H3C F100-C-A5防火墙内部服务器NAT不生效问题
- 0关注
- 0收藏,2404浏览
问题描述:
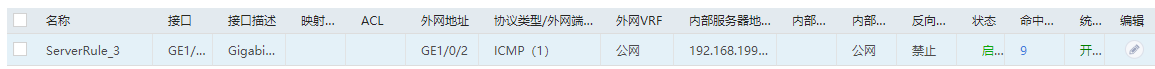
你好,请教一下,我想要对一个内部服务器映射到公网可以访问,公网固定ip(防火墙接口地址):51.58.199.6,尝试在外网ping51.58.199.6,但实测无法ping通,配置如下:
1、int g1/0/2(对接公网接口) nat server protocol icmp global current-interface inside 192.168.199.199(内部服务器)
nat outbound 2002(匹配内部服务器地址)
nat static enable
2、int g1/0/4(内网服务器方向接口) nat hairpin enable
3、安全策略
rule 18 name untrust-trust
action pass
source-zone Untrust
destination-zone Trust
destination-ip-host 192.168.199.199
rule 19 name trust-trust
action pass
source-zone Trust
destination-zone Trust
上述配置,实测从外网访问公网网址时,nat命中次数能够增加,但安全策略中流量始终为0,无法ping通,请教各位大佬,谢谢。

- 2024-05-13提问
- 举报
-
(0)

换个其他服务试试
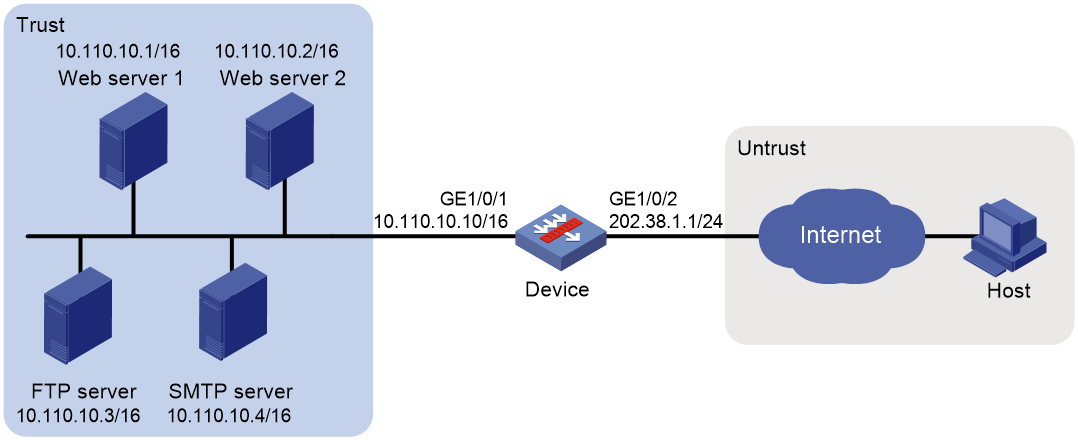
2.13.3 外网用户通过外网地址访问内网服务器配置举例
1. 组网需求
某公司内部对外提供Web、FTP和SMTP服务,而且提供两台Web服务器。公司内部网址为10.110.0.0/16。其中,内部FTP服务器地址为10.110.10.3/16,内部Web服务器1的IP地址为10.110.10.1/16,内部Web服务器2的IP地址为10.110.10.2/16,内部SMTP服务器IP地址为10.110.10.4/16。公司拥有202.38.1.1至202.38.1.3三个公网IP地址。需要实现如下功能:
· 外部的主机可以访问内部的服务器。
· 选用202.38.1.1作为公司对外提供服务的IP地址,Web服务器2对外采用8080端口。
2. 组网图
图2-5 外网用户通过外网地址访问内网服务器配置组网图
3. 配置步骤
(1) 配置接口IP地址
# 根据组网图中规划的信息,配置各接口的IP地址,具体配置步骤如下。
<Device> system-view
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] ip address 10.110.10.10 16
[Device-GigabitEthernet1/0/1] quit
请参考以上步骤配置其他接口的IP地址,具体配置步骤略。
(2) 将接口加入安全域
# 请根据组网图中规划的信息,将接口加入对应的安全域,具体配置步骤如下。
[Device] security-zone name trust
[Device-security-zone-Trust] import interface gigabitethernet 1/0/1
[Device-security-zone-Trust] quit
[Device] security-zone name untrust
[Device-security-zone-Untrust] import interface gigabitethernet 1/0/2
[Device-security-zone-Untrust] quit
(3) 配置安全策略
# 配置名称为untrust-trust的安全策略,保证Untrust安全域中的Host可以访问Trust安全域中的Server,具体配置步骤如下。
[Device] security-policy ip
[Device-security-policy-ip] rule name untrust-trust
[Device-security-policy-ip-1-untrust-trust] source-zone untrust
[Device-security-policy-ip-1-untrust-trust] destination-zone trust
[Device-security-policy-ip-1-untrust-trust] destination-ip-host 10.110.10.1
[Device-security-policy-ip-1-untrust-trust] destination-ip-host 10.110.10.2
[Device-security-policy-ip-1-untrust-trust] destination-ip-host 10.110.10.3
[Device-security-policy-ip-1-untrust-trust] destination-ip-host 10.110.10.4
[Device-security-policy-ip-1-untrust-trust] action pass
[Device-security-policy-ip-1-untrust-trust] quit
[Device-security-policy-ip] quit
(4) 配置NAT功能
# 配置服务对象组,提供FTP、Web和SMTP服务。
[Device] object-group service service1
[Device-obj-grp-service-service1] service tcp destination eq 21
[Device-obj-grp-service-service1] quit
[Device] object-group service service2
[Device-obj-grp-service-service2] service tcp destination eq 80
[Device-obj-grp-service-service2] quit
[Device] object-group service service3
[Device-obj-grp-service-service3] service tcp destination eq 8080
[Device-obj-grp-service-service3] quit
[Device] object-group service service4
[Device-obj-grp-service-service4] service tcp destination eq 25
[Device-obj-grp-service-service4] quit
# 配置全局NAT规则,允许外网主机访问内网服务器。
[Device] nat global-policy
[Device-nat-global-policy] rule name rule1
[Device-nat-global-policy-rule-rule1] destination-ip host 202.38.1.1
[Device-nat-global-policy-rule-rule1] source-zone untrust
[Device-nat-global-policy-rule-rule1] service service1
[Device-nat-global-policy-rule-rule1] action dnat ip-address 10.110.10.3 local-port 21
[Device-nat-global-policy-rule-rule1] quit
[Device-nat-global-policy] rule name rule2
[Device-nat-global-policy-rule-rule2] destination-ip host 202.38.1.1
[Device-nat-global-policy-rule-rule2] source-zone untrust
[Device-nat-global-policy-rule-rule2] service service2
[Device-nat-global-policy-rule-rule2] action dnat ip-address 10.110.10.1 local-port 80
[Device-nat-global-policy-rule-rule2] quit
[Device-nat-global-policy] rule name rule3
[Device-nat-global-policy-rule-rule3] destination-ip host 202.38.1.1
[Device-nat-global-policy-rule-rule3] source-zone untrust
[Device-nat-global-policy-rule-rule3] service service3
[Device-nat-global-policy-rule-rule3] action dnat ip-address 10.110.10.2 local-port 80
[Device-nat-global-policy-rule-rule3] quit
[Device-nat-global-policy] rule name rule4
[Device-nat-global-policy-rule-rule4] destination-ip host 202.38.1.1
[Device-nat-global-policy-rule-rule4] source-zone untrust
[Device-nat-global-policy-rule-rule4] service service4
[Device-nat-global-policy-rule-rule4] action dnat ip-address 10.110.10.4 local-port 25
[Device-nat-global-policy-rule-rule4] quit
[Device-nat-global-policy] quit
4. 验证配置
# 以上配置完成后,外网Host能够通过NAT地址访问各内网服务器。通过查看如下显示信息,可以验证以上配置成功。
[Device] display nat all
NAT global-policy information:
Totally 4 NAT global-policy rules.
Rule name: rule1
Type : nat
DestIP address : 202.38.1.1
Source-zone name : untrust
Service object group : service1
DNAT action:
IPv4 address: 10.110.10.3
Port: 21
NAT counting : 0
Config status: Active
Rule name: rule2
Type : nat
DestIP address : 202.38.1.1
Source-zone name : untrust
Destination-zone name : trust
Service object group : service2
DNAT action:
IPv4 address: 10.110.10.1
Port: 80
NAT counting : 0
Config status: Active
Rule name: rule3
Type : nat
DestIP address : 202.38.1.1
Source-zone name : untrust
Destination-zone name : trust
Service object group : service3
DNAT action:
IPv4 address: 10.110.10.2
Port: 80
NAT counting : 0
Config status: Active
Rule name: rule4
Type : nat
DestIP address : 202.38.1.1
Source-zone name : untrust
Destination-zone name : trust
Service object group : service4
DNAT action:
IPv4 address: 10.110.10.4
Port: 25
NAT counting : 0
Config status: Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NO-PAT IP usage : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Disabled
ICMP-ERROR : Enabled
ILS : Disabled
MGCP : Disabled
NBT : Disabled
PPTP : Enabled
RTSP : Enabled
RSH : Disabled
SCCP : Disabled
SCTP : Disabled
SIP : Disabled
SQLNET : Disabled
TFTP : Disabled
XDMCP : Disabled
Static NAT load balancing: Disabled
NAT link-switch recreate-session: Disabled
NAT configuration-for-new-connection: Disabled
# 通过以下显示命令,可以看到Host访问FTP server时生成NAT会话信息。
[Device] display nat session verbose
Slot 1:
Initiator:
Source IP/port: 202.38.1.2/52802
Destination IP/port: 202.38.1.1/21
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/2
Source security zone: Untrust
Responder:
Source IP/port: 10.110.10.3/21
Destination IP/port: 202.38.1.2/52802
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: TCP(6)
Inbound interface: GigabitEthernet1/0/1
Source security zone: Trust
State: TCP_ESTABLISHED
Application: FTP
Rule ID: -/-/-
Rule name:
Start time: 2017-05-21 11:13:39 TTL: 3597s
Initiator->Responder: 7 packets 313 bytes
Responder->Initiator: 6 packets 330 bytes
Total sessions found: 1
- 2024-05-13回答
- 评论(8)
- 举报
-
(0)
一开始就是用HTTP不行,后买才尝试ICMP
直接用端口号试试
试过TCP端口号9443,也不行,很奇怪NAT能命中,但就是没有流量
内网业务9443正常吗?
安全策略全部放通测试一下
unturst/trust全部ANY,安全策略也没有命中
nat static enable 这个删除试试
案例加答案了 ,参考下吧

配置静态一对一nat试试
服务器检查下再内网能不能ping通
- 2024-05-13回答
- 评论(3)
- 举报
-
(0)
NAT有命中,安全策略无命中,也没有会话表
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明

案例加答案了 ,参考下吧