AP反制
- 0关注
- 3收藏,4694浏览
问题描述:
需求:对除了内网AP外的其他AP进行反制,内网AP和AC有不同厂家的设备,在SSID都相同的情况下,怎么去匹配区分是内网的AP还是非法的AP?
配置对外部AP进行反制:
countermeasure external-ap
这个命令是通过什么机制来识别是内网AP还是非法的外部AP呢?
组网及组网描述:
无
- 2022-06-29提问
- 举报
-
(0)
最佳答案

分类与反制配置举例
1. 组网需求
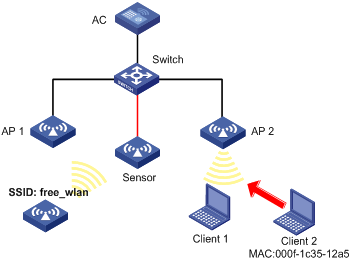
如图1-3所示,AP通过交换机与AC相连,AP1和AP2为Client提供无线服务,SSID为“abc”,在Sensor上开启WIPS功能,配置分类策略,将非法客户端的MAC地址(000f-1c35-12a5)添加到静态禁用列表中,将SSID“abc”添加到静态信任列表中,要求对检测到的潜在外部AP和未授权客户端进行反制。
2. 组网图
图1-3 WIPS分类与反制组网图
3. 配置步骤
在AC上完成无线服务的相关配置,具体配置步骤可参见“WLAN配置指导”中的“WLAN接入”,此处不再重复。
# 配置虚拟安全域vsd1。
<AC> system-view
[AC] wips
[AC-wips] virtual-security-domain vsd1
[AP-wips-vsd-vsd1] quit
[AC-wips] quit
# 创建AP名称为Sensor,开启WIPS功能。
[AC] wlan ap Sensor model WA4320i-ACN
[AC-wlan-ap-Sensor] serial-id 210235A1GQB139000435
[AC-wlan-ap-Sensor] radio 1
[AC-wlan-ap-Sensor-radio-1] radio enable
[AC-wlan-ap-Sensor-radio-1] wips enable
[AC-wlan-ap-Sensor-radio-1] quit
# 配置Sensor加入虚拟安全域vsd1。
[AC-wlan-ap-Sensor] wips virtual-security-domain vsd1
[AC-wlan-ap-Sensor] quit
# 配置分类策略class1,将Client 2的MAC地址配置禁用MAC地址,并且将名为“abc”的SSID配置为信任SSID。
[AC] wips
[AC-wips] classification policy class1
[AC-wips-cls-class1] block mac-address 000f-1c35-12a5
[AC-wips-cls-class1] trust ssid abc
[AC-wips-cls-class1] quit
# 虚拟安全域vsd1应用分类策略class1。
[AC-wips] virtual-security-domain vsd1
[AC-wips-vsd-vsd1] apply classification policy class1
[AC-wips-vsd-vsd1] quit
# 配置反制策略protect,反制未授权客户端和潜在外部AP。
[AC-wips] countermeasure policy protect
[AC-wips-cms-protect] countermeasure unauthorized-client
[AC-wips-cms-protect] countermeasure potential-external-ap
[AC-wips-cms-protect] quit
# 虚拟安全域vsd1应用反制策略protect。
[AC-wips] virtual-security-domain vsd1
[AC-wips-vsd-vsd1] apply countermeasure policy protect
[AC-wips-vsd-vsd1] quit
[AC-wips] quit
4. 验证配置
(1) 通过display wips virtual-security-domain命令查看无线设备的分类结果。
[AC] display wips virtual-security-domain vsd1 device
Total 3 detected devices in virtual-security-domain vsd1
Class: Auth - authorization; Ext - extern; Mis - mistake;
Unauth - unauthorized; Uncate - uncategorized;
(A) - associate; (C) - config; (P) - potential
MAC address Type Class Duration Sensors Channel Status
00e0-fc00-5829 AP Auth 00h 10m 24s 1 149 Active
000f-e228-2528 AP Auth 00h 10m 04s 1 149 Active
000f-e223-1616 AP Ext(P) 00h 10m 46s 1 149 Active
000f-1c35-12a5 Client Unauth 00h 10m 02s 1 149 Active
000f-e201-0102 Client Auth 00h 10m 02s 1 149 Active
在虚拟安全域vsd1,MAC地址为000f-e223-1616的AP被分类成潜在外部AP,MAC地址为000f-1c35-12a5的客户端被分类为未授权的客户端。
(2) 通过命令行display wips virtual-security-domain vsd1 countermeasure record命令查看反制过的设备记录信息。
[AC] display wips virtual-security-domain vsd1 countermeasure record
Total 2 times countermeasure, current 2 countermeasure record in virtual-security-domain vsd1
Reason: Attack; Ass - associated; Black - blacklist;
Class - classification; Manu - manual;
MAC address Type Reason Countermeasure AP Radio ID Time
000f-e223-1616 AP Class Sensor 1 2014-06-03/10:30:36
000f-1c35-12a5 Client Class Sensor 1 2014-06-03/09:13:26
在虚拟安全域vsd1,MAC地址为000f-1c35-12a5的未授权客户端和MAC地址为000f-e223-1616的潜在外部AP被反制。
1.15.2 WIPS畸形报文检测和泛洪攻击检测配置举例
1. 组网需求
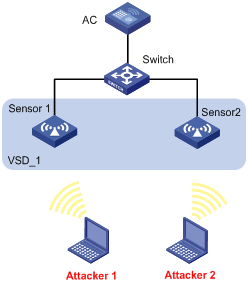
如图1-4所示,AP通过交换机与AC相连,将两台AP分别配置为Sensor,配置虚拟安全域VSD_1,并配置两台Sensor属于这个虚拟安全域,当检测到攻击者对无线网络进行IE重复的畸形报文或Beacon帧泛洪攻击时,AP向AC发送告警信息。
2. 组网图
3. 配置步骤
在AC上完成无线服务的相关配置,具体配置步骤可参见“WLAN配置指导”中的“WLAN接入”,此处不再重复。
# 创建AP名称为sensor1,开启WIPS功能。
<AC> system-view
[AC] wlan ap sensor1 model WA4320i-ACN
[AC-wlan-ap-sensor1] serial-id 210235A1GQB139000435
[AC-wlan-ap-sensor1] radio 1
[AC-wlan-ap-sensor1-radio-1] radio enable
[AC-wlan-ap-sensor1-radio-1] wips enable
[AC-wlan-ap-sensor1-radio-1] return
# 创建AP名称为sensor2,开启WIPS功能。
<AC> system-view
[AC] wlan ap sensor2 model WA4320i-ACN
[AC-wlan-ap-sensor2] serial-id 210235A1GQB139000436
[AC-wlan-ap-sensor2] radio 1
[AC-wlan-ap-sensor2-radio-1] radio enable
[AC-wlan-ap-sensor2-radio-1] wips enable
[AC-wlan-ap-sensor2-radio-1] quit
[AC-wlan-ap-sensor2] quit
# 配置虚拟安全域VSD_1。
[AC] wips
[AC-wips] virtual-security-domain VSD_1
[AP-wips-vsd-VSD_1] quit
# 创建攻击检测策略,当检测到IE重复的畸形报文和Beacon帧泛洪攻击时,向AC发送日志信息或告警信息。检测IE重复的畸形报文的静默时间为50秒,检测Beacon帧的统计周期为100秒,触发阈值为200,静默时间为50秒。
[AC-wips] detect policy dtc1
[AC-wips-dtc-dtc1] malformed duplicated-ie quiet 50
[AC-wips-dtc-dtc1] flood beacon interval 100 quiet 50 threshold 200
[AC-wips-dtc-dtc1] quit
# 在虚拟安全域VSD_1上应用攻击检测策略。
[AC-wips] virtual-security-domain VSD_1
[AC-wips-vsd-VSD_1] apply detect policy dtc1
[AC-wips-vsd-VSD_1] quit
[AC-wips] quit
# 配置sensor1加入虚拟安全域VSD_1。
[AC] wlan ap sensor1
[AC-wlan-ap-sensor1] wips virtual-security-domain VSD_1
[AC-wlan-ap-sensor1] quit
# 配置sensor2加入虚拟安全域VSD_1。
[AC] wlan ap sensor2
[AC-wlan-ap-sensor2] wips virtual-security-domain VSD_1
[AC-wlan-ap-sensor2] return
4. 验证结果
(1) 当网络中没有攻击者时,在AC上通过命令行display wips statistics receive命令查看收到报文的统计信息,畸形报文和泛洪报文的统计个数为0。
<AC> display wips statistics receive
Information from sensor 1
Information about attack statistics:
Detected association-request flood messages: 0
Detected authentication flood messages: 0
Detected beacon flood messages: 0
Detected block-ack flood messages: 0
Detected cts flood messages: 0
Detected deauthentication flood messages: 0
Detected disassociation flood messages: 0
Detected eapol-start flood messages: 0
Detected null-data flood messages: 0
Detected probe-request flood messages: 0
Detected reassociation-request flood messages: 0
Detected rts flood messages: 0
Detected duplicated-ie messages: 0
Detected fata-jack messages: 0
Detected illegal-ibss-ess messages: 0
Detected invalid-address-combination messages: 0
Detected invalid-assoc-req messages: 0
Detected invalid-auth messages: 0
Detected invalid-deauth-code messages: 0
Detected invalid-disassoc-code messages: 0
Detected invalid-ht-ie messages: 0
Detected invalid-ie-length messages: 0
Detected invalid-pkt-length messages: 0
Detected large-duration messages: 0
Detected null-probe-resp messages: 0
Detected overflow-eapol-key messages: 0
Detected overflow-ssid messages: 0
Detected redundant-ie messages: 0
Detected AP spoof AP messages: 0
Detected AP spoof client messages: 0
Detected AP spoof ad-hoc messages: 0
Detected ad-hoc spoof AP messages: 0
Detected client spoof AP messages: 0
Detected weak IV messages: 0
Detected excess AP messages: 0
Detected excess client messages: 0
Detected sig rule messages: 0
Information from sensor 2
Information about attack statistics:
Detected association-request flood messages: 0
Detected authentication flood messages: 0
Detected beacon flood messages: 0
Detected block-ack flood messages: 0
Detected cts flood messages: 0
Detected deauthentication flood messages: 0
Detected disassociation flood messages: 0
Detected eapol-start flood messages: 0
Detected null-data flood messages: 0
Detected probe-request flood messages: 0
Detected reassociation-request flood messages: 0
Detected rts flood messages: 0
Detected duplicated-ie messages: 0
Detected fata-jack messages: 0
Detected illegal-ibss-ess messages: 0
Detected invalid-address-combination messages: 0
Detected invalid-assoc-req messages: 0
Detected invalid-auth messages: 0
Detected invalid-deauth-code messages: 0
Detected invalid-disassoc-code messages: 0
Detected invalid-ht-ie messages: 0
Detected invalid-ie-length messages: 0
Detected invalid-pkt-length messages: 0
Detected large-duration messages: 0
Detected null-probe-resp messages: 0
Detected overflow-eapol-key messages: 0
Detected overflow-ssid messages: 0
Detected redundant-ie messages: 0
Detected AP spoof AP messages: 0
Detected AP spoof client messages: 0
Detected AP spoof ad-hoc messages: 0
Detected ad-hoc spoof AP messages: 0
Detected client spoof AP messages: 0
Detected weak IV messages: 0
Detected excess AP messages: 0
Detected excess client messages: 0
Detected sig rule messages: 0
(2) 当检测到IE重复的畸形报文和Beacon帧泛洪攻击时,在AC上通过命令行display wips statistics receive查看收到报文的统计信息,IE重复的畸形报文的统计个数为28和Beacon帧泛洪攻击的统计个数为18。
<AC> display wips statistics receive
Information from sensor 1
Information about attack statistics:
Detected association-request flood messages: 0
Detected authentication flood messages: 0
Detected beacon flood messages: 18
Detected block-ack flood messages: 0
Detected cts flood messages: 0
Detected deauthentication flood messages: 0
Detected disassociation flood messages: 0
Detected eapol-start flood messages: 0
Detected null-data flood messages: 0
Detected probe-request flood messages: 0
Detected reassociation-request flood messages: 0
Detected rts flood messages: 0
Detected duplicated-ie messages: 0
Detected fata-jack messages: 0
Detected illegal-ibss-ess messages: 0
Detected invalid-address-combination messages: 0
Detected invalid-assoc-req messages: 0
Detected invalid-auth messages: 0
Detected invalid-deauth-code messages: 0
Detected invalid-disassoc-code messages: 0
Detected invalid-ht-ie messages: 0
Detected invalid-ie-length messages: 0
Detected invalid-pkt-length messages: 0
Detected large-duration messages: 0
Detected null-probe-resp messages: 0
Detected overflow-eapol-key messages: 0
Detected overflow-ssid messages: 0
Detected redundant-ie messages: 0
Detected AP spoof AP messages: 0
Detected AP spoof client messages: 0
Detected AP spoof ad-hoc messages: 0
Detected ad-hoc spoof AP messages: 0
Detected client spoof AP messages: 0
Detected weak IV messages: 0
Detected excess AP messages: 0
Detected excess client messages: 0
Detected sig rule messages: 0
Information from sensor 2
Information about attack statistics:
Detected association-request flood messages: 0
Detected authentication flood messages: 0
Detected beacon flood messages: 0
Detected block-ack flood messages: 0
Detected cts flood messages: 0
Detected deauthentication flood messages: 0
Detected disassociation flood messages: 0
Detected eapol-start flood messages: 0
Detected null-data flood messages: 0
Detected probe-request flood messages: 0
Detected reassociation-request flood messages: 0
Detected rts flood messages: 0
Detected duplicated-ie messages: 28
Detected fata-jack messages: 0
Detected illegal-ibss-ess messages: 0
Detected invalid-address-combination messages: 0
Detected invalid-assoc-req messages: 0
Detected invalid-auth messages: 0
Detected invalid-deauth-code messages: 0
Detected invalid-disassoc-code messages: 0
Detected invalid-ht-ie messages: 0
Detected invalid-ie-length messages: 0
Detected invalid-pkt-length messages: 0
Detected large-duration messages: 0
Detected null-probe-resp messages: 0
Detected overflow-eapol-key messages: 0
Detected overflow-ssid messages: 0
Detected redundant-ie messages: 0
Detected AP spoof AP messages: 0
Detected AP spoof client messages: 0
Detected AP spoof ad-hoc messages: 0
Detected ad-hoc spoof AP messages: 0
Detected client spoof AP messages: 0
Detected weak IV messages: 0
Detected excess AP messages: 0
Detected excess client messages: 0
Detected sig rule messages: 0
- 2022-06-29回答
- 评论(3)
- 举报
-
(0)
这个配置好像不能实现我说的那个需求吧,如果有个SSID为abc的非法AP接入,不能对其进行反制吧?
第一个案例不符合嘛


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明


如果有个非法的SSID也是abc,那是不是也不能进行反制了