WX系列Rogue AP的检测和反制
一、组网需求

本配置举例中AC使用WX3024无线控制器,版本为3120p13。AC作为AP的网关(Vlan-int1:192.168.1.254/24),配置DHCP Server地址池为Fit AP分配IP地址,并作为STA的网关(Vlan-int10:192.168.10.254/24)配置DHCP Server地址池为Client 分配IP地址。AP的交换模板使能POE功能,为AP供电
二、配置步骤
一、AC侧配置
[WX3024]dis cu
#
version 5.20, Release 3120P13
#
sysname WX3024
#
domain default enable system
#
telnet server enable
#使能端口安全
port-security enable
#
oap management-ip 192.168.0.101 slot 0
#
password-recovery enable
#管理vlan
vlan 1
#业务vlan
vlan 10
#
domain system
access-limit disable
state active
idle-cut disable
self-service-url disable
#AP注册地址池
dhcp server ip-pool pool-ap
network 192.168.1.0 mask 255.255.255.0
gateway-list 192.168.1.254
#业务地址池
dhcp server ip-pool pool-client
network 192.168.10.0 mask 255.255.255.0
gateway-list 192.168.10.254
dns-list 8.8.8.8
#
user-group system
group-attribute allow-guest
#
local-user admin
password cipher $c$3$Rpm6XcShL5Ye3Uaq4F7d5RiMqjB7eI+Z
authorization-attribute level 3
service-type telnet
#
wlan rrm
dot11a mandatory-rate 6 12 24
dot11a supported-rate 9 18 36 48 54
dot11b mandatory-rate 1 2
dot11b supported-rate 5.5 11
dot11g mandatory-rate 1 2 5.5 11
dot11g supported-rate 6 9 12 18 24 36 48 54
#配置无线服务模板
wlan service-template 1 clear
ssid www
bind WLAN-ESS 1
service-template enable
#
wlan ap-group default_group
ap ap1
ap ap2
ap ap3
#
interface NULL0
#
interface Vlan-interface1
ip address 192.168.1.254 255.255.255.0
#
interface Vlan-interface10
ip address 192.168.10.254 255.255.255.0
#
interface GigabitEthernet1/0/1
#设置无线虚接口
interface WLAN-ESS1
port access vlan 10
#创建AP管理模板
wlan ap ap1 model WA2612-AGN id 1
serial-id 210235A35WB09C000028
device-detection enable
radio 1
max-power 10
service-template 1
radio enable
#进入wlan ids视图进行相关配置
wlan ids
countermeasures enable
countermeasures mode all
device permit ssid IToIP
device permit ssid H3C-iMC-BYOD
#使能dhcp
dhcp enable
#使能arp-snooping功能
arp-snooping enable
#
user-interface con 0
user-interface vty 0 4
authentication-mode scheme
user privilege level 3
#
Return
二、配置关键点
1.使能AP的设备检测功能,既能提供接入服务,也能够进行非法AP检测:
[AC-wlan-ap-ap] device-detection enable
2.在WLAN IDS视图下添加所允许的SSID/MAC/OUI列表
①基于SSID的Rogue AP检测
[AC-wlan-ids]device permit ssid h3c
②基于MAC的Rogue AP检测
[AC-wlan-ids]device permit mac-address H-H-H
③基于OUI的Rogue AP检测
[AC-wlan-ids]device permit vendor
3.攻击Rogue AP,先使能反制rogue设备的功能,再配置反制模式为all:
[AC-wlan-ids] countermeasures enable
[AC-wlan-ids] countermeasures mode all
4.查看Rogue AP
[AC]display wlan ids detected all
三、结果验证
1.查看Rogue AP,发现SSID=IT o IP,SSID=H3C-Imc-BYOD为p,即permit AP。

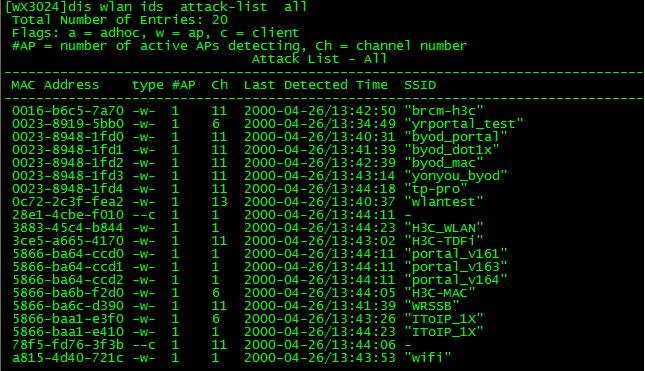
2. [WX3024]display wlan ids attack-list all
查看WIDS的反制攻击列表,说明反制已被应用,由于测试连接的SSID=H3C-MAC,认证模式属于open-system,故反制现象感知很低。对于802.1x认证等反制效果应该会更好些。
3.若AP开启了设备检测功能,即AC设备上连接的AP,则此AP发送的SSID信号不会出现在Rogue AP检测列表中。可以通过两个AP设置不同SSID都开启检测功能,通过查看Rogue AP检测列表,就能看见与AC相连AP发送的SSID信号,但是检测出此信号的设备是由对端AP检测到的。
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作