问题描述:
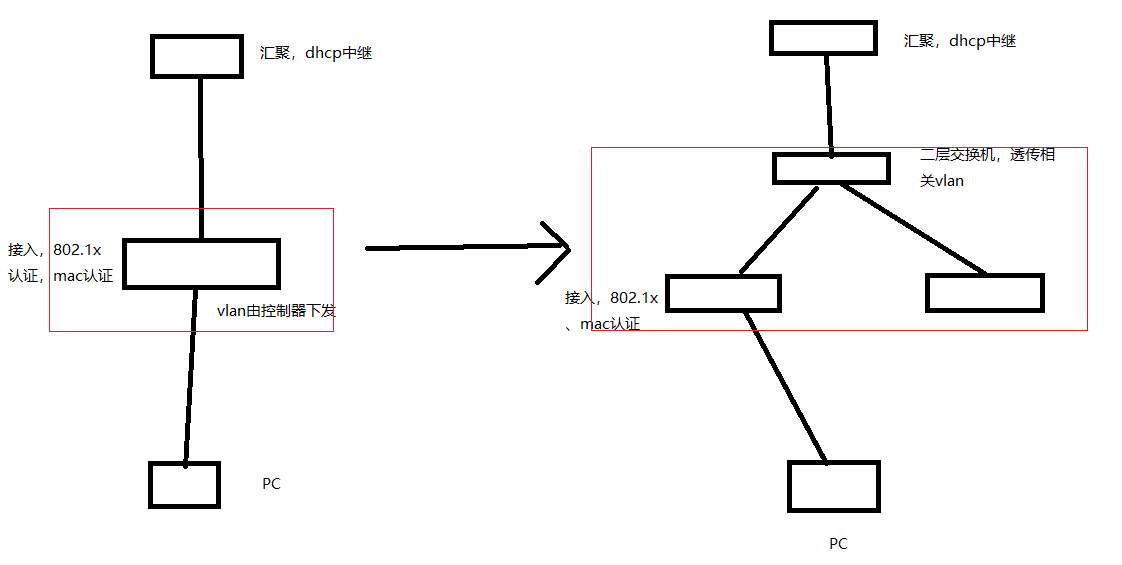
一台接入交换机(左侧红框)替换成有图三台s5130交换机(右侧红框),替换前设备802.1x认证功能正常,可以正常上网。
替换后,由最下方两台充当接入交换机,配置802.1x认证及mac认证,由一台二层交换机透传到汇聚,交换机替换之后,终端就无法进行802.1x认证无法上网了,在接入交换机上无法学习到pc的mac,pc上查看发现无ip地址。
备注: 将接入下联pc的端口取消802.1x及mac认证后,手动配置port access vlan xxx可以正常上网。
原老交换机为v5版本,型号忘了,有些指令在新交换机上不支持,如radius方案里的server-type extended,domain域下的access-limit disable ,idle-cut disable,self-service-url disable等指令。其他配置和老交换机基本一直。
请问是啥原因导致无法认证上网啊
组网及组网描述:
- 2023-09-20提问
- 举报
-
(0)
最佳答案

这个交换机上面开启debug 日志 看下有没有什么报错信息
- 2023-09-20回答
- 评论(1)
- 举报
-
(0)
基本没有什么报错,就是阶段性显示,instance‘s 0 port xxx端口,was notified a topology change。但是检查了下组网发现是无环路的

交换机管理地址有设置免认证吗
https://www.h3c.com/cn/d_202308/1904486_30005_0.htm
- 2023-09-20回答
- 评论(4)
- 举报
-
(0)
管理地址免认证?请问指令是啥呀?
dot1x ead-assistant free-ip 172.27.100.31 255.255.255.255
[S5130S-N-3F]dis cu # version 7.1.070, Release 6343P08 # sysname S5130S-N-3F # telnet server enable # irf mac-address persistent timer irf auto-update enable undo irf link-delay irf member 1 priority 1 # dot1x dot1x authentication-method eap dot1x quiet-period dot1x access-user log enable abnormal-logoff failed-login normal-logoff successful-login dot1x ead-assistant enable dot1x ead-assistant url https://10.60.10.2:7443/system/nacclient dot1x ead-assistant free-ip 172.27.100.31 255.255.255.255 # lldp global enable # password-recovery enable # vlan 1 # vlan 27 # vlan 103 # stp global enable # interface NULL0 # interface Vlan-interface27 description 远程管理 ip address 172.27.100.31 255.255.255.0 # interface Vlan-interface103 # interface GigabitEthernet1/0/1 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/2 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/3 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/4 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/5 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/6 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/7 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/8 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/9 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/10 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/11 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/12 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/13 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/14 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/15 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/16 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/17 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/18 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/19 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/20 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/21 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/22 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/23 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/24 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/25 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/26 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/27 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/28 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/29 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/30 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/31 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/32 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/33 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/34 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/35 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/36 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/37 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/38 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/39 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/40 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/41 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/42 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/43 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/44 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/45 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/46 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/47 port access vlan 103 stp edged-port dot1x undo dot1x handshake undo dot1x multicast-trigger # interface GigabitEthernet1/0/48 port access vlan 103 stp edged-port undo dot1x handshake undo dot1x multicast-trigger # interface Ten-GigabitEthernet1/0/49 port link-type trunk undo port trunk permit vlan 1 port trunk permit vlan 27 103 # interface Ten-GigabitEthernet1/0/50 port link-type trunk undo port trunk permit vlan 1 port trunk permit vlan 27 103 # interface Ten-GigabitEthernet1/0/51 port link-type trunk undo port trunk permit vlan 1 port trunk permit vlan 27 103 # interface Ten-GigabitEthernet1/0/52 description CH-S12504G-N-XG2/0/2 port link-type trunk undo port trunk permit vlan 1 port trunk permit vlan 27 103 # scheduler logfile size 16 # line class aux user-role network-admin # line class vty user-role network-operator # line aux 0 user-role network-admin # line vty 0 63 authentication-mode scheme user-role network-operator # ip route-static 0.0.0.0 0 172.27.100.254 # info-center loghost 172.17.100.250 # snmp-agent snmp-agent local-engineid 800063A28014962D968B5A00000001 snmp-agent community read read snmp-agent community write write snmp-agent sys-info version all snmp-agent trap enable arp snmp-agent trap enable radius snmp-agent trap enable stp snmp-agent trap enable syslog # ifmonitor crc-error slot 1 high-threshold 1000 low-threshold 100 interval 30 ifmonitor input-error slot 1 high-threshold 1000 low-threshold 100 interval 30 ifmonitor output-error slot 1 high-threshold 1000 low-threshold 100 interval 30 # ssh server enable # undo password-control length enable undo password-control composition enable password-control length 4 undo password-control complexity user-name check # radius session-control enable # radius scheme system primary authentication 10.60.10.2 key cipher $c$3$kh8hsGJFoXGWKSf4DKCbydvNLUKnkhTAmQ== primary accounting 10.60.10.2 key cipher $c$3$WYjPLIV8GQxf+IwXqx2F/fQV2vBjspA3Qw== key authentication cipher $c$3$LtuH3Sd7NbESzQMrubMF0BEciF2TJ1NsbA== key accounting cipher $c$3$tqvpIpNaYITNzl7KAgTZBdvl17TxUqPKqQ== user-name-format without-domain nas-ip 172.27.100.31 # radius scheme topnac primary authentication 10.60.10.2 key cipher $c$3$kh8hsGJFoXGWKSf4DKCbydvNLUKnkhTAmQ== primary accounting 10.60.10.2 key cipher $c$3$WYjPLIV8GQxf+IwXqx2F/fQV2vBjspA3Qw== key authentication cipher $c$3$LtuH3Sd7NbESzQMrubMF0BEciF2TJ1NsbA== key accounting cipher $c$3$tqvpIpNaYITNzl7KAgTZBdvl17TxUqPKqQ== user-name-format without-domain nas-ip 172.27.100.31 # domain system authorization-attribute idle-cut 15 1024 authentication lan-access radius-scheme topnac authorization lan-access radius-scheme topnac accounting lan-access radius-scheme topnac # domain topsec authorization-attribute idle-cut 15 1024 authentication lan-access radius-scheme topnac authorization lan-access radius-scheme topnac accounting lan-access radius-scheme topnac # domain default enable topsec # role name level-0 description Predefined level-0 role # role name level-1 description Predefined level-1 role # role name level-2 description Predefined level-2 role # role name level-3 description Predefined level-3 role # role name level-4 description Predefined level-4 role # role name level-5 description Predefined level-5 role # role name level-6 description Predefined level-6 role # role name level-7 description Predefined level-7 role # role name level-8 description Predefined level-8 role # role name level-9 description Predefined level-9 role # role name level-10 description Predefined level-10 role # role name level-11 description Predefined level-11 role # role name level-12 description Predefined level-12 role # role name level-13 description Predefined level-13 role # role name level-14 description Predefined level-14 role # user-group system # local-user admin class manage password hash $h$6$sjYof+1HcCT8HJyn$8RV7JoJmPczsOE4WuyxtMrOUB6WVy7mqNbzYzD7gt4K3XJpg3ngSo8lmiuawfKb6yLbA+GWmeNMbFqF0uH15uw== service-type telnet ssh authorization-attribute user-role network-admin authorization-attribute user-role network-operator # return
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明


基本没有什么报错,就是阶段性显示,instance‘s 0 port xxx端口,was notified a topology change。但是检查了下组网发现是无环路的