问题描述:
从原先的自动拨号改为固定IP接互联网(附上配置文件)web界面无修改模块 ,该如何修改
固定IPIP地址:58.221.215.174子网掩码:255.255.255.252网关地址:58.221.215.173dns61.147.37.1
组网及组网描述:
设置列表
- 有序列表
- 无序列表
对齐方式
- 靠左
- 居中
- 靠右
#
version 7.1.064, Ess 9504P11
#
sysname H3C
#
context Admin id 1
#
ip vpn-instance management
route-distinguisher 1000000000:1
vpn-target 1000000000:1 import-extcommunity
vpn-target 1000000000:1 export-extcommunity
#
telnet server enable
#
irf mac-address persistent timer
irf auto-update enable
undo irf link-delay
irf member 1 priority 1
#
dialer flow-interval 1
dialer-group 1 rule ip permit
#
dhcp enable
#
password-recovery enable
#
vlan 1
#
object-group ip address 1
0 network host address 192.168.8.110
#
object-group ip address waiwang
description waiwang
0 network host address 192.168.0.0
#
object-group ip address wan
description wan
0 network host address 192.168.10.0
#
object-group ip address wuxian
description wuxian
0 network host address 192.168.5.0
#
object-group service 2
0 service tcp destination eq 5000
#
object-group service 5000
0 service tcp source eq 5000 destination eq 5000
#
dhcp server ip-pool neiwang
gateway-list 192.168.8.1
network 192.168.8.0 mask 255.255.255.0
dns-list 114.114.114.114
static-bind ip-address 192.168.8.110 mask 255.255.255.0 hardware-address 0110-9836-a6aa-7e
static-bind ip-address 192.168.8.250 mask 255.255.255.0 hardware-address 0134-e894-f550-b4
#
dhcp server ip-pool wan
gateway-list 192.168.10.1
network 192.168.10.0 mask 255.255.255.0
dns-list 202.96.209.133 202.96.209.6
nbns-list 192.168.10.1
#
dhcp server ip-pool wuxian
gateway-list 192.168.5.1
network 192.168.5.0 mask 255.255.255.0
dns-list 202.96.209.133
#
interface Dialer1
ppp chap password cipher $c$3$jhIxsfmrZTU2gMk14K07uC/I3CHsJ+qfadup
ppp chap user ad79366445
ppp pap local-user ad79366445 password cipher $c$3$9eOoxYoLY0axhnZd0JCzujrPJrXk5jK9ohVN
dialer bundle enable
dialer-group 1
dialer timer idle 0
ip address ppp-negotiate
tcp mss 1024
nat outbound
nat server protocol tcp global current-interface 5000 inside 192.168.8.80 5000 acl 2000
nat server protocol tcp global current-interface 5002 inside 192.168.8.110 5002 acl 2000
nat server protocol tcp global current-interface 6690 inside 192.168.8.80 6690
nat server global 2000 inside 192.168.8.110 5000
#
interface NULL0
#
interface GigabitEthernet1/0/0
port link-mode route
combo enable copper
ip address 192.168.0.1 255.255.255.0
#
interface GigabitEthernet1/0/1
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/2
port link-mode route
ip binding vpn-instance management
ip address 192.168.1.1 255.255.255.0
#
interface GigabitEthernet1/0/3
port link-mode route
ip address 192.168.8.1 255.255.255.0
#
interface GigabitEthernet1/0/4
port link-mode route
ip address 192.168.10.1 255.255.255.0
#
interface GigabitEthernet1/0/5
port link-mode route
duplex full
ip address 192.168.5.1 255.255.255.0
#
interface GigabitEthernet1/0/6
port link-mode route
#
interface GigabitEthernet1/0/7
port link-mode route
#
interface GigabitEthernet1/0/8
port link-mode route
#
interface GigabitEthernet1/0/9
port link-mode route
pppoe-client dial-bundle-number 1
#
interface GigabitEthernet1/0/10
port link-mode route
#
interface GigabitEthernet1/0/11
port link-mode route
#
object-policy ip Any-Any
rule 1 pass
#
object-policy ip Untrust-Trust
rule 0 inspect 5_3_0_IPv4 counting
rule 1 pass destination-ip 1 service 5000
#
object-policy ip wuxian-Trust
rule 0 drop source-ip wuxian disable
#
object-policy ip wuxian-Untrust
rule 0 pass source-ip wuxian
#
security-zone name Local
#
security-zone name Trust
import interface GigabitEthernet1/0/3
#
security-zone name DMZ
#
security-zone name Untrust
import interface Dialer1
import interface GigabitEthernet1/0/9
attack-defense apply policy 2001
#
security-zone name Management
import interface GigabitEthernet1/0/2
#
security-zone name WAN
import interface GigabitEthernet1/0/0
import interface GigabitEthernet1/0/4
#
security-zone name wuxian
import interface GigabitEthernet1/0/5
#
zone-pair security source Any destination Any
object-policy apply ip Any-Any
#
zone-pair security source Local destination Trust
packet-filter 2000
#
zone-pair security source Local destination Untrust
packet-filter 2000
#
zone-pair security source Local destination WAN
packet-filter 2000
#
zone-pair security source Local destination wuxian
packet-filter 2000
#
zone-pair security source Trust destination Local
packet-filter 2000
#
zone-pair security source Trust destination Untrust
packet-filter 2000
#
zone-pair security source Trust destination WAN
packet-filter 2000
#
zone-pair security source Untrust destination Trust
object-policy apply ip Untrust-Trust
#
zone-pair security source Untrust destination wuxian
packet-filter 2000
#
zone-pair security source WAN destination Local
packet-filter 2000
#
zone-pair security source WAN destination Trust
packet-filter 2000
#
zone-pair security source WAN destination Untrust
packet-filter 2000
#
zone-pair security source WAN destination WAN
packet-filter 2000
#
zone-pair security source wuxian destination Local
packet-filter 2000
#
zone-pair security source wuxian destination Trust
object-policy apply ip wuxian-Trust
#
zone-pair security source wuxian destination Untrust
object-policy apply ip wuxian-Untrust
packet-filter 2000
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
user-role network-admin
#
line class vty
user-role network-operator
#
line aux 0
user-role network-admin
#
line con 0
authentication-mode scheme
user-role network-admin
#
line vty 0 63
authentication-mode scheme
user-role network-admin
#
ip route-static 0.0.0.0 0 Dialer1
ip route-static 192.168.20.0 24 192.168.0.254
ip route-static 192.168.30.0 24 192.168.0.254
ip route-static 192.168.40.0 24 GigabitEthernet1/0/0 192.168.0.254
ip route-static 192.168.100.0 24 192.168.0.254
#
ssh server enable
#
acl basic 2000
rule 0 permit
#
acl advanced 3000
rule 0 permit ip
#
domain system
#
aaa session-limit ftp 16
aaa session-limit telnet 16
aaa session-limit ssh 16
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user admin class manage
password hash $h$6$pMyZjViP0IYsyyKU$fPm+NK94buyZ8NRr2M2XZ9Kqww12IUJItyAoewSRbziC9l281cpe1J8YduKFbKKEwVsYo8sffnFDCtxqvooYaA==
service-type ssh telnet terminal http https
authorization-attribute user-role level-15
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
ip http enable
ip https port 8443
ip https enable
#
attack-defense policy 2001
syn-flood action drop
ack-flood action drop
syn-ack-flood action drop
rst-flood action drop
fin-flood action drop
udp-flood action drop
icmp-flood action drop
icmpv6-flood action drop
dns-flood action drop
http-flood action drop
#
data-filter keyword-group 迅雷
description 下载
#
url-filter policy 过滤
default-action drop
category Pre-AdvertisementsAndPop-Ups action drop
category Pre-CriminalActivity action drop logging
category Pre-Cults action drop logging
category Pre-Gambling action drop
category Pre-Games action drop
category Pre-Nudity action drop
category Pre-Pornography_SexuallyExplicit action drop logging
category Pre-Religion action drop
category Pre-SpamSites action drop
category Pre-Weapons action drop
#
app-profile 5_3_0_IPv4
anti-virus apply policy default mode protect
#
app-profile antifilter
anti-virus apply policy default mode protect
#
inspect block-source parameter-profile ips_block_default_parameter
#
ips policy default
#
anti-virus policy default
#
return
- 2021-09-30提问
- 举报
-
(0)
最佳答案

您好,参考
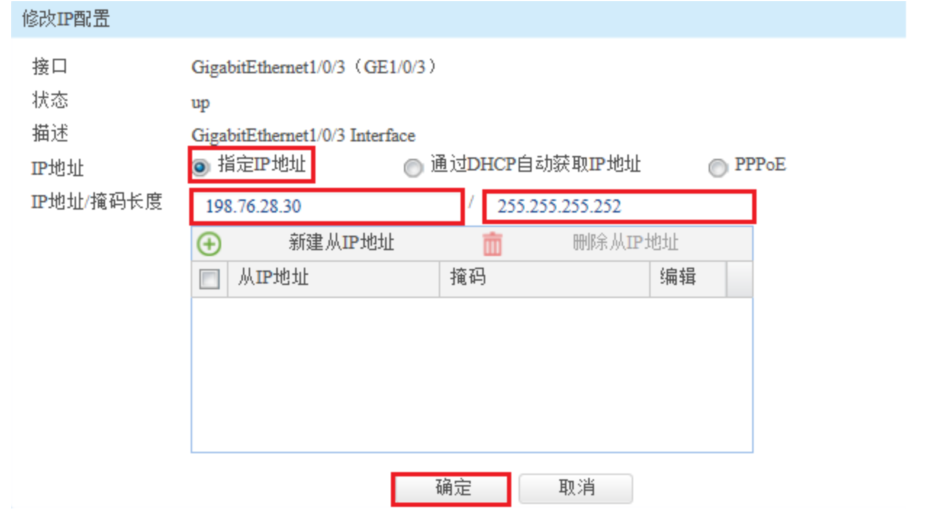
3.2 配置外网接口
#在“网络”>“IP”选项中选择1/0/3接口并点击此接口最后面的”编辑”按钮。

#“IP地址”填写运营商给的公网地址198.76.28.30,掩码为255.255.255.252。
- 2021-09-30回答
- 评论(2)
- 举报
-
(0)

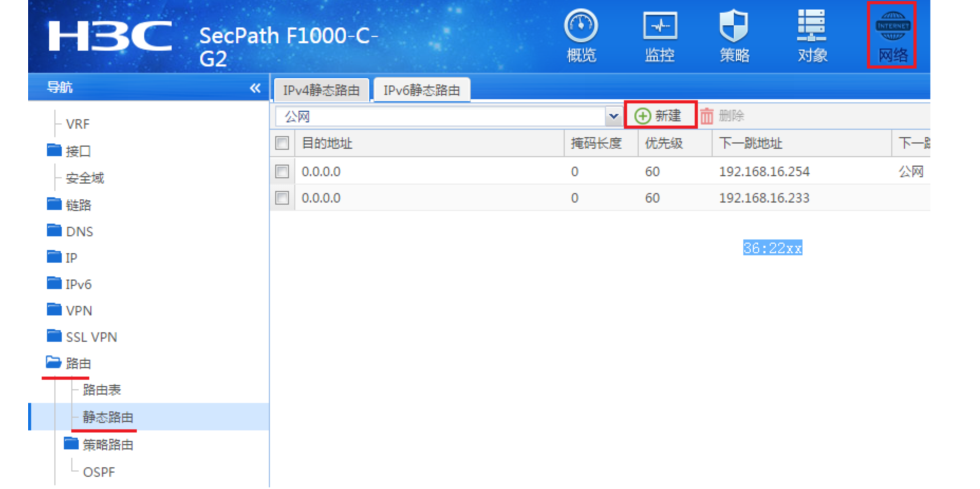
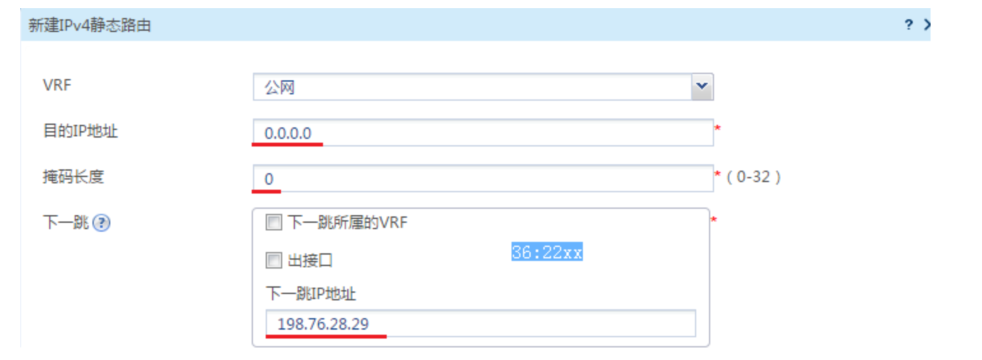
在接口修改配置和NAT转换后再配置路由即可,以下是参考命令:
int gi 1/0/1
ip address 58.221.215.174 255.255.255.252
nat outbound
quit
ip route-static 0.0.0.0 0.0.0.0 58.221.215.173
- 2021-09-30回答
- 评论(0)
- 举报
-
(0)
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明






保存配置就行,无需重启