再次IPSec VPN多网段互访问题
- 0关注
- 1收藏,3312浏览
问题描述:
成功建立VPN(野蛮模式),西安有10个网段需要和东莞1个网段互访,现在启用ike dpd,Ike和ipsec都可以建立,但只有西安1网段和东莞10网段可以相互访问,东莞可以访问西安的其他网段,但西安的其他网段必须从东莞先ping一下,才可以短暂访问,如果在东莞做到西安某个网段的nqa entry,西安的这个网段才可以访问东莞,请问为社么?只能在东莞做nqa entry吗?(这个做了多的话,路由器能行吗?)
昨天提问,“李云龙的意大利炮”说可以在两端配置设备配置LoopBack接口,然后将接口地址加入感兴趣流,NQA就只需要探测这个LoopBack接口就行了,没必要探测16个NQA。昨晚上试了不行,两端设备重启,DPD启用后,建立了西安192.168.1.0/24到东莞192.168.10.0/24的隧道,双方可以互ping通,东莞向西安别的网段发起通信后也能建立ipsec隧道,东莞能ping通西安的网段,但西安别的网段ping不通东莞,除非东莞先ping一下,能短暂通。
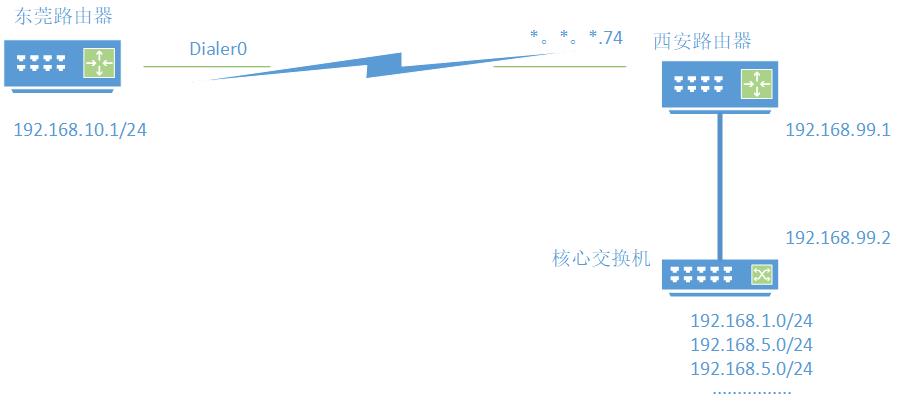
下面是网络图、ACL、路由(西安路由器下联三层交换机),ike和ipsec配置正确就省略了,请大家帮忙看看。
组网及组网描述:
设置列表
- 有序列表
- 无序列表
对齐方式
- 靠左
- 居中
- 靠右
东莞ACL及接口设置
acl advanced 3002 (兴趣流)
rule 5 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
rule 7 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.5.0 0.0.0.255
rule 8 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.6.0 0.0.0.255
rule 9 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.7.0 0.0.0.255
rule 10 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.8.0 0.0.0.255
rule 11 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.9.0 0.0.0.255
rule 12 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.11.0 0.0.0.255
rule 13 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.12.0 0.0.0.255
rule 14 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255
rule 15 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.30.0 0.0.0.255
rule 18 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.99.0 0.0.0.255
rule 49 permit ip source 172.16.102.0 0.0.0.255 destination 172.16.101.0 0.0.0.255
#
ipsec policy IPSEC 1 isakmp
transform-set 10
security acl 3002
remote-address *.*.*.74
ike-profile 10
acl advanced 3000
rule 51 permit ip
#
interface Dialer0
···········
nat outbound 3000
ipsec apply policy IPSEC
ipsec no-nat-process enable
东莞路由表
ip route-static 0.0.0.0 0 Dialer0
ip route-static 192.168.1.0 24 Dialer0
ip route-static 192.168.5.0 24 Dialer0
ip route-static 192.168.6.0 24 Dialer0
ip route-static 192.168.7.0 24 Dialer0
ip route-static 192.168.8.0 24 Dialer0
ip route-static 192.168.9.0 24 Dialer0
ip route-static 192.168.11.0 24 Dialer0
ip route-static 192.168.12.0 24 Dialer0
ip route-static 192.168.20.0 24 Dialer0
ip route-static 192.168.30.0 24 Dialer0
西安设置
西安ACL及接口设置
acl advanced 3002
rule 5 permit ip source 192.168.1.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 7 permit ip source 192.168.5.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 8 permit ip source 192.168.6.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 9 permit ip source 192.168.7.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 10 permit ip source 192.168.8.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 11 permit ip source 192.168.9.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 12 permit ip source 192.168.11.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 14 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 15 permit ip source 192.168.30.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 18 permit ip source 192.168.99.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 49 permit ip source 172.16.101.0 0.0.0.255 destination 172.16.102.0 0.0.0.255
#
ipsec policy-template IPSEC 10
transform-set 10
local-address *.*.*.74
ike-profile 10
security acl 3002
acl advanced 3000
rule 51 permit ip
#
interface GigabitEthernet0/0
ip address *.*.*.74 255.255.255.252
·······················
tcp mss 1450
nat outbound 3000
ipsec apply policy IPSECVPN
ipsec no-nat-process eable
西安路由表
#
ip route-static 0.0.0.0 0 GigabitEthernet0/0 *.*.*.73
ip route-static 192.168.1.0 24 192.168.99.2
ip route-static 192.168.3.0 24 192.168.99.2
ip route-static 192.168.5.0 24 192.168.99.2
ip route-static 192.168.6.0 24 192.168.99.2
ip route-static 192.168.7.0 24 192.168.99.2
ip route-static 192.168.8.0 24 192.168.99.2
ip route-static 192.168.9.0 24 192.168.99.2
ip route-static 192.168.10.0 24 GigabitEthernet0/0 *.*.*.73
ip route-static 192.168.11.0 24 192.168.99.2
ip route-static 192.168.12.0 24 192.168.99.2
ip route-static 192.168.16.0 24 192.168.99.2
ip route-static 192.168.20.0 24 192.168.99.2
ip route-static 192.168.30.0 24 192.168.99.2
ip route-static 192.168.50.0 24 192.168.99.2
ip route-static 192.168.60.0 24 192.168.99.2
ip route-static 192.168.70.0 24 192.168.99.2
ip route-static 192.168.71.0 24 192.168.99.2
ip route-static 192.168.90.0 24 192.168.99.2
ip route-static 192.168.91.0 24 192.168.99.2
西安核心路由表
ip route-static 0.0.0.0 0 192.168.99.1
ip route-static 192.168.10.0 24 192.168.99.1
- 2021-12-03提问
- 举报
-
(0)

根据描述,nqa问题可能性不大。
另外2端都是单出口的话,路由表没必要走明细(个人建议)
怀疑可能是nat out流没拒绝ipsec流和野蛮模式nat穿越问题
建议调整下
1.2端nat流拒绝ipsec流 也就是acl 3000 deny ipsec流
2.调整ipsec模式为gre over IPSec并配置ospf方式保证流量会话。
- 2021-12-03回答
- 评论(3)
- 举报
-
(0)
ipsec no-nat-process enable这个deny ipsec流了吧?
gre over IPSec一端是动态拨号可以做吗?
西安还有2个拨号宽带,我只列出的和专线有关的路由。


ipsec no-nat-process enable这个deny ipsec流了吧?
gre over IPSec一端是动态拨号可以做吗?
西安还有2个拨号宽带,我只列出的和专线有关的路由。
- 2021-12-03回答
- 评论(0)
- 举报
-
(0)
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明

西安还有2个拨号宽带,我只列出的和专线有关的路由。