
H3C V7版本是自动的,不需要配置
V5版本的配置,参考
https://www.h3c.com/cn/d_201401/812724_30005_0.htm
- 2023-11-17回答
- 评论(0)
- 举报
-
(0)
暂无评论

您好,请知:
以下是配置案例,请参考:
3.1 组网需求
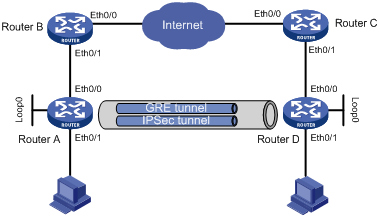
如图1所示,Router A为某组织分支网关,Router D为总部网关,Router B和Router C为边界防火墙使用NAT访问Internet。要求Router A和Router D之间使用GRE over IPsec实现分支与总部间互访。
图1 MSR系列路由器GRE over IPsec总部分支分别穿越NAT配置组网图
设备 | 接口 | IP地址 | 设备 | 接口 | IP地址 |
Router A | Eth0/0 | 10.0.0.1/24 | Router C | Eth0/0 | 1.1.1.2/24 |
| Eth0/1 | 30.0.0.1/24 |
| Eth0/1 | 192.168.1.2/24 |
| Loop0 | 100.0.0.2/32 | Router D | Eth0/0 | 192.168.1.1/24 |
Router B | Eth0/0 | 1.1.1.1/24 |
| Eth0/1 | 20.0.0.1/24 |
| Eth0/1 | 10.0.0.2/24 |
| Loop0 | 100.0.0.1/32 |
3.2 配置思路
· 由于网络中使用了NAT转换来访问Internet,而在IKE协商过程中主模式不支持NAT转换,所以协商模式要配置成野蛮模式,并且要以name的ID类型标识对等体。
· 由于IKE协商使用的源端口号和目的端口号都是500,为了避免NAT地址端口转换的情况,需要在Router B和Router C上配置静态端口映射。
· 为了使IPsec报文能够正常穿越NAT,需要使用UDP封装IPsec ESP报文。
3.3 使用版本
本举例是在Release 2317版本上进行配置和验证的。
3.4 配置注意事项
在配置GRE隧道之前,需确保Router A和Router D之间路由可达。
3.5 配置步骤
3.5.1 Router A的配置
# 配置接口Ethernet0/1的IP地址。
<RouterA> system-view
[RouterA] interface ethernet 0/1
[RouterA-Ethernet0/1] ip address 30.0.0.1 255.255.255.0
[RouterA-Ethernet0/1] quit
# 配置接口Ethernet0/0的IP地址。
[RouterA] interface ethernet 0/0
[RouterA-Ethernet0/0] ip address 10.0.0.1 255.255.255.0
[RouterA-Ethernet0/0] quit
# 配置GRE隧道Tunnel0口的IP地址。
[RouterA] interface tunnel 0
[RouterA-Tunnel0] ip address 172.16.0.2 255.255.255.0
# 配置Tunnel0口的源端地址。
[RouterA-Tunnel0] source 10.0.0.1
# 配置Tunnel0接口的目的地址。
[RouterA-Tunnel0] destination 192.168.1.1
[RouterA-Tunnel0] quit
# 配置到总部网络的默认路由。
[RouterA] ip route-static 0.0.0.0 0.0.0.0 10.0.0.2
# 配置通过GRE隧道访问对端内网的静态路由。
[RouterA] ip route-static 20.0.0.0 255.255.255.0 Tunnel0
# 创建ACL3000,用于匹配通过IPsec隧道的GRE数据流。
[RouterA] acl number 3000
[RouterA-acl-adv-3000] rule 0 permit gre source 172.16.0.0 0.0.0.255 destination
172.16.0.0 0.0.0.255
[RouterA-acl-adv-3000] rule 5 permit gre source 30.0.0.0 0.0.0.255 destination 2
0.0.0.0 0.0.0.255
[RouterA-acl-adv-3000] rule 10 permit gre source 10.0.0.0 0.0.0.255 destination
192.168.1.0 0.0.0.2
[RouterA-acl-adv-3000] quit
# 配置本端安全网关的名字为branch1。
[RouterA] ike local-name branch1
# 创建一个IKE对等体,并进入IKE-Peer视图。
[RouterA] ike peer center
# 配置IKE第一阶段的协商模式为野蛮模式。
[RouterA-ike-peer-center] exchange-mode aggressive
# 配置预共享密钥。
[RouterA-ike-peer-center] pre-shared-key 123
# 选择IKE第一阶段的协商过程中使用ID的类型为name。
[RouterA-ike-peer-center] id-type name
# 配置对端安全网关的名字。
[RouterA-ike-peer-center] remote-name center
# 启用NAT穿越功能。
[RouterA-ike-peer-center] nat traversal
[RouterA-ike-peer-center] quit
# 采用安全提议的缺省配置。
[RouterA] ipsec proposal def
# 配置ESP协议采用md5认证算法。
[RouterA-ipsec-transform-set-def] esp authentication-algorithm md5
[RouterA-ipsec-transform-set-def] quit
# 创建IPsec安全策略center,其协商方式为isakmp。
[RouterA] ipsec policy center 1 isakmp
# 配置IPsec安全策略引用的访问控制列表。
[RouterA-ipsec-policy-isakmp-center-1] security acl 3000
# 在IPsec安全策略中引用IKE对等体。
[RouterA-ipsec-policy-isakmp-center-1] ike-peer center
# 配置IPsec安全策略所引用的IPsec安全提议。
[RouterA-ipsec-policy-isakmp-center-1] proposal def
[RouterA-ipsec-policy-isakmp-center-1] quit
# 在接口Ethernet0/0上应用安全策略。
[RouterA] interface ethernet 0/0
[RouterA-Ethernet0/0] ipsec policy center
[RouterA-Ethernet0/0] quit
3.5.2 Router B的配置
# 配置接口Ethernet0/1的IP地址。
<RouterB> system-view
[RouterB] interface ethernet 0/1
[RouterB-Ethernet0/1] ip address 10.0.0.2 255.255.255.0
[RouterB-Ethernet0/1] quit
# 配置接口Ethernet0/0的IP地址。
[RouterB] interface ethernet 0/0
[RouterB-Ethernet0/0] ip address 1.1.1.1 255.255.255.0
# 配置内部服务器,将相应的外部地址和端口映射到内部服务器的私有地址和端口上。
[RouterB-Ethernet0/0] nat server protocol udp global 1.1.1.1 500 inside 10.0.0.1
500
[RouterB-Ethernet0/0] nat server protocol udp global 1.1.1.1 4500 inside 10.0.0.
1 4500
[RouterB-Ethernet0/0] quit
# 配置到30.0.0.1/24的静态路由。
[RouterB] ip route-static 30.0.0.0 255.255.255.0 10.0.0.1
# 配置到192.168.1.0/24的静态路由。
[RouterB] ip route-static 192.168.1.0 255.255.255.0 1.1.1.2
3.5.3 Router C的配置
# 配置接口Ethernet0/1的IP地址。
<RouterC> system-view
[RouterC] interface ethernet 0/1
[RouterC-Ethernet0/1] ip address 192.168.1.2 255.255.255.0
[RouterC-Ethernet0/1] quit
# 配置接口Ethernet0/0的IP地址。
[RouterC] interface ethernet 0/0
[RouterC-Ethernet0/0] ip address 1.1.1.2 255.255.255.0
# 配置内部服务器,将相应的外部地址和端口映射到内部服务器的私有地址和端口上。
[RouterC-Ethernet0/0] nat server protocol udp global 1.1.1.2 500 inside 192.168.
1.1 500
[RouterC-Ethernet0/0] nat server protocol udp global 1.1.1.2 4500 inside 1
92.168.1.1 4500
[RouterC-Ethernet0/0] quit
# 配置到10.0.0.0/24网段的静态路由。
[RouterC] ip route-static 10.0.0.0 255.255.255.0 1.1.1.1
# 配置到20.0.0.1/24的静态路由。
[RouterC] ip route-static 20.0.0.0 255.255.255.0 192.168.1.1
3.5.4 Router D的配置
# 配置接口Ethernet0/0的IP地址。
<RouterD> system-view
[RouterD] interface ethernet 0/0
[RouterD-Ethernet0/0] ip address 192.168.1.1 255.255.255.0
[RouterD-Ethernet0/0] quit
# 配置接口Ethernet0/1的IP地址。
[RouterD] interface ethernet 0/1
[RouterD-Ethernet0/1] ip address 20.0.0.1 255.255.255.0
[RouterD-Ethernet0/1] quit
# 配置GRE隧道Tunnel0口的IP地址。
[RouterD] interface tunnel 0
[RouterD-Tunnel0] ip address 172.16.0.1 255.255.255.0
# 配置Tunnel0口的源端地址。
[RouterD-Tunnel0] source 192.168.1.1
# 配置Tunnel0接口的目的地址。
[RouterD-Tunnel0] destination 10.0.0.1
[RouterD-Tunnel0] quit
# 配置到分支网络的默认路由。
[RouterD] ip route-static 0.0.0.0 0.0.0.0 192.168.1.2
# 配置通过GRE隧道访问对端内网的静态路由。
[RouterD] ip route-static 30.0.0.0 255.255.255.0 tunnel 0
# 创建ACL3001,用于匹配通过IPsec隧道的GRE数据流。
[RouterD] acl number 3001
[RouterD-acl-adv-3001] rule 0 permit gre source 172.16.0.0 0.0.255.255 destinatio
n 172.16.0.0 0.0.255.255
[RouterD-acl-adv-3001] rule 5 permit gre source 20.0.0.0 0.0.0.255 destination 3
0.0.0.0 0.0.0.255
[RouterD-acl-adv-3001] rule 10 permit gre source 192.168.1.0 0.0.0.255 destinatio
n 10.0.0.0 0.0.0.255
[RouterD-acl-adv-3001] quit
# 配置本端安全网关的名字为center。
[RouterD] ike local-name center
# 创建一个IKE对等体,并进入IKE-Peer视图。
[RouterD] ike peer branch1
# 配置IKE第一阶段的协商模式为野蛮模式。
[RouterD-ike-peer-branch1] exchange-mode aggressive
# 配置预共享密钥。
[RouterD-ike-peer-branch1] pre-shared-key 123
# 选择IKE第一阶段的协商过程中使用ID的类型为name。
[RouterD-ike-peer-branch1] id-type name
# 配置对端安全网关的名字。
[RouterD-ike-peer-branch1] remote-name branch1
# 启用NAT穿越功能。
[RouterD-ike-peer-branch1] nat traversal
[RouterD-ike-peer-branch1] quit
# 采用安全提议的缺省配置。
[RouterD] ipsec proposal default
# 配置ESP协议采用md5认证算法。
[RouterD-ipsec-transform-set-default] esp authentication-algorithm md5
[RouterD-ipsec-transform-set-default] quit
# 创建IPsec安全策略branch1,其协商方式为isakmp。
[RouterD] ipsec policy branch1 1 isakmp
# 配置IPsec安全策略引用的访问控制列表。
[RouterD-ipsec-policy-isakmp-branch1-1] security acl 3001
# 在IPsec安全策略中引用IKE对等体。
[RouterD-ipsec-policy-isakmp-branch1-1] ike-peer branch1
# 配置IPsec安全策略所引用的IPsec安全提议。
[RouterD-ipsec-policy-isakmp-branch1-1] proposal default
[RouterD-ipsec-policy-isakmp-branch1-1] quit
# 在接口Ethernet0/0上应用安全策略。
[RouterD] interface ethernet 0/0
[RouterD-Ethernet0/0] ipsec policy branch1
[RouterD-Ethernet0/0] quit
3.6 验证配置
完成以上配置后,Router A和Router D后面的内网主机可以通过GRE隧道实现互访,且数据经过IPsec进行加密。此处以Router A为例进行验证。
# 可以通过如下显示信息看到,内网主机间实现互通。
<RouterA> ping -a 30.0.0.1 20.0.0.1
PING 20.0.0.1: 56 data bytes, press CTRL_C to break
Reply from 20.0.0.1: bytes=56 Sequence=0 ttl=255 time=2 ms
Reply from 20.0.0.1: bytes=56 Sequence=1 ttl=255 time=1 ms
Reply from 20.0.0.1: bytes=56 Sequence=2 ttl=255 time=1 ms
Reply from 20.0.0.1: bytes=56 Sequence=3 ttl=255 time=2 ms
Reply from 20.0.0.1: bytes=56 Sequence=4 ttl=255 time=2 ms
--- 20.0.0.1 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 1/1/2 ms
# 可以通过如下显示信息看到,GRE隧道建立成功并有内网数据通过。
<RouterA> display interface tunnel0
Tunnel0 current state: UP
Line protocol current state: UP
Description: Tunnel0 Interface
The Maximum Transmit Unit is 1476
Internet Address is 172.16.0.2/24 Primary
Encapsulation is TUNNEL, service-loopback-group ID not set.
Tunnel source 10.0.0.1, destination 192.168.1.1
Tunnel bandwidth 64 (kbps)
Tunnel keepalive disabled
Tunnel protocol/transport GRE/IP
GRE key disabled
Checksumming of GRE packets disabled
Output queue : (Urgent queuing : Size/Length/Discards) 0/100/0
Output queue : (Protocol queuing : Size/Length/Discards) 0/500/0
Output queue : (FIFO queuing : Size/Length/Discards) 0/75/0
Last clearing of counters: Never
Last 300 seconds input: 0 bytes/sec, 0 packets/sec
Last 300 seconds output: 0 bytes/sec, 0 packets/sec
30 packets input, 2520 bytes
0 input error
30 packets output, 2520 bytes
0 output error
# 可以通过如下显示信息看到,IKE协商成功,生成了两个阶段的SA。
[RouterA] display ike sa
total phase-1 SAs: 1
connection-id peer flag phase doi
----------------------------------------------------------------
7 1.1.1.2 RD|ST 1 IPSEC
8 1.1.1.2 RD|ST 2 IPSEC
flag meaning
RD--READY ST--STAYALIVE RL--REPLACED FD--FADING TO--TIMEOUT RK—REKEY
# 可以通过如下显示信息查看协商生成的IPsec SA。
[RouterA] display ipsec sa
===============================
Interface: Ethernet0/0
path MTU: 1500
===============================
-----------------------------
IPsec policy name: "center"
sequence number: 1
acl version: ACL4
mode: isakmp
-----------------------------
PFS: N, DH group: none
tunnel:
local address: 10.0.0.1
remote address: 1.1.1.2
flow:
sour addr: 10.0.0.0/255.255.255.0 port: 0 protocol: GRE
dest addr: 192.168.1.0/255.255.255.0 port: 0 protocol: GRE
[inbound ESP SAs]
spi: 0x5F1FC99C(1595918748)
transform: ESP-ENCRYPT-NULL ESP-AUTH-MD5
in use setting: Tunnel
connection id: 3
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843199/3451
anti-replay detection: Enabled
anti-replay window size(counter based): 32
udp encapsulation used for nat traversal: Y
[outbound ESP SAs]
spi: 0x8898E051(2291720273)
transform: ESP-ENCRYPT-NULL ESP-AUTH-MD5
in use setting: Tunnel
connection id: 4
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843199/3451
anti-replay detection: Enabled
anti-replay window size(counter based): 32
udp encapsulation used for nat traversal: Y
3.7 配置文件
· Router A:
ike local-name branch1
#
acl number 3000
rule 0 permit gre source 172.16.0.0 0.0.0.255 destination 172.16.0.0 0.0.0.255
rule 5 permit gre source 20.0.0.0 0.0.0.255 destination 30.0.0.0 0.0.0.255
rule 10 permit gre source 10.0.0.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
#
ike peer center
exchange-mode aggressive
pre-shared-key cipher $c$3$pBqPp455GaR40HAZQGAHoaa7zJuGUg==
id-type name
remote-name center
remote-address 1.1.1.2
nat traversal
#
ipsec transform-set def
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
#
ipsec policy center 1 isakmp
security acl 3000
ike-peer center
transform-set def
#
interface Ethernet0/1
port link-mode route
ip address 30.0.0.1 255.255.255.0
#
interface Ethernet0/0
port link-mode route
ip address 10.0.0.1 255.255.255.0
ipsec policy center
#
interface Tunnel0
ip address 172.16.0.2 255.255.255.0
source 10.0.0.1
destination 192.168.1.1
#
ip route-static 0.0.0.0 0.0.0.0 10.0.0.2
ip route-static 20.0.0.0 255.255.255.0 Tunnel0
#
· Router B:
interface Ethernet0/0
port link-mode route
nat server protocol udp global 1.1.1.1 500 inside 10.0.0.1 500
nat server protocol udp global 1.1.1.1 4500 inside 10.0.0.1 4500
ip address 1.1.1.1 255.255.255.0
#
interface Ethernet0/1
port link-mode route
ip address 10.0.0.2 255.255.255.0
#
ip route-static 30.0.0.0 255.255.255.0 10.0.0.1
ip route-static 192.168.1.0 255.255.255.0 1.1.1.2
#
· Router C:
interface Ethernet0/0
port link-mode route
nat server protocol udp global 1.1.1.2 500 inside 192.168.1.1 500
nat server protocol udp global 1.1.1.2 4500 inside 192.168.1.1 4500
ip address 1.1.1.2 255.255.255.0
#
interface Ethernet0/1
port link-mode route
ip address 192.168.1.2 255.255.255.0
#
ip route-static 10.0.0.0 255.255.255.0 1.1.1.1
ip route-static 20.0.0.0 255.255.255.0 192.168.1.1
#
· Router D:
ike local-name center
#
acl number 3001
rule 0 permit gre source 172.16.0.0 0.0.255.255 destination 172.16.0.0 0.0.255.2
55
rule 5 permit gre source 20.0.0.0 0.0.0.255 destination 30.0.0.0 0.0.0.255
rule 10 permit gre source 192.168.1.0 0.0.0.255 destination 10.0.0.0 0.0.0.255
#
ike peer branch1
exchange-mode aggressive
pre-shared-key cipher $c$3$p99rji8C/7e0RVFvvaPoZJr2L43QEw==
id-type name
remote-name branch1
nat traversal
#
ipsec transform-set default
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
#
ipsec policy branch1 1 isakmp
security acl 3001
ike-peer branch1
transform-set default
#
interface Ethernet0/0
port link-mode route
ip address 192.168.1.1 255.255.255.0
ipsec policy branch1
#
interface Ethernet0/1
port link-mode route
ip address 20.0.0.1 255.255.255.0
#
interface Tunnel0
ip address 172.16.0.1 255.255.255.0
source 192.168.1.1
destination 10.0.0.1
#
ip route-static 0.0.0.0 0.0.0.0 192.168.1.2
ip route-static 30.0.0.0 255.255.255.0 Tunnel0
#
4 相关资料
· H3C MSR 系列路由器 命令参考(V5)-R2311
· H3C MSR 系列路由器 配置指导(V5)-R2311
- 2023-11-17回答
- 评论(0)
- 举报
-
(0)
暂无评论
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明



暂无评论