组网及说明
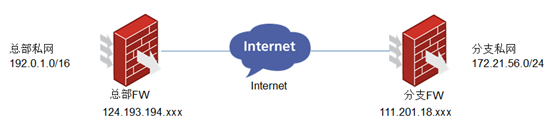
总部和多分支建立ipsec,总部采用模板方式,图中只画了一个分支作为示例。
问题描述
F1030作为总部和多个分支建立ipsec,ipsec建立成功但是流量不通。
总部情况:
[CXVPN_F1030]dis ip inter brief
*down: administratively down
(s): spoofing (l): loopback
Interface Physical Protocol IP Address Description
GE1/0/0 up up 192.0.1.110 --
GE1/0/1 up up 124.193.194.xxx –
[CXVPN_F1030]dis ike sa
Connection-ID Remote Flag DOI
-------------------------------------------------------------------------------
311 111.201.18.xxx RD IPsec
[CXVPN_F1030]dis ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/1
-------------------------------
-----------------------------
IPsec policy: zx
Sequence number: 1
Mode: Template
-----------------------------
Tunnel id: 21
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1444
Tunnel:
local address: 124.193.194.xxx
remote address: 111.201.18.xxx
Flow:
sour addr: 192.0.0.0/255.255.0.0 port: 0 protocol: ip
dest addr: 172.21.56.0/255.255.255.0 port: 0 protocol: ip
分支情况:
<zfylq>dis ip inter brief
*down: administratively down
(s): spoofing (l): loopback
Interface Physical Protocol IP Address Description
Cellular0/0 down down -- --
Dia10 up up 111.201.18.xxx --
GE0/0 up up -- --
GE0/4 down down -- --
Vlan1 up up 172.21.56.1 --
<zfylq>dis ike sa
total phase-1 SAs: 1
connection-id peer flag phase doi
----------------------------------------------------------------
536 124.193.194.xxx RD|ST 1 IPSEC
537 124.193.194.xxx RD|ST 2 IPSEC
<zfylq> dis ipsec sa
===============================
Interface: Dialer10
path MTU: 1400
===============================
-----------------------------
IPsec policy name: "yz"
sequence number: 10
acl version: ACL4
mode: isakmp
-----------------------------
PFS: N, DH group: none
inside VRF:
tunnel:
local address: 111.201.18.xxx
remote address: 124.193.194.xxx
flow:
sour addr: 172.21.56.0/255.255.255.0 port: 0 protocol: IP
dest addr: 192.0.0.0/255.255.0.0 port: 0 protocol: IP
ping测试记录
[CXVPN_F1030] ping -a 192.0.1.110 172.21.56.1
Ping 172.21.56.1 (172.21.56.1) from 192.0.1.110: 56 data bytes, press CTRL_C to break
Request time out
Request time out
Request time out
Request time out
Request time out
过程分析
两端ipsec已经建立,排除IPSEC参数配置问题。
Nat的acl里也将ipsec的流量deny掉了,排除nat配置问题
两端设备带原地址互ping排除内网其他设备内网路由等干扰因素
互ping地址是设备自身地址,设备上已经放通了untrust到local的域间策略。
总部ping分支,在分支debug ip packet无报文发过来。怀疑存在分支地址冲突,流量走到别的ipsec隧道。查看查看总部的ipsec协商情况,发现有一个隧道协商出的流目的地址为全0。
IPsec policy: zx
Sequence number: 1
Mode: Template
-----------------------------
Tunnel id: 17
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1436
Tunnel:
local address: 124.193.194.xxx
remote address: 122.97.174.142
Flow:
sour addr: 192.0.0.0/255.255.0.0 port: 0 protocol: ip
dest addr: 0.0.0.0/0.0.0.0 port: 0 protocol: ip
怀疑是流量走了全0的ipsec隧道,将此ipsec隧道reset重协商之后正常。
解决方法
将此全0的ipsec流量reset,或者将总部ipsec模板里此分支的ipsec里加上acl。
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
