组网及说明
spoke----hub-----spoke
问题描述
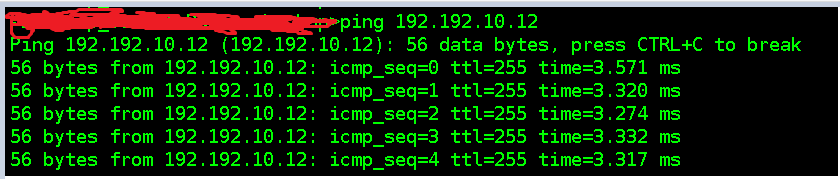
1.Spoke1的tunnel地址 ping HUB的tunnel地址不通
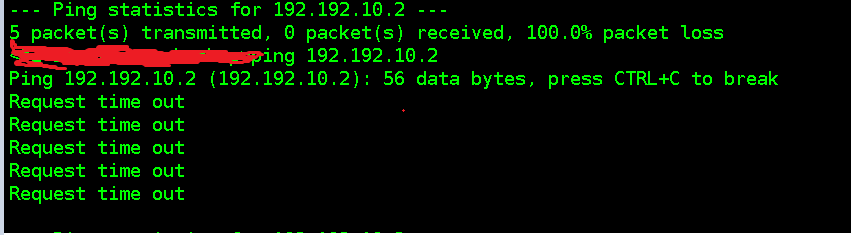
2.HUB的tunnel地址ping Spoke1的tunnel地址正常通的
过程分析
1、
#HUB tunnel 100的配置
interface Tunnel100 mode advpn udp
ip address ri 255.255.255.0
ospf network-type broadcast
source GigabitEthernet2/0/0
tunnel protection ipsec profile hub
vam client hub2 compatible advpn0
#spoke tunnel 100的配置
interface Tunnel100 mode advpn udp
ip address 192.192.10.12 255.255.255.0
ospf network-type broadcast
ospf dr-priority 0
source GigabitEthernet2/0/1
tunnel protection ipsec profile spoke
vam client spoke12 compatible advpn0
2、
采用的是ospf进行通信,并且ospf邻居关系已经起来了
===============display ospf peer===============
OSPF Process 10 with Router ID 192.192.10.2
Neighbor Brief Information
Area: 0.0.0.0
Router ID Address Pri Dead-Time State Interface
192.192.10.12 192.192.10.12 0 37 Full/DROther Tun100
192.192.10.23 192.192.10.23 0 39 Full/DROther Tun100
3、查看现场的ike sa 和ipsec sa 都已经起来了
3.1 ike sa
===============display ike sa verbose===============
-----------------------------------------------
Connection ID: 26
Outside VPN:
Inside VPN:
Profile:
Transmitting entity: Responder
Initiator COOKIE: 8dce0c0c24af8e5d
Responder COOKIE: 16ef7e2740aae161
-----------------------------------------------
Local IP/port: 175.25.49.88/500
Local ID type: IPV4_ADDR
Local ID: 175.25.49.88
Remote IP/port: 120.133.226.87/500
Remote ID type: IPV4_ADDR
Remote ID: 120.133.226.87
Authentication-method: PRE-SHARED-KEY
Authentication-algorithm: SHA1
Encryption-algorithm: 3DES-CBC
Life duration(sec): 86400
Remaining key duration(sec): 82690
Exchange-mode: Main
Diffie-Hellman group: Group 2
NAT traversal: Not detected
Extend authentication: Disabled
Assigned IP address:
Vendor ID index:0xa59
Vendor ID sequence number:0x19
-----------------------------------------------
Connection ID: 27
Outside VPN:
Inside VPN:
Profile:
Transmitting entity: Responder
Initiator COOKIE: 88b586a403200ae9
Responder COOKIE: e4f655afad5dff3c
-----------------------------------------------
Local IP/port: 175.25.49.88/500
Local ID type: IPV4_ADDR
Local ID: 175.25.49.88
Remote IP/port: 120.133.66.181/500
Remote ID type: IPV4_ADDR
Remote ID: 120.133.66.181
Authentication-method: PRE-SHARED-KEY
Authentication-algorithm: SHA1
Encryption-algorithm: 3DES-CBC
Life duration(sec): 86400
Remaining key duration(sec): 83803
Exchange-mode: Main
Diffie-Hellman group: Group 2
NAT traversal: Not detected
Extend authentication: Disabled
Assigned IP address:
Vendor ID index:0x793
Vendor ID sequence number:0x1a
-----------------------------------------------
Connection ID: 1
Outside VPN:
Inside VPN:
Profile: hub
Transmitting entity: Initiator
Initiator COOKIE: 2a7e7604289e3b74
Responder COOKIE: 37176d3ed068b5a7
-----------------------------------------------
Local IP/port: 175.25.49.88/500
Local ID type: IPV4_ADDR
Local ID: 175.25.49.88
Remote IP/port: 175.25.49.89/500
Remote ID type: IPV4_ADDR
Remote ID: 175.25.49.89
Authentication-method: PRE-SHARED-KEY
Authentication-algorithm: SHA1
Encryption-algorithm: 3DES-CBC
Life duration(sec): 86400
Remaining key duration(sec): 78266
Exchange-mode: Main
Diffie-Hellman group: Group 2
NAT traversal: Not detected
Extend authentication: Disabled
Assigned IP address:
Vendor ID index:0x722
Vendor ID sequence number:0x0
===================================================
===============display ike proposal===============
Priority Authentication Authentication Encryption Diffie-Hellman Duration
method algorithm algorithm group (seconds)
----------------------------------------------------------------------------
10 PRE-SHARED-KEY SHA1 3DES-CBC Group 2 86400
default PRE-SHARED-KEY SHA1 DES-CBC Group 1 86400
3.2 ipsec sa
===============display ipsec sa===============
-------------------------------
Interface: Tunnel100
-------------------------------
-----------------------------
IPsec profile: hub
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect forward secrecy:
Transmitting entity: Responder
Path MTU: 1320
Tunnel:
local address: 175.25.49.88
remote address: 120.133.226.87
Flow:
sour addr: 175.25.49.88/255.255.255.255 port: 18001 protocol: udp
dest addr: 120.133.226.87/255.255.255.255 port: 18001 protocol: udp 感兴趣流
[Inbound ESP SAs]
SPI: 1144551649 (0x443878e1)
Connection ID: 244813135873
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843145/286
Max received sequence-number: 0
Anti-replay check enable: N
Anti-replay window size:
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 551662763 (0x20e1b4ab)
Connection ID: 141733920768
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843145/286
Max sent sequence-number: 442
UDP encapsulation used for NAT traversal: N
Status: Active
-----------------------------
IPsec profile: hub
Mode: ISAKMP
-----------------------------
Tunnel id: 1
Encapsulation mode: tunnel
Perfect forward secrecy:
Transmitting entity: Responder
Path MTU: 1320
Tunnel:
local address: 175.25.49.88
remote address: 120.133.66.181
Flow:
sour addr: 175.25.49.88/255.255.255.255 port: 18001 protocol: udp
dest addr: 120.133.66.181/255.255.255.255 port: 18001 protocol: udp
[Inbound ESP SAs]
SPI: 740990799 (0x2c2a9f4f)
Connection ID: 12884901891
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843153/1011
Max received sequence-number: 0
Anti-replay check enable: N
Anti-replay window size:
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 4261032774 (0xfdfa3346)
Connection ID: 12884901890
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843152/1011
Max sent sequence-number: 388
UDP encapsulation used for NAT traversal: N
Status: Active
-----------------------------
IPsec profile: hub
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect forward secrecy:
Transmitting entity: Responder
Path MTU: 1320
Tunnel:
local address: 175.25.49.88
remote address: 120.133.226.87
Flow:
sour addr: 175.25.49.88/255.255.255.255 port: 18001 protocol: udp
dest addr: 120.133.226.87/255.255.255.255 port: 18001 protocol: udp
[Inbound ESP SAs]
SPI: 2305858321 (0x89709b11)
Connection ID: 4294967300
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843191/2987
Max received sequence-number: 0
Anti-replay check enable: N
Anti-replay window size:
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 278442632 (0x1098b288)
Connection ID: 4294967301
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843192/2987
Max sent sequence-number: 62
UDP encapsulation used for NAT traversal: N
Status: Active
4、现场进行debug,在HUB上看,能收到icmp报文,也回复给spoke了,但spoke收不到

解决方法
在tunnel口下加了一个service slot 2
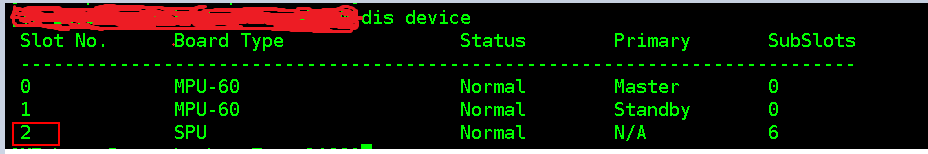
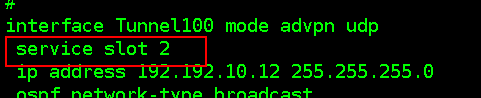

原因: msr多槽位的设备的逻辑接口处理会话报文时需要加上service slot命令指定一下接口, 不指定槽位的时候可能会有全局接口把会话报文被分开处理,然后时序问题或者报文匹配不上会话
注意事项: tunnel,route-aggregation 等全局性的接口如果涉及会话流量在非堆叠场景下都推荐配置service slot 命令
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
