IPSecVPN配置好后,分部可以访问总部内网,但是总部无法访问分部内网
- 0关注
- 1收藏,4679浏览
问题描述:
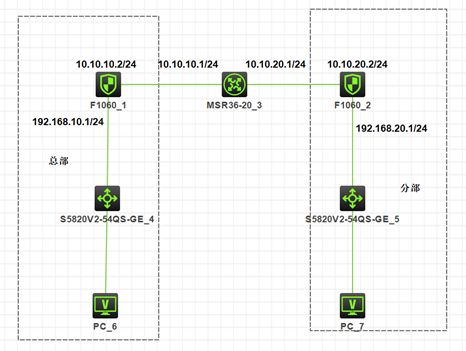
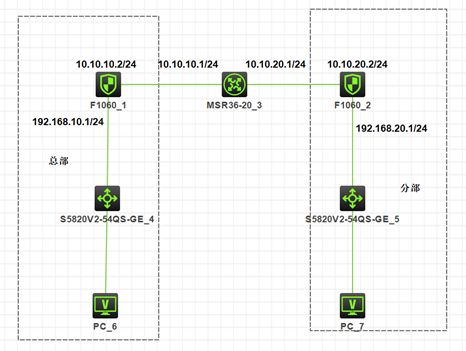
IPSecVPN配置完后,PC7可以ping通PC6,但是PC6无法ping通PC7和PC7的网关,但是PC6可以ping通分部防火墙的出口地址10.10.20.2 。拓扑图如下:
组网及组网描述:
IPSecVPN配置完后,PC7可以ping通PC6,但是PC6无法ping通PC7和PC7的网关,但是PC6可以ping通分部防火墙的出口地址10.10.20.2 。拓扑图如下:
- 2020-07-09提问
- 举报
-
(0)

反向的策略放通了吗
- 2020-07-09回答
- 评论(1)
- 举报
-
(0)
总部防火墙配置: # dhcp enable # object-group ip address 192.168.10.0 0 network subnet 192.168.10.0 255.255.255.0 # object-group ip address 192.168.20.0 0 network subnet 192.168.20.0 255.255.255.0 # dhcp server ip-pool 1 gateway-list 192.168.10.1 network 192.168.10.0 mask 255.255.255.0 dns-list 114.114.114.114 # interface GigabitEthernet1/0/2 port link-mode route combo enable copper ip address 10.10.10.2 255.255.255.0 nat outbound 3888 ipsec apply policy GE1/0/2 # interface GigabitEthernet1/0/3 port link-mode route combo enable copper ip address 192.168.10.1 255.255.255.0 # object-policy ip Local-Untrust rule 0 pass # object-policy ip Untrust-Local rule 0 pass # object-policy ip Untrust-Trust rule 0 pass source-ip 192.168.20.0 destination-ip 192.168.10.0 # object-policy ip pass rule 0 pass # security-zone name Local # security-zone name Trust import interface GigabitEthernet1/0/3 # security-zone name DMZ # security-zone name Untrust import interface GigabitEthernet1/0/2 # security-zone name Management # zone-pair security source Local destination Trust object-policy apply ip pass # zone-pair security source Local destination Untrust object-policy apply ip Local-Untrust # zone-pair security source Trust destination Local object-policy apply ip pass # zone-pair security source Trust destination Untrust object-policy apply ip pass # zone-pair security source Untrust destination Local object-policy apply ip Untrust-Local # zone-pair security source Untrust destination Trust object-policy apply ip Untrust-Trust # ip route-static 0.0.0.0 0 10.10.10.1 # acl advanced 3888 rule 0 deny ip source 192.168.10.0 0.0.0.255 destination 191.168.20.0 0.0.0.255 rule 5 permit ip # acl advanced 3999 rule 0 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255 # ipsec transform-set 1 esp encryption-algorithm aes-cbc-128 esp authentication-algorithm sha1 # ipsec policy GE1/0/2 1 isakmp transform-set 1 security acl 3999 local-address 10.10.10.2 remote-address 10.10.20.2 ike-profile 1 # ike profile 1 keychain 1 local-identity address 10.10.10.2 match remote identity address 10.10.20.2 255.255.255.255 proposal 1 # ike proposal 1 # ike keychain 1 pre-shared-key address 10.10.20.2 255.255.255.255 key cipher $c$3$4LVZia7hN/heDxTWLqgLpp/DZtfvE8L68g== # 分部防火墙配置: # dhcp enable # object-group ip address 192.168.10.0 0 network subnet 192.168.10.0 255.255.255.0 # object-group ip address 192.168.20.0 0 network subnet 192.168.20.0 255.255.255.0 # dhcp server ip-pool 1 gateway-list 192.168.20.1 network 192.168.20.0 mask 255.255.255.0 dns-list 114.114.114.114 # interface GigabitEthernet1/0/2 port link-mode route combo enable copper ip address 10.10.20.2 255.255.255.0 nat outbound 3888 ipsec apply policy GE1/0/2 # interface GigabitEthernet1/0/3 port link-mode route combo enable copper ip address 192.168.20.1 255.255.255.0 # object-policy ip Local-Unreust rule 0 pass # object-policy ip Local-Untrust rule 0 pass # object-policy ip Untrust-Local rule 0 pass # object-policy ip Untrust-Trust rule 0 pass source-ip 192.168.10.0 destination-ip 192.168.20.0 # object-policy ip pass rule 0 pass # security-zone name Local # security-zone name Trust import interface GigabitEthernet1/0/3 # security-zone name DMZ # security-zone name Untrust import interface GigabitEthernet1/0/2 # security-zone name Management # security-zone name Utrust # zone-pair security source Local destination Trust object-policy apply ip pass # zone-pair security source Local destination Untrust object-policy apply ip Local-Untrust # zone-pair security source Trust destination Local object-policy apply ip pass # zone-pair security source Trust destination Untrust object-policy apply ip pass # zone-pair security source Untrust destination Local object-policy apply ip Untrust-Local # zone-pair security source Untrust destination Trust object-policy apply ip Untrust-Trust # ip route-static 0.0.0.0 0 10.10.20.1 # acl advanced 3888 rule 0 deny ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255 rule 5 permit ip # acl advanced 3999 rule 0 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255 # ipsec transform-set 1 esp encryption-algorithm aes-cbc-128 esp authentication-algorithm sha1 # ipsec policy GE1/0/2 1 isakmp transform-set 1 security acl 3999 local-address 10.10.20.2 remote-address 10.10.10.2 ike-profile 1 # ike profile 1 keychain 1 local-identity address 10.10.20.2 match remote identity address 10.10.10.2 255.255.255.255 proposal 1 # ike proposal 1 # ike keychain 1 pre-shared-key address 10.10.10.2 255.255.255.255 key cipher $c$3$1I1Px77NuL+VBk0089I8Ii3mmnCKTBeIPQ== #

您好,请知:
请确认分部这边的感兴趣数据流是否包含了总部的业务地址。
另外分部这边需要做双向的域间策略及安全策略,因为总部也需要访问过来。
- 2020-07-09回答
- 评论(2)
- 举报
-
(0)
这是两台设备的配置, 按理说分部和总部除了兴趣流相反以外其他的基本配置一致嘛! 但是我详细看过配置并没发现其他地方有不对的
总部防火墙配置: # dhcp enable # object-group ip address 192.168.10.0 0 network subnet 192.168.10.0 255.255.255.0 # object-group ip address 192.168.20.0 0 network subnet 192.168.20.0 255.255.255.0 # dhcp server ip-pool 1 gateway-list 192.168.10.1 network 192.168.10.0 mask 255.255.255.0 dns-list 114.114.114.114 # interface GigabitEthernet1/0/2 port link-mode route combo enable copper ip address 10.10.10.2 255.255.255.0 nat outbound 3888 ipsec apply policy GE1/0/2 # interface GigabitEthernet1/0/3 port link-mode route combo enable copper ip address 192.168.10.1 255.255.255.0 # object-policy ip Local-Untrust rule 0 pass # object-policy ip Untrust-Local rule 0 pass # object-policy ip Untrust-Trust rule 0 pass source-ip 192.168.20.0 destination-ip 192.168.10.0 # object-policy ip pass rule 0 pass # security-zone name Local # security-zone name Trust import interface GigabitEthernet1/0/3 # security-zone name DMZ # security-zone name Untrust import interface GigabitEthernet1/0/2 # security-zone name Management # zone-pair security source Local destination Trust object-policy apply ip pass # zone-pair security source Local destination Untrust object-policy apply ip Local-Untrust # zone-pair security source Trust destination Local object-policy apply ip pass # zone-pair security source Trust destination Untrust object-policy apply ip pass # zone-pair security source Untrust destination Local object-policy apply ip Untrust-Local # zone-pair security source Untrust destination Trust object-policy apply ip Untrust-Trust # ip route-static 0.0.0.0 0 10.10.10.1 # acl advanced 3888 rule 0 deny ip source 192.168.10.0 0.0.0.255 destination 191.168.20.0 0.0.0.255 rule 5 permit ip # acl advanced 3999 rule 0 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255 # ipsec transform-set 1 esp encryption-algorithm aes-cbc-128 esp authentication-algorithm sha1 # ipsec policy GE1/0/2 1 isakmp transform-set 1 security acl 3999 local-address 10.10.10.2 remote-address 10.10.20.2 ike-profile 1 # ike profile 1 keychain 1 local-identity address 10.10.10.2 match remote identity address 10.10.20.2 255.255.255.255 proposal 1 # ike proposal 1 # ike keychain 1 pre-shared-key address 10.10.20.2 255.255.255.255 key cipher $c$3$4LVZia7hN/heDxTWLqgLpp/DZtfvE8L68g== # 分部防火墙配置: # dhcp enable # object-group ip address 192.168.10.0 0 network subnet 192.168.10.0 255.255.255.0 # object-group ip address 192.168.20.0 0 network subnet 192.168.20.0 255.255.255.0 # dhcp server ip-pool 1 gateway-list 192.168.20.1 network 192.168.20.0 mask 255.255.255.0 dns-list 114.114.114.114 # interface GigabitEthernet1/0/2 port link-mode route combo enable copper ip address 10.10.20.2 255.255.255.0 nat outbound 3888 ipsec apply policy GE1/0/2 # interface GigabitEthernet1/0/3 port link-mode route combo enable copper ip address 192.168.20.1 255.255.255.0 # object-policy ip Local-Unreust rule 0 pass # object-policy ip Local-Untrust rule 0 pass # object-policy ip Untrust-Local rule 0 pass # object-policy ip Untrust-Trust rule 0 pass source-ip 192.168.10.0 destination-ip 192.168.20.0 # object-policy ip pass rule 0 pass # security-zone name Local # security-zone name Trust import interface GigabitEthernet1/0/3 # security-zone name DMZ # security-zone name Untrust import interface GigabitEthernet1/0/2 # security-zone name Management # security-zone name Utrust # zone-pair security source Local destination Trust object-policy apply ip pass # zone-pair security source Local destination Untrust object-policy apply ip Local-Untrust # zone-pair security source Trust destination Local object-policy apply ip pass # zone-pair security source Trust destination Untrust object-policy apply ip pass # zone-pair security source Untrust destination Local object-policy apply ip Untrust-Local # zone-pair security source Untrust destination Trust object-policy apply ip Untrust-Trust # ip route-static 0.0.0.0 0 10.10.20.1 # acl advanced 3888 rule 0 deny ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255 rule 5 permit ip # acl advanced 3999 rule 0 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255 # ipsec transform-set 1 esp encryption-algorithm aes-cbc-128 esp authentication-algorithm sha1 # ipsec policy GE1/0/2 1 isakmp transform-set 1 security acl 3999 local-address 10.10.20.2 remote-address 10.10.10.2 ike-profile 1 # ike profile 1 keychain 1 local-identity address 10.10.20.2 match remote identity address 10.10.10.2 255.255.255.255 proposal 1 # ike proposal 1 # ike keychain 1 pre-shared-key address 10.10.10.2 255.255.255.255 key cipher $c$3$1I1Px77NuL+VBk0089I8Ii3mmnCKTBeIPQ== #
这是两台设备的配置, 按理说分部和总部除了兴趣流相反以外其他的基本配置一致嘛! 但是我详细看过配置并没发现其他地方有不对的
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明



总部防火墙配置: # dhcp enable # object-group ip address 192.168.10.0 0 network subnet 192.168.10.0 255.255.255.0 # object-group ip address 192.168.20.0 0 network subnet 192.168.20.0 255.255.255.0 # dhcp server ip-pool 1 gateway-list 192.168.10.1 network 192.168.10.0 mask 255.255.255.0 dns-list 114.114.114.114 # interface GigabitEthernet1/0/2 port link-mode route combo enable copper ip address 10.10.10.2 255.255.255.0 nat outbound 3888 ipsec apply policy GE1/0/2 # interface GigabitEthernet1/0/3 port link-mode route combo enable copper ip address 192.168.10.1 255.255.255.0 # object-policy ip Local-Untrust rule 0 pass # object-policy ip Untrust-Local rule 0 pass # object-policy ip Untrust-Trust rule 0 pass source-ip 192.168.20.0 destination-ip 192.168.10.0 # object-policy ip pass rule 0 pass # security-zone name Local # security-zone name Trust import interface GigabitEthernet1/0/3 # security-zone name DMZ # security-zone name Untrust import interface GigabitEthernet1/0/2 # security-zone name Management # zone-pair security source Local destination Trust object-policy apply ip pass # zone-pair security source Local destination Untrust object-policy apply ip Local-Untrust # zone-pair security source Trust destination Local object-policy apply ip pass # zone-pair security source Trust destination Untrust object-policy apply ip pass # zone-pair security source Untrust destination Local object-policy apply ip Untrust-Local # zone-pair security source Untrust destination Trust object-policy apply ip Untrust-Trust # ip route-static 0.0.0.0 0 10.10.10.1 # acl advanced 3888 rule 0 deny ip source 192.168.10.0 0.0.0.255 destination 191.168.20.0 0.0.0.255 rule 5 permit ip # acl advanced 3999 rule 0 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255 # ipsec transform-set 1 esp encryption-algorithm aes-cbc-128 esp authentication-algorithm sha1 # ipsec policy GE1/0/2 1 isakmp transform-set 1 security acl 3999 local-address 10.10.10.2 remote-address 10.10.20.2 ike-profile 1 # ike profile 1 keychain 1 local-identity address 10.10.10.2 match remote identity address 10.10.20.2 255.255.255.255 proposal 1 # ike proposal 1 # ike keychain 1 pre-shared-key address 10.10.20.2 255.255.255.255 key cipher $c$3$4LVZia7hN/heDxTWLqgLpp/DZtfvE8L68g== # 分部防火墙配置: # dhcp enable # object-group ip address 192.168.10.0 0 network subnet 192.168.10.0 255.255.255.0 # object-group ip address 192.168.20.0 0 network subnet 192.168.20.0 255.255.255.0 # dhcp server ip-pool 1 gateway-list 192.168.20.1 network 192.168.20.0 mask 255.255.255.0 dns-list 114.114.114.114 # interface GigabitEthernet1/0/2 port link-mode route combo enable copper ip address 10.10.20.2 255.255.255.0 nat outbound 3888 ipsec apply policy GE1/0/2 # interface GigabitEthernet1/0/3 port link-mode route combo enable copper ip address 192.168.20.1 255.255.255.0 # object-policy ip Local-Unreust rule 0 pass # object-policy ip Local-Untrust rule 0 pass # object-policy ip Untrust-Local rule 0 pass # object-policy ip Untrust-Trust rule 0 pass source-ip 192.168.10.0 destination-ip 192.168.20.0 # object-policy ip pass rule 0 pass # security-zone name Local # security-zone name Trust import interface GigabitEthernet1/0/3 # security-zone name DMZ # security-zone name Untrust import interface GigabitEthernet1/0/2 # security-zone name Management # security-zone name Utrust # zone-pair security source Local destination Trust object-policy apply ip pass # zone-pair security source Local destination Untrust object-policy apply ip Local-Untrust # zone-pair security source Trust destination Local object-policy apply ip pass # zone-pair security source Trust destination Untrust object-policy apply ip pass # zone-pair security source Untrust destination Local object-policy apply ip Untrust-Local # zone-pair security source Untrust destination Trust object-policy apply ip Untrust-Trust # ip route-static 0.0.0.0 0 10.10.20.1 # acl advanced 3888 rule 0 deny ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255 rule 5 permit ip # acl advanced 3999 rule 0 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255 # ipsec transform-set 1 esp encryption-algorithm aes-cbc-128 esp authentication-algorithm sha1 # ipsec policy GE1/0/2 1 isakmp transform-set 1 security acl 3999 local-address 10.10.20.2 remote-address 10.10.10.2 ike-profile 1 # ike profile 1 keychain 1 local-identity address 10.10.20.2 match remote identity address 10.10.10.2 255.255.255.255 proposal 1 # ike proposal 1 # ike keychain 1 pre-shared-key address 10.10.10.2 255.255.255.255 key cipher $c$3$1I1Px77NuL+VBk0089I8Ii3mmnCKTBeIPQ== #