组网及说明
路由器设备结合IMC做有线portal
问题描述
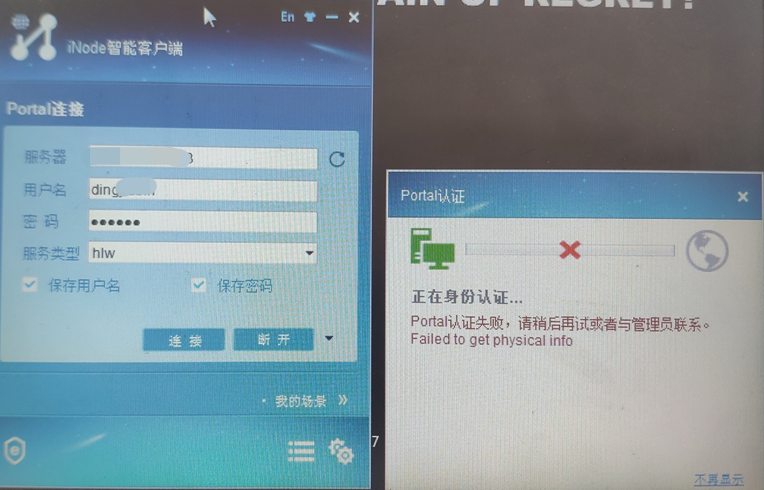
inode认证过程报错,如下:
过程分析
检查设备侧配置,无明显问题
ip vpn-instance ZWWW232 创建VPN实例,终端认证和IMC服务器均在实例进行认证交互报文
route-distinguisher 65010:232
vpn-target 65010:232 65010:2 import-extcommunity
vpn-target 65010:232 export-extcommunity
policy-based-route AAA permit node 1 通过策略路由进行VPN实例引入
if-match acl 3000
apply access-vpn vpn-instance ZWWW232
interface LoopBack2 使用该接口作为bas ip和nas ip
ip binding vpn-instance ZWWW232
ip address XX.221.185.132 255.255.255.255
interface GigabitEthernet0/2
port link-mode route
combo enable copper
ip address XX.218.99.125 255.255.255.252
ip policy-based-route AAA portal认证接口通过策略路由把终端的认证信息引入VPN实例进行
portal enable method layer3 采用三层portal认证
portal bas-ip XX.221.185.132
portal apply web-server portal
配置实例路由
#
ip route-static vpn-instance ZWWW232 XX.218.119.64 26 XX.218.99.126 public
ip route-static vpn-instance HLW332 XX.218.119.64 26 XX.218.99.126 public
#
radius scheme cxzwww
primary authentication XX.221.184.253 key cipher $c$3$ctPPrQoFq+yA8Qy6Kp76T1eh+3uQqWxaPA==
primary accounting XX.221.184.253 key cipher $c$3$AjKVSfogPrFrOAJq2o4Wx9WP/Eny8WoefQ==
nas-ip XX.221.185.132
vpn-instance ZWWW232
#
#
domain zwww
authorization-attribute idle-cut 30 10240
authorization-attribute vpn-instance ZWWW232
authentication portal radius-scheme cxzwww
authorization portal radius-scheme cxzwww
accounting portal radius-scheme cxzwww
#
#
portal free-rule 0 destination ip XX.221.184.253 255.255.255.255
portal free-rule 1 destination ip XX.221.185.2 255.255.255.255
portal free-rule 2 destination ip XX.221.185.3 255.255.255.255
portal free-rule 3 destination ip XX.221.185.4 255.255.255.255
#
portal web-server portal
url http://XX.221.184.253:8080/portal
vpn-instance ZWWW232
url-parameter ip source-address
url-parameter mac source-mac
#
portal server portal
ip XX.221.184.253 vpn-instance ZWWW232 key cipher $c$3$E54F2NtUXNWJ93PW80aQqHxsP3ZerqQ4Mw==
#
IMC侧检查配置无异常,同时在IMC侧打印调试信息
imc侧显示用户上线了,但是设备侧查看没有在线用户,查看日志,认证过程为:Imc发了req_auth --- 设备发送 radius code1 --- imc回复radius code 2 ---设备回ack_auth,携带error code 4,然后就终止了
Packet Type:ACK_AUTH(4)
SerialNo:147
Address:XX.221.184.253
Port:50908
RemoteIp:XX.221.185.132
RemotePort:2000
Version:portal 2.0
Auth Type:PAP
ErrorID:4
UserIP:XX.218.119.67
UserPort:0
ReqID:0
Rsvd:0
attriNum:3
</Head>
<Attributes>
Relay Message:36 06 00 00 00 00 37 06 00 00 00 00 38 06 00 00 00 00 3a 06 00 00 00 00 42 06 00 00 00 00 4a 06 00 00 00 00 43 11 52 30 30 33 42 30 35 44 30 34 32 53 50 30 35 3d 0a 48 47 4e 52 48 4d 4c 65
Text Info:Failed to get physical info
Device Ip:XX.221.185.132
同时在设备侧debug打印认证过程
*Mar 11 10:39:03:849 2021 PE-JT-3620 PORTAL/7/EVENT: User-SM[10.218.119.67]: Received authentication response, RespCode=0.
*Mar 11 10:39:03:849 2021 PE-JT-3620 PORTAL/7/FSM: Auth-SM: Started to run.
*Mar 11 10:39:03:849 2021 PE-JT-3620 PORTAL/7/FSM: Auth-SM [XX.218.119.67]: Entered state Authenticated.
*Mar 11 10:39:03:849 2021 PE-JT-3620 PORTAL/7/FSM: User-SM[XX.218.119.67]: Begin to run.
*Mar 11 10:39:03:849 2021 PE-JT-3620 PORTAL/7/FSM: User-SM [XX.218.119.67]: State changed from Authenticating to Waiting_Author.
*Mar 11 10:39:03:849 2021 PE-JT-3620 RADIUS/7/EVENT:
PAM_RADIUS: Processing RADIUS authorization.
*Mar 11 10:39:03:849 2021 PE-JT-3620 RADIUS/7/EVENT:
PAM_RADIUS: RADIUS Authorization successfully.
*Mar 11 10:39:03:849 2021 PE-JT-3620 PORTAL/7/EVENT: User-SM[XX.218.119.67]: AAA processed authorization request and returned success.
*Mar 11 10:39:03:849 2021 PE-JT-3620 PORTAL/7/EVENT: User-SM[XX.218.119.67]: Received session-timeout is 86400 sec.
*Mar 11 10:39:03:849 2021 PE-JT-3620 PORTAL/7/FSM: User-SM [XX.218.119.67]: State changed from Waiting_Author to Waiting_Rule_OK.
*Mar 11 10:39:03:850 2021 PE-JT-3620 PORTAL/7/ERROR: Failed to look up FIB info.
*Mar 11 10:39:03:850 2021 PE-JT-3620 PORTAL/7/ERROR: User(XX.218.119.67) will be logged off because the system failed to get user physical info while deploying the rule.
*Mar 11 10:39:03:850 2021 PE-JT-3620 PORTAL/7/FSM: Auth-SM: Started to run.
*Mar 11 10:39:03:850 2021 PE-JT-3620 PORTAL/7/FSM: Auth-SM [XX.218.119.67]: Entered state Offline.
*Mar 11 10:39:03:850 2021 PE-JT-3620 PORTAL/7/ERROR: User mac is invalid.
*Mar 11 10:39:03:850 2021 PE-JT-3620 PORTAL/7/ERROR: Failed to get get ssid by user mac,UserMac is Zero.
*Mar 11 10:39:03:850 2021 PE-JT-3620 PORTAL/7/PACKET:
Portal sent 132 bytes of packet: Type=ack_auth(4), ErrCode=4, IP=XX.218.119.67
*Mar 11 10:39:03:850 2021 PE-JT-3620 PORTAL/7/PACKET:
[ 33 RELAYMSG ] [ 65] [6]
[ 5 TEXTINFO ] [ 29] [Failed to get physical info]
[ 10 BASIP ] [ 6] [XX.221.185.132]
通过设备侧debug可见,在设备认证过程中在设备上查找FIB表失败,设备无法获取终端的mac信息,向IMC发送Type=ack_auth(4), ErrCode=4报错信息
二层portal查找终端ARP,三层portal找路由,debug显示FIB表查找失败,而FIB表由路由表生成,设备侧已配置静态路由,如下:
ip route-static vpn-instance ZWWW232 XX.218.119.64 26 XX.218.99.126 public
ip route-static vpn-instance HLW332 XX.218.119.64 26 XX.218.99.126 public
路由在对应的实例内引入,没什么问题,连通性也正常
后续再检查配置
interface GigabitEthernet0/2
port link-mode route
combo enable copper
ip address XX.218.99.125 255.255.255.252
ip policy-based-route AAA
portal enable method layer3
portal bas-ip XX.221.185.132
portal apply web-server portal
发现portal的认证接口是通过策略路由引入到vpn实例内的,正常情况portal接口是通过绑定vpn实例来将终端的引入对应实例内,而Portal查路由表是在启用portal的接口绑定的实例查找路由表的,现场配置的0/2接口是没有绑定vpn的,是通过策略路由引入VPN的,策略路由不会下发路由表,所有在portal查找过程中,设备底层实现就会去查到公网路由表,但是我们之前配置的静态路由是在VPN里面引入的,此时portal在公网路由表查找不到FIB表,所有就报错失败了
解决方法
#
ip route-static XX.218.119.64 26 XX.218.99.126
ip route-static vpn-instance ZWWW232 XX.218.119.64 26 XX.218.99.126 public
ip route-static vpn-instance HLW332 XX.218.119.64 26 XX.218.99.126 public
#
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
