组网及说明
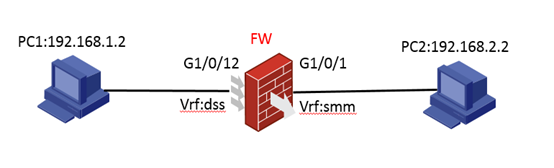
组网图如下:G1/0/1绑定VPN实例smm,G1/0/12绑定VPN实例dss。
问题描述
过程分析
- 接口不加入安全域,在安全域中import ip,放通对应的域间策略。
#
object-group ip address PC1
0 network subnet 192.168.1.0 255.255.255.0
#
object-group ip address PC2
0 network subnet 192.168.2.0 255.255.255.0
#
interface GigabitEthernet1/0/1
port link-mode route
ip binding vpn-instance smm
ip address 192.168.2.1 255.255.255.0
#
interface GigabitEthernet1/0/12
port link-mode route
ip binding vpn-instance dss
ip address 192.168.1.1 255.255.255.0
#
object-policy ip PC2-PC1
rule 0 pass source-ip PC2 destination-ip PC1
rule 1 pass source-ip PC2 destination-ip PC1 vrf smm
#
ip route-static vpn-instance dss 192.168.2.0 24 vpn-instance smm 192.168.2.2
ip route-static vpn-instance smm 192.168.1.0 24 vpn-instance dss 192.168.1.2 //记得在在带VPN实例时,写明VPN实例之间的路由,不然访问不通
#
acl advanced 3010
rule 0 permit icmp source 192.168.2.2 0 destination 192.168.1.2 0
rule 5 permit icmp source 192.168.1.2 0 destination 192.168.2.2 0
rule 10 permit icmp vpn-instance smm source 192.168.2.2 0 destination 192.168.1.2 0
rule 15 permit icmp vpn-instance smm source 192.168.1.2 0 destination 192.168.2.2 0
#
security-zone name ds
import ip 192.168.2.0 24
import ip 192.168.2.0 24 vpn-instance smm
#
security-zone name sd
import ip 192.168.1.0 24
import ip 192.168.1.0 24 vpn-instance dss
#
zone-pair security source ds destination sd
object-policy apply ip PC2-PC1
实验结果:(debug object-policy)*Nov 4 09:50:16:316 2018 H3C FILTER/7/PACKET: -COntext=1; The packet is permitted. Src-ZOne=ds, Dst-ZOne=sd;If-In=GigabitEthernet1/0/1(2), If-Out=GigabitEthernet1/0/12(13); Packet Info:Src-IP=192.168.2.2, Dst-IP=192.168.1.2, VPN-Instance=smm,Src-Port=8, Dst-Port=0, Protocol=ICMP(1), Application=ICMP(22742), ObjectPolicy=PC2-PC1, Rule-ID=1.
实验结论:匹配的是域间策略当中的rule1,源目地址带VPN实例和接口的VPN实例要相互一一对应。 删除安全域sd中目的IP(192.168.1.0)所带的VPN实例,就会导致网络不通,实验结果如下:
[H3C]security-zone name sd
[H3C-security-zone-sd]undo import ip 192.168.1.0 24 vpn-instance dssdebug 查看策略匹配的过程如下:
*Nov 4 10:03:12:325 2018 H3C ASPF/7/PACKET: -COntext=1; The packet was dropped by ASPF for nonexistent zone pair. Src-ZOne=ds, Dst-ZOne=-;If-In=GigabitEthernet1/0/1(2), If-Out=GigabitEthernet1/0/12(13); Packet Info:Src-IP=192.168.2.2, Dst-IP=192.168.1.2, VPN-Instance=smm, Src-Port=1, Dst-Port=2048. Protocol=ICMP(1).
将接口上绑定的VPN实例配置也删除,就可以访问通,如下:
[H3C-GigabitEthernet1/0/12]undo ip binding vpn-instance
策略匹配的结果为:*Nov 4 10:27:03:488 2018 H3C FILTER/7/PACKET: -COntext=1; The packet is permitted. Src-ZOne=ds, Dst-ZOne=sd;If-In=GigabitEthernet1/0/1(2), If-Out=GigabitEthernet1/0/12(13); Packet Info:Src-IP=192.168.2.2, Dst-IP=192.168.1.2, VPN-Instance=smm,Src-Port=8, Dst-Port=0, Protocol=ICMP(1), Application=ICMP(22742), ObjectPolicy=PC2-PC1, Rule-ID=1.
解决方法
当安全域中import ip,接口上也绑定了VPN实例,那么导入源目IP地址/地址段绑定的VPN实例应该与报文出入接口上绑定的VPN实例一一对应,缺一不可。
#
interface GigabitEthernet1/0/1
port link-mode route
ip binding vpn-instance smm
ip address 192.168.2.1 255.255.255.0
#
interface GigabitEthernet1/0/12
port link-mode route
ip binding vpn-instance dss
ip address 192.168.1.1 255.255.255.0
#
security-zone name ds
import ip 192.168.2.0 24 vpn-instance smm
#
security-zone name sd
import ip 192.168.1.0 24 vpn-instance dss
#
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
