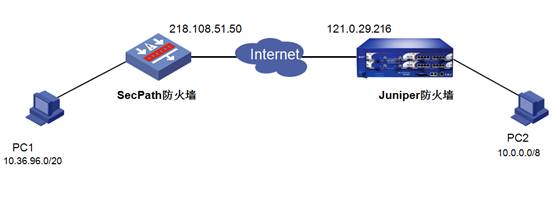
H3C SecPath防火墙和Juniper(Netscreen)防火墙对接S2S主模式IPSec典型配置
- 0关注
- 2收藏 1486浏览
H3C SecPath防火墙和Juniper(Netscreen)防火墙
对接S2S主模式IPSec典型配置
一、组网需求
IPSec协议属于标准的安全协议,现在主流的防火墙和VPN设备基本均支持IPSec VPN,但各厂商在配置方面却差别较大。此文档对H3C SecPath系列防火墙同Juniper防火墙(Netscreen防火墙)对接Site to Site 类型的IPSec VPN给出典型配置说明。
【说明】:和Juniper对接野蛮模式的IPsec,请参考案例http://kms.h3c.com/kms/kms/search/view.html?id=13614
二、网络拓扑
三、配置步骤
1. H3C SecPath配置
#
//内部用户上网使用的ACL
acl number 3000
//为避免IPSec数据流匹配NAT,首先阻断两端内网互访的流量
rule 2 deny ip source 10.36.96.0 0.0.15.255 destination 10.0.0.0 0.255.255.255
rule 6 permit ip source 10.36.96.0 0.0.15.255
//创建IPSec的感兴趣数据流
acl number 3100
rule 5 permit ip source 10.36.96.0 0.0.15.255 destination 10.0.0.0 0.255.255.255
#
//创建IKE提议
ike proposal 1
encryption-algorithm 3des-cbc
dh group2
sa duration 28800
#
//创建IKE对等体,协商模式为主模式、认证ID类型为IP地址、验证方式为预共享密钥方式
ike peer hz
pre-shared-key simple 1234
remote-address 121.0.29.216
#
//创建IPSec提议
ipsec proposal hz
esp authentication-algorithm sha1
esp encryption-algorithm 3des
#
//创建IPSec策略
ipsec policy 1 1 isakmp
security acl 3100
pfs dh-group2
ike-peer hz
proposal hz
#
interface GigabitEthernet0/2
port link-mode route
//创建NAT Outbound,负责内部用户访问Internet
nat outbound 3000 address-group 0
ip address 218.108.51.50 255.255.255.248
undo dhcp select server global-pool
//接口下引用IPSec策略
ipsec policy 1
#
//配置去往公网的路由
ip route-static 0.0.0.0 0.0.0.0 218.108.51.49
2. Juniper防火墙配置
1. 创建Tunnel并将对端路由指向此Tunnel
![]()
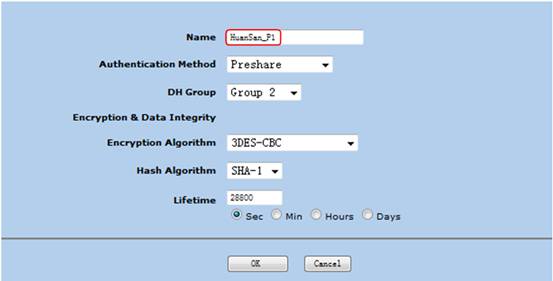
2. 指定IPSec Phase1阶段的策略
创建IKE提议名字HuanSan_P1,其中参数对应用SecPath的IKE Proposal的配置。
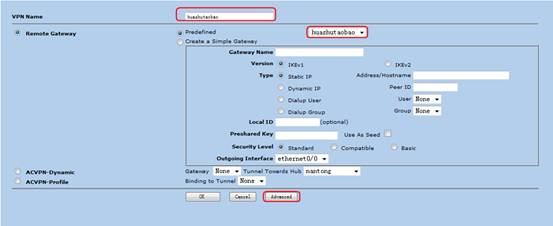
3. 指定对端网关
创建对端网关,名字为huashutaobao,其中参数类似于SecPath的IKE Peer配置。
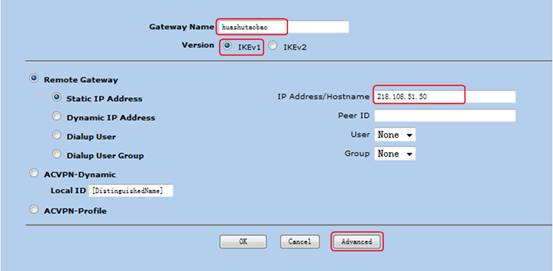
点击Advanced按钮,进行IKE提议的配置选择,选择前面创建的HuanSan_P1提议。

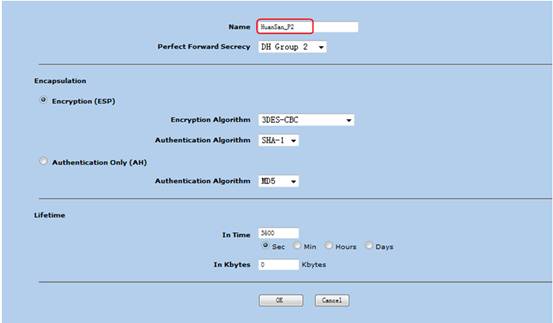
4. 指定IPSec Phase2阶段的参数
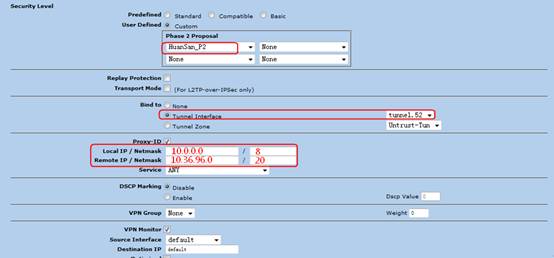
配置名称为HuanSan_P2,参数对应于H3C SecPath的IPSec Proposal的配置。
5. 创建IPSec策略
Remote gateway指定预先配置的huashutaobao网关名字。
点击Advanced按钮,指定Phase2的策略
6. 创建访问控制策略,允许对端通过VPN访问本端私网
五、验证结果
<H3C> display ike sa
total phase-1 SAs: 1
connection-id peer flag phase doi
----------------------------------------------------------
72 121.0.29.216 RD|ST 2 IPSEC
66 121.0.29.216 RD 1 IPSEC
<H3C>display ipsec sa
===============================
Interface: GigabitEthernet0/2
path MTU: 1500
===============================
-----------------------------
IPsec policy name: "1"
sequence number: 1
mode: isakmp
-----------------------------
connection id: 5
encapsulation mode: tunnel
perfect forward secrecy: DH group 2
tunnel:
local address: 218.108.51.50
remote address: 121.0.29.216
Flow :
sour addr: 10.36.96.0/255.255.240.0 port: 0 protocol: IP
dest addr: 10.0.0.0/255.0.0.0 port: 0 protocol: IP
[inbound ESP SAs]
spi: 1094354255 (0x413a854f)
proposal: ESP-ENCRYPT-3DES ESP-AUTH-SHA1
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1842702/3270
max received sequence-number: 1702
anti-replay check enable: Y
anti-replay window size: 32
udp encapsulation used for nat traversal: N
[outbound ESP SAs]
spi: 3766371807 (0xe07e45df)
proposal: ESP-ENCRYPT-3DES ESP-AUTH-SHA1
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843109/3270
max sent sequence-number: 1315
udp encapsulation used for nat traversal: N
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作