组网及说明
需求:
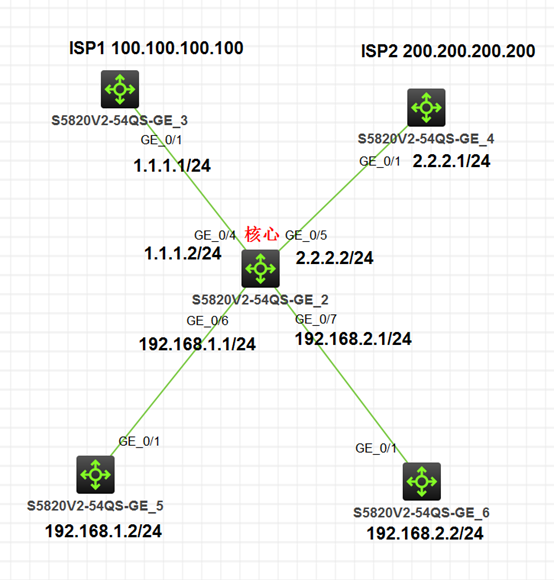
内网192.168.1.0/24网段的用户走ISP1链路,192.168.2.0/24网段用户走ISP2链路;
拓扑:
配置步骤
核心交换机配置:
#
ip vpn-instance isp1
#
ip vpn-instance isp2
#
interface Vlan-interface10
ip binding vpn-instance isp1
ip address 1.1.1.2 255.255.255.0
#
interface Vlan-interface20
ip binding vpn-instance isp2
ip address 2.2.2.2 255.255.255.0
#
interface Vlan-interface100
ip binding vpn-instance isp1
ip address 192.168.1.1 255.255.255.0
#
interface Vlan-interface200
ip binding vpn-instance isp2
ip address 192.168.2.1 255.255.255.0
#
interface GigabitEthernet1/0/4
port link-mode bridge
port access vlan 10
#
interface GigabitEthernet1/0/5
port link-mode bridge
port access vlan 20
#
interface GigabitEthernet1/0/6
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet1/0/7
port link-mode bridge
port access vlan 200
#
ip route-static vpn-instance isp1 0.0.0.0 0 1.1.1.1
ip route-static vpn-instance isp2 0.0.0.0 0 2.2.2.1
#
PC1:
#
interface Vlan-interface1
ip address 192.168.1.2 255.255.255.0
#
ip route-static 0.0.0.0 0 192.168.1.1
#
PC2:
#
interface Vlan-interface1
ip address 192.168.2.2 255.255.255.0
#
ip route-static 0.0.0.0 0 192.168.2.1
#
ISP1配置:
#
interface LoopBack0
ip address 100.100.100.100 255.255.255.255
#
interface Vlan-interface1
ip address 1.1.1.1 255.255.255.0
#
ip route-static 0.0.0.0 0 1.1.1.2
#
ISP2配置:
#
interface LoopBack0
ip address 200.200.200.200 255.255.255.255
#
interface Vlan-interface1
ip address 2.2.2.1 255.255.255.0
#
ip route-static 0.0.0.0 0 2.2.2.2
#
测试:
PC1 :
[PC1]ping 100.100.100.100
Ping 100.100.100.100 (100.100.100.100): 56 data bytes, press CTRL_C to break
56 bytes from 100.100.100.100: icmp_seq=0 ttl=254 time=3.776 ms
56 bytes from 100.100.100.100: icmp_seq=1 ttl=254 time=1.938 ms
56 bytes from 100.100.100.100: icmp_seq=2 ttl=254 time=1.829 ms
56 bytes from 100.100.100.100: icmp_seq=3 ttl=254 time=1.906 ms
56 bytes from 100.100.100.100: icmp_seq=4 ttl=254 time=1.533 ms
--- Ping statistics for 100.100.100.100 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 1.533/2.196/3.776/0.803 ms
[PC1]
[PC1]PING 200.200.200.200
Ping 200.200.200.200 (200.200.200.200): 56 data bytes, press CTRL_C to break
Request time out
Request time out
Request time out
Request time out
Request time out
--- Ping statistics for 200.200.200.200 ---
5 packet(s) transmitted, 0 packet(s) received, 100.0% packet loss
[PC1]
PC2测试:
[PC2]ping 200.200.200.200
Ping 200.200.200.200 (200.200.200.200): 56 data bytes, press CTRL_C to break
56 bytes from 200.200.200.200: icmp_seq=0 ttl=254 time=4.175 ms
56 bytes from 200.200.200.200: icmp_seq=1 ttl=254 time=1.894 ms
56 bytes from 200.200.200.200: icmp_seq=2 ttl=254 time=2.714 ms
56 bytes from 200.200.200.200: icmp_seq=3 ttl=254 time=2.412 ms
56 bytes from 200.200.200.200: icmp_seq=4 ttl=254 time=3.112 ms
--- Ping statistics for 200.200.200.200 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 1.894/2.861/4.175/0.768 ms
[PC2]
[PC2]ping 100.100.100.100
Ping 100.100.100.100 (100.100.100.100): 56 data bytes, press CTRL_C to break
Request time out
Request time out
Request time out
Request time out
Request time out
--- Ping statistics for 100.100.100.100 ---
5 packet(s) transmitted, 0 packet(s) received, 100.0% packet loss
[PC2]
核心测试:
<H3C>ping -vpn-instance isp1 100.100.100.100
Ping 100.100.100.100 (100.100.100.100): 56 data bytes, press CTRL_C to b reak
56 bytes from 100.100.100.100: icmp_seq=0 ttl=255 time=1.820 ms
56 bytes from 100.100.100.100: icmp_seq=1 ttl=255 time=1.166 ms
56 bytes from 100.100.100.100: icmp_seq=2 ttl=255 time=3.330 ms
56 bytes from 100.100.100.100: icmp_seq=3 ttl=255 time=1.155 ms
56 bytes from 100.100.100.100: icmp_seq=4 ttl=255 time=0.636 ms
--- Ping statistics for 100.100.100.100 in VPN instance isp1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 0.636/1.621/3.330/0.933 ms
<H3C>
<H3C>ping -vpn-instance isp2 200.200.200.200
Ping 200.200.200.200 (200.200.200.200): 56 data bytes, press CTRL_C to b reak
56 bytes from 200.200.200.200: icmp_seq=0 ttl=255 time=1.455 ms
56 bytes from 200.200.200.200: icmp_seq=1 ttl=255 time=1.142 ms
56 bytes from 200.200.200.200: icmp_seq=2 ttl=255 time=2.517 ms
56 bytes from 200.200.200.200: icmp_seq=3 ttl=255 time=0.516 ms
56 bytes from 200.200.200.200: icmp_seq=4 ttl=255 time=1.160 ms
--- Ping statistics for 200.200.200.200 in VPN instance isp2 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 0.516/1.358/2.517/0.655 ms
<H3C>
<H3C>
<H3C>
<H3C>ping 100.100.100.100
Ping 100.100.100.100 (100.100.100.100): 56 data bytes, press CTRL_C to b reak
Request time out
--- Ping statistics for 100.100.100.100 ---
2 packet(s) transmitted, 0 packet(s) received, 100.0% packet loss
<H3C>ping 1.1.1.1
Ping 1.1.1.1 (1.1.1.1): 56 data bytes, press CTRL_C to break
Request time out
--- Ping statistics for 1.1.1.1 ---
2 packet(s) transmitted, 0 packet(s) received, 100.0% packet loss
<H3C>
配置关键点
核心上的静态路由一定要将实例放在前面,添加到各自的vpn实例路由表中:
ip route-static vpn-instance isp1 0.0.0.0 0 1.1.1.1
ip route-static vpn-instance isp2 0.0.0.0 0 2.2.2.1
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
