SecPath防火墙与Windows XP实现IPSec互通的典型配置
- 0关注
- 0收藏 426浏览
SecPath防火墙与Windows XP实现IPSec互通的
典型配置
一、 组网需求:
某司分支使用Windows XP模拟一台路由与中心SecPath1000F建立IPSEC VPN,从而实现中心和分支之间内网的互联。
二、 组网图
SecPath100F:Version 3.40, R1606;
Windows XP:模拟路由器。
三、 配置信息
1、SecPath安全网关的主要配置
#
sysname Quidway
#
firewall packet-filter enable
firewall packet-filter default permit
#
undo connection-limit enable
connection-limit default deny
connection-limit default amount upper-limit 50 lower-limit 20
#
firewall statistic system enable
#
radius scheme system
#
domain system
#
ike dpd 1 //配置ike dpd
#
ike peer 1 //配置ike peer
pre-shared-key 123
remote-address 202.38.1.2
local-address 202.38.1.1
dpd 1
#
ipsec proposal 1 //配置ipsec安全提议
encapsulation-mode transport //封装模式为“传输”
esp authentication-algorithm sha1
esp encryption-algorithm 3des
#
ipsec policy pol1 1 isakmp //创建ipsec策略
security acl 3000
ike-peer 1
proposal 1
#
acl number 3000
rule 0 permit ip
#
interface Aux0
async mode flow
#
interface Ethernet1/0
#
interface GigabitEthernet0/0
ip address 202.38.1.1 255.255.255.0
ipsec policy pol1 //应用IPSEC策略
#
interface GigabitEthernet0/1
ip address 192.168.1.1 255.255.255.0
#
interface Encrypt2/0
#
interface NULL0
#
firewall zone local
set priority 100
#
firewall zone trust
add interface GigabitEthernet0/1
set priority 85
#
firewall zone untrust
add interface GigabitEthernet0/0
set priority 5
#
firewall zone DMZ
set priority 50
#
firewall interzone local trust
#
firewall interzone local untrust
#
firewall interzone local DMZ
#
firewall interzone trust untrust
#
firewall interzone trust DMZ
#
firewall interzone DMZ untrust
#
ip route-static 0.0.0.0 0.0.0.0 202.38.1.2
#
2、Windows XP的配置要点
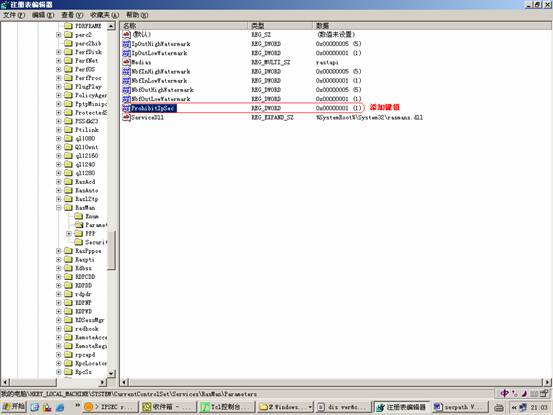
修改注册表,在下面的路径下添加一个DWORD值为1名称为“ProhibitIpSec”的键值:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\RasMan\Parameters
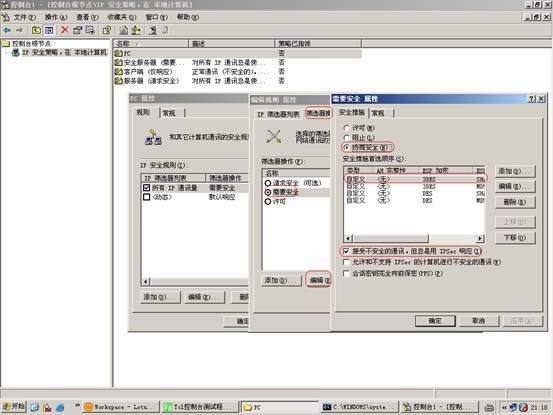
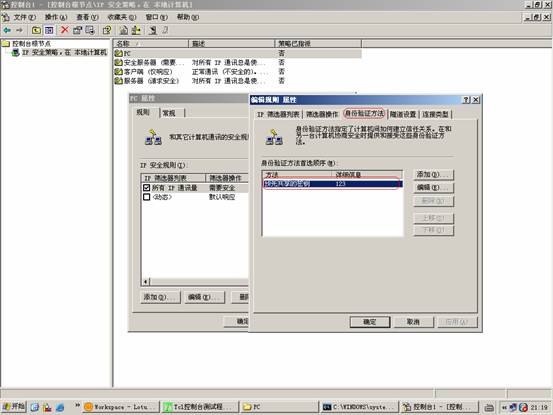
“控制面板”—“管理工具”—“本地安全策略”-“IP安全策略”,新建一个策略:
指派IP策略:

四、 配置关键点
Windows配置IPSEC时,默认采用证书方式。
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作