sslvpn登录采用LADP认证时,无法用账号属性账户中的用户名进行认证登录。
Debug信息如下:
*Mar 23 14:28:41:929 2016 F1060 LDAP/7/EVENT: -Context=1;
PAM_LDAP[State]:State switch from authentication searching to binding user.
*Mar 23 14:28:41:929 2016 F1060 LDAP/7/ERROR: -Context=1;
PAM_LDAP:Failed to bind user lisi for the result of searching DN is NULL. //查找DN没有找到该lisi账号
*Mar 23 14:28:41:929 2016 F1060 LDAP/7/EVENT: -Context=1;
PAM_LDAP:Processing LDAP authentication.
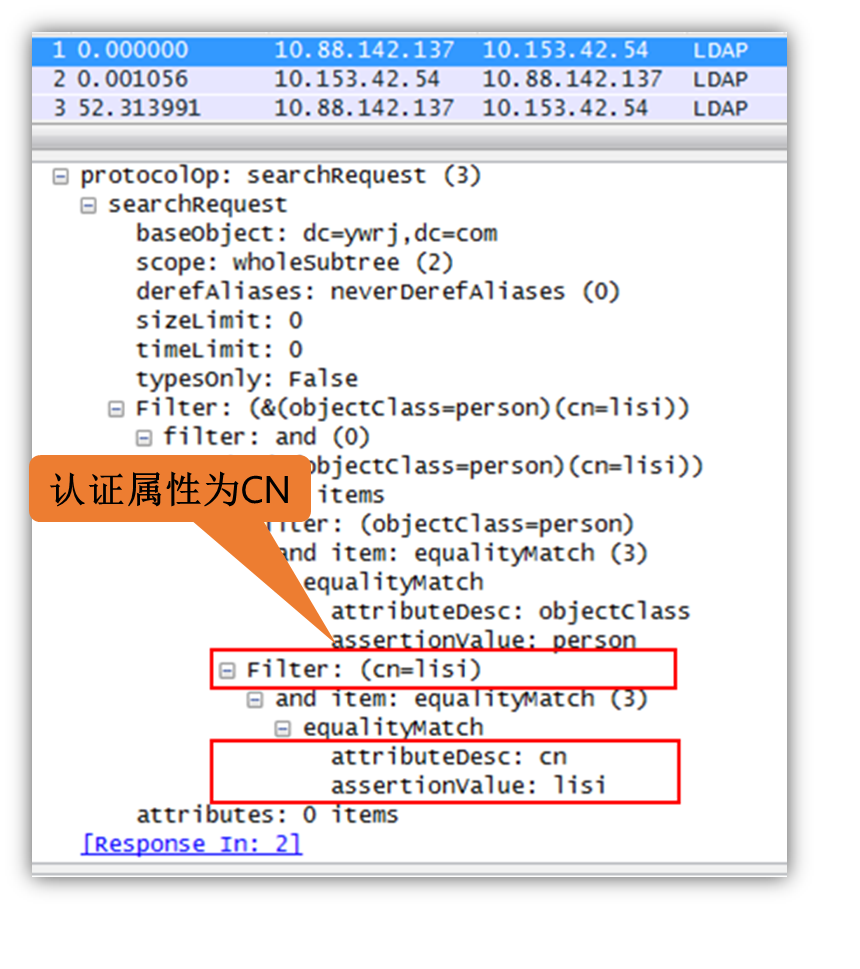
V7防火墙上配置ladp server策略时,认证的属性参数配置不对,导致无法在LADP服务器读取参数进行匹配。
通常LADP认证的账号在LADP服务器的cn下,在cn查找账号并校验密码即可认证通过。而用账号属性账户中的用户名进行认证登录时,查找的匹配参数是帐号属性参数。
通常的配置如下:
ldap server ldap1
login-dn cn=administrator,cn=users,dc=ywrj,dc=com
search-base-dn dc=ywrj,dc=com
ip 10.153.42.54
login-password cipher $c$3$tdHA3BHYnzteNTct2N3lBIo2/gn6DbhwIyv5
#
ldap scheme shm1
authentication-server ldap1
authorization-server ldap1
attribute-map test
#
ldap attribute-map test
map ldap-attribute memberof prefix cn= delimiter , aaa-attribute user-group
#
domain ldap
authentication sslvpn ldap-scheme shm1
authorization sslvpn ldap-scheme shm1
accounting sslvpn none
#
sslvpn context ctx
aaa domain ldap

修改防火墙的LADP server配置,增加账号属性参数userprincipalname,并且用户名格式为with-domain方式:
ldap server ldap1
login-dn cn=administrator,cn=users,dc=ywrj,dc=com
search-base-dn dc=ywrj,dc=com
ip 10.153.42.54
login-password cipher $c$3$tdHA3BHYnzteNTct2N3lBIo2/gn6DbhwIyv5
user-parameters user-name-attribute userprincipalname
user-parameters user-name-format with-domain
#
ldap scheme shm1
authentication-server ldap1
authorization-server ldap1
attribute-map test
#
ldap attribute-map test
map ldap-attribute memberof prefix cn= delimiter , aaa-attribute user-group
……
domain ***.***
authentication sslvpn ldap-scheme shm1
authorization sslvpn ldap-scheme shm1
accounting sslvpn none
#
sslvpn context ctx
aaa domain ***.***


该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
