The configuration of IPSEC aggressive mode and NAT traserval for SR66 series router
- 0关注
- 0收藏 610浏览
The configuration of IPSEC aggressive mode and NAT traserval for SR66 series router
一、 Customer requirements:
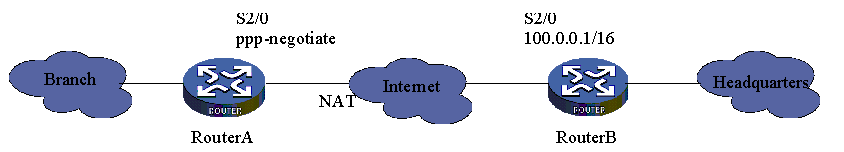
The branch links to center’s intranet. Router A’s serial2/0 has a static address and Router B uses dynamic address. We need configure NAT traserval on Router B to ensure information secure.
二、 Topology:
三、 Active Configurations:
(1) Router A configuration
# configure local ike name
<RouterA> system-view
[RouterA] ike local-name routera
# configure acl
[RouterA] acl number 3101 match-order auto
[RouterA-acl-adv-3101] rule permit ip source any destination any
[RouterA-acl-adv-3101] quit
# configure ip pool
[RouterA] ip pool 1 10.0.0.2 10.0.0.10
# configure IKE peer
[RouterA] ike peer peer
[RouterA-ike-peer-peer] exchange-mode aggressive
[RouterA-ike-peer-peer] pre-shared-key abc
[RouterA-ike-peer-peer] id-type name
[RouterA-ike-peer-peer] remote-name routerb
[RouterA-ike-peer-peer] quit
# configure IPSec secure proposal
[RouterA] ipsec proposal prop
[RouterA-ipsec-proposal-prop] encapsulation-mode tunnel
[RouterA-ipsec-proposal-prop] transform esp
[RouterA-ipsec-proposal-prop] esp encryption-algorithm des
[RouterA-ipsec-proposal-prop] esp authentication-algorithm sha1
[RouterA-ipsec-proposal-prop] quit
# configure secure policy
[RouterA] ipsec policy policy 10 isakmp
[RouterA-ipsec-policy-isakmp-policy-10] ike-peer peer
[RouterA-ipsec-policy-isakmp-policy-10] security acl 3101
[RouterA-ipsec-policy-isakmp-policy-10] proposal prop
[RouterA-ipsec-policy-isakmp-policy-10] quit
# configure the ip address of Serial2/0
[RouterA] interface serial 2/0
[RouterA-Serial2/0] ip address 100.0.0.1 255.255.0.0
# using secure policy
[RouterA-Serial2/0] ipsec policy policy
[RouterA-Serial2/0] remote address pool 1
(2)Router B configuration
# configure local ike name
<RouterB> system-view
[RouterB] ike local-name routerb
# configure acl。
[RouterB] acl number 3101 match-order auto
[RouterB-acl-adv-3101] rule permit ip source any destination any
[RouterB-acl-adv-3101] quit
# configure IKE peer。
[RouterB] ike peer peer
[RouterB-ike-peer-peer] exchange-mode aggressive
[RouterB-ike-peer-peer] pre-shared-key abc
[RouterB-ike-peer-peer] id-type name
[RouterB-ike-peer-peer] remote-name routera
[RouterB-ike-peer-peer] remote-ip 10.0.0.1
[RouterB-ike-peer-peer] nat traversal
[RouterB-ike-peer-peer] quit
# configure IPSec proposal
[RouterB] ipsec proposal prop
[RouterB-ipsec-proposal-prop] encapsulation-mode tunnel
[RouterB-ipsec-proposal-prop] transform esp
[RouterB-ipsec-proposal-prop] esp encryption-algorithm des
[RouterB-ipsec-proposal-prop] esp authentication-algorithm sha1
[RouterB-ipsec-proposal-prop] quit
# configure secure policy
[RouterB] ipsec policy policy 10 isakmp
[RouterB-ipsec-policy-isakmp-policy-10] ike-peer peer
[RouterB-ipsec-policy-isakmp-policy-10] security acl 3101
[RouterB-ipsec-policy-isakmp-policy-10] proposal prop
[RouterB-ipsec-policy-isakmp-policy-10] quit
# configure the ip address of Serial2/0
[RouterB] interface serial 2/0
[RouterB-Serial2/0] ip address ppp-negotiate
# using secure policy
[RouterB-Serial2/0] ipsec policy policy
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作