对端pppoe建立_IPv4_1 //IKE秘钥参数
match local address GigabitEthernet1/0/3
pre-shared-key address 145.1.1.2 255.255.255.255 key cipher $c$3$LuD7NdgcyP4upvaTM1YEo+w3VVTY6g==
#
security-policy ip //全放通的安全策略
rule 0 name 1
action pass
FW11:


interface GigabitEthernet1/0/2 //定义外网口和应用ipsec策略
port link-mode route
combo enable copper
ip address 10.3.3.1 255.255.255.0
ipsec apply policy 和对端公网建立
#
interface GigabitEthernet1/0/3 //定义内网口
port link-mode route
combo enable copper
ip address 10.2.2.2 255.255.255.0
#
security-zone name Trust //内网接口加入Trust区域
import interface GigabitEthernet1/0/3
#
security-zone name Untrust //外网接口加入Untrust区域
import interface GigabitEthernet1/0/2
#
ip route-static 0.0.0.0 0 10.3.3.2 //默认路由
#
acl advanced name IPsec_和对端公网建立_IPv4_1 //感兴趣流网段的ACL
rule 0 permit ip source 10.2.2.0 0.0.0.255 destination 10.1.1.0 0.0.0.255
#
ipsec transform-set 和对端公网建立_IPv4_1 //ipsec转换流,aes-cbc-128加密,sha1认证方式,均为默认
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec policy 和对端公网建立 1 isakmp //ipsec策略,包括ipsec转化流,感兴趣网段,IP标识,ike模板
transform-set 和对端公网建立_IPv4_1
security acl name IPsec_和对端公网建立_IPv4_1
local-address 10.3.3.1
remote-address 150.1.1.2
description 对端公网地址
ike-profile 和对端公网建立_IPv4_1
sa trigger-mode auto
#
nat global-policy //配置全局策略NAT,第一条排除感兴趣网段,第二条是允许内网访问外网
rule name 禁止感兴网段
source-ip subnet 10.2.2.0 24
destination-ip subnet 10.1.1.0 24
action snat no-nat
counting enable
rule name SNAT
action snat easy-ip
counting enable
#
ike profile 和对端公网建立_IPv4_1 //IKE模板,引用秘钥参数,野蛮模式,本端和对端地址,ike提议等
keychain 和对端公网建立_IPv4_1
exchange-mode aggressive
local-identity address 145.1.1.2
match remote identity address 150.1.1.2 255.255.255.255
match local address GigabitEthernet1/0/2
proposal 2
#
ike proposal 2 //新建了IKE提议1,和default提议参数一致
#
ike keychain 和对端公网建立_IPv4_1 //IKE秘钥参数
match local address GigabitEthernet1/0/2
pre-shared-key address 150.1.1.2 255.255.255.255 key cipher $c$3$TMdccoAEkBSoOFeQp57RqcEym2Rnlw==
#
security-policy ip //全放通的安全策略
rule 0 name 1
action pass
二、底层完整文件
见附件
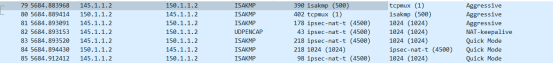
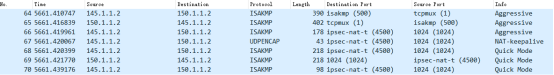
三、抓包查看
FW10(完整包见附件):
出口路由器(完整包见附件):
四、验证数据流是否正常
1、在防火墙上查看第一阶段和第二阶段SA
<FW10>dis ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
9 145.1.1.2/1024 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
<FW10>dis ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/3
-------------------------------
-----------------------------
IPsec policy: 和对端pppoe建立
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Transmitting entity: Responder
Path MTU: 1420
Tunnel:
local address: 150.1.1.2
remote address: 145.1.1.2
Flow:
sour addr: 10.1.1.0/255.255.255.0 port: 0 protocol: ip
dest addr: 10.2.2.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 1752173956 (0x68700d84)
Connection ID: 4294967298
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/1044
Max received sequence-number: 0
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: Y
Status: Active
[Outbound ESP SAs]
SPI: 2852432862 (0xaa04abde)
Connection ID: 4294967299
Transform set: ESP-ENCRYPT-AES-CBC-128 ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/1044
Max sent sequence-number: 0
UDP encapsulation used for NAT traversal: Y
Status: Active
2、内网互访
<SW12>ping 10.2.2.1
Ping 10.2.2.1 (10.2.2.1): 56 data bytes, press CTRL+C to break
56 bytes from 10.2.2.1: icmp_seq=0 ttl=253 time=2.000 ms
56 bytes from 10.2.2.1: icmp_seq=1 ttl=253 time=2.000 ms
56 bytes from 10.2.2.1: icmp_seq=2 ttl=253 time=2.000 ms
56 bytes from 10.2.2.1: icmp_seq=3 ttl=253 time=2.000 ms
56 bytes from 10.2.2.1: icmp_seq=4 ttl=253 time=2.000 ms
--- Ping statistics for 10.2.2.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 2.000/2.000/2.000/0.000 ms
<SW12>%Dec 17 18:05:06:303 2022 SW12 PING/6/PING_STATISTICS: Ping statistics for 10.2.2.1: 5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss, round-trip min/avg/max/std-dev = 2.000/2.000/2.000/0.000 ms.
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
