CAS中抓包并将抓包文件拷贝到本地电脑分析
- 0关注
- 0收藏 1350浏览
当处理问题的时候,有时需要查看CAS系统接口的抓包信息,而CAS是基于Unbantu 开发的一个系统,所以传统的使用wireshark抓包的方式是不可行的。本文简单介绍使用Linux系统自带的tcpdump工具进行抓包,并通过软件将抓包文件传到用户本地电脑。
一:首先进入cas后台使用tcpdump抓包
root@cvknode:~# tcpdump -i eth0 host 192.168.154.1 //此命令为直接查看分析
tcpdump: WARNING: eth0: no IPv4 address assigned
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 65535 bytes
00:37:51.157455 IP cvknode.ssh > 192.168.154.1.62737: Flags [P.], seq 3779824190:3779824290, ack 2369285737, win 279, length 100
00:37:51.157676 IP 192.168.154.1.62737 > cvknode.ssh: Flags [.], ack 100, win 255, length 0
00:37:51.158731 IP cvknode.ssh > 192.168.154.1.62737: Flags [P.], seq 100:296, ack 1, win 279, length 196
00:37:51.238032 IP cvknode.ssh > 192.168.154.1.62737: Flags [P.], seq 296:668, ack 1, win 279, length 372
00:37:51.238423 IP cvknode.ssh > 192.168.154.1.62737: Flags [P.], seq 668:816, ack 1, win 279, length 148
00:37:51.238445 IP 192.168.154.1.62737 > cvknode.ssh: Flags [.], ack 668, win 256, length 0
00:37:51.238604 IP cvknode.ssh > 192.168.154.1.62737: Flags [P.], seq 816:1060, ack 1, win 279, length 244
00:37:51.242231 IP 192.168.154.1.62737 > cvknode.ssh: Flags [.], ack 1060, win 255, length 0
00:37:51.242450 IP cvknode.ssh > 192.168.154.1.62737: Flags [P.], seq 1060:1304, ack 1, win 279, length 244
00:37:51.242579 IP cvknode.ssh > 192.168.154.1.62737: Flags [P.], seq 1304:1452, ack 1, win 279, length 148
00:37:51.242702 IP cvknode.ssh > 192.168.154.1.62737: Flags [P.], seq 1452:1600, ack 1, win 279, length 148
00:37:51.242808 IP 192.168.154.1.62737 > cvknode.ssh: Flags [.], ack 1452, win 256, length 0
00:37:51.242820 IP cvknode.ssh > 192.168.154.1.62737: Flags [P.], seq 1600:1748, ack 1, win 279, length 148
00:37:51.243081 IP 192.168.154.1.62737 > cvknode.ssh: Flags [.], ack 1748, win 255, length 0
00:37:51.243121 IP cvknode.ssh > 192.168.154.1.62737: Flags [P.], seq 1748:2088, ack 1, win 279, length 340
00:37:51.243250 IP cvknode.ssh > 192.168.154.1.62737: Flags [P.], seq 2088:2236, ack 1, win 279, length 148
root@cvknode:~# tcpdump -i eth0 host 192.168.154.1 -w abc.cap //此命令抓包相应的包并写入到本地一个abc.cap 文件
tcpdump: WARNING: eth0: no IPv4 address assigned
tcpdump: listening on eth0, link-type EN10MB (Ethernet), capture size 65535 bytes
^C26 packets captured
27 packets received by filter
0 packets dropped by kernel
root@cvknode:~#
ctrl+C停止
root@cvknode:~# ll //通过命令ll 查看到此文件保存在路径 /root 下面
total 934996
drwx------ 4 root root 4096 Oct 21 00:23 ./
drwxr-xr-x 25 root root 4096 Oct 14 17:53 ../
-rw-r--r-- 1 root root 3001 Oct 21 00:38 abc.cap
-rw------- 1 root root 82 Oct 20 04:28 .bash_history
-rw-r--r-- 1 root root 3106 Apr 19 2012 .bashrc
drwx------ 2 root root 4096 Oct 14 18:38 .cache/
-rw-r--r-- 1 root root 948236288 Oct 20 04:31 FQHY_GHOST_XP_SP3_V2015_07.iso
-rw-r--r-- 1 root root 140 Apr 19 2012 .profile
drwxr-xr-x 2 root root 4096 Oct 14 18:38 .ssh/
-rw-r--r-- 1 root root 9161840 Oct 16 22:05 wa2600_fat.bin
root@cvknode:~#
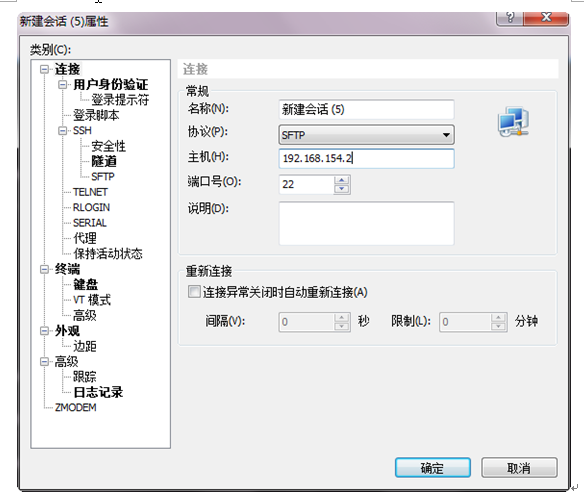
在本地电脑上通过SFTP 登陆到CAS中,以xShell为例
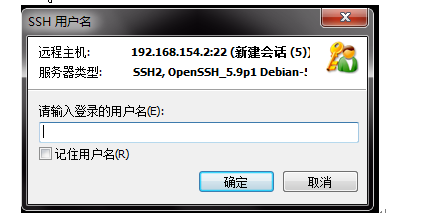
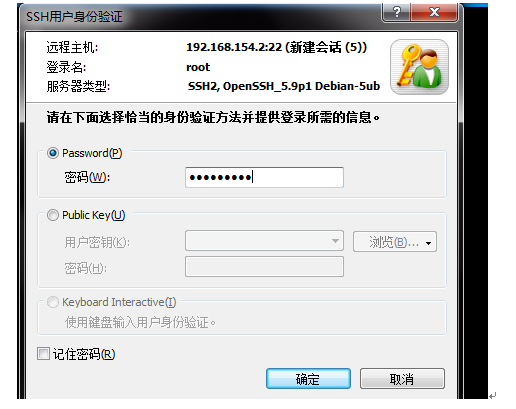
输入用户名和密码之后登陆到CAS中
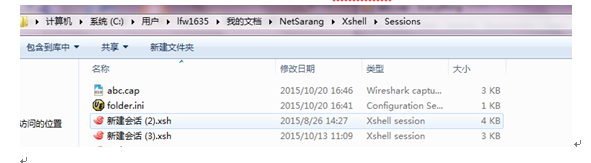
Your current local directory is
C:\Users\lfw1635\Documents\NetSarang\Xshell\Sessions
Type `help' to browse available commnands.
sftp:/root>
sftp:/root>
通过命令ls看到此文件
sftp:/root> ls
-rw-r--r-- 1 root root 9161840 Oct 16 22:05 wa2600_fat.bin
-rw-r--r-- 1 root root 3001 Oct 21 00:38 abc.cap
-rw-r--r-- 1 root root 948236288 Oct 20 04:31 FQHY_GHOST_XP_SP3_V2015_07.iso
-rw------- 1 root root 82 Oct 20 04:28 .bash_history
drwx------ 4 root root 4096 Oct 21 00:23 .
drwx------ 2 root root 4096 Oct 14 18:38 .cache
-rw-r--r-- 1 root root 140 Apr 19 2012 .profile
drwxr-xr-x 2 root root 4096 Oct 14 18:38 .ssh
-rw-r--r-- 1 root root 3106 Apr 19 2012 .bashrc
drwxr-xr-x 25 root root 4096 Oct 14 17:53 ..
sftp:/root>
sftp:/root> get abc.cap abc.cap //将CAS本地的abc.cap文件拷贝到登陆电脑的以abc.cap文件保存
sftp: cannot open /root/def.cap to read
Fetching /root/abc.cap to abc.cap
sftp: received 2.93 KB in 0.01 seconds
然后就可以在对应路径下面看到此文件,可以通过wireshark软件打开
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
