手机vpn连接问题
- 0关注
- 0收藏,4760浏览
问题描述:
以前手机支持L2TP、L2TP/IPSec PSK这些vpn类型,防火墙可以通过配置l2tp over ipsec实现手机端的vpn连接,但现在很多手机系统只保留了IKEv2/IPSec MSCHAPv2、IKEv2/IPSec PSK、IKEv2/IPSec RSA这3种类型,我尝试按照l2tp over ipsec的配置方法将ikev1的配置修改成ikev2发现是无法连接上的,不知道是不是不支持这种做法,手机只有这3种vpn类型的话华三设备还有没有哪种配置方法可以做到手机端vpn接入的?不考虑SSL VPN
- 2024-03-04提问
- 举报
-
(0)

ipsec也是可以的
将防火墙部署在互联网出口用于L2TP VPN网关,目前需要安卓(Android)\苹果(IOS)手机使用系统自带的L2TP客户端连接VPN访问内网资源。
【小知识】由于安全性考虑,Android 4.0以后的版本和IOS系统L2TP登录方式全部改为L2TP OVER IPSEC方式,所以防火墙只配置L2TP VPN手机终端无法拨入,需要在防火墙增加IPSEC的配置。
2 组网图
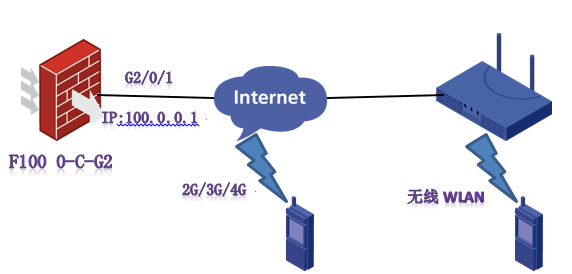
注:防火墙外网接口地址为10.0.0.1。
配置步骤
3 配置步骤
3.1 防火墙上网配置
略(请参考防火墙上网配置案例进行配置)
3.2 L2TP VPN配置
3.2.1 启用L2TP VPN
进入系统视图后开启L2TP功能
[H3C]l2tp enable
3.2.2 配置地址池用于向L2TP用户下发地址
创建L2TP地址池用于向L2TP用户下发地址,需要注意L2TP下发网段不能与内网网段冲突。
[H3C]ip pool 1 172.16.1.2 172.16.1.254
3.2.3 配置虚模板
在虚模板下绑定全局下创建的L2TP地址池,服务模板下的ip address为L2TP VPN用户的网关,需要和地址池内地址在同一网段。
[H3C]interface Virtual-Template 1
[H3C-Virtual-Template1]ppp authentication-mode chap pap
[H3C-Virtual-Template1]remote address pool 1
[H3C-Virtual-Template1]ip address 172.16.1.1 24
[H3C-Virtual-Template1]quit
3.2.4 创建L2TP用户组
创建L2TP组绑定虚模板
[H3C]l2tp-group 1 mode lns
[H3C-l2tp1]undo tunnel authentication
[H3C-l2tp1]allow l2tp virtual-template 1
[H3C-l2tp1]quit
3.2.5 创建用户
创建的L2TP账号为z,密码为z。
[H3C]local-user z class network
[H3C-luser-network-z]service-type ppp
[H3C-luser-network-z]password simple z
[H3C-luser-network-z]quit
3.2.6 将Virtual-Template接口加入到安全域并放通安全策略
将Virtual-Template 1接口加入Trust区域,如果内网接口也在Trust区域需要放通同域间的安全策略。
[H3C]security-zone name Trust
[H3C-security-zone-Trust]import interface Virtual-Template 1
[H3C-security-zone-Trust]quit
[H3C]security-zone intra-zone default permit
3.3 IPSEC VPN配置
3.3.1 配置共享秘钥
配置共享秘钥为123
[H3C]ike keychain 1
[H3C-ike-keychain-1]pre-shared-key address 0.0.0.0 0 key simple 123
[H3C-ike-keychain-1]quit
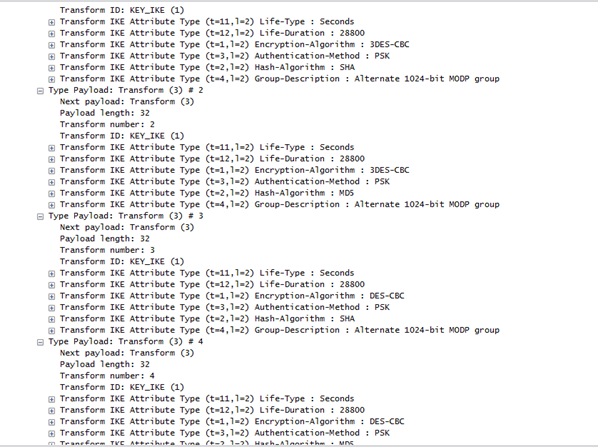
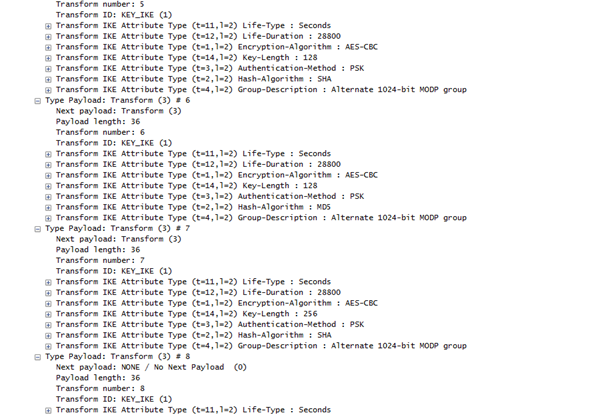
3.3.2 配置IKE安全提议
配置多个安全提议用于匹配不同的终端认证\加密算法。
[H3C]ike proposal 1
[H3C-ike-proposal-1]encryption-algorithm aes-cbc-128
[H3C-ike-proposal-1]dh group2
[H3C-ike-proposal-1]authentication-algorithm md5
[H3C-ike-proposal-1]quit
[H3C]ike proposal 2
[H3C-ike-proposal-2]encryption-algorithm 3des-cbc
[H3C-ike-proposal-2]dh group2
[H3C-ike-proposal-2]authentication-algorithm md5
[H3C-ike-proposal-2]quit
[H3C]ike proposal 3
[H3C-ike-proposal-3]encryption-algorithm 3des-cbc
[H3C-ike-proposal-3]dh group2
[H3C-ike-proposal-3]authentication-algorithm sha
[H3C-ike-proposal-3]quit
[H3C]ike proposal 4
[H3C-ike-proposal-4]encryption-algorithm aes-cbc-256
[H3C-ike-proposal-4]dh group2
[H3C-ike-proposal-4]authentication-algorithm sha
[H3C-ike-proposal-4]quit
[H3C]ike proposal 5
[H3C-ike-proposal-5]encryption-algorithm DES-CBC
[H3C-ike-proposal-5]dh group2
[H3C-ike-proposal-5]authentication-algorithm sha
[H3C-ike-proposal-5]quit
[H3C]ike proposal 6
[H3C-ike-proposal-6]encryption-algorithm aes-cbc-192
[H3C-ike-proposal-6]dh group2
[H3C-ike-proposal-6]authentication-algorithm sha
[H3C-ike-proposal-6]quit
3.3.3 配置IKE安全框架
配置IKE安全框架调用创建的6个安全提议。
[H3C]ike profile 1
[H3C-ike-profile-1]keychain 1
[H3C-ike-profile-1]match remote identity address 0.0.0.0 0
[H3C-ike-profile-1]proposal 1 2 3 4 5 6
[H3C-ike-profile-1]quit
3.3.4 配置IPSEC安全提议
[H3C]ipsec transform-set 1
[H3C-ipsec-transform-set-1]encapsulation-mode transport
[H3C-ipsec-transform-set-1]esp encryption-algorithm 3des-cbc
[H3C-ipsec-transform-set-1]esp authentication-algorithm MD5
[H3C-ipsec-transform-set-1]quit
[H3C]ipsec transform-set 2
[H3C-ipsec-transform-set-2]encapsulation-mode transport
[H3C-ipsec-transform-set-2]esp encryption-algorithm aes-cbc-128
[H3C-ipsec-transform-set-2]esp authentication-algorithm sha1
[H3C-ipsec-transform-set-2]quit
[H3C]ipsec transform-set 3
[H3C-ipsec-transform-set-3]encapsulation-mode transport
[H3C-ipsec-transform-set-3]esp encryption-algorithm aes-cbc-256
[H3C-ipsec-transform-set-3]esp authentication-algorithm sha1
[H3C-ipsec-transform-set-3]quit
[H3C]ipsec transform-set 4
[H3C-ipsec-transform-set-4]encapsulation-mode transport
[H3C-ipsec-transform-set-4]esp encryption-algorithm des-cbc
[H3C-ipsec-transform-set-4]esp authentication-algorithm sha1
[H3C-ipsec-transform-set-4]quit
[H3C]ipsec transform-set 5
[H3C-ipsec-transform-set-5]encapsulation-mode transport
[H3C-ipsec-transform-set-5]esp encryption-algorithm 3des-cbc
[H3C-ipsec-transform-set-5]esp authentication-algorithm sha1
[H3C-ipsec-transform-set-5]quit
[H3C]ipsec transform-set 6
[H3C-ipsec-transform-set-6]encapsulation-mode transport
[H3C-ipsec-transform-set-6]esp encryption-algorithm aes-cbc-192
[H3C-ipsec-transform-set-6]esp authentication-algorithm sha1
[H3C-ipsec-transform-set-6]quit
3.3.5 配置IPSEC模板
配置IPSEC模板并调用之前创建的6个模板
[H3C]ipsec policy-template z 1
[H3C-ipsec-policy-template-z-1]transform-set 1 2 3 4 5 6
[H3C-ipsec-policy-template-z-1]ike-profile 1
[H3C-ipsec-policy-template-z-1]quit
3.3.6 配置IPSEC策略
[H3C]ipsec policy a 10 isakmp template z
3.3.7 将IPSEC策略在外网接口调用
[H3C]interface GigabitEthernet 2/0/1
[H3C-GigabitEthernet2/0/1]ipsec apply policy a
[H3C-GigabitEthernet2/0/1]quit
3.3.8 外网接口NAT中添加ACL拒绝掉L2TP数据流量做地址转换。
因为在防火墙处理流程上是先进行NAT后进行IPSEC VPN,如果出接口不拒绝掉L2TP数据流会导致回包无法匹配IPSEC兴趣流。
[H3C]acl advanced 3000
[H3C-acl-ipv4-adv-3000]rule deny udp destination-port 1701
[H3C-acl-ipv4-adv-3000]rule permit ip source any
[H3C-acl-ipv4-adv-3000]quit
[H3C]interface GigabitEthernet 2/0/1
[H3C-GigabitEthernet2/0/1]nat outbound 3000
[H3C-GigabitEthernet2/0/1]quit
3.4 保存配置
[H3C]quit
3.5 实验验证
3.5.1 使用安卓手机拨入VPN


3.5.2 使用苹果手机拨入VPN
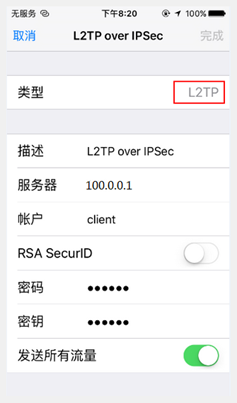

3.6 注意事项
3.6.1 协商模式
安卓手机自带的客户端默认为传输模式,和IKE主模式协商。
3.6.2 关于IKE安全提议
安卓手机IKE第一阶段协商的加密算法和验证算法,安卓自带客户端会发送8种组合方式,所以本次案例选取6种以便与更多的系统兼容。
3.6.3 关于IPSEC安全提议
安卓手机自带客户端第二阶段协商为3DES加密算法,SHA1验证算法。也支持AES-CBC-256加密算法和SHA1验证算法(苹果手机也是支持这个)。如果苹果手机需要接入,只需再增加一个transform-set 配置为传输模式AES-CBC-256加密算法和SHA1验证算法。
3.6.4 关于V5平台设备是否支持手机端拨入
V5平台的设备例如部分防火墙和部分MSR设备使用传输模式配置l2tp over ipsec时,封装会出现问题,将会导致l2tp报文无法正常封装。故无法实现手机使用自带客户端l2tp over ipsec拨号需求。
- 2024-03-04回答
- 评论(7)
- 举报
-
(0)
有配置案例吗?
L2TP的加答案了
你这个就是我说的L2TP over IPSEC的配法呀,现在手机只支持那3种vpn的话配这个是连不上的
安装inode,通过inode进行拨号
手机inode好像只支持ssl vpn
https://www.h3c.com/cn/pub/Document_Center/2023/08/WebHelp_H3C_SecPath_FHQCP_DXPZALJ(V7)/default_auto.htm?CHID=904200
答非所问!!!我也想知道那3种vpn怎么配?鸿蒙4.3只有这三种VPN。
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明

答非所问!!!我也想知道那3种vpn怎么配?鸿蒙4.3只有这三种VPN。