问题描述:
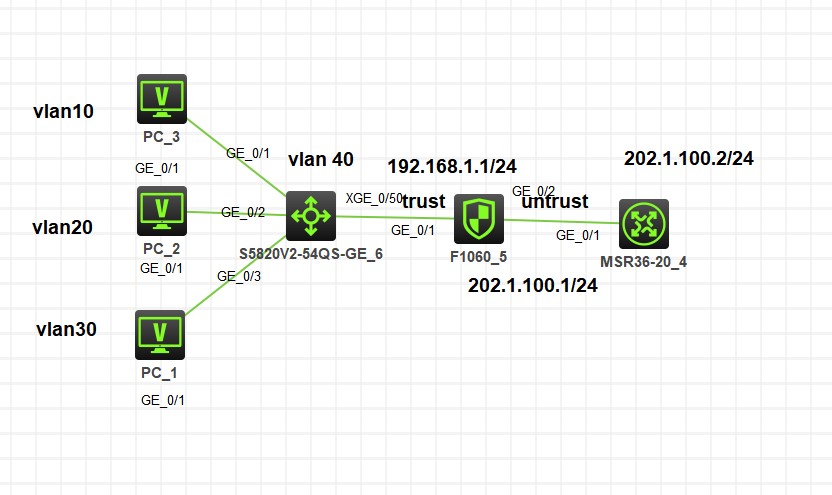
pc可以ping通防火墙的g1 192.168.1.1,ping不通202.1.100.2,也没有NAT会话,不知道哪里配置错误,请解惑
组网及组网描述:
设置列表
- 有序列表
- 无序列表
对齐方式
- 靠左
- 居中
- 靠右
- 附件下载: route.txt
- 2021-05-28提问
- 举报
-
(0)
最佳答案

您好,以下参考
1、设否配置nat outbound
2、安全域放通了吗
3、默认路由配置了吗
- 2021-05-28回答
- 评论(3)
- 举报
-
(0)
ip route-static 0.0.0.0 0 10.2.2.2 ip route-static 192.168.10.0 24 192.168.1.2 ip route-static 192.168.20.0 24 192.168.1.2 ip route-static 192.168.30.0 24 192.168.1.2 nat policy rule name out source-ip vlan10 source-ip vlan20 source-ip vlan30 outbound-interface GigabitEthernet1/0/2 action easy-ip # ip http enable ip https enable # security-policy ip rule 10 name out action pass counting enable source-zone local source-zone trust destination-zone untrust destination-zone dmz destination-zone trust destination-zone local
ip route-static 0.0.0.0 0 202.1.100.2 (上面之前的记录,复制错了)
3楼防火墙配置,看下什么问题

喵的我知道原因了。你前面建立的安全区是Trust,后面安全策略里用的是trust,大小写不一样。。。。。。
[F5]dis cur
#
version 7.1.064, Alpha 7164
#
sysname F5
#
context Admin id 1
#
telnet server enable
#
irf mac-address persistent timer
irf auto-update enable
undo irf link-delay
irf member 1 priority 1
#
xbar load-single
password-recovery enable
lpu-type f-series
#
vlan 1
#
object-group ip address vlan10
0 network subnet 192.168.10.0 255.255.255.0
#
object-group ip address vlan20
0 network subnet 192.168.20.0 255.255.255.0
#
object-group ip address vlan30
0 network subnet 192.168.30.0 255.255.255.0
#
interface NULL0
#
interface GigabitEthernet1/0/0
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/1
port link-mode route
combo enable copper
ip address 192.168.1.1 255.255.255.0
#
interface GigabitEthernet1/0/2
port link-mode route
combo enable copper
ip address 202.1.100.1 255.255.255.0
#
interface GigabitEthernet1/0/3
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/4
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/5
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/6
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/7
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/8
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/9
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/10
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/11
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/12
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/13
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/14
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/15
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/16
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/17
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/18
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/19
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/20
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/21
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/22
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/23
port link-mode route
combo enable copper
#
security-zone name Local
#
security-zone name Trust
import interface GigabitEthernet1/0/1
#
security-zone name DMZ
#
security-zone name Untrust
import interface GigabitEthernet1/0/2
#
security-zone name Management
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line aux 0
user-role network-admin
#
line con 0
authentication-mode scheme
user-role network-admin
#
line vty 0 4
authentication-mode scheme
user-role network-admin
#
line vty 5 63
user-role network-operator
#
ip route-static 0.0.0.0 0 202.1.100.2
ip route-static 192.168.10.0 24 192.168.1.2
ip route-static 192.168.20.0 24 192.168.1.2
ip route-static 192.168.30.0 24 192.168.1.2
#
domain system
#
aaa session-limit ftp 16
aaa session-limit telnet 16
aaa session-limit ssh 16
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user admin class manage
password hash $h$6$UbIhNnPevyKUwfpm$LqR3+yg1IjNct39MkOR0H0iQXLkYB3jMqM4vbAeoXOhbabIIFnjJPEGR00YiYA1Sz4LiY3FmEdru2fOLMb1shQ==
service-type telnet terminal http
authorization-attribute user-role level-3
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
nat policy
rule name out
source-ip vlan10
source-ip vlan20
source-ip vlan30
outbound-interface GigabitEthernet1/0/2
action easy-ip
#
ip http enable
ip https enable
#
security-policy ip
rule 10 name out
action pass
source-zone Local
source-zone Trust
destination-zone Untrust
destination-zone Trust
destination-zone Local
#
return
- 2021-05-28回答
- 评论(3)
- 举报
-
(0)
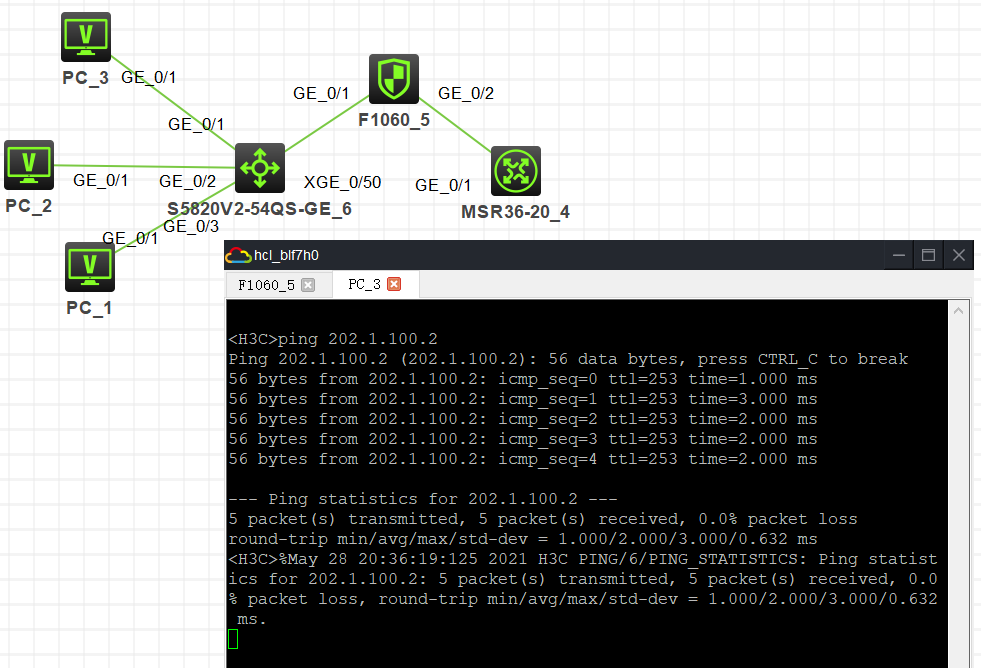
可以了,交换机忘了配路由
安全策略里加了 source-zone untrust 一样不行
我改了,也是不行,好奇怪
可以了,交换机忘了配路由

您好,请知:
PC PING不通防火墙的外网接口地址,以下是排查要点,请参考:
1、检查交换机与防火墙的路由是否已配置完成。
2、防火墙上涉及到的物理端口需加入安全域并放通安全策略或域间策略, 尤其是LOCAL域,需分别作为源和目的进行放通。以下是域间策略放通的参考命令:
[SSL_VPN]acl basic 2001
[SSL_VPN-acl-ipv4-basic-2001]rule 0 permit source any
[SSL_VPN-acl-ipv4-basic-2001]quit
[SSL_VPN]
[SSL_VPN]zone-pair security source trust destination untrust
[SSL_VPN-zone-pair-security-Trust-Untrust]packet-filter 2001
[SSL_VPN-zone-pair-security-Trust-Untrust]quit
[SSL_VPN]
[SSL_VPN]zone-pair security source untrust destination trust
[SSL_VPN-zone-pair-security-Untrust-Trust]packet-filter 2001
[SSL_VPN-zone-pair-security-Untrust-Trust]quit
[SSL_VPN]
[SSL_VPN]zone-pair security source trust destination local
[SSL_VPN-zone-pair-security-Trust-Local]packet-filter 2001
[SSL_VPN-zone-pair-security-Trust-Local]quit
[SSL_VPN]
[SSL_VPN]zone-pair security source local destination trust
[SSL_VPN-zone-pair-security-Local-Trust]packet-filter 2001
[SSL_VPN-zone-pair-security-Local-Trust]quit
[SSL_VPN]
[SSL_VPN]zone-pair security source untrust destination local
[SSL_VPN-zone-pair-security-Untrust-Local]packet-filter 2001
[SSL_VPN-zone-pair-security-Untrust-Local]quit
[SSL_VPN]
[SSL_VPN]zone-pair security source local destination untrust
[SSL_VPN-zone-pair-security-Local-Untrust]packet-filter 2001
[SSL_VPN-zone-pair-security-Local-Untrust]quit
3、进一步检查NAT的策略配置。比如外网口是否配置为nat outbound。
- 2021-05-28回答
- 评论(1)
- 举报
-
(0)
3楼防火墙配置,看下什么问题
3楼防火墙配置,看下什么问题


object-group ip address vlan10
0 network subnet 192.168.10.0 255.255.255.0
#
object-group ip address vlan20
0 network subnet 192.168.20.0 255.255.255.0
#
object-group ip address vlan30
0 network subnet 192.168.30.0 255.255.255.0
interface GigabitEthernet1/0/1
port link-mode route
combo enable copper
ip address 192.168.1.1 255.255.255.0
interface GigabitEthernet1/0/2
port link-mode route
combo enable copper
ip address 202.1.100.1 255.255.255.0
security-zone name Trust
import interface GigabitEthernet1/0/1
security-zone name Untrust
import interface GigabitEthernet1/0/2
zone-pair security source Local destination Trust
packet-filter 3000
#
zone-pair security source Trust destination Local
packet-filter 3000
#
ip route-static 0.0.0.0 0 202.1.100.2
ip route-static 192.168.10.0 24 192.168.1.2
ip route-static 192.168.20.0 24 192.168.1.2
ip route-static 192.168.30.0 24 192.168.1.2
#
acl advanced 3000
rule 0 permit ip
#
nat policy
rule name out
source-ip vlan10
source-ip vlan20
source-ip vlan30
outbound-interface GigabitEthernet1/0/2
action easy-ip
#
ip http enable
ip https enable
#
security-policy ip
rule 10 name out
action pass
counting enable
source-zone local
source-zone trust
destination-zone untrust
destination-zone dmz
destination-zone trust
destination-zone local
#
- 2021-05-28回答
- 评论(1)
- 举报
-
(0)
帮忙看下,别沉了
帮忙看下,别沉了
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明



3楼防火墙配置,看下什么问题