MSR5620
- 0关注
- 1收藏,2311浏览
问题描述:
两台华三路由通过2M线组网,本端查看BGP状态established
公网、私网路由都已学到,数据通信暂未发现异常。
如图:
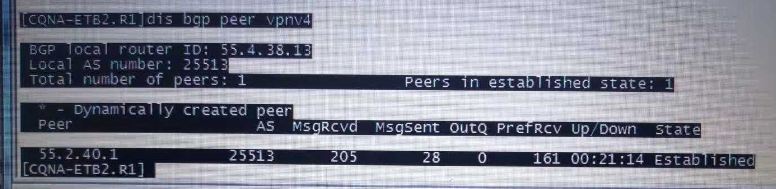
可对端路由查看BGP状态为 no neg
请问该问题应该如何解决?
两台都为华三路由。
本地路由配置如下:
[CQNA-ETB2.R1]dis cu
#
version 7.1.059, Release 0306P11
#
sysname CQNA-ETB2.R1
#
clock timezone beijing add 08:00:00
#
ip vpn-instance vpn-nrt
route-distinguisher 25513:2
vpn-target 25513:2110 30000:802 20000:200 import-extcommunity
vpn-target 25513:2110 25588:200 export-extcommunity
#
ip vpn-instance vpn-rt
route-distinguisher 25513:1
vpn-target 25513:1110 30000:801 20000:100 import-extcommunity
vpn-target 25513:1110 25588:100 export-extcommunity
#
router id 55.4.38.13
#
ospf 1
area 0.0.0.9
network 55.4.38.13 0.0.0.0
network 55.5.50.48 0.0.0.3
#
mpls lsr-id 55.4.38.13
mpls ttl propagate vpn
#
password-recovery enable
#
vlan 1
#
traffic classifier c_vpn-nrt-in operator and
if-match acl 2001
#
traffic classifier c_vpn-nrt-out operator and
if-match mpls-exp 3
#
traffic classifier c_vpn-rt-in operator and
if-match acl 2001
#
traffic classifier c_vpn-rt-out operator and
if-match mpls-exp 4
#
traffic behavior b_vpn-nrt-in
remark dscp af31
#
traffic behavior b_vpn-nrt-out
queue af bandwidth pct 30
#
traffic behavior b_vpn-rt-in
remark dscp af41
#
traffic behavior b_vpn-rt-out
queue af bandwidth pct 70
#
qos policy p_vpn-nrt-in
classifier c_vpn-nrt-in behavior b_vpn-nrt-in
#
qos policy p_vpn-out
classifier c_vpn-rt-out behavior b_vpn-rt-out
classifier c_vpn-nrt-out behavior b_vpn-nrt-out
#
qos policy p_vpn-rt-in
classifier c_vpn-rt-in behavior b_vpn-rt-in
#
mpls ldp
#
controller Cellular2/0/0
#
controller Cellular2/0/1
#
interface Serial2/1/0
description DD2-ETB2-2M
fe1 unframed
ppp mp MP-group2/0/0
#
interface Serial2/1/1
description DD2-ETB2-2M
fe1 unframed
ppp mp MP-group2/0/0
#
interface Serial2/2/0
#
interface Serial2/2/1
#
interface MP-group2/0/0
ip address 55.5.50.50 255.255.255.252
ospf authentication-mode md5 1 cipher $c$3$BF3d5gYm4snQVlV+iF6EjlrTo16TQaxtZg==
mpls enable
mpls ldp enable
mpls ldp transport-address interface
#
interface NULL0
#
interface LoopBack0
ip address 55.4.38.13 255.255.255.255
#
interface GigabitEthernet2/0/0
port link-mode route
description R1-S1
combo enable copper
ip binding vpn-instance vpn-rt
ip address 55.178.38.126 255.255.255.128
qos apply policy p_vpn-rt-in inbound
#
interface GigabitEthernet2/0/1
port link-mode route
description R1-S2
combo enable copper
ip binding vpn-instance vpn-nrt
ip address 55.179.38.126 255.255.255.128
qos apply policy p_vpn-nrt-in inbound
#
interface GigabitEthernet2/0/2
port link-mode route
combo enable copper
#
interface GigabitEthernet2/5/0
port link-mode bridge
#
interface GigabitEthernet2/5/1
port link-mode bridge
#
interface GigabitEthernet2/5/2
port link-mode bridge
#
interface GigabitEthernet2/5/3
port link-mode bridge
#
interface GigabitEthernet2/5/4
port link-mode bridge
#
interface GigabitEthernet2/5/5
port link-mode bridge
#
interface GigabitEthernet2/5/6
port link-mode bridge
combo enable copper
#
interface GigabitEthernet2/5/7
port link-mode bridge
combo enable copper
#
interface GigabitEthernet2/6/0
port link-mode bridge
#
interface GigabitEthernet2/6/1
port link-mode bridge
#
interface GigabitEthernet2/6/2
port link-mode bridge
#
interface GigabitEthernet2/6/3
port link-mode bridge
#
interface GigabitEthernet2/6/4
port link-mode bridge
#
interface GigabitEthernet2/6/5
port link-mode bridge
#
interface GigabitEthernet2/6/6
port link-mode bridge
combo enable copper
#
interface GigabitEthernet2/6/7
port link-mode bridge
combo enable copper
#
interface M-GigabitEthernet0
#
interface Ten-GigabitEthernet2/0/3
port link-mode route
#
interface Ten-GigabitEthernet2/0/4
port link-mode route
#
bgp 25513
group ibgp-peer internal
peer ibgp-peer connect-interface LoopBack0
peer 55.2.40.1 group ibgp-peer
#
address-family vpnv4
peer ibgp-peer enable
#
ip vpn-instance vpn-nrt
#
address-family ipv4 unicast
import-route direct
#
ip vpn-instance vpn-rt
#
address-family ipv4 unicast
import-route direct
#
scheduler logfile size 16
#
line class console
user-role network-admin
#
line class tty
user-role network-admin
#
line class vty
user-role network-admin
#
line con 0 1
authentication-mode scheme
user-role level-15
user-role network-admin
idle-timeout 5 0
#
line vty 0 4
authentication-mode scheme
user-role level-15
user-role network-admin
protocol inbound telnet
idle-timeout 5 0
#
line vty 5 10
authentication-mode scheme
user-role level-15
user-role network-admin
protocol inbound ssh
idle-timeout 5 0
#
line vty 11 63
user-role level-15
user-role network-operator
#
info-center loghost 55.254.13.1
info-center loghost 55.254.113.1
#
snmp-agent
snmp-agent local-engineid 800063A280487ADAFE71B400000001
snmp-agent community read CQEP-READ
snmp-agent community write CQEP-WRITE
snmp-agent sys-info version v3
snmp-agent group v3 CQEP privacy read-view CQEP-READ write-view CQEP-WRITE notify-view CQEP-READ
snmp-agent target-host trap address udp-domain 55.254.13.1 params securityname CQEP-READ
snmp-agent mib-view included CQEP-READ iso
snmp-agent mib-view included CQEP-WRITE iso
snmp-agent usm-user v3 cqdl CQEP cipher authentication-mode sha $c$3$Qu0/8A8t8hTCHXXdN1WnsI3lgr2359J9pYWBovYWd96DTSFHxjc= privacy-mode des56 $c$3$65rSudD79U/DnWOc7CBtj4XoQBWfSXCuYkgcUO/yPWkBoQ==
snmp-agent trap source LoopBack0
#
ssh server enable
ssh user cqdl service-type stelnet authentication-type password
#
ntp-service unicast-server 55.2.40.1
ntp-service unicast-server 55.2.40.5
#
acl basic 2001
rule 0 permit source 55.254.13.0 0.0.0.255
rule 5 permit source 55.254.113.0 0.0.0.255
rule 10 deny
#
acl basic 2002
rule 0 permit source 55.254.113.0 0.0.0.255
rule 5 permit source 55.254.13.0 0.0.0.255
rule 10 permit source 55.5.0.0 0.0.255.255
rule 15 deny
#
domain system
#
aaa session-limit ftp 16
aaa session-limit telnet 16
aaa session-limit http 16
aaa session-limit ssh 16
aaa session-limit https 16
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user cqdl class manage
password hash $h$6$mBr/npIPlh0SPmWP$CyXWlkjfTYXZE3TgSiywNH5/pUfVyM/+mmEJyllfsR5FjkUYVAeVRXt0yBMJw0QUjnrtFI4WzMzy5mns1Cmz8g==
service-type ssh telnet terminal
authorization-attribute user-role level-15
authorization-attribute user-role network-admin
#
local-user cqdl-ssh class manage
password hash $h$6$T0goFcNjVHPObvrU$AYYsjwmxPrVOOEwD44GRdJNE52t5u1iPMstLkxMNyeLhTg/XV2cT4Jlst9Y45Ro+7hvLA1ldSkZ96w6jRo5jSQ==
service-type ssh
authorization-attribute user-role level-15
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
public-key peer 55.178.38.124
public-key-code begin
30819F300D06092A864886F70D010101050003818D0030818902818100C46C78C234801C04
09F39CE0BACF3E47F71CBA7456B7F2072A58364BB0CF5DA6AA9EF2D2D0F834D64FF6F5A620
5E1E6A267FDEE6E838A8BE61892206C77C23B8EBDC3325A12F5EEE8F658AD07F16C61D2046
51707CEE8B9EDA98C51A3C42798234FCCA84628A12E9E919290B54573E1C3BE822B7D8ED30
4DC5A47283191D83A70203010001
public-key-code end
peer-public-key end
#
public-key peer 55.179.38.124
public-key-code begin
30819F300D06092A864886F70D010101050003818D0030818902818100B1F4843C2CDE1554
394056A9E7FFFA44B88CE3A3FE0D46C46B6A37E8F9BA14CFB90952D2DC0A2787ACF25182F9
2EF660AF5CFD4DCF783ED6391143EDBD46D76468E16B08FBF66710F8748C6170B1DFFA4E31
F3C7CFA0BAD14437EA7C7C8FCAE32FCB97A72E930F52ECA1E2719BC3A8AFFEB08C5E87123E
B50F846ABDBF70A63D0203010001
public-key-code end
peer-public-key end
#
return
- 2018-11-02提问
- 举报
-
(0)
最佳答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明


暂无评论