组网及说明
无
问题描述
某局点客户反馈WX554H版本是Release 5219在公网配置802.1x认证,客户端认证不成功。相同配置情况下,AC和AP走VPN隧道时是可以认证成功的。
AC侧debug显示终端802.1x认证失败
测试终端地址1c4d-70e6-6a1d
%Apr 21 12:01:34:810 2018 New_WirelessAC_5540H DOT1X/5/DOT1X_WLAN_LOGIN_FAILURE: -Username=-UserMAC=1c4d-70e6-6a1d-BSSID=9ce8-95c5-7c00-SSID=Glodon_Wifi-VLANID=1005; A user failed 802.1X authentication.
过程分析
第一步
确认清楚组网,AC和AP是跨过公网注册的,AC互联网出口设备映射了AC UDP 5246/5247端口,AP所在局域网出口也有NAT设备,此时AP可以正常上线
AP注册信息
[5540H]dis wlan ap all add | in tianjin
tian-ap-01 111.62.80.22 9ce8-95c5-7c00
tian-ap-02 111.62.80.22 7425-8a4b-0e40
tian-ap-03 111.62.80.22 7425-8a4b-0f80
tian-ap-04 111.62.80.22 7425-8a80-2a60
[5540H]
第二步
AC、AP相关配置
服务模板
[5540H-wlan-st-101]dis this
wlan service-template 101
ssid GlodWifi
vlan 1005
client forwarding-location ap///本地转发,集中认证
akm mode dot1x
cipher-suite ccmp
security-ie rsn
client-security authentication-mode dot1x
dot1x domain dot1x
service-template enable
#
AP配置
[5540H-wlan-ap-tianjin-ap-04]dis this
#
wlan ap tianjin-ap-04 model WA2620i-AGN
serial-id 219801A0CNC15B001360
map-configuration cfa0:/ap.txt
hybrid-remote-ap enable
radio 1
radio enable
service-template 101 vlan 1005
service-template 102 vlan 1006
radio 2
radio enable
service-template 101 vlan 1005
service-template 102 vlan 1006
802.1x认证相关配置没有问题
第三步
AC侧收集下面DEBUG信息分析
debugging wlan access-security all
debugging dot1x all
Debug radius packet
T d
T m
*Apr 21 13:05:39:852 2018 New_WirelessAC_5540H STAMGR/7/Event: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]Started 802.1X authentication.
*Apr 21 13:05:39:852 2018 New_WirelessAC_5540H STAMGR/7/FSM: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]PAE state machine entered Initialize state.
*Apr 21 13:05:39:852 2018 New_WirelessAC_5540H STAMGR/7/FSM: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]BE state machine entered Initialize state.
*Apr 21 13:05:39:852 2018 New_WirelessAC_5540H STAMGR/7/FSM: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]PAE state machine entered Disconnect state.
*Apr 21 13:05:39:852 2018 New_WirelessAC_5540H STAMGR/7/FSM: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]BE state machine entered Idle state.
*Apr 21 13:05:39:852 2018 New_WirelessAC_5540H STAMGR/7/FSM: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]PAE state machine entered Restart state.
*Apr 21 13:05:39:853 2018 New_WirelessAC_5540H STAMGR/7/FSM: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]PAE state machine entered Connecting state.
*Apr 21 13:05:39:853 2018 New_WirelessAC_5540H STAMGR/7/FSM: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]PAE state machine entered Authenticating state.
*Apr 21 13:05:39:853 2018 New_WirelessAC_5540H STAMGR/7/FSM: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]BE state machine entered Request state.
*Apr 21 13:05:39:854 2018 New_WirelessAC_5540H STAMGR/7/PktSend: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]
-----Packet HEAD-----
Mac Frame Type: 0x888e
Protocol Version ID: 0x1
Packet Type: 0x0///EAP-Packet
Packet Length: 5
-----Packet Body-----
Code: 0x1 ///Request (eap-request),AC发了EAP用户名请求报文
Identifier: 1
Length: 5
*Apr 21 13:05:39:854 2018 New_WirelessAC_5540H STAMGR/7/Timer: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]Created the client response timer.
*Apr 21 13:05:42:910 2018 New_WirelessAC_5540H STAMGR/7/Timer: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]Client response timer expired.
*Apr 21 13:05:42:910 2018 New_WirelessAC_5540H STAMGR/7/Timer: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]Deleted the client response timer.
*Apr 21 13:05:42:911 2018 New_WirelessAC_5540H STAMGR/7/FSM: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]BE state machine entered Request state.
*Apr 21 13:05:42:911 2018 New_WirelessAC_5540H STAMGR/7/PktSend: [MAC: 1c4d-70e6-6a1d, BSSID: 9ce8-95c5-7c00]
-----Packet HEAD-----
Mac Frame Type: 0x888e
Protocol Version ID: 0x1
Packet Type: 0x0///EAP-Packet
Packet Length: 5
-----Packet Body-----
Code: 0x1 ///Request (eap-request),AC再次发了EAP用户名请求报文
Identifier: 1
Length: 5
通过上述DEBUG信息分析,应该还是网络问题,AC一直没有收到AP的EAP回复报文
第四步
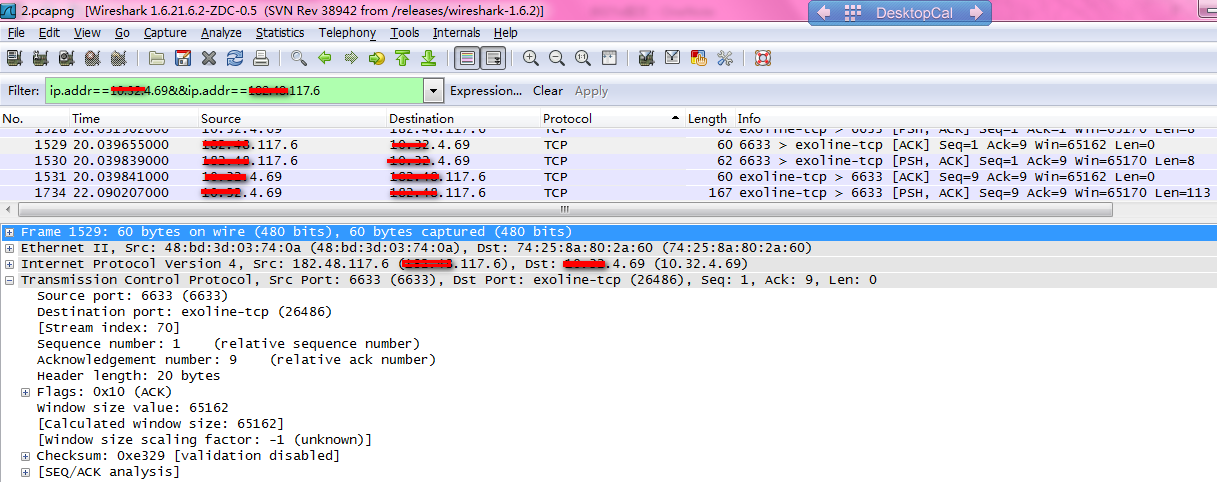
客户反馈AC和AP走VPN隧道时是可以认证成功的,同时出口协议分析软件记录到AP和AC之间不光用UDP 5246/5247端口通信,还有AC的TCP 6633端口通信,AP地址是x.x.4.69,AC地址是x.x.2.250

此时,建议客户走公网时也映射AC的tcp 6633端口测试,映射之后802.1x认证问题解决。
为了确认上述端口用途,在走公网时,抓取AP的报文,也证实了上述分析,AC以TCP6633端口为源端口向AP发三次请求报文,由于AC没有映射TCP6633端口,因此AP直接中断了三次握手。
解决方法
AC出口NAT设备映射AC的TCP6633端口,找研发确认集中认证,本地转发的情况下,DOT1X的EAP报文是借助OpenFlow通道(TCP 6633)跟AC传递的,否则EAP报文交互就不通。
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
