组网及说明
不涉及
告警信息
不涉及
问题描述
ASPF(Advanced Stateful Packet Filter,高级状态包过滤)是为了解决包过滤防火墙存在的问题而提出的概念,主要功能有
· 应用层协议检测:检查应用层协议信息,如报文的协议类型和端口号等信息,并且监控每一个连接的应用层协议状态。对于所有连接,每一个连接状态信息都将被ASPF维护,并用于动态地决定数据包是否被允许通过防火墙进入内部网络,以阻止恶意的入侵。
· 传输层协议检测:检测传输层协议信息,包括TCP协议、UDP协议、UDP-Lite协议、SCTP协议、Raw IP协议、ICMP协议、ICMPv6协议和DCCP协议。例如TCP/UDP检测,能够根据源、目的地址及端口号决定TCP或UDP报文是否可以通过防火墙进入内部网络。
· ICMP差错报文检测:正常ICMP差错报文中均携带有本报文对应连接的相关信息,根据这些信息可以匹配到相应的连接。如果匹配失败,则根据当前配置决定是否丢弃该ICMP报文。
· TCP连接首包检测:对TCP连接的首报文进行检测,查看是否为SYN报文,如果不是SYN报文则根据当前配置决定是否丢弃该报文。缺省情况下,不丢弃非SYN首包,适用于不需要严格TCP协议状态检查的组网场景。例如当防火墙设备首次加入网络时,网络中原有TCP连接的非首包在经过新加入的设备时如果被丢弃,会中断已有的连接,造成不好的用户体验,因此建议暂且不丢弃非SYN首包,等待网络拓扑稳定后,再开启非SYN首包丢弃功能。
对于ASPF的研究可以参考该案例:H3C防火墙ASPF状态检测机制
本案例针对TCP协议简述防火墙处理流程
过程分析
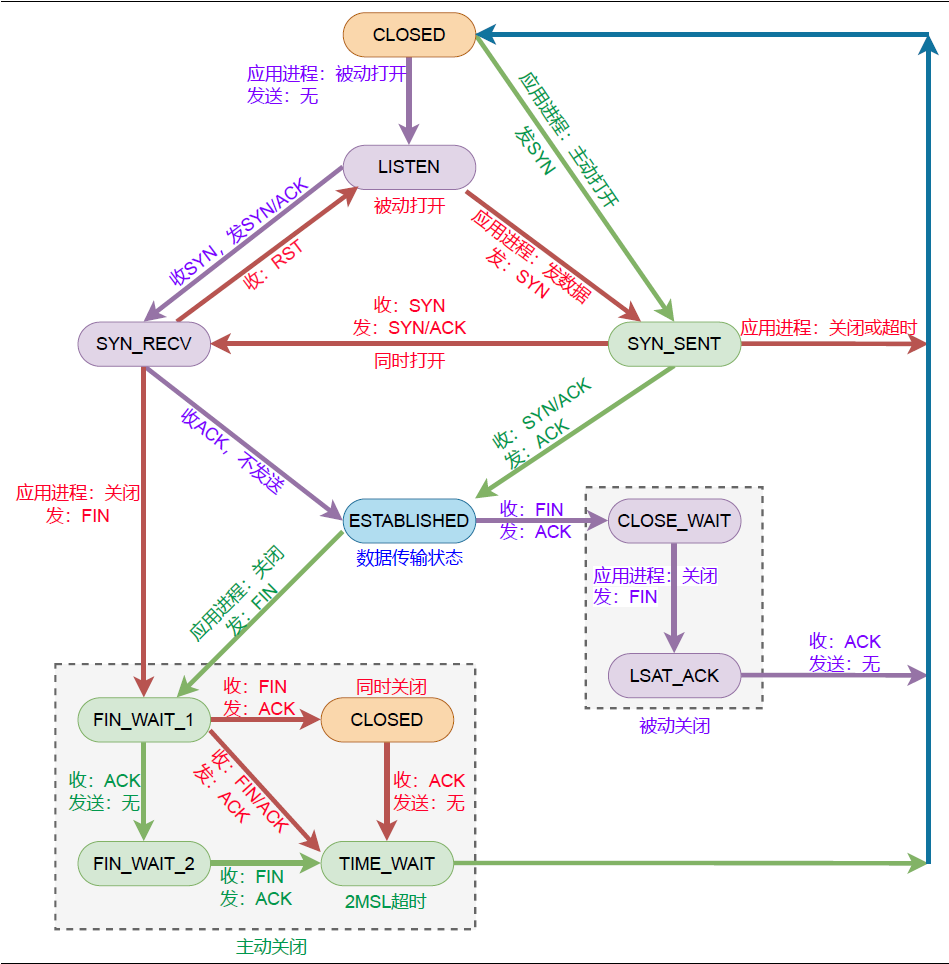
常见的TCP状态机流程图如下:
先说结论,目前防火墙默认syn包,和ack报文在策略允许的情况下可以建立会话,syn+ack,fin+ack,reset+ack不可以建立会话。
syn包建立会话以及syn/ack无法建立会话这些观点应该没有问题,下面测试ack报文能否建立会话:
Receiving, interface = M-GigabitEthernet1/0/0/0
version = 4, headlen = 20, tos = 0
pktlen = 40, pktid = 53008, offset = 0, ttl = 128, protocol = 6
checksum = 56064, s = 10.153.43.154, d = 10.63.16.77
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
VsysID = 1
prompt: Receiving IP packet from interface M-GigabitEthernet1/0/0/0.
Payload: TCP
source port = 4151, destination port = 80
sequence num = 0x270bd60e, acknowledgement num = 0xd89bde2f, flags = 0x10
window size = 65535, checksum = 0x9aa9, header length = 20.
*Jan 13 18:45:06:648 2024 F5080D_1 SESSION/7/TABLE:
Tuple5(EVENT): 10.153.43.154/4151-->10.63.16.77/80(TCP(6))
Session entry was created.
*Jan 13 18:45:06:648 2024 F5080D_1 FILTER/7/PACKET: The packet is permitted. Src-ZOne=Management, Dst-ZOne=DMZ;If-In=M-GigabitEthernet1/0/0/0(325), If-Out=Route-Aggregation1.100(337); Packet Info:Src-IP=10.153.43.154, Dst-IP=10.63.16.77, VPN-Instance=, Src-MacAddr=0024-e8ae-161f,Src-Port=4151, Dst-Port=80, Protocol=TCP(6), Application=http(31),Terminal=invalid(0), Url-category=invalid(65535), SecurityPolicy=any, Rule-ID=0.
*Jan 13 18:45:06:648 2024 F5080D_1 IPFW/7/IPFW_PACKET:
Sending, interface = Route-Aggregation1.100
version = 4, headlen = 20, tos = 0
pktlen = 40, pktid = 53008, offset = 0, ttl = 127, protocol = 6
checksum = 56320, s = 10.153.43.154, d = 10.63.16.77
channelID = 0, vpn-InstanceIn = 0, vpn-InstanceOut = 0.
VsysID = 1
prompt: Sending IP packet received from interface M-GigabitEthernet1/0/0/0 at interface Route-Aggregation1.100.
Payload: TCP
source port = 4151, destination port = 80
sequence num = 0x270bd60e, acknowledgement num = 0xd89bde2f, flags = 0x10
window size = 65535, checksum = 0x9aa9, header length = 20.
查看会话计数,确实收到一个报文就建立会话:
RBM_P<F5080D_1>disp session ta ipv4 dest 80 v
Slot 0 in chassis 1:
Initiator:
Source IP/port: 10.153.43.154/4151
Destination IP/port: 10.63.16.77/80
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: M-GigabitEthernet1/0/0/0
Source security zone: Management
Responder:
Source IP/port: 10.63.16.77/80
Destination IP/port: 10.153.43.154/4151
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: Route-Aggregation1.100
Source security zone: DMZ
State: TCP_ESTABLISHED
Application: HTTP
Rule ID: 0
Rule name: any
Start time: 2024-01-13 18:45:06 TTL: 1194s
Initiator->Responder: 1 packets 40 bytes
Responder->Initiator: 0 packets 0 bytes
如果收到正向的syn报文能否转发呢,答案是可以:
RBM_P<F5080D_1>disp session ta ipv4 dest 80 v
Slot 0 in chassis 1:
Initiator:
Source IP/port: 10.153.43.154/4151
Destination IP/port: 10.63.16.77/80
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: M-GigabitEthernet1/0/0/0
Source security zone: Management
Responder:
Source IP/port: 10.63.16.77/80
Destination IP/port: 10.153.43.154/4151
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: Route-Aggregation1.100
Source security zone: DMZ
State: TCP_ESTABLISHED
Application: HTTP
Rule ID: 0
Rule name: any
Start time: 2024-01-13 18:45:06 TTL: 1196s
Initiator->Responder: 2 packets 88 bytes
Responder->Initiator: 0 packets 0 bytes
如果收到反向的syn/ack或者syn能否转发呢,答案还是可以。
RBM_P<F5080D_1>disp session ta ipv4 dest 80 v
Slot 0 in chassis 1:
Initiator:
Source IP/port: 10.153.43.154/4151
Destination IP/port: 10.63.16.77/80
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: M-GigabitEthernet1/0/0/0
Source security zone: Management
Responder:
Source IP/port: 10.63.16.77/80
Destination IP/port: 10.153.43.154/4151
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: Route-Aggregation1.100
Source security zone: DMZ
State: TCP_ESTABLISHED
Application: HTTP
Rule ID: 0
Rule name: any
Start time: 2024-01-13 18:45:06 TTL: 1171s
Initiator->Responder: 2 packets 88 bytes
Responder->Initiator: 1 packets 48 bytes
---------------------------------------------------------------------------------
Slot 0 in chassis 1:
Initiator:
Source IP/port: 10.153.43.154/4151
Destination IP/port: 10.63.16.77/80
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: M-GigabitEthernet1/0/0/0
Source security zone: Management
Responder:
Source IP/port: 10.63.16.77/80
Destination IP/port: 10.153.43.154/4151
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: Route-Aggregation1.100
Source security zone: DMZ
State: TCP_ESTABLISHED
Application: HTTP
Rule ID: 0
Rule name: any
Start time: 2024-01-13 18:45:06 TTL: 1193s
Initiator->Responder: 2 packets 88 bytes
Responder->Initiator: 2 packets 96 bytes
解决方法
有些友商的机制和我司实现并不相同,譬如:
|
协议 |
开启状态检测功能 |
关闭状态检测功能 |
|
|---|---|---|---|
|
TCP |
SYN报文 |
创建会话,转发报文 |
创建会话,转发报文 |
|
SYN+ACK、ACK报文 |
不创建会话,丢弃报文 |
创建会话,转发报文 |
|
我司可以使用如下命令配置ACK报文无法建立会话:
tcp syn-check命令用来开启非SYN的TCP首报文丢弃功能。
undo tcp syn-check命令用来关闭非SYN的TCP首报文丢弃功能。
【命令】
tcp syn-check
undo tcp syn-check
【缺省情况】
非SYN的TCP首报文丢弃功能处于关闭状态。
【视图】
ASPF策略视图
【缺省用户角色】
network-admin
mdc-admin
vsys-admin
【使用指导】
ASPF对TCP连接的首报文进行检测,查看是否为SYN报文,如果不是SYN报文则根据当前配置决定是否丢弃该报文。
当设备首次加入网络时,网络中原有TCP连接的非首包在经过新加入的设备时如果被丢弃,会中断已有的连接,造成不好的用户体验,因此建议暂且不丢弃非SYN首包,等待网络拓扑稳定后,再开启非SYN首包丢弃功能。
【举例】
# 设置ASPF策略1丢弃非SYN的TCP首报文。
<Sysname> system-view
[Sysname] aspf policy 1
[Sysname-aspf-policy-1] tcp syn-check
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
