问题描述:
A端:迪普防火墙(公网固定IP)--------------- B端: F5(公网静态映射)-----F5010(私网地址)
F5010 与 迪普防火墙做IPSEC对接,使用野蛮模式对接
问题:IKE 建立不成功,IPSEC不成功
# ipsec transform-set 4000_IPv4_1
esp encryption-algorithm 3des-cbc esp
authentication-algorithm sha1
#
ipsec policy 4000 1 isakmp
transform-set 4000_IPv4_1
security acl 3000
local-address 11.14.248.65
remote-address 211.92.142.35
ike-profile 4000_IPv4_1
#
ike profile 4000_IPv4_1
keychain 4000_IPv4_1
exchange-mode aggressive
local-identity address 222.85.230.63
match remote identity address 211.92.142.35 255.255.255.255
match local address 11.14.248.65
proposal 1
#
ike proposal 1
encryption-algorithm 3des-cbc
dh group2
#
ike keychain 4000_IPv4_1
match local address Ten-GigabitEthernet1/0/24
pre-shared-key address 211.92.142.35 255.255.255.255 key cipher $c$3$IQ/Snis4BtKAIAYoBlX02xCWWFq8LMTmvmBD
<GSH-BGHLW-VPN5010-01>res ike sa
<GSH-BGHLW-VPN5010-01>dis ike sa Connection-ID Remote Flag DOI ------------------------------------------------------------------
<GSH-BGHLW-VPN5010-01>
<GSH-BGHLW-VPN5010-01>
<GSH-BGHLW-VPN5010-01
dis ike sa Connection-ID Remote Flag DOI ------------------------------------------------------------------
<GSH-BGHLW-VPN5010-01>
<GSH-BGHLW-VPN5010-01>
<GSH-BGHLW-VPN5010-01>
<GSH-BGHLW-VPN5010-01>
<GSH-BGHLW-VPN5010-01>
<GSH-BGHLW-VPN5010-01>
<GSH-BGHLW-VPN5010-01>t m
The current terminal is enabled to display logs.
<GSH-BGHLW-VPN5010-01>*Jan 26 16:36:40:880 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Sent delete SA message to all nodes, message type is 0x16. *Jan 26 16:36:40:880 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; The SA doesn't exist in kernel. *Jan 26 16:36:41:344 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Can't find block-flow node. *Jan 26 16:36:41:344 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:36:41:344 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:36:41:344 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Sent SA-Acquire message : SP ID = 0 *Jan 26 16:36:41:344 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Received negotiatiate SA message from IPsec kernel. *Jan 26 16:36:41:344 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Got SA time-based soft lifetime settings when filling Sp data. Configured soft lifetime buffer : 0 seconds. Configured global soft lifetime buffer : 0 seconds. *Jan 26 16:36:41:345 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Received message from ipsec, message type is 0. *Jan 26 16:36:41:345 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Received SA acquire message from IPsec. *Jan 26 16:36:41:345 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; IKE thread 1099111125680 processes a job. *Jan 26 16:36:41:345 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Received SA acquire message from IPsec. *Jan 26 16:36:41:345 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Set IPsec SA state to IKE_P2_STATE_INIT. *Jan 26 16:36:41:345 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; IKE SA not found. Initiate IKE SA negotiation. *Jan 26 16:36:41:345 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Obtained profile 4000_IPv4_1. *Jan 26 16:36:41:345 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Initiator created an SA for peer 211.92.142.35, local port 500, remote port 500. *Jan 26 16:36:41:345 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Set IKE SA state to IKE_P1_STATE_INIT. *Jan 26 16:36:41:345 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; IKE thread 1099111125680 processes a job. *Jan 26 16:36:41:345 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Begin Aggressive mode exchange. *Jan 26 16:36:41:346 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Found pre-shared key that matches address 211.92.142.35 in keychain 4000_IPv4_1. *Jan 26 16:36:41:346 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Encryption algorithm is 3DES-CBC. *Jan 26 16:36:41:346 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Hash algorithm is HMAC-SHA1. *Jan 26 16:36:41:346 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 DH group 2. *Jan 26 16:36:41:346 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Authentication method is Pre-shared key. *Jan 26 16:36:41:346 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Lifetime type is in seconds. *Jan 26 16:36:41:346 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Life duration is 86400. *Jan 26 16:36:41:346 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Construct transform payload for transform 1. *Jan 26 16:36:41:346 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Constructed SA payload. *Jan 26 16:36:41:347 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Construct KE payload. *Jan 26 16:36:41:347 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Construct NONCE payload. *Jan 26 16:36:41:347 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Local ID type: IPV4_ADDR (1). *Jan 26 16:36:41:347 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Local ID value: 222.85.230.63. *Jan 26 16:36:41:347 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Construct ID payload. *Jan 26 16:36:41:347 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Construct DPD vendor ID payload. *Jan 26 16:36:41:347 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Construct NAT-T rfc3947 vendor ID payload. *Jan 26 16:36:41:347 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Construct NAT-T draft3 vendor ID payload. *Jan 26 16:36:41:347 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Construct NAT-T draft2 vendor ID payload. *Jan 26 16:36:41:347 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Construct NAT-T draft1 vendor ID payload. *Jan 26 16:36:41:348 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Construct XAUTH Cisco Unity 1.0 vendor ID payload. *Jan 26 16:36:41:348 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Construct XAUTH draft6 vendor ID payload. *Jan 26 16:36:41:348 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 IKE SA state changed from IKE_P1_STATE_INIT to IKE_P1_STATE_SEND1. *Jan 26 16:36:41:348 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sending packet to 211.92.142.35 remote port 500, local port 500. *Jan 26 16:36:41:348 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 I-COOKIE: 8c8e73324c770a69 R-COOKIE: 0000000000000000 next payload: SA version: ISAKMP Version 1.0 exchange mode: Aggressive flags: message ID: 0 length: 380 *Jan 26 16:36:41:348 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sending an IPv4 packet. *Jan 26 16:36:41:348 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sent data to socket successfully. *Jan 26 16:36:43:545 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:36:43:545 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:36:43:545 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:36:45:746 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:36:45:747 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:36:45:747 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:36:46:878 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Retransmit phase 1 packet. *Jan 26 16:36:46:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sending packet to 211.92.142.35 remote port 500, local port 500. *Jan 26 16:36:46:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 I-COOKIE: 8c8e73324c770a69 R-COOKIE: 0000000000000000 next payload: SA version: ISAKMP Version 1.0 exchange mode: Aggressive flags: message ID: 0 length: 380 *Jan 26 16:36:46:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sending an IPv4 packet. *Jan 26 16:36:46:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sent data to socket successfully. *Jan 26 16:36:47:947 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:36:47:947 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:36:47:947 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:36:50:149 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:36:50:149 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:36:50:149 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:36:52:349 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:36:52:349 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:36:52:349 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:36:54:551 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:36:54:551 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:36:54:551 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:36:56:751 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:36:56:751 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:36:56:751 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:36:58:952 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:36:58:952 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:36:58:952 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:36:59:878 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Retransmit phase 1 packet. *Jan 26 16:36:59:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sending packet to 211.92.142.35 remote port 500, local port 500. *Jan 26 16:36:59:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 I-COOKIE: 8c8e73324c770a69 R-COOKIE: 0000000000000000 next payload: SA version: ISAKMP Version 1.0 exchange mode: Aggressive flags: message ID: 0 length: 380 *Jan 26 16:36:59:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sending an IPv4 packet. *Jan 26 16:36:59:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sent data to socket successfully. *Jan 26 16:37:01:153 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:01:153 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:01:153 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:03:354 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:03:354 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:03:354 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:05:554 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:05:554 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:05:554 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:07:755 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:07:755 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:07:755 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:09:956 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:09:956 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:09:956 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:10:878 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Retransmit phase 1 packet. *Jan 26 16:37:10:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sending packet to 211.92.142.35 remote port 500, local port 500. *Jan 26 16:37:10:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 I-COOKIE: 8c8e73324c770a69 R-COOKIE: 0000000000000000 next payload: SA version: ISAKMP Version 1.0 exchange mode: Aggressive flags: message ID: 0 length: 380 *Jan 26 16:37:10:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sending an IPv4 packet. *Jan 26 16:37:10:879 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Sent data to socket successfully. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Received packet successfully. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received packet from 211.92.142.35 source port 500 destination port 500. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 I-COOKIE: 8c8e73324c770a69 R-COOKIE: 2a2a2cfde7d3fd00 next payload: SA version: ISAKMP Version 1.0 exchange mode: Aggressive flags: message ID: 0 length: 472 *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; IKE thread 1099111125680 processes a job. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Phase1 process started. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received ISAKMP Security Association Payload. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received ISAKMP Key Exchange Payload. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received ISAKMP Nonce Payload. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received ISAKMP Identification Payload. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received ISAKMP Vendor ID Payload. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received ISAKMP Vendor ID Payload. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received ISAKMP NAT-D Payload. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received ISAKMP NAT-D Payload. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received ISAKMP Hash Payload. *Jan 26 16:37:10:890 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Process NONCE payload. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Process KE payload. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Process ID payload. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Peer ID type: IPV4_ADDR (1). *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Peer ID value: address 211.92.142.35. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Process SA payload. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Check ISAKMP transform 1. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Encryption algorithm is 3DES-CBC. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 HASH algorithm is HMAC-SHA1. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 DH group is 2. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Authentication method is Pre-shared key. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Lifetime type is 1. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Life duration is 86400. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Found pre-shared key in keychain 4000_IPv4_1 matching address 211.92.142.35. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Attributes is acceptable. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Oakley transform 1 is acceptable. *Jan 26 16:37:10:891 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Process vendor ID payload. *Jan 26 16:37:10:892 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Vendor ID DPD is matched. *Jan 26 16:37:10:892 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Vendor ID NAT-T rfc3947 is matched. *Jan 26 16:37:10:892 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received 2 NAT-D payload. *Jan 26 16:37:10:892 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 I am behind NAT. *Jan 26 16:37:10:892 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/4500 Float port to local port 4500 and remote port 4500 *Jan 26 16:37:10:893 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/4500 Verify HASH payload. *Jan 26 16:37:10:893 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/4500 HASH: 826e469a 6bb3da6b 4b6a0de9 569e459a 412632e8 *Jan 26 16:37:10:893 2022 GSH-BGHLW-VPN5010-01 IKE/7/ERROR: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/4500 Failed to verify the peer HASH. *Jan 26 16:37:10:893 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/4500 Construct notification packet: AUTHENTICATION_FAILED. *Jan 26 16:37:10:893 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/4500 Sending packet to 211.92.142.35 remote port 4500, local port 4500. *Jan 26 16:37:10:893 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/4500 I-COOKIE: 8c8e73324c770a69 R-COOKIE: 2a2a2cfde7d3fd00 next payload: NOTIFY version: ISAKMP Version 1.0 exchange mode: Info flags: message ID: 0 length: 56 *Jan 26 16:37:10:893 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/4500 Sending an IPv4 packet. *Jan 26 16:37:10:893 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/4500 Sent data to socket successfully. *Jan 26 16:37:12:157 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:12:158 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:12:158 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:14:358 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:14:358 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:14:358 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:15:894 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Received packet successfully. *Jan 26 16:37:15:894 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received packet from 211.92.142.35 source port 500 destination port 500. *Jan 26 16:37:15:894 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 I-COOKIE: 8c8e73324c770a69 R-COOKIE: 2a2a2cfde7d3fd00 next payload: SA version: ISAKMP Version 1.0 exchange mode: Aggressive flags: message ID: 0 length: 472 *Jan 26 16:37:15:894 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; IKE thread 1099111125680 processes a job. *Jan 26 16:37:15:894 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Phase1 process started. *Jan 26 16:37:15:894 2022 GSH-BGHLW-VPN5010-01 IKE/7/ERROR: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Can't find IKE SA. *Jan 26 16:37:16:559 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:16:559 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:16:559 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:18:759 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:18:759 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:18:759 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:20:032 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Received packet successfully. *Jan 26 16:37:20:032 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received packet from 211.92.142.35 source port 500 destination port 500. *Jan 26 16:37:20:032 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 I-COOKIE: 8c8e73324c770a69 R-COOKIE: 2a2a2cfde7d3fd00 next payload: SA version: ISAKMP Version 1.0 exchange mode: Aggressive flags: message ID: 0 length: 472 *Jan 26 16:37:20:033 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; IKE thread 1099111125680 processes a job. *Jan 26 16:37:20:033 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Phase1 process started. *Jan 26 16:37:20:034 2022 GSH-BGHLW-VPN5010-01 IKE/7/ERROR: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Can't find IKE SA. *Jan 26 16:37:20:961 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:20:961 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:20:961 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:23:163 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:23:163 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:23:163 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:25:363 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:25:363 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:25:363 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:27:564 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:27:564 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:27:564 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:29:764 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:29:764 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:29:764 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:30:042 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Received packet successfully. *Jan 26 16:37:30:042 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received packet from 211.92.142.35 source port 500 destination port 500. *Jan 26 16:37:30:043 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 I-COOKIE: 8c8e73324c770a69 R-COOKIE: 2a2a2cfde7d3fd00 next payload: SA version: ISAKMP Version 1.0 exchange mode: Aggressive flags: message ID: 0 length: 472 *Jan 26 16:37:30:043 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; IKE thread 1099111125680 processes a job. *Jan 26 16:37:30:044 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Phase1 process started. *Jan 26 16:37:30:044 2022 GSH-BGHLW-VPN5010-01 IKE/7/ERROR: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Can't find IKE SA. *Jan 26 16:37:31:966 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:31:966 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:31:966 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:34:166 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:34:166 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:34:166 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:36:367 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:36:367 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:36:367 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:38:568 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:38:568 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:38:568 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:40:706 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Received packet successfully. *Jan 26 16:37:40:706 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received packet from 211.92.142.35 source port 500 destination port 500. *Jan 26 16:37:40:706 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 I-COOKIE: 8c8e73324c770a69 R-COOKIE: 2a2a2cfde7d3fd00 next payload: SA version: ISAKMP Version 1.0 exchange mode: Aggressive flags: message ID: 0 length: 472 *Jan 26 16:37:40:707 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; IKE thread 1099111125680 processes a job. *Jan 26 16:37:40:707 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Phase1 process started. *Jan 26 16:37:40:707 2022 GSH-BGHLW-VPN5010-01 IKE/7/ERROR: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Can't find IKE SA. *Jan 26 16:37:40:770 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:40:770 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:40:770 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:42:970 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:42:970 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:42:970 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:45:171 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:45:171 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:45:171 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:47:372 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:47:372 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:47:372 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:49:573 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:49:573 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:49:573 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:50:716 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Received packet successfully. *Jan 26 16:37:50:716 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Received packet from 211.92.142.35 source port 500 destination port 500. *Jan 26 16:37:50:716 2022 GSH-BGHLW-VPN5010-01 IKE/7/PACKET: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 I-COOKIE: 8c8e73324c770a69 R-COOKIE: 2a2a2cfde7d3fd00 next payload: SA version: ISAKMP Version 1.0 exchange mode: Aggressive flags: message ID: 0 length: 472 *Jan 26 16:37:50:717 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; IKE thread 1099111125680 processes a job. *Jan 26 16:37:50:717 2022 GSH-BGHLW-VPN5010-01 IKE/7/EVENT: -COntext=1; Phase1 process started. *Jan 26 16:37:50:717 2022 GSH-BGHLW-VPN5010-01 IKE/7/ERROR: -COntext=1; vrf = 0, local = 11.14.248.65, remote = 211.92.142.35/500 Can't find IKE SA. *Jan 26 16:37:51:773 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:51:773 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:51:773 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:53:974 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:53:974 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:53:974 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:56:175 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:56:176 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:56:176 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:37:58:377 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:37:58:377 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:37:58:377 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:38:00:577 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:38:00:577 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:38:00:577 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:38:02:778 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:38:02:778 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:38:02:778 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. *Jan 26 16:38:04:978 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:38:04:978 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:38:04:978 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. <GSH-BGHLW-VPN5010-01> <GSH-BGHLW-VPN5010-01> <GSH-BGHLW-VPN5010-01>unt*Jan 26 16:38:07:180 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:38:07:180 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:38:07:180 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. o <GSH-BGHLW-VPN5010-01>unto t ^ % Unrecognized command found at '^' position. <GSH-BGHLW-VPN5010-01> <GSH-BGHLW-VPN5010-01>undo t *Jan 26 16:38:09:380 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:38:09:380 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:38:09:380 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. <GSH-BGHLW-VPN5010-01>undo t , ^ % Unrecognized command found at '^' position. <GSH-BGHLW-VPN5010-01>undo t *Jan 26 16:38:11:581 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/EVENT: -COntext=1; Found block-flow node. *Jan 26 16:38:11:581 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/PACKET: -COntext=1; Failed to find SA by SP, SP Index = 0, SP Convert-Seq = 65536. *Jan 26 16:38:11:581 2022 GSH-BGHLW-VPN5010-01 IPSEC/7/ERROR: -COntext=1; The reason of dropping packet is no available IPsec tunnel. <GSH-BGHLW-VPN5010-01>undo t m The current terminal is disabled to display logs.
组网及组网描述:
- 2022-01-26提问
- 举报
-
(0)
最佳答案

您好,参考这个
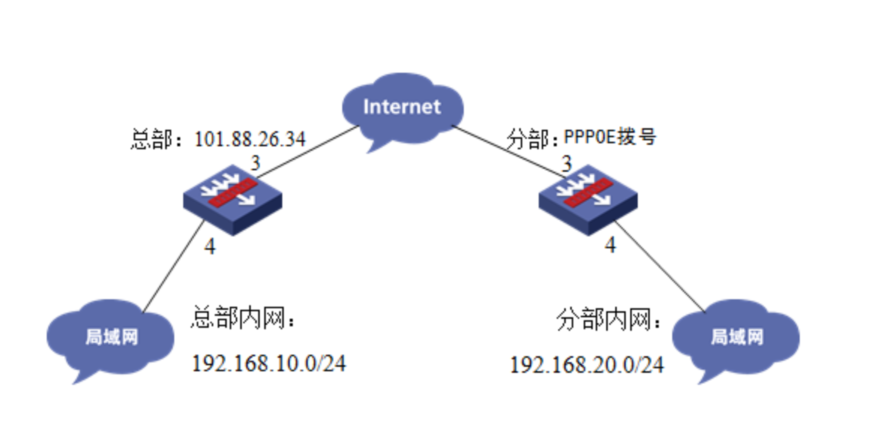
两台防火墙一端固定IP,一端PPPOE拨号搭建IPSEC VPN配置案例(野蛮模式命令行)
1.2 配置需求及实现的效果
总部和分部各有一台防火墙部署在互联网出口,因业务需要两端内网需要通过VPN相互访问。IP地址及接口规划如下表所示:
|
公司名称 |
外网接口 |
公网地址/掩码 |
公网网关 |
内网接口 |
内网地址/掩码 |
|
总部 |
1/0/3 |
101.88.26.34/30 |
101.88.26.33 |
1/0/4 |
192.168.10.0/24 |
|
分部 |
1/0/3 |
PPPOE拨号 |
自动获取网关 |
1/0/4 |
192.168.20.0/24 |
2 组网图
3 配置步骤
3.1 两端防火墙上网配置
防火墙上网配置请参考“2.3.2 防火墙外网使用固定IP地址上网配置方法”及“2.3.1 防火墙外网使用拨号上网配置方法”进行配置,本文只针对IPSEC VPN配置进行介绍。
3.2 总部侧排除IPSEC兴趣流不做NAT
#创建acl 3888调用在外网接口用于排除IPSEC兴趣流不做NAT。
[H3C]acl advanced 3888
[H3C-acl-ipv4-adv-3888]rule deny ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255
[H3C-acl-ipv4-adv-3888]rule permit ip source any
[H3C-acl-ipv4-adv-3888]quit
3.3 总部侧创建IPSEC安全提议
#加密类型设置为aes-cbc-128,认证类型设置为sha1。
[H3C]ipsec transform-set GE1/0/3_IPv4_1
[H3C-ipsec-transform-set-1] esp encryption-algorithm aes-cbc-128
[H3C-ipsec-transform-set-1] esp authentication-algorithm sha1
[H3C-ipsec-transform-set-1]quit
3.4 总部侧创建IKE安全提议
#IKE安全提议默认的认证类型为sha1,加密类型为DES-CBC,DH组为DH1,所以不需要配置也存在这些参数。
[H3C]ike proposal 1
[H3C-ike-proposal-1]quit
3.5 总部侧创建IKE安全密钥
#创建IKE密钥,地址填写0.0.0.0/0,密码设置为123456。
[H3C]ike keychain 1
[H3C-ike-keychain-1]pre-shared-key address 0.0.0.0 0.0.0.0 key simple 123456
[H3C-ike-keychain-1]quit
3.6 总部侧创建IKE安全框架
#创建IKE安全框架,协商模式调整为野蛮模式。本端身份识别为center,分部身份识别为branch。
[H3C]ike profile 1
[H3C-ike-profile-1]keychain 1
[H3C-ike-profile-1] exchange-mode aggressive
[H3C-ike-profile-1] local-identity fqdn center
[H3C-ike-profile-1]match remote identity address 0.0.0.0 0.0.0.0
[H3C-ike-profile-1]match remote identity fqdn branch
[H3C-ike-profile-1]proposal 1
[H3C-ike-profile-1]quit
3.7 总部侧创建IPSEC安全策略模板
[H3C]ipsec policy-template GE1/0/3 1
[H3C-ipsec-policy- template-GE1/0/3-1]transform-set GE1/0/3_IPv4_1
[H3C-ipsec-policy- template-GE1/0/3-1]local-address 101.88.26.34
[H3C-ipsec-policy- template-GE1/0/3-1]ike-profile 1
[H3C-ipsec-policy- template-GE1/0/3-1]quit
3.8 总部侧创建IPSEC安全策略
#创建IKE安全策略GE1/0/3将安全策略模板和安全策略绑定。
[H3C]ipsec policy GE1/0/3 1 isakmp template GE1/0/3
3.9 总部侧外网接口调用IPSEC策略和NAT动态转换策略
[H3C]interface GigabitEthernet 1/0/3
[H3C-GigabitEthernet1/0/3]ipsec apply policy GE1/0/3
[H3C-GigabitEthernet1/0/3]nat outbound 3888
[H3C-GigabitEthernet1/0/3]quit
3.10 保存配置
[H3C]save force
3.11 分部侧创建IPSEC兴趣流匹配到总部的数据
#创建IPSEC的感兴趣流,用于匹配IPSEC数据。
<H3C>system
[H3C]acl advanced 3999
[H3C-acl-ipv4-adv-3999]rule permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
[H3C-acl-ipv4-adv-3999]quit
#创建acl 3888调用在外网接口用于排除IPSEC兴趣流不做NAT。
[H3C]acl advanced 3888
[H3C-acl-ipv4-adv-3888]rule deny ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
[H3C-acl-ipv4-adv-3888]rule permit ip source any
[H3C-acl-ipv4-adv-3888]quit
3.12 分部侧创建IPSEC安全提议
#加密类型设置为aes-cbc-128,认证类型设置为sha1。
[H3C]ipsec transform-set GE1/0/3_IPv4_1
[H3C-ipsec-transform-set-1] esp encryption-algorithm aes-cbc-128
[H3C-ipsec-transform-set-1] esp authentication-algorithm sha1
[H3C-ipsec-transform-set-1]quit
3.13 分部侧创建IKE安全提议
#IKE安全提议默认的认证类型为sha1,加密类型为DES-CBC,DH组为DH1,所以不需要配置也存在这些参数。
[H3C]ike proposal 1
[H3C-ike-proposal-1]quit
3.14 分部侧创建IKE安全密钥
#创建IKE密钥,地址填写总部侧设备的公网IP,密码设置为123456。
[H3C]ike keychain 1
[H3C-ike-keychain-1] pre-shared-key address 101.88.26.34 255.255.255.255 key simple 123456
[H3C-ike-keychain-1]quit
3.15 分部侧创建IKE安全框架
#创建IKE安全框架,匹配keychain 1安全密匙,协商模式调整为野蛮模式。本端身份识别为branch,分部身份识别为center,并制定对端地址为总部侧公网地址。
[H3C]ike profile 1
[H3C-ike-profile-1]keychain 1
[H3C-ike-profile-1]exchange-mode aggressive
[H3C-ike-profile-1] local-identity fqdn branch
[H3C-ike-profile-1] match remote identity fqdn center
[H3C-ike-profile-1] match remote identity address 101.88.26.34 255.255.255.255
[H3C-ike-profile-1]proposal 1
[H3C-ike-profile-1]quit
3.16 分部侧创建IPSEC安全策略
#创建IKE安全策略GE1/0/3将transform-set、acl、ike-profile、本端地址、对端地址关联起来。
[H3C]ipsec policy GE1/0/3 1 isakmp
[H3C-ipsec-policy-isakmp-GE1/0/3-1] transform-set GE1/0/3_IPv4_1
[H3C-ipsec-policy-isakmp-GE1/0/3-1]security acl 3999
[H3C-ipsec-policy-isakmp-GE1/0/3-1] remote-address 101.88.26.34
[H3C-ipsec-policy-isakmp-GE1/0/3-1]ike-profile 1
[H3C-ipsec-policy-isakmp-GE1/0/3-1]quit
3.17 分部侧外网接口调用IPSEC策略和NAT动态转换策略
[H3C]interface GigabitEthernet 1/0/3
[H3C-GigabitEthernet1/0/3]ipsec apply policy GE1/0/3
[H3C-GigabitEthernet1/0/3]nat outbound 3888
[H3C-GigabitEthernet1/0/3]quit
3.18 保存配置
[H3C]save force
- 2022-01-27回答
- 评论(0)
- 举报
-
(0)


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明



暂无评论