在SecPath ACG1000和U200-A之间建立一个IPSec隧道,对SecPath ACG1000下属的子网(192.168.1.0/24)与U200-A下属的子网(192.168.2.0/24)之间的数据流进行安全保护
1. SecPath ACG1000和U200-A之间采用IKE协商方式建立IPSec SA
2. U200-A侧使用缺省的IKE提议
3. 使用预共享密钥认证方法
设备清单:SecPath ACG1000 1台、U200-A 1台、PC 2台

图1 SecPath ACG1000与U200-A IPSec 主模式的典型配置组网图
SecPath ACG1000设备版本:i-Ware software,Version 1.10,Release 6604P01
U200-A设备版本:Comware Software, Version 5.20, Release 5142P04
SecPath ACG1000配置:
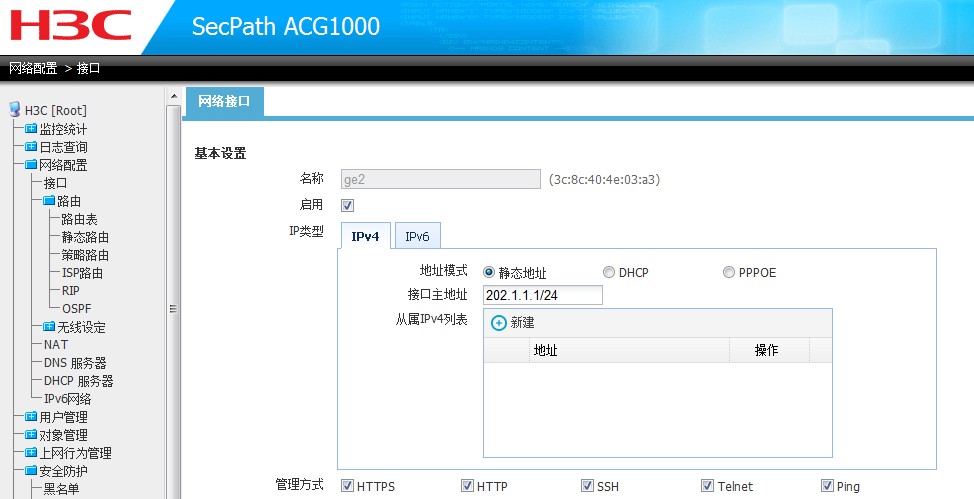
1.配置0/2接口
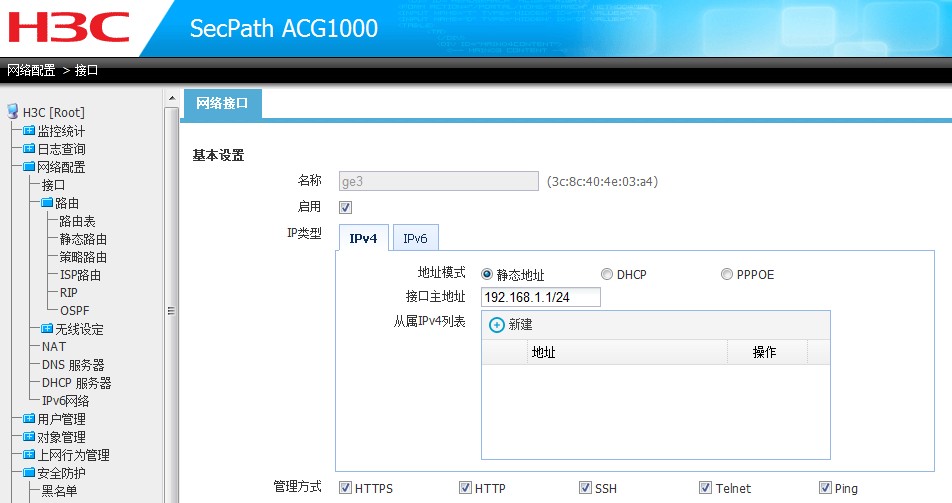
2.配置0/3接口
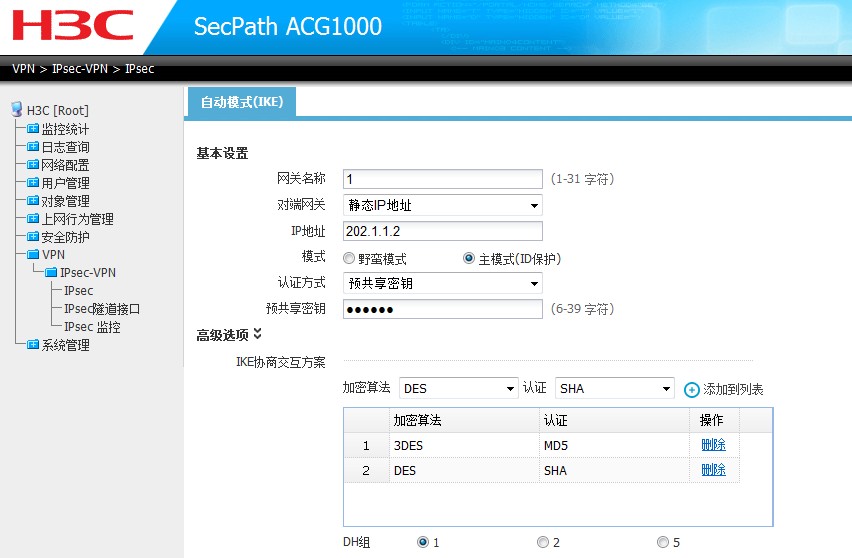
3.配置IKE参数
4.配置IPSec参数

5.配置IPSec隧道参数

6.配置去往对端的静态路由

7.配置去往公网的静态路由

U200-A配置:
1.配置外网接口地址
[U200-A]interface GigabitEthernet 0/2
[U200-A-GigabitEthernet0/2]
[U200-A-GigabitEthernet0/2]ip address 202.1.1.2 24
2.配置内网接口地址
[U200-A]interface GigabitEthernet 0/3
[U200-A-GigabitEthernet0/3]
[U200-A-GigabitEthernet0/3]ip address 192.168.2.1 24
3.配置安全区域
[U200-A]zone name trust
[U200-A-zone-trust]
[U200-A-zone-trust]import interface GigabitEthernet 0/3
[U200-A-zone-trust]quit
[U200-A]
[U200-A]zone name untrust
[U200-A-zone-untrust]
[U200-A-zone-untrust]import interface GigabitEthernet 0/2
4.配置路由信息
[U200-A]ip route-static 192.168.1.0 24 202.1.1.1
5.配置安全acl 3000
[U200-A]acl number 3000
[U200-A-acl-adv-3000]
[U200-A-acl-adv-3000]rule 0 permit ip source 192.168.2.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[U200-A-acl-adv-3000]quit
6.配置IKE peer
[U200-A]ike peer 2
[U200-A-ike-peer-2]
[U200-A-ike-peer-2]pre-shared-key simple 123456
[U200-A-ike-peer-2]remote-address 202.1.1.1
[U200-A-ike-peer-2]quit
7.配置IPSec安全提议
[U200-A]ipsec transform-set 2
[U200-A-ipsec-transform-set-2]
[U200-A-ipsec-transform-set-2]encapsulation-mode tunnel
[U200-A-ipsec-transform-set-2]transform esp
[U200-A-ipsec-transform-set-2]esp encryption-algorithm 3des
[U200-A-ipsec-transform-set-2]esp authentication-algorithm sha1
[U200-A-ipsec-transform-set-2]quit
8.配置IPSec策略
[U200-A]ipsec policy 2 10 isakmp
[U200-A-ipsec-policy-isakmp-2-10]
[U200-A-ipsec-policy-isakmp-2-10]security acl 3000
[U200-A-ipsec-policy-isakmp-2-10]ike-peer 2
[U200-A-ipsec-policy-isakmp-2-10]transform-set 2
[U200-A-ipsec-policy-isakmp-2-10]quit
9.配置接口ipsec调用
[U200-A]interface GigabitEthernet 0/2
[U200-A-GigabitEthernet0/2]
[U200-A-GigabitEthernet0/2]ipsec policy 2
[U200-A-GigabitEthernet0/2]quit
10.配置对应安全策略
[U200-A]interzone source untrust destination trust
[U200-A-interzone-untrust-trust]
[U200-A-interzone-untrust-trust]rule 0 permit
[U200-A-interzone-untrust-trust-rule-0]
[U200-A-interzone-untrust-trust-rule-0]source-ip any_address
[U200-A-interzone-untrust-trust-rule-0]destination-ip any_address
[U200-A-interzone-untrust-trust-rule-0]service any_service
[U200-A-interzone-untrust-trust-rule-0]rule enable
[U200-A-interzone-untrust-trust-rule-0]quit
[U200-A-interzone-untrust-trust]
[U200-A-interzone-untrust-trust]quit
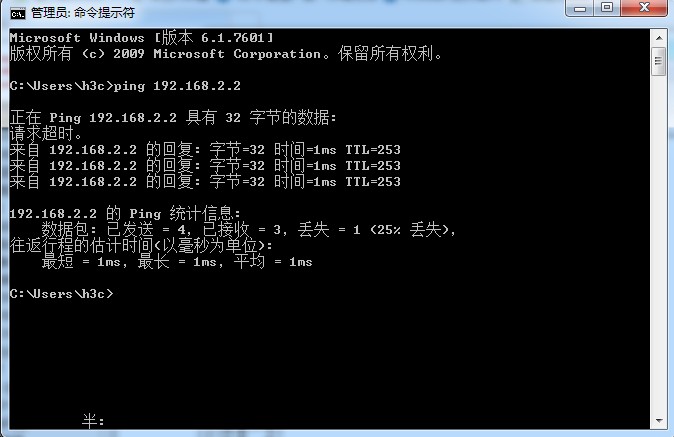
测试结果:
1.ping测试
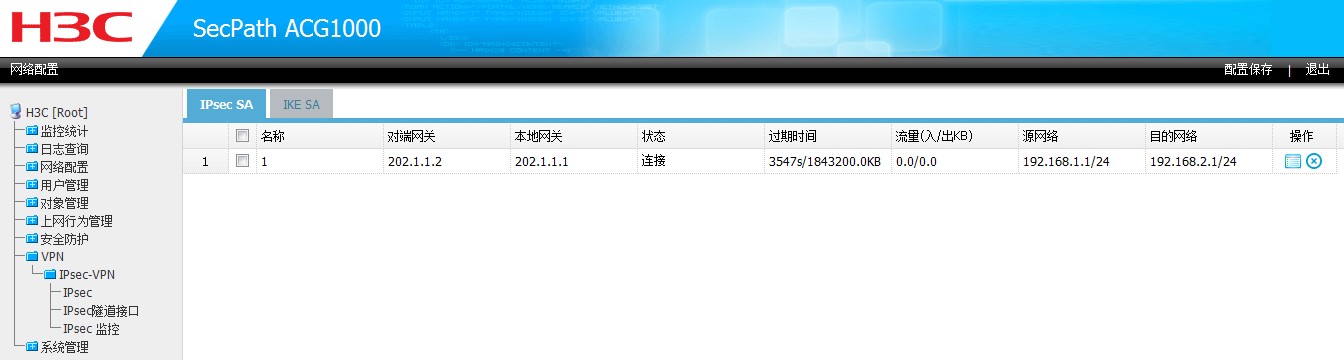
2.查看ACG 1000 IKE SA信息
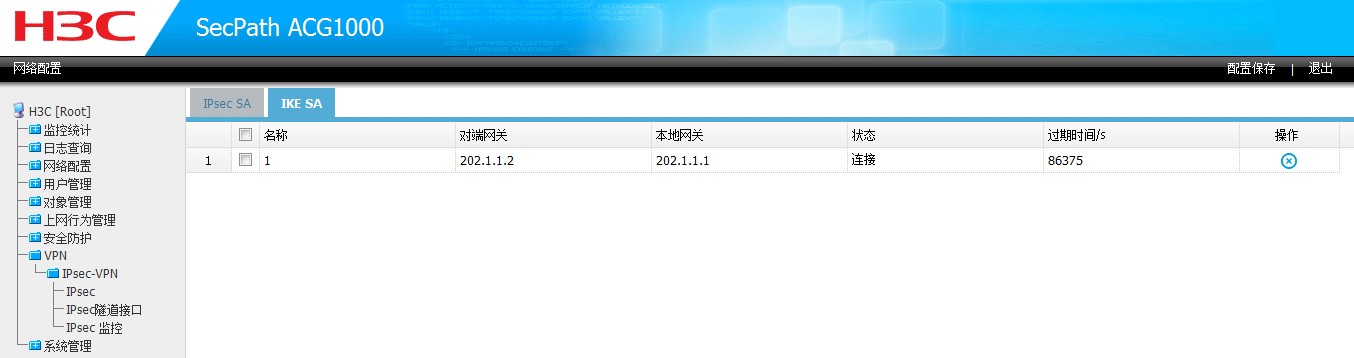
3. 查看ACG 1000 IPSec SA信息
4.查看U200-A ike sa信息
[U200-A]display ike sa
total phase-1 SAs: 1
connection-id peer flag phase doi
----------------------------------------------------------------
17 202.1.1.1 RD 1 IPSEC
18 202.1.1.1 RD 2 IPSEC
flag meaning
RD--READY ST--STAYALIVE RL--REPLACED FD--FADING TO—TIMEOUT
5.查看U200-A ipsec sa
[U200-A]display ipsec sa
===============================
Interface: GigabitEthernet0/2
path MTU: 1500
===============================
-----------------------------
IPsec policy name: "2"
sequence number: 10
acl version: ACL4
mode: isakmp
-----------------------------
connection id: 2
encapsulation mode: tunnel
perfect forward secrecy:
tunnel:
local address: 202.1.1.2
remote address: 202.1.1.1
flow:
sour addr: 192.168.2.1/255.255.255.0 port: 0 protocol: I
dest addr: 192.168.1.1/255.255.255.0 port: 0 protocol: I
[inbound ESP SAs]
spi: 1519083824 (0x5a8b6130)
proposal: ESP-ENCRYPT-3DES ESP-AUTH-SHA1
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843199/3489
max sequence number received: 3
anti-replay check enable: Y
anti-replay window size: 32
udp encapsulation used for nat traversal: N
[outbound ESP SAs]
spi: 217203258 (0xcf2423a)
proposal: ESP-ENCRYPT-3DES ESP-AUTH-SHA1
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843199/3489
max sequence number sent: 4
udp encapsulation used for nat traversal: N
配置关键点:
1. acg 1000 配置对端内网的路由必须指向和ipsec相关连的tunnel接口
2. tunnel接口地址没有固定要求 可以随意填写
3. acg 1000 默认的安全提议和U200-A安全提议不一致,配置时需要修改两端的安全提议一致,修改acg 1000的安全提议时选择之后要添加到列表才生效。
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
