v5路由器msr2600-10
- 0关注
- 0收藏,1339浏览
问题描述:
请问各位大佬,现在遇到了一个SSL VPN的问题,配置后,iNode拨号提示证书验证失败,可是路由器并没有证书相关的配置,认证方式也是本地认证;查看官网上的配置文档发现是结合认证服务器的场景,由于现场原因无法与官网上的配置1:1,请问有没有纯本地认证配置的场景案例,并且路由器的系统为V5版本,请问有没有大佬实施过我这种相关案例
- 2024-01-04提问
- 举报
-
(0)


您好,参考
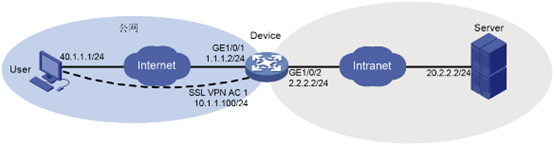
SSL VPN配置示例:
IP接入配置举例(缺省证书)
#
interface SSLVPN-AC1
ip address 10.1.1.100 255.255.255.0
#
acl advanced 3000
rule 0 permit ip source 10.1.1.0 0.0.0.255 destination 20.2.2.0 0.0.0.255
#
sslvpn ip address-pool sslvpnpool 10.1.1.1 10.1.1.10
#
sslvpn gateway gw
ip address 1.1.1.2 port 4430
service enable
#
sslvpn context ctxip
gateway gw domain domainip
ip-tunnel interface SSLVPN-AC1
ip-tunnel address-pool sslvpnpool mask 255.255.255.0
ip-route-list rtlist
include 20.2.2.0 255.255.255.0
policy-group resourcegrp
filter ip-tunnel acl 3000
ip-tunnel access-route ip-route-list rtlist
service enable
#
local-user sslvpnuser class network
password simple 123456
service-type sslvpn
authorization-attribute user-role network-operator
authorization-attribute sslvpn-policy-group resourcegrp
#
[H3C]display sslvpn gateway
Gateway name: gw
Operation state: Up
IP: 1.1.1.2 Port: 4430
Front VPN instance: Not configured
[H3C]display sslvpn context
Context name: ctxip
Operation state: Up
AAA domain: Not specified
Certificate authentication: Disabled
Password authentication: Enabled
Authentication use: All
Dynamic password: Disabled
Code verification: Disabled
Default policy group: Not configured
Associated SSL VPN gateway: gw
Domain name: domainip
Maximum users allowed: 1048575
VPN instance: Not configured
Idle timeout: 30 min
IPsec野蛮模式配置示例:
RTA------------------------------------------------------------------RTB
RTA分部:
192.168.1.0/24 1.1.1.1/24 1.1.1.2/24 192.168.2.0/24
#
interface LoopBack0
ip address 192.168.1.1 255.255.255.255
#
interface GigabitEthernet0/0
ip address 1.1.1.1 255.255.255.0
ipsec apply policy policy1
#
ip route-static 0.0.0.0 0 1.1.1.2
#
acl advanced 3000
rule 0 permit ip source 192.168.1.0 0.0.0.255 destination 192.168.2.0 0.0.0.255
#
ipsec transform-set tran1
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec policy policy1 1 isakmp
transform-set tran1
security acl 3000
remote-address 1.1.1.2
ike-profile 1
#
ike identity fqdn RTA
#
ike profile 1
keychain 1
exchange-mode aggressive
#
match remote identity fqdn RTB
proposal 1
#
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
#
ike keychain 1
pre-shared-key address 1.1.1.2 255.255.255.0 key simple 123
#
RTB:总部
#
interface LoopBack0
ip address 192.168.2.1 255.255.255.255
#
interface GigabitEthernet0/0
ip address 1.1.1.2 255.255.255.0
ipsec apply policy 1
#
ip route-static 0.0.0.0 0 1.1.1.1
#
acl advanced 3000
rule 0 permit ip source 192.168.2.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
#
ipsec transform-set tran1
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec policy-template template1 1
transform-set tran1
#可以不写ACL
#security acl 3000
ike-profile 1
#
ipsec policy 1 1 isakmp template template1
#
ike identity fqdn RTB
#
ike profile 1
keychain 1
exchange-mode aggressive
match remote identity fqdn RTA
proposal 1
#
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
#
ike keychain 1
pre-shared-key hostname RTA key simple 123
#
- 2024-01-04回答
- 评论(0)
- 举报
-
(0)
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明

暂无评论