SECPATH F1050内部服务器设置失败
- 1关注
- 1收藏,2943浏览
问题描述:
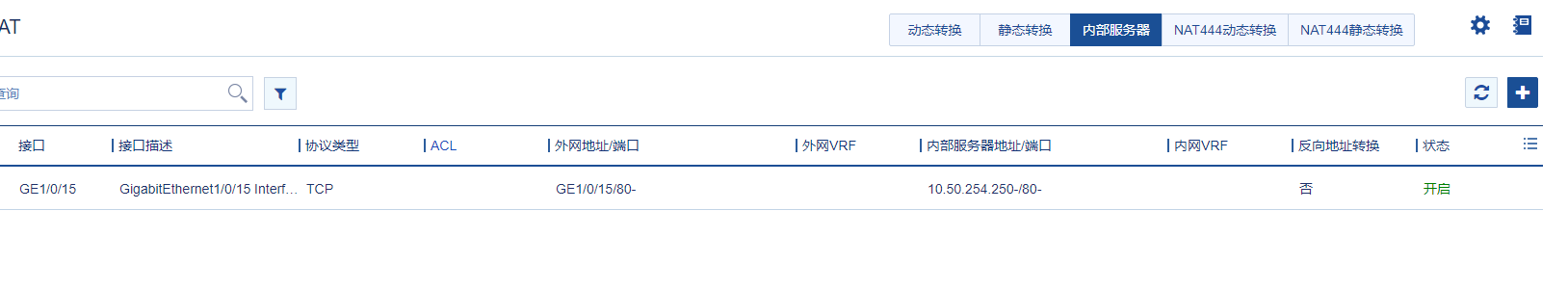
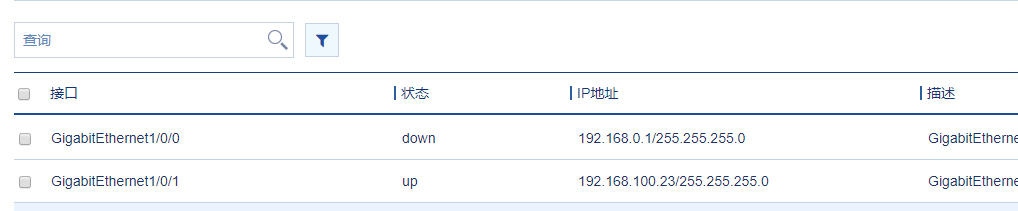
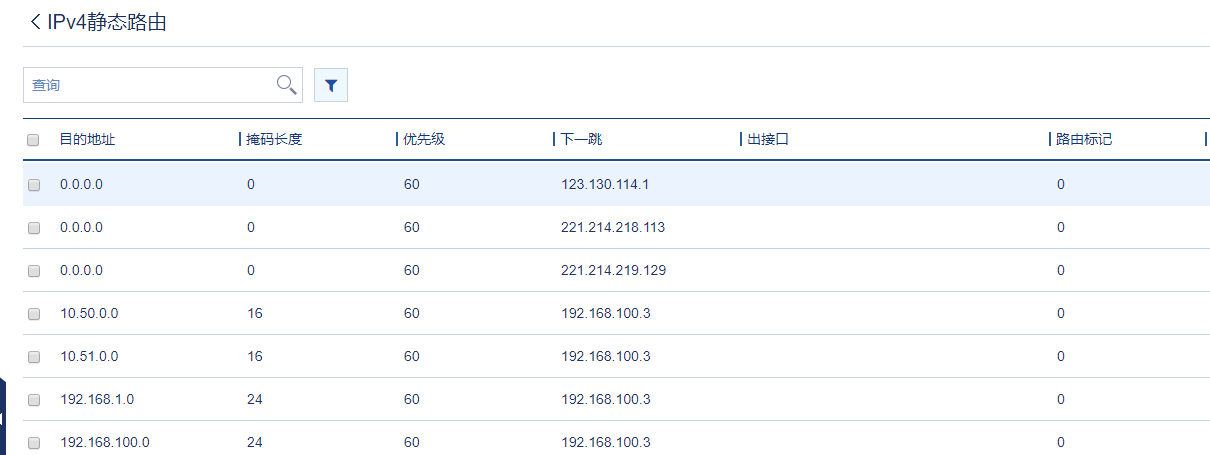
内部服务器10.50.254.250,通过端口1(192.168.100.23)可以访问。192.168.100.3为核心交换机(H3C 7510)
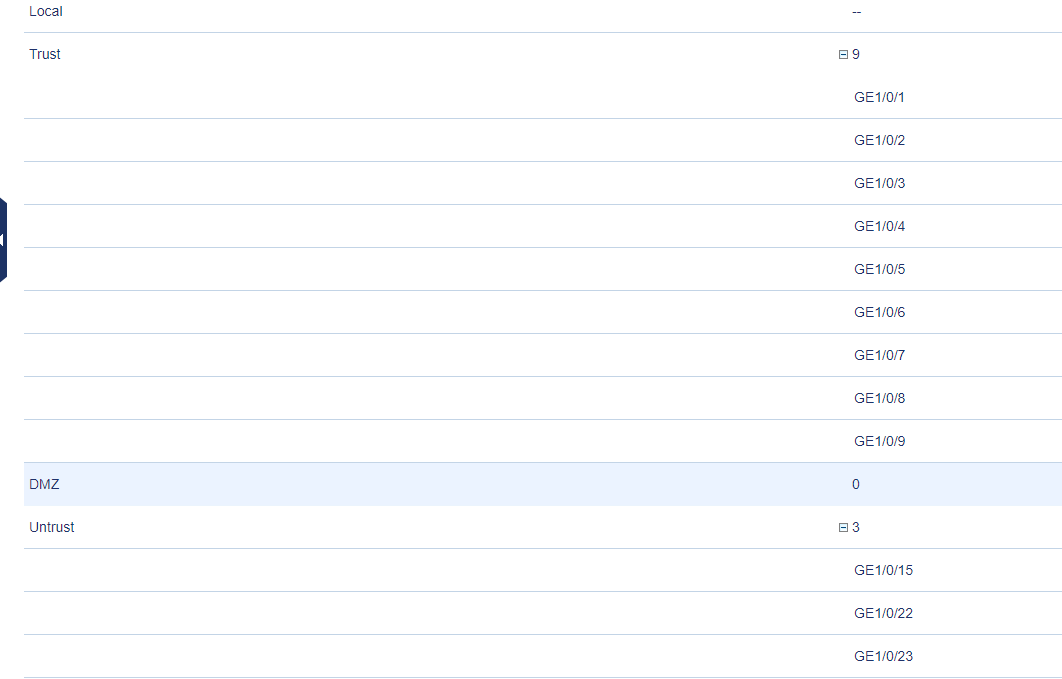
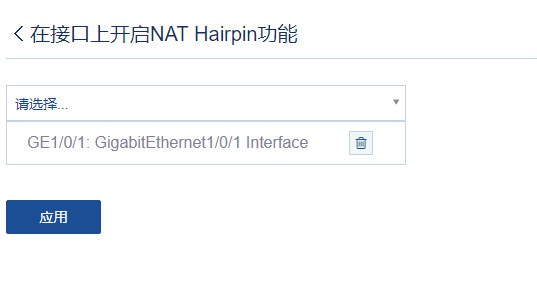
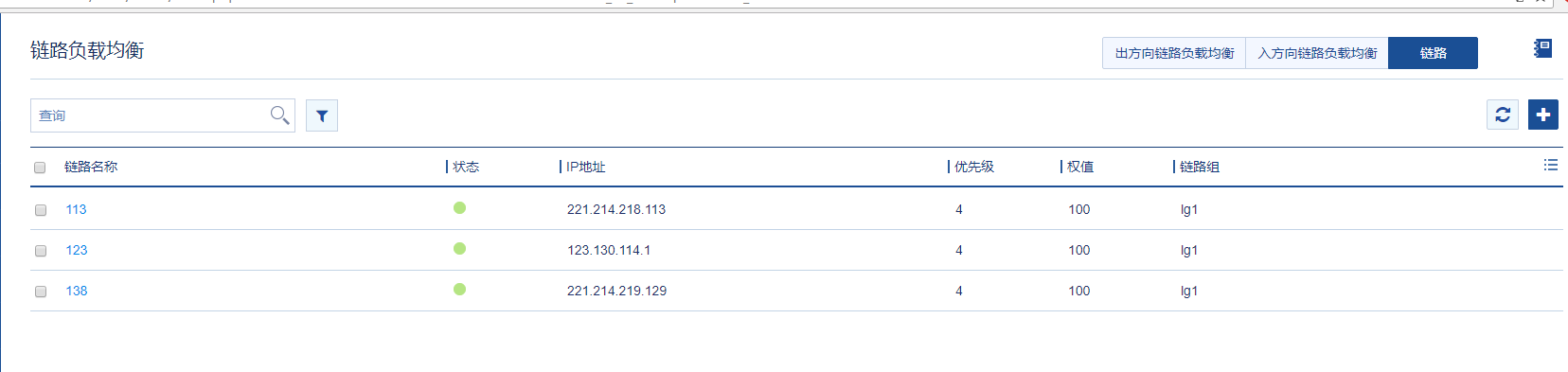
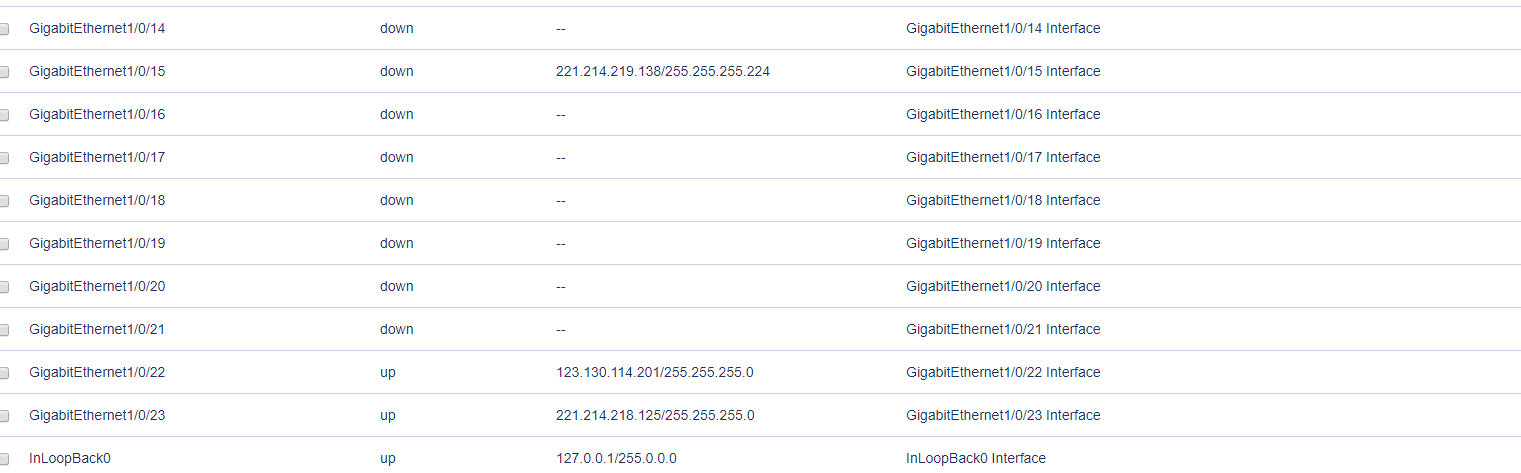
外网有三个链路(15,22,23口),已做负载均衡,其中221.214.219.138(15口)为网站的公网IP。已做NAT,并在NAT做内部服务器,安全策略已做trust与untrust双向互通,麻烦专家们给看一下什么情况,谢谢


组网及组网描述:
# version 7.1.064, Ess 9310P12 # sysname H3C # context Admin id 1 # ip vpn-instance management route-distinguisher 1000000000:1 vpn-target 1000000000:1 import-extcommunity vpn-target 1000000000:1 export-extcommunity # telnet server enable # irf mac-address persistent timer irf auto-update enable undo irf link-delay irf member 1 priority 1 # security-zone intra-zone default permit # ip unreachables enable ip ttl-expires enable # dns proxy enable dns server 202.102.152.3 dns server 202.102.134.68 # password-recovery enable # vlan 1 # nqa template icmp t1 # nqa template icmp t123.130.114.1 destination ip 123.130.114.1 # nqa template icmp t221.214.218.113 destination ip 221.214.218.113 # nqa template icmp t221.214.219.129 # interface NULL0 # interface GigabitEthernet1/0/0 port link-mode route ip binding vpn-instance management ip address 192.168.0.1 255.255.255.0 # interface GigabitEthernet1/0/1 port link-mode route ip address 192.168.100.23 255.255.255.0 nat hairpin enable # interface GigabitEthernet1/0/2 port link-mode route # interface GigabitEthernet1/0/3 port link-mode route # interface GigabitEthernet1/0/4 port link-mode route # interface GigabitEthernet1/0/5 port link-mode route # interface GigabitEthernet1/0/6 port link-mode route # interface GigabitEthernet1/0/7 port link-mode route # interface GigabitEthernet1/0/8 port link-mode route # interface GigabitEthernet1/0/9 port link-mode route # interface GigabitEthernet1/0/10 port link-mode route # interface GigabitEthernet1/0/11 port link-mode route # interface GigabitEthernet1/0/12 port link-mode route # interface GigabitEthernet1/0/13 port link-mode route nat outbound 3000 # interface GigabitEthernet1/0/14 port link-mode route # interface GigabitEthernet1/0/15 port link-mode route ip address 221.214.219.138 255.255.255.224 nat outbound 3000 nat server protocol tcp global current-interface 80 inside 10.50.254.226 80 # interface GigabitEthernet1/0/16 port link-mode route # interface GigabitEthernet1/0/17 port link-mode route # interface GigabitEthernet1/0/18 port link-mode route # interface GigabitEthernet1/0/19 port link-mode route # interface GigabitEthernet1/0/20 port link-mode route # interface GigabitEthernet1/0/21 port link-mode route # interface GigabitEthernet1/0/22 port link-mode route ip address 123.130.114.201 255.255.255.0 nat outbound 3000 # interface GigabitEthernet1/0/23 port link-mode route ip address 221.214.218.125 255.255.255.0 nat outbound 3000 # object-policy ip Local-Local rule 0 pass # object-policy ip Local-Trust rule 0 pass # object-policy ip Local-Untrust rule 0 pass # object-policy ip Trust-Local rule 0 pass # object-policy ip Trust-Trust rule 0 pass # object-policy ip Trust-Untrust rule 0 pass counting # object-policy ip Untrust-Local rule 0 pass counting # object-policy ip Untrust-Trust rule 0 pass counting # object-policy ip Untrust-Untrust rule 0 pass counting # security-zone name Local # security-zone name Trust import interface GigabitEthernet1/0/1 import interface GigabitEthernet1/0/2 import interface GigabitEthernet1/0/3 import interface GigabitEthernet1/0/4 import interface GigabitEthernet1/0/5 import interface GigabitEthernet1/0/6 import interface GigabitEthernet1/0/7 import interface GigabitEthernet1/0/8 import interface GigabitEthernet1/0/9 # security-zone name DMZ # security-zone name Untrust import interface GigabitEthernet1/0/15 import interface GigabitEthernet1/0/22 import interface GigabitEthernet1/0/23 # security-zone name Management import interface GigabitEthernet1/0/0 # zone-pair security source Any destination Any # zone-pair security source Local destination Local object-policy apply ip Local-Local # zone-pair security source Local destination Trust object-policy apply ip Local-Trust # zone-pair security source Local destination Untrust object-policy apply ip Local-Untrust # zone-pair security source Trust destination Local object-policy apply ip Trust-Local # zone-pair security source Trust destination Trust object-policy apply ip Trust-Trust # zone-pair security source Trust destination Untrust object-policy apply ip Trust-Untrust # zone-pair security source Untrust destination Local object-policy apply ip Untrust-Local # zone-pair security source Untrust destination Trust object-policy apply ip Untrust-Trust # zone-pair security source Untrust destination Untrust object-policy apply ip Untrust-Untrust # scheduler logfile size 16 # line class aux user-role network-operator # line class console user-role network-admin # line class vty user-role network-operator # line aux 0 user-role network-admin # line con 0 authentication-mode scheme user-role network-admin # line vty 0 63 authentication-mode scheme user-role network-admin # ip route-static 0.0.0.0 0 123.130.114.1 ip route-static 0.0.0.0 0 221.214.218.113 ip route-static 0.0.0.0 0 221.214.219.129 ip route-static 10.50.0.0 16 192.168.100.3 ip route-static 10.51.0.0 16 192.168.100.3 ip route-static 192.168.1.0 24 192.168.100.3 ip route-static 192.168.100.0 24 192.168.100.3 # snmp-agent snmp-agent local-engineid 800063A28084D93181B0B300000001 snmp-agent community read YTLG-R snmp-agent community write YTLG-W # ssh server enable # acl advanced 3000 rule 0 permit ip # acl advanced 3010 description 内网服务器 rule 0 permit ip source 10.50.254.0 0.0.0.255 rule 0 comment 内网访问外网 # domain system # aaa session-limit ftp 16 aaa session-limit telnet 16 aaa session-limit ssh 16 domain default enable system # role name level-0 description Predefined level-0 role # role name level-1 description Predefined level-1 role # role name level-2 description Predefined level-2 role # role name level-3 description Predefined level-3 role # role name level-4 description Predefined level-4 role # role name level-5 description Predefined level-5 role # role name level-6 description Predefined level-6 role # role name level-7 description Predefined level-7 role # role name level-8 description Predefined level-8 role # role name level-9 description Predefined level-9 role # role name level-10 description Predefined level-10 role # role name level-11 description Predefined level-11 role # role name level-12 description Predefined level-12 role # role name level-13 description Predefined level-13 role # role name level-14 description Predefined level-14 role # user-group system # local-user admin class manage password hash $h$6$to7dn7J98dr8Yypk$y2RKu9lxZoayrhU4ASR2uY2ijwTJsFTcHc1SSxx1eMOHe1CyDiQcveGGZ+8UbXV3eV+RmjPqPsxZetExym6vrw== service-type ssh telnet terminal https authorization-attribute user-role level-3 authorization-attribute user-role network-admin authorization-attribute user-role network-operator # ip https enable # loadbalance link-group lg1 transparent enable probe t123.130.114.1 probe t221.214.218.113 probe t221.214.219.129 success-criteria at-least 1 # loadbalance action ##defaultactionforllbipv4##%%autocreatedbyweb%% type link-generic link-group lg1 # loadbalance policy ##defaultpolicyforllbipv4##%%autocreatedbyweb%% type link-generic default-class action ##defaultactionforllbipv4##%%autocreatedbyweb%% # virtual-server ##defaultvsforllbipv4##%%autocreatedbyweb%% type link-ip virtual ip address 0.0.0.0 0 lb-policy ##defaultpolicyforllbipv4##%%autocreatedbyweb%% service enable bandwidth busy-protection enable bandwidth interface statistics enable # loadbalance link 113 router ip 221.214.218.113 link-group lg1 rate-limit bandwidth 200000 probe t221.214.218.113 # loadbalance link 123 router ip 123.130.114.1 link-group lg1 rate-limit bandwidth 200000 probe t123.130.114.1 # loadbalance link 138 router ip 221.214.219.129 link-group lg1 probe t221.214.219.129 # traffic-policy # ips policy default # anti-virus policy default # return
- 2018-11-12提问
- 举报
-
(0)
最佳答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明





暂无评论