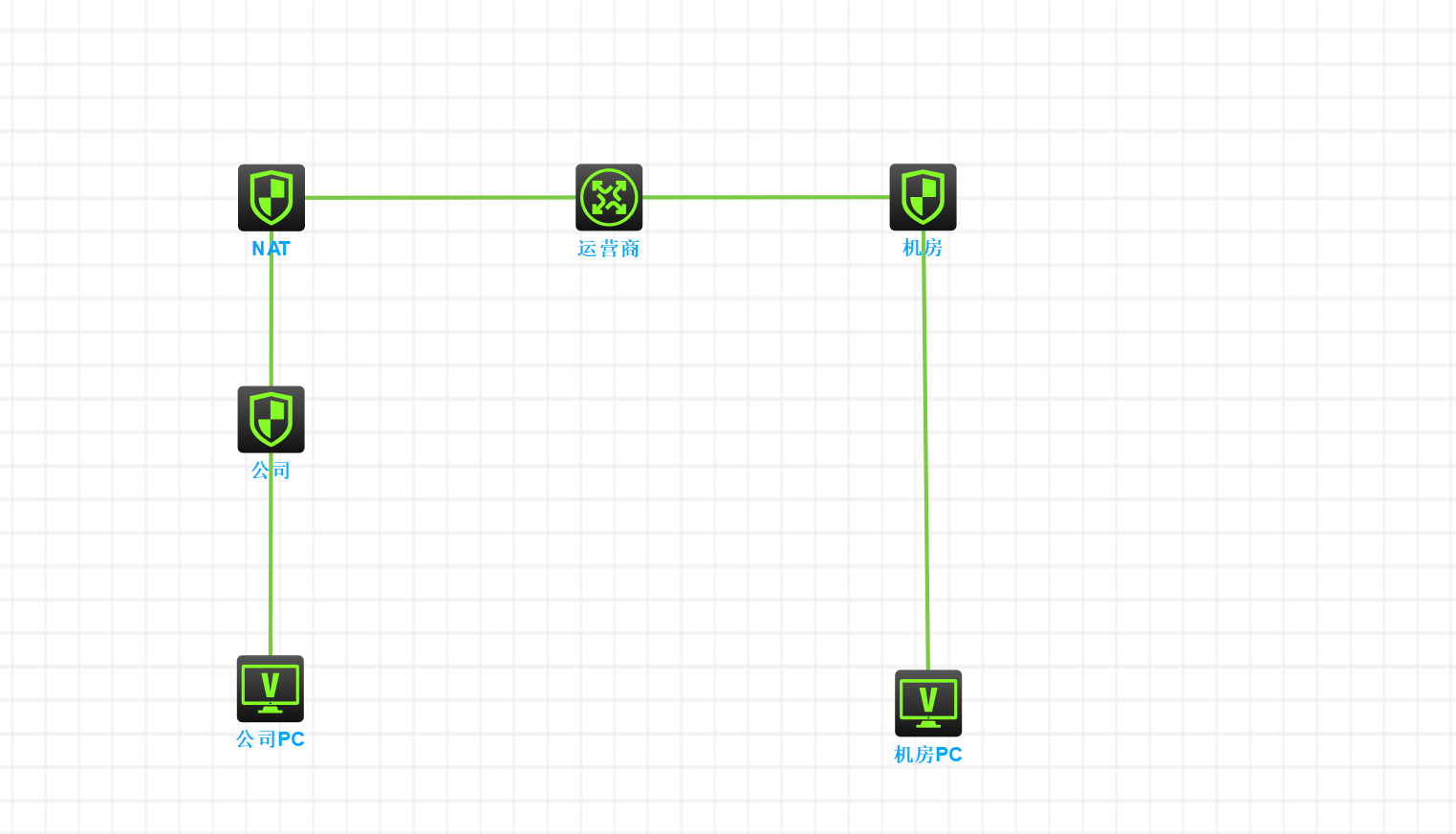
求大神帮忙指点一二!有NAT穿越场景的网络拓扑,只能从没有NAT一侧创建IPSec
- 0关注
- 0收藏,1589浏览
问题描述:
公司防火墙:作为IPSec连接点+DHCP网关
公司NAT:仅作为NAT设备使用
机房防火墙:作为NAT+IPSec连接点+DHCP网关
问题:可以从机房侧带源ping,实现NAT穿越激活IPSec隧道,但是如果从公司侧则无法激活IPSec,NAT设备已经做了端口映射,配置如下
【公司防火墙】
<IDC>dis cu
#
version 7.1.064, Alpha 7164
#
sysname IDC
#
context Admin id 1
#
telnet server enable
#
irf mac-address persistent timer
irf auto-update enable
undo irf link-delay
irf member 1 priority 1
#
dhcp enable
#
xbar load-single
password-recovery enable
lpu-type f-series
#
vlan 1
#
vlan 100
#
dhcp server ip-pool pool
gateway-list 192.168.20.1
network 192.168.20.0 mask 255.255.255.0
dns-list 114.114.114.114
#
interface NULL0
#
interface Vlan-interface100
ip address 192.168.20.1 255.255.255.0
dhcp server apply ip-pool pool
#
interface GigabitEthernet1/0/0
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/1
port link-mode route
combo enable copper
ip address 20.1.1.2 255.255.255.0
nat outbound 3101
ipsec apply policy ipp
#
interface GigabitEthernet1/0/3
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/4
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/5
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/6
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/7
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/8
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/9
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/10
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/11
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/12
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/13
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/14
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/15
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/16
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/17
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/18
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/19
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/20
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/21
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/22
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/23
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/2
port link-mode bridge
port access vlan 100
combo enable copper
#
security-zone name Local
#
security-zone name Trust
import interface Vlan-interface100
import interface GigabitEthernet1/0/2 vlan 100
#
security-zone name DMZ
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
#
security-zone name Management
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line aux 0
user-role network-admin
#
line con 0
authentication-mode scheme
user-role network-admin
#
line vty 0 4
authentication-mode scheme
user-role network-admin
#
line vty 5 63
user-role network-operator
#
ip route-static 0.0.0.0 0 20.1.1.1
#
info-center loghost 127.0.0.1 port 3301 format default
info-center source CFGLOG loghost level informational
#
acl advanced 3100
rule 10 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
#
acl advanced 3101
rule 10 deny ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 20 permit ip source 192.168.20.0 0.0.0.255
#
domain system
#
aaa session-limit ftp 16
aaa session-limit telnet 16
aaa session-limit ssh 16
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user admin class manage
password hash $h$6$UbIhNnPevyKUwfpm$LqR3+yg1IjNct39MkOR0H0iQXLkYB3jMqM4vbAeoXOhbabIIFnjJPEGR00YiYA1Sz4LiY3FmEdru2fOLMb1shQ==
service-type telnet terminal http
authorization-attribute user-role level-3
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
ipsec transform-set trans
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy ipp 1 isakmp
transform-set trans
security acl 3100
local-address 20.1.1.2
remote-address 10.1.1.2
ike-profile ikep
#
ike profile ikep
keychain keychain
local-identity address 20.1.1.2
match remote identity address 10.1.1.2 255.255.255.255
proposal 1
#
ike proposal 1
encryption-algorithm 3des-cbc
dh group2
authentication-algorithm md5
#
ike keychain keychain
pre-shared-key address 10.1.1.2 255.255.255.255 key cipher $c$3$+VGnDeOD1HRY2XQaRB1Zb8i7q7NmWZHB8A==
#
ip http enable
ip https enable
#
security-policy ip
rule 0 name allow
action pass
#
return
【公司NAT】
[NAT]dis cu
#
version 7.1.064, Alpha 7164
#
sysname NAT
#
context Admin id 1
#
telnet server enable
#
irf mac-address persistent timer
irf auto-update enable
undo irf link-delay
irf member 1 priority 1
#
xbar load-single
password-recovery enable
lpu-type f-series
#
vlan 1
#
interface NULL0
#
interface GigabitEthernet1/0/0
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/1
port link-mode route
combo enable copper
ip address 10.1.1.2 255.255.255.0
nat outbound 2000
nat server protocol udp global 10.1.1.2 500 inside 172.16.0.249 500 rule ServerRule_2
nat server protocol udp global 10.1.1.2 4500 inside 172.16.0.249 4500 rule ServerRule_1
#
interface GigabitEthernet1/0/2
port link-mode route
combo enable copper
ip address 172.16.0.254 255.255.255.0
nat outbound 2001
#
interface GigabitEthernet1/0/3
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/4
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/5
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/6
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/7
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/8
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/9
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/10
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/11
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/12
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/13
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/14
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/15
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/16
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/17
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/18
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/19
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/20
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/21
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/22
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/23
port link-mode route
combo enable copper
#
security-zone name Local
#
security-zone name Trust
import interface GigabitEthernet1/0/2
#
security-zone name DMZ
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
#
security-zone name Management
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line aux 0
user-role network-admin
#
line con 0
authentication-mode scheme
user-role network-admin
#
line vty 0 4
authentication-mode scheme
user-role network-admin
#
line vty 5 63
user-role network-operator
#
ip route-static 0.0.0.0 0 10.1.1.1
ip route-static 192.168.10.0 24 172.16.0.249
#
info-center loghost 127.0.0.1 port 3301 format default
info-center source CFGLOG loghost level informational
#
acl basic 2000
rule 0 permit
#
acl basic 2001
rule 0 permit source 192.168.10.0 0.0.0.255
rule 5 deny
#
acl advanced 3200
rule 0 permit ip
#
domain system
#
aaa session-limit ftp 16
aaa session-limit telnet 16
aaa session-limit ssh 16
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user admin class manage
password hash $h$6$UbIhNnPevyKUwfpm$LqR3+yg1IjNct39MkOR0H0iQXLkYB3jMqM4vbAeoXOhbabIIFnjJPEGR00YiYA1Sz4LiY3FmEdru2fOLMb1shQ==
service-type telnet terminal http
authorization-attribute user-role level-3
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
ip http enable
ip https enable
#
security-policy ip
rule 0 name allow
action pass
#
security-policy ipv6
#
return
【机房防火墙】
<IDC>dis cu
#
version 7.1.064, Alpha 7164
#
sysname IDC
#
context Admin id 1
#
telnet server enable
#
irf mac-address persistent timer
irf auto-update enable
undo irf link-delay
irf member 1 priority 1
#
dhcp enable
#
xbar load-single
password-recovery enable
lpu-type f-series
#
vlan 1
#
vlan 100
#
dhcp server ip-pool pool
gateway-list 192.168.20.1
network 192.168.20.0 mask 255.255.255.0
dns-list 114.114.114.114
#
interface NULL0
#
interface Vlan-interface100
ip address 192.168.20.1 255.255.255.0
dhcp server apply ip-pool pool
#
interface GigabitEthernet1/0/0
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/1
port link-mode route
combo enable copper
ip address 20.1.1.2 255.255.255.0
nat outbound 3101
ipsec apply policy ipp
#
interface GigabitEthernet1/0/3
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/4
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/5
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/6
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/7
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/8
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/9
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/10
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/11
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/12
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/13
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/14
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/15
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/16
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/17
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/18
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/19
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/20
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/21
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/22
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/23
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/2
port link-mode bridge
port access vlan 100
combo enable copper
#
security-zone name Local
#
security-zone name Trust
import interface Vlan-interface100
import interface GigabitEthernet1/0/2 vlan 100
#
security-zone name DMZ
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
#
security-zone name Management
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line aux 0
user-role network-admin
#
line con 0
authentication-mode scheme
user-role network-admin
#
line vty 0 4
authentication-mode scheme
user-role network-admin
#
line vty 5 63
user-role network-operator
#
ip route-static 0.0.0.0 0 20.1.1.1
#
info-center loghost 127.0.0.1 port 3301 format default
info-center source CFGLOG loghost level informational
#
acl advanced 3100
rule 10 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
#
acl advanced 3101
rule 10 deny ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 20 permit ip source 192.168.20.0 0.0.0.255
#
domain system
#
aaa session-limit ftp 16
aaa session-limit telnet 16
aaa session-limit ssh 16
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user admin class manage
password hash $h$6$UbIhNnPevyKUwfpm$LqR3+yg1IjNct39MkOR0H0iQXLkYB3jMqM4vbAeoXOhbabIIFnjJPEGR00YiYA1Sz4LiY3FmEdru2fOLMb1shQ==
service-type telnet terminal http
authorization-attribute user-role level-3
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
ipsec transform-set trans
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy ipp 1 isakmp
transform-set trans
security acl 3100
local-address 20.1.1.2
remote-address 10.1.1.2
ike-profile ikep
#
ike profile ikep
keychain keychain
local-identity address 20.1.1.2
match remote identity address 10.1.1.2 255.255.255.255
proposal 1
#
ike proposal 1
encryption-algorithm 3des-cbc
dh group2
authentication-algorithm md5
#
ike keychain keychain
pre-shared-key address 10.1.1.2 255.255.255.255 key cipher $c$3$+VGnDeOD1HRY2XQaRB1Zb8i7q7NmWZHB8A==
#
ip http enable
ip https enable
#
security-policy ip
rule 0 name allow
action pass
#
return
- 2024-01-15提问
- 举报
-
(0)

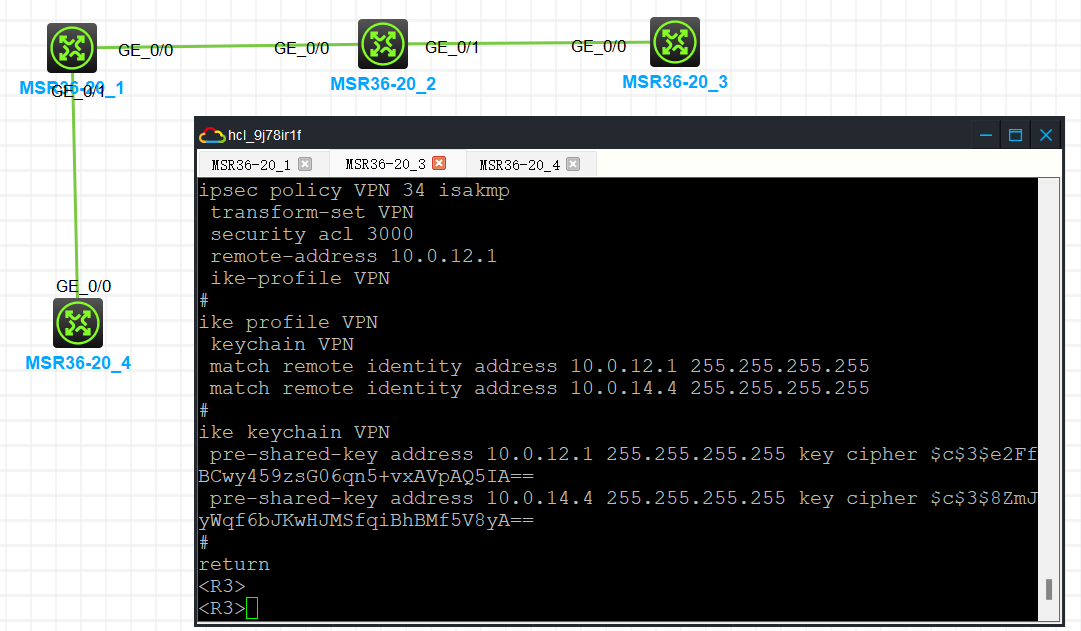
你这配置贴得不对吧,怎么公司防火墙和机房防火墙一样啊。
我用模拟器做了个差不多的场景,结论是你要把公司防火墙出接口的ip加到机房防火墙的ike keychain以及ike profile里,否则只能单向激活,换个方向debug会显示ipsec policy不匹配(实际上是ipsec policy对应的ike keychain以及ike profile不匹配)。
- 2024-01-15回答
- 评论(1)
- 举报
-
(1)
非常感谢,这个答案非常完美!
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明



非常感谢,这个答案非常完美!